CA和证书
安全机制
墨菲定律
如果有两种选择,其中一种将导致灾难,则必定有人会作出这种选择。即:做事不要有侥幸心理。
常用安全技术
认证、授权、审计、安全通信
加密算法和协议
对称加密算法
加密和解密使用同一个秘钥。
特性
- 加密、解密使用同一个秘钥,效率高
- 将原始数据分割为固定大小的块,逐个加密
缺陷
- 秘钥过多
- 秘钥分发
- 数据来源无法确认
常见算法
DES、3DES、AES、IDEA、Blowfish、RC6
非对称加密算法
秘钥是成对出现
- 公钥:public key,公开给所有人,主要给别人加密使用
- 私钥:secret key,private key,自己留存,必须保证其私密性,用于自己加密签名
- 特点:用公钥加密数据,只能使用与之配对的私钥解密;反之亦然
功能:
- 数据加密:适合加密较小数据;如:加密对称秘钥
- 数字签名:主要在于让接收方确认发送方身份
缺点
- 密钥长,算法复杂
- 加密解密,效率低下
常见算法
RSA、DSA、ECC
场景
非对称加密实现加密
接收者:生成公钥/秘钥对,公开公钥,保密秘钥
发送者:使用接收者的公钥来加密消息,将加密后的消息发送给接收者
接收者:使用秘钥来解密消息
非对称加密实现数字签名
发送者:生成公钥/秘钥对,公开公钥,保密秘钥,使用秘钥加密消息,将加密后的消息发送给接收者
接收者:使用发送者的公钥来解密
CA和证书
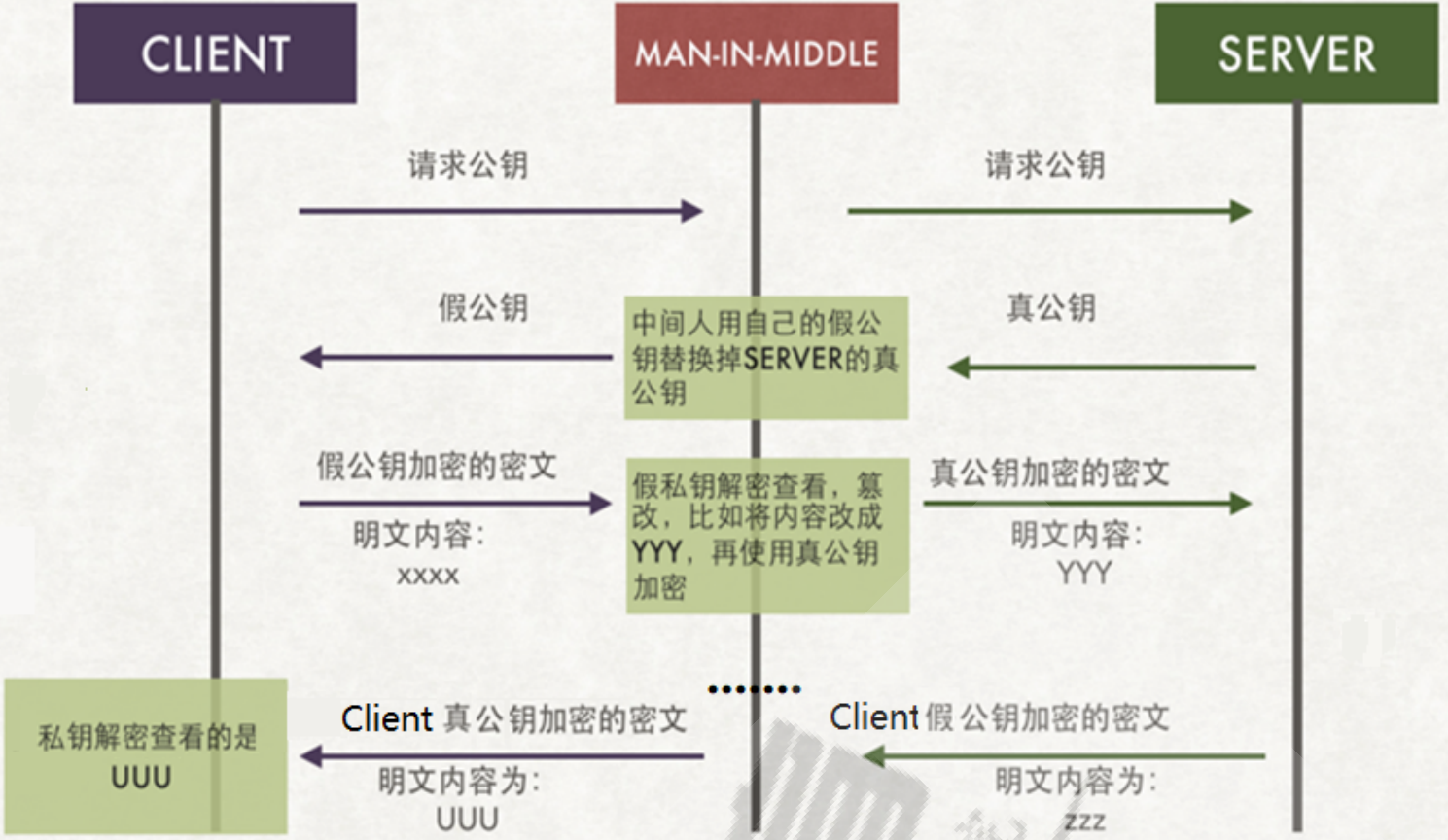
中间人攻击(MTM)
攻击者与通讯的两端分别创建独立的联系,并交换其所收到的数据,使通讯的两端认为他们正在通过一个私密的连接与对方直接对话,但事实上整个会话都被攻击者完全控制。 在中间人攻击中,攻击者可以拦截通讯双方的通话并插入新的内容。
SSL/TLS
SSL:Secure Socket Layer??????? TLS:Transport Layer Security
功能
- 身份验证:SSL身份验证,指在客户端与服务器之间建立SSL连接时,通过SSL证书对服务器进行身份验证的过程。SSL证书是由可信的第三方机构(称为CA机构)颁发的,用于证明服务器身份的数字证书。
- 数据加密:SSL数据加密,指在客户端与服务器之间建立SSL连接后,通过使用加密算法对传输的数据进行加密处理,以保证数据在传输过程中不被窃听、篡改或伪造。
- 数据完整性:SSL数据完整性,是指通过数字签名等技术,在客户端与服务器之间建立的SSL连接中,保证传输的数据在传输过程中不被篡改或损坏。
HTTPS
http协议 + ssl/tls协议。
工作流程
1. 客户端发起HTTPS请求
用户在浏览器里输入一个https网址,然后连接到服务器的443端口
2. 服务端的配置
采用HTTPS协议的服务器必须要有一套数字证书,可以自己制作,也可以向组织申请。区别就是自己颁发的证书需要客户端验证通过,才可以继续访问,而使用受信任的公司申请的证书则不会弹出提示页面。这套证书其实就是一对公钥和私钥
3. 传送服务器的证书给客户端
证书里其实就是公钥,并且还包含了很多信息,如证书的颁发机构,过期时间等等
4. 客户端解析验证服务器证书
这部分工作是由客户端的TLS来完成的,首先会验证公钥是否有效,比如:颁发机构,过期时间等
等,如果发现异常,则会弹出一个警告框,提示证书存在问题。如果证书没有问题,那么就生成一
个随机值。然后用证书中公钥对该随机值进行非对称加密
5. 客户端将加密信息传送服务器
这部分传送的是用证书加密后的随机值,目的就是让服务端得到这个随机值,以后客户端和服务端
的通信就可以通过这个随机值来进行加密解密了
6. 服务端解密信息
服务端将客户端发送过来的加密信息用服务器私钥解密后,得到了客户端传过来的随机值
7. 服务器加密信息并发送信息
服务器将数据利用随机值进行对称加密,再发送给客户端
8. 客户端接收并解密信息
客户端用之前生成的随机值解密服务段传过来的数据,于是获取了解密后的内容
术语
PKI:公共秘钥加密体系
CA:签证机构
RA:注册机构
CRL:证书吊销列表
证书存取库:
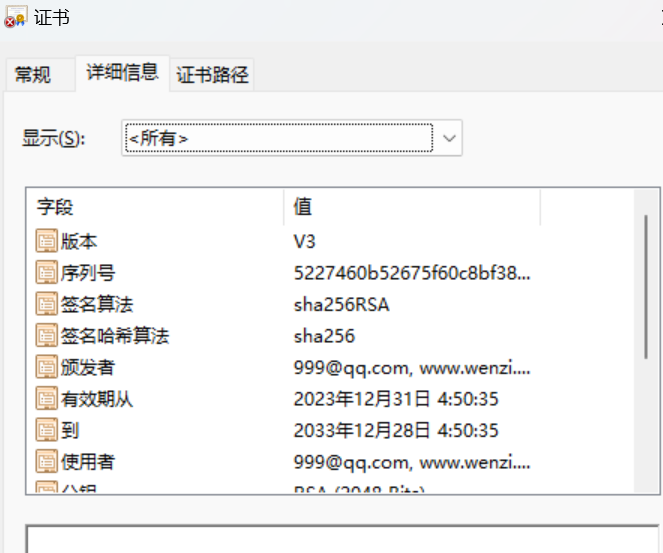
X.509:定义了证书的结构以及认证协议标准
- 版本号
- 序列号
- 签名算法
- 颁发者
- 有效期限
- 主体名称
证书类型
- 证书授权机构的证书
- 服务器证书
- 用户证书
获取证书两种方法
- 自签名证书:自己签发自己的公钥
- 使用证书授权机构:
- 生成证书请求CSR
- 将证书请求CSR发送给CA
- CA签名颁发证书
OpenSSL
OpenSSL是一个开放源代码的软件库包,应用程序可以使用这个包来进行安全通信,避免窃听,同时确认另一端连线者的身份。
组件
- ibcrypto:用于实现加密和解密的库
- libssl:用于实现ssl通信协议的安全库
- openssl:多用途命令行工具
命令
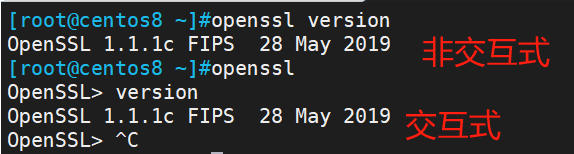
两种运行模式
- 交互模式
- 批处理模式
三种子命令
- 标准命令
- 消息摘要命令
- 加密命令
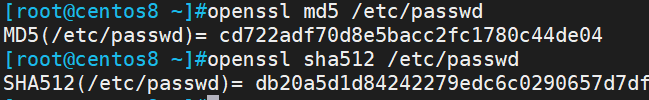
单向哈希加密
工具:openssl dgst
算法:md5sum, sha1sum, sha224sum,sha256sum
生成用户密码
openssl passwd [options] [password]
常用选项:
-1:表示使用MD5加密算法
-5:表示使用SHA256加密算法
-6:表示使用SHA512加密算法,/etc/shadow使用该算法
-in:表示从文件中读取密码
-stdin:表示从标准输入读取密码
-salt:指定salt值,不使用随机产生的salt。在使用加密算法进行加密时,即使密码一样,salt不一样,所计算出来的hash值也不一样。除非密码一样,salt值也一样,计算出来的hash值才一样。
[root@centos8 ~]#echo wenzi | openssl passwd -6 -salt Y16DiwuVQtL6XCQK -stdin
$6$Y16DiwuVQtL6XCQK$MQEkn8e5iJ7haOIpJcO9cGkPS5c7gBG..7DxCVnr/9ozge2K5oAVpvoNDOWI0pBG7czyCMU4TaGmDo5W1H4c91
创建新用户同时指定密码,在CentOS8和Ubuntu都通用
[root@centos8 ~]#useradd -p `echo admin | openssl passwd -6 -salt abcdefghijk -stdin` liubei
查看
[root@centos8 ~]#getent shadow liubei
liubei:$6$abcdefghijk$heeR9m6lKuX0TKg/89kyy.po/71nRAlKWIocZj5Jg7AylICvzBMi8ZSYZJoOJ1V4lxMu4bxxWWGmyG2DQUHJr.:19721:0:99999:7:::
生成随机数
openssl rand -base64
生成随机10位长度密码
[root@centos8 ~]#openssl rand -base64 9 | head -c 10
l0t440TrGA
[root@centos8 ~]#tr -dc '[[:alnum:]]' < /dev/urandom | head -c 10
a1YZyCEtkB实现PKI
文档:man genrsa
生成私钥
(umask 077;openssl genrsa -out 私钥存储路径 2048)
[root@centos8 ~]#(umask 077;openssl genrsa -out /data/test1.key 2048)
Generating RSA private key, 2048 bit long modulus (2 primes)
...........................+++++
.+++++
e is 65537 (0x010001)
[root@centos8 ~]#cat /data/test1.key
-----BEGIN RSA PRIVATE KEY-----
MIIEpAIBAAKCAQEAqdmKz6zw6NNUnOxd00e5qa3kTzzhvjylQvixBMd4IethRptV
HddgmYcveFR6FbDwjEhoxyRNnAYWXX2J3pUyq0qTN2r/Mk5k3PI9ucznbfH+gLz5
SJJs19eRuTUniDYLObaRqA6KhhCOauiQinQ+w+WlUpS97e9Rqy7EO/3m0IC4WhK8
X0wpIlHnIAeGHDf9VOgWLP/PuzNeVkxk+7nScQVfNCQ5eh5qfuCDhjkotAtK89IM
3cSsKHuYbnR55RqGm5Z4fVk4AziiW8UgWBVmjyMHL4SZfRDFBDo1qi0NrJMNVB1Q
SUdcfdljYewdRhCEUeL5dXhA2Jsn4CxxLVl61wIDAQABAoIBAQCTFFV21sxa4T2h
EbGB1td4jqNo1lCpOrzlDJPFjrGBteErkjEXwTzeVckOiyCZDfqPj9hjshUeqcrO
NHqh61LQL6jh0V6hgm8nQQGglkZF18tKUdoQNPPZyMtgtR3BfwMje+wPul/MDiQ1
gaRAsL71RjRuGW2Kz7VJ5hp51Lj+DT+oSFPzq85I479fXl/QGBl4G9ZoXjMRu/ef
YPE9DzXnTVa54aPr1E0lRcDfEPgcunvFRVZDOZZf0X2WBWv14tq1P5hyoBQj2aW5
k9yQkJEJWPDhmndpjvsPYw6NhnOI6tcNSjJt/PHF0/jJ0ruIPSWTz4Tu4Rsu4N7D
fDyjspoJAoGBANkNWe556n56XkQnoGcnU04kTVoJFpmsmHemAiEQaDaXYd6xSaHx
9HPQpIt0G2n4MPcoPDu86jnUBC/IDIJP6ag7wnlKOcfVu43k3+/tkiB1jJv5hxP+
aJECBIr2JMybmUZrBKGb9ZitRUj0CVpXvOhJRoWRLuIwIf1zlNIpnY79AoGBAMhT
3y2AMX6bsNsFzSqcWmPdh5oKjDrVnSC/Txf/Cd8fuC4TzVN+8UwfxmCae4EGjRyG
Hcmenmq6KVqyBZDRW8rBfQuk9Va1k01+wns6XMwf68hdHdjEN+e6Iicct6uqwsC1
GQbEBW+8isfnEv2hwmviVd8ME86AlA+/2uayuJtjAoGAN3bk8z6uQHGuowXpRFLV
Q9Oc/JPz9YMYVwLR6ncR2llmxgxRv5NfnzTCx2v9EWA9yvq6IZ3N0Mcv5rHdGHOp
Rrc2o93m0/z293R0ERCJVcgUDUt/TAmn2N5GIOhzUOG2EjuIrG95G/GzEchil3Zy
LH2FCt6lt2ELXoPplKbTv1UCgYEAh6aTp6H44fzXQ1ioV0RMyPcHjb26u1RO9A/X
pS4kJxy5gSoTjYiWKLATivLQ0sv23evLW+225BpvSmTl8+xwtdlTrYDkSPTnbEB7
vSoGEItFBAZZ4aDtIlMeMVH25Z3aBtgavEQcUk9fwoGskGbq2lcHQuRQvTLAD/Ig
brty2nUCgYB00pNNZUBr3LFJV5tQcv5dCJC6ydlVwNaljsULYq8QfHxGuFeJ//6P
ktMngrII33qb/EffNBXF/0nDhqxKfTzi77izzywN35kUYIgMkdRf9yYl8p21ijv9
CHnO9jVnYPwqR3Xtq/0f9LAbCVJekBjIK8+da6EYjj2YFNYucKDq5Q==
-----END RSA PRIVATE KEY-----
解密加密的私钥
openssl rsa -in 原私钥路径 -out 新私钥路径
生成加密的私钥
[root@centos8 data]#openssl genrsa -out /data/test1.key -des3 1024
Generating RSA private key, 1024 bit long modulus (2 primes)
..........................................+++++
.........+++++
e is 65537 (0x010001)
Enter pass phrase for /data/test1.key:
Verifying - Enter pass phrase for /data/test1.key:
[root@centos8 data]#cat /data/test1.key
-----BEGIN RSA PRIVATE KEY-----
Proc-Type: 4,ENCRYPTED
DEK-Info: DES-EDE3-CBC,7FB3B71681AD9D1C
M/hy2ShToDhzdE4fLHNHonBZBSL3y+RVMmxwMCcsN8ZZ8fynzH9mhQI5VlF8yi8f
PLUr+G+3clQCYozZVNGsoGS/FObN2NpU+LU6hTUpQqgRnBqyB9UXcSfOK/0fUqgG
iQ0IJ7em4OsTiGwHl+wE23/xbsST6eTEnjXcYe6TszSh0YwsFcCfu7WlWtOLTvfb
P/GDnQqtaMhGcUVUqdkRok6188AmX1f9YI693I5DkJxbAhSyuhgqFjzRnt7zcyDM
kv8VT+HGmkuJZCLaQIdTbNpDkrx41rrExdYO+LdnvQQr71eEYr34egAXGf6pU7MW
fm69skDcrQJqBjt2+hyI0mp0RwQ9rYYGEdRaa7oHlwSXPnMWJu1fOg9o1wZmOgPu
pm4pu/ugu46/f0XMaIyvwMKn/5dVBuKpOpg/hj+1+3wGfYeRbFSwIsVJIZPCbfYZ
fLqAcmNaFWmD+XkuUoLppfnY2wuMf7Kf3+zGdZqx30LaDg1+U21NZN9hreyMqxIl
tvc66Vf1BiaTNiyLZibS9TzCO/DiXtERMJmPETcSx4zwdOTHJaP0rck1M/lgHSZU
4+2/ODk9le8EcKSOGO6BfksTysL1MXUxwRXCl+4UB6bV9xu33GelPM2PR8wf+c8p
SI5J85/YditCXdpO85geNPvljAizn/+0YYbJasHwPZNGUm6QGPLCECBQWWAyM3A0
2tOH7lMa3g4ZFV383GZ6CTS1U7kMZeKTysIqTnLfPirTnhcTBTJG0+C8FiThJWmt
hmfa7dSTSa5+NoToIeo+SGB12IE05ZyCvUDhwQojbivOEb8OUS9dYw==
-----END RSA PRIVATE KEY-----
解密加密的私钥
[root@centos8 data]#openssl rsa -in /data/test1.key -out /data/test2.key
Enter pass phrase for /data/test1.key:
writing RSA key
[root@centos8 data]#ll /data/
total 8
-rw------- 1 root root 963 Dec 31 03:50 test1.key
-rw------- 1 root root 887 Dec 31 03:51 test2.key
[root@centos8 data]#cat test2.key
-----BEGIN RSA PRIVATE KEY-----
MIICXQIBAAKBgQD3Xxxc1vhCK10Arz3ENbaMX/2QYl8MdULe6lrPhM4wsp9uzkOv
K+YD2ORT+AC70GAdE3kbGmq24z09/232iUB0AJxBvQp++MusDgTr3OpEB/1YLL9a
ZusvjEfgUIkLNL0lTVsEAu7cY2p4yPuWBDwpyEZoxzVYn/2k4xSRFPgtIQIDAQAB
AoGAITNmvx8rGtZvGRRsGdWLtrN7eNF7KFTksL6LiaatdePDej+83dnqeUG3A34Z
uxtwivZ+HqEhCYLeSV/rBlfNioCtGGL/yAbMm/Oke4ztraBmObFLYKCRj6l6pzHQ
NbPN/qOxuERFwEloHCf5jO6TaCRjnn/5c3lTQKpGylJOVzECQQD9VQ+cQdc/Sx3M
qZWZlr3vtXdAiSGG/ZGT49jPpfE55Yz+w9jUg35URRyZ83F5iblGCJpiZmvI99I7
jbP+X0wLAkEA+fn7D27PWPlusvd5nNCY5NQ3UVi98L6xyf1UjsINo6etNntYpGg1
OLHyIDJ98i513q7hCEIxj7JLVXgPspN7AwJBAIJUJHfLF6WkS2xjQmeFual8viEh
a3I7OY3QBlatlHCou+TFdOO/0logRBqft51DUWHKQ0KkVodJl4qz2AnhlQkCQQDK
lYSZpTv053CHKXgtVgASssmB62FDUcfT4rI8X5eeIa2Gkb/svWckY1HONh1Lv8tW
hHNqtfpkciILShmup0bxAkAkxNRZLVpZsTs+D07FfmuIL5DhXHCRlZ7PF5N6RouM
fpStaqpbqU+c17ffm2HdnfA8NaH5dwbzrfWxCYKDY8WG
-----END RSA PRIVATE KEY-----
从私钥中提取公钥
openssl rsa -in 私钥路径 -pubout -out 公钥存储路径
[root@centos8 ~]#openssl rsa -in /data/test1.key -pubout -out /data/test1.key.pub
writing RSA key
[root@centos8 ~]#ll /data/
total 8
-rw------- 1 root root 1679 Dec 31 03:38 test1.key
-rw-r--r-- 1 root root 451 Dec 31 03:42 test1.key.pub
[root@centos8 ~]#cat /data/test1.key.pub
-----BEGIN PUBLIC KEY-----
MIIBIjANBgkqhkiG9w0BAQEFAAOCAQ8AMIIBCgKCAQEAqdmKz6zw6NNUnOxd00e5
qa3kTzzhvjylQvixBMd4IethRptVHddgmYcveFR6FbDwjEhoxyRNnAYWXX2J3pUy
q0qTN2r/Mk5k3PI9ucznbfH+gLz5SJJs19eRuTUniDYLObaRqA6KhhCOauiQinQ+
w+WlUpS97e9Rqy7EO/3m0IC4WhK8X0wpIlHnIAeGHDf9VOgWLP/PuzNeVkxk+7nS
cQVfNCQ5eh5qfuCDhjkotAtK89IM3cSsKHuYbnR55RqGm5Z4fVk4AziiW8UgWBVm
jyMHL4SZfRDFBDo1qi0NrJMNVB1QSUdcfdljYewdRhCEUeL5dXhA2Jsn4CxxLVl6
1wIDAQAB
-----END PUBLIC KEY-----建立私有CA实现证书申请颁发
openssl配置文件:/etc/pki/tls/openssl.cnf
其中重要项:
[ CA_default ]
dir = /etc/pki/CA CA的主要目录,用于存储证书、私钥、CRL等文件。
certs = $dir/certs 存储已颁发的证书
crl_dir = $dir/crl 存储已签名的证书撤销列表(CRL)
database = $dir/index.txt 数据库索引文件,存储证书对应哪个网站
#unique_subject = no # Set to 'no' to allow creation of
# several certs with same subject.
new_certs_dir = $dir/newcerts 新证书的默认存储位置
certificate = $dir/cacert.pem CA的证书文件
serial = $dir/serial 当前的序列号,用于标识新证书
#crlnumber = $dir/crlnumber # the current crl number
# must be commented out to leave a V1 CRL
crl = $dir/crl.pem 当前的CRL文件
private_key = $dir/private/cakey.pem CA的私钥文件
x509_extensions = usr_cert 要添加到证书的扩展
[ policy_match ] 匹配策略,用于定义证书主题字段的匹配规则
countryName = match
stateOrProvinceName = match
organizationName = match
organizationalUnitName = optional
commonName = supplied
emailAddress = optional三种策略:
- match:要求申请填写的信息根CA设置的信息必须一致
- optional:可有可无,跟CA设置信息可不一致
- supplied:必须填写这项信息
建立私有CA
-
OpenCA:OpenCA开源组织使用Perl对OpenSSL进行二次开发而成的一套完善的PKI免费软件
-
openssl:相关包 openssl和openssl-libs
1、创建CA所需要文件
生成证书索引数据库文件
touch /etc/pki/CA/index.txt
指定第一个颁发证书的序列号
echo 01 > /etc/pki/CA/serial
2、生成CA私钥
cd /etc/pki/CA;(umask 066; openssl genrsa -out private/cakey.pem 2048)
3、生成CA自签名证书
openssl req -new -x509 -key /etc/pki/CA/private/cakey.pem -days 3650 -out /etc/pki/CA/cacert.pem
选项说明:
-new:生成新证书签署请求
-x509:专用于CA生成自签证书
-key:生成请求时用到的私钥文件
-days n:证书的有效期限
-out /PATH/TO/SOMECERTFILE: 证书的保存路径
CentOS7
从CentOS7将/etc/pki/CA目录内容复制到CentOS8,免去建立目录的步骤
[root@wenzi ~]#tree -d /etc/pki/CA
/etc/pki/CA
├── certs
├── crl
├── newcerts
└── private
[root@wenzi ~]#scp -r /etc/pki/CA root@192.168.28.10:/etc/pki/
CentOS8
生成CA私钥
[root@centos8 ~]#cd /etc/pki/CA;(umask 066; openssl genrsa -out private/cakey.pem 2048)
Generating RSA private key, 2048 bit long modulus (2 primes)
.......................................................................................................+++++
........................................................................................................................................................................................+++++
e is 65537 (0x010001)
[root@centos8 CA]#ll private/cakey.pem
-rw------- 1 root root 1675 Dec 31 04:42 private/cakey.pem
生成CA自签名证书
[root@centos8 CA]#openssl req -new -x509 -key /etc/pki/CA/private/cakey.pem -days 3650 -out /etc/pki/CA/cacert.pem
You are about to be asked to enter information that will be incorporated
into your certificate request.
What you are about to enter is what is called a Distinguished Name or a DN.
There are quite a few fields but you can leave some blank
For some fields there will be a default value,
If you enter '.', the field will be left blank.
-----
Country Name (2 letter code) [XX]:CN 国家
State or Province Name (full name) []:henan 省份
Locality Name (eg, city) [Default City]:zhengzhou 市名
Organization Name (eg, company) [Default Company Ltd]:wenzi 公司
Organizational Unit Name (eg, section) []:yunwei 部门
Common Name (eg, your name or your server's hostname) []:www.wenzi.com 使用证书的网站域名
Email Address []:999@qq.com 邮箱
查看生成的CA自签证书,建议将此文件传输到windows系统,后缀改为.crt
[root@centos8 CA]#openssl x509 -in cacert.pem -noout -text
Certificate:
Data:
Version: 3 (0x2)
Serial Number:
52:27:46:0b:52:67:5f:60:c8:bf:38:25:b9:c7:0e:66:d4:52:95:6a
Signature Algorithm: sha256WithRSAEncryption
Issuer: C = CN, ST = henan, L = zhengzhou, O = wenzi, OU = yunwei, CN = www.wenzi.com, emailAddress = 999@qq.com
Validity
Not Before: Dec 30 20:50:35 2023 GMT
Not After : Dec 27 20:50:35 2033 GMT
Subject: C = CN, ST = henan, L = zhengzhou, O = wenzi, OU = yunwei, CN = www.wenzi.com, emailAddress = 999@qq.com
Subject Public Key Info:
Public Key Algorithm: rsaEncryption
RSA Public-Key: (2048 bit)
Modulus:
00:bc:ac:9d:47:2c:4c:83:a6:2c:12:52:ba:f7:93:
6b:33:a6:e1:f0:9b:e7:4c:51:59:b0:95:db:b2:68:
ec:4a:2c:36:57:73:72:11:3c:21:6e:d3:fb:5a:0f:
a4:ca:05:21:fd:d5:a6:d7:4d:1f:72:91:15:3e:60:
da:cf:3a:e3:b2:c6:7b:c3:0e:4e:39:14:2c:94:f1:
ae:47:30:64:27:95:76:84:12:2e:a2:e0:60:2f:7c:
c9:83:3b:c9:d9:6a:4d:1f:78:a6:41:ea:ac:12:85:
d3:9a:43:f9:24:c7:66:f0:09:c7:01:91:ee:6a:ec:
1d:a4:7f:72:19:43:ca:91:78:ac:23:9e:6b:43:84:
5e:40:09:61:5e:b6:32:f2:19:9d:c6:b7:00:f8:d0:
00:fd:66:f3:f7:a2:a3:5a:81:71:1a:b0:2a:c2:e7:
42:f8:a9:b7:54:f6:1e:da:47:87:4a:6a:29:26:7f:
16:20:b9:e9:76:a7:92:b2:19:3a:4e:de:b0:ab:63:
12:6e:7a:f3:64:e5:91:93:1f:35:09:0b:b6:79:dd:
a3:27:8d:7a:2d:9a:3b:7f:a1:b1:d3:df:a2:0a:81:
60:0e:ec:69:9b:1a:a7:32:19:71:fa:9a:f1:93:91:
e7:48:8f:be:2a:85:a4:6d:f7:90:92:92:d7:08:06:
94:65
Exponent: 65537 (0x10001)
X509v3 extensions:
X509v3 Subject Key Identifier:
5D:EE:41:48:03:D1:0D:A6:85:DA:BC:05:29:AF:81:BF:82:67:11:05
X509v3 Authority Key Identifier:
keyid:5D:EE:41:48:03:D1:0D:A6:85:DA:BC:05:29:AF:81:BF:82:67:11:05
X509v3 Basic Constraints: critical
CA:TRUE
Signature Algorithm: sha256WithRSAEncryption
5d:65:b2:c9:2d:8c:89:79:85:46:12:0a:17:12:87:21:3f:e1:
f3:bb:f5:c4:82:24:b9:43:74:c2:d6:52:5c:80:65:75:9d:3c:
45:fa:c4:88:5f:43:6d:1d:0e:3d:84:a0:e7:ab:60:35:f6:88:
c0:ac:8e:c7:ca:70:f7:71:09:ea:03:6f:3a:c7:2f:4e:bd:3b:
35:4c:ca:4e:ce:17:90:67:5a:8f:4b:8a:ef:3d:ce:3a:bc:9c:
ee:2a:cf:7d:3a:f0:36:9b:f7:19:71:73:f5:e7:4d:30:50:8c:
12:f8:f1:92:02:91:f7:3b:30:ce:07:4e:09:b9:f6:0f:72:92:
4d:76:c4:11:6c:a9:e3:56:ca:2f:fc:9e:05:b5:dd:e4:86:45:
6a:dd:c4:77:70:3e:bc:4a:5f:55:6e:eb:74:7d:46:4f:00:c4:
db:23:bc:d3:71:74:ef:e0:e4:06:27:8a:29:b6:e0:62:b3:04:
7e:fe:51:71:91:04:52:f4:61:12:55:37:48:8e:63:6a:50:05:
a3:e2:15:8f:cf:e5:d1:5b:d1:9c:bc:33:b1:88:6e:1b:21:89:
5b:3c:3f:34:0a:a3:b2:95:29:cf:8b:b6:fa:b9:47:28:17:56:
ff:95:28:20:68:fe:94:c6:49:79:f7:8e:16:03:46:f0:68:bd:
cd:a6:73:3c 
申请证书并颁发证书
1、为需要使用证书的主机生成生成私钥
(umask 066; openssl genrsa -out ? /data/test.key 2048)
2、为需要使用证书的主机生成证书申请文件
openssl req -new -key /data/test.key -out /data/test.csr
3、在CA签署证书并将证书颁发给请求者
可以将客户端生成的申请文件发送至CA,生成证书后再把证书传送至客户端
openssl ca -in /data/test.csr ?-out ? /etc/pki/CA/certs/test.crt -days 100
注意:默认要求 国家,省,公司名称三项必须和CA一致
4、查看证书中的信息
openssl x509 -in /PATH/FROM/CERT_FILE -noout ? -text|issuer|subject|serial|dates
查看指定编号的证书状态
openssl ca -status SERIAL
用户生成自己的私钥,私钥应该存放至各应用相应目录下
[root@wenzi ~]#(umask 066;openssl genrsa -out /data/test.key 2048)
Generating RSA private key, 2048 bit long modulus (2 primes)
.........................+++++
.....+++++
e is 65537 (0x010001)
生成证书申请文件,其中国家代码、省名、公司名必须和CA中一致
[root@wenzi ~]#openssl req -new -key /data/test.key -out /data/test.csr
You are about to be asked to enter information that will be incorporated
into your certificate request.
What you are about to enter is what is called a Distinguished Name or a DN.
There are quite a few fields but you can leave some blank
For some fields there will be a default value,
If you enter '.', the field will be left blank.
-----
Country Name (2 letter code) [XX]:CN
State or Province Name (full name) []:henan
Locality Name (eg, city) [Default City]:luoyang
Organization Name (eg, company) [Default Company Ltd]:wenzi
Organizational Unit Name (eg, section) []:kaifa
Common Name (eg, your name or your server's hostname) []:www.wenzi.org
Email Address []:666@163.com
Please enter the following 'extra' attributes
to be sent with your certificate request
A challenge password []:
An optional company name []:
将客户端证书申请文件上传至CA
[root@wenzi ~]#rsync -av /data/test.csr root@192.168.28.10:/data/
root@192.168.28.10's password:
sending incremental file list
test.csr
sent 1,135 bytes received 35 bytes 780.00 bytes/sec
total size is 1,041 speedup is 0.89
在CA上颁发证书
提前创建这两个必须存在的文件,不然会报错,提示找不到文件
[root@centos8 CA]#touch /etc/pki/CA/index.txt;touch /etc/pki/CA/serial
指定证书颁发起始序号
[root@centos8 CA]#echo 01 > /etc/pki/CA/serial
颁发证书
[root@centos8 CA]#openssl ca -in /data/test.csr -out /etc/pki/CA/certs/test.crt -days 100
Using configuration from /etc/pki/tls/openssl.cnf
Check that the request matches the signature
Signature ok
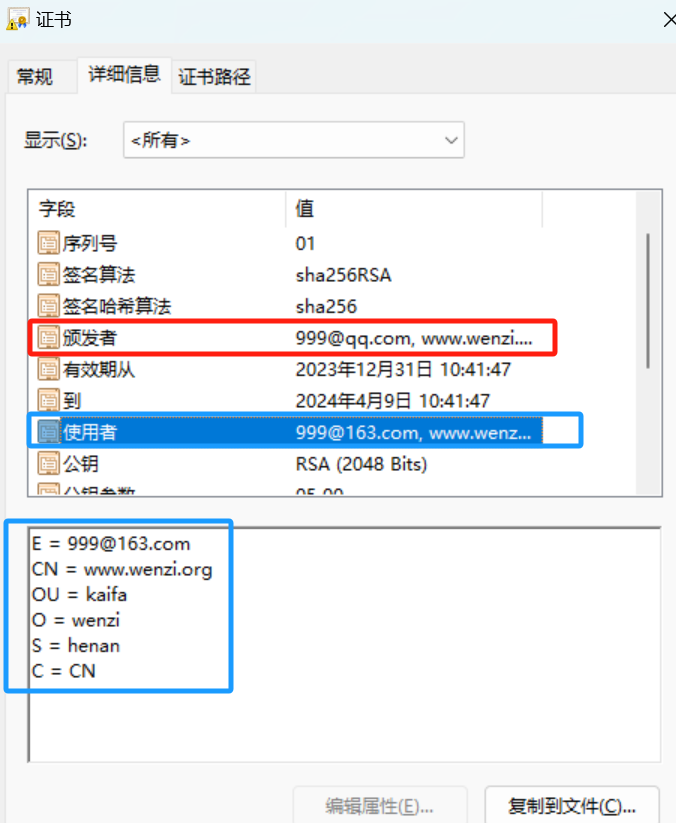
Certificate Details:
Serial Number: 1 (0x1)
Validity
Not Before: Dec 31 02:41:47 2023 GMT
Not After : Apr 9 02:41:47 2024 GMT
Subject:
countryName = CN
stateOrProvinceName = henan
organizationName = wenzi
organizationalUnitName = kaifa
commonName = www.wenzi.org
emailAddress = 999@163.com
X509v3 extensions:
X509v3 Basic Constraints:
CA:FALSE
Netscape Comment:
OpenSSL Generated Certificate
X509v3 Subject Key Identifier:
35:72:9F:AE:C3:0D:1C:CE:43:34:84:F1:83:88:59:0E:DE:5E:B5:7C
X509v3 Authority Key Identifier:
keyid:5D:EE:41:48:03:D1:0D:A6:85:DA:BC:05:29:AF:81:BF:82:67:11:05
Certificate is to be certified until Apr 9 02:41:47 2024 GMT (100 days)
Sign the certificate? [y/n]:y
1 out of 1 certificate requests certified, commit? [y/n]y
Write out database with 1 new entries
Data Base Updated
查看当前CA目录下文件
[root@centos8 CA]#tree /etc/pki/CA/
/etc/pki/CA/
├── cacert.pem
├── certs
│?? └── test.crt
├── crl
├── index.txt
├── index.txt.attr
├── index.txt.old
├── newcerts
│?? └── 01.pem
├── private
│?? └── cakey.pem
├── serial
└── serial.old
查看下一个颁发证书的序号
[root@centos8 CA]#cat /etc/pki/CA/serial
02
查看颁发记录。 有效期 序号 信息
[root@centos8 CA]#cat /etc/pki/CA/index.txt
V 240409024147Z 01 unknown /C=CN/ST=henan/O=wenzi/OU=kaifa/CN=www.wenzi.org/emailAddress=999@163.com
查看证书信息
[root@centos8 CA]#openssl x509 -in /etc/pki/CA/certs/test.crt -noout -text
Certificate:
Data:
Version: 3 (0x2)
Serial Number: 1 (0x1)
Signature Algorithm: sha256WithRSAEncryption
Issuer: C = CN, ST = henan, L = zhengzhou, O = wenzi, OU = yunwei, CN = www.wenzi.com, emailAddress = 999@qq.com
Validity
Not Before: Dec 31 02:41:47 2023 GMT
Not After : Apr 9 02:41:47 2024 GMT
Subject: C = CN, ST = henan, O = wenzi, OU = kaifa, CN = www.wenzi.org, emailAddress = 999@163.com
Subject Public Key Info:
Public Key Algorithm: rsaEncryption
RSA Public-Key: (2048 bit)
Modulus:
00:f2:cf:6e:74:80:8f:e2:19:09:19:20:8f:3d:5b:
d6:3c:96:99:30:d7:07:9e:a0:5a:7c:79:a2:9a:d6:
63:cb:a9:77:f1:10:d5:5f:69:55:53:90:8a:13:66:
f9:77:7b:69:2c:0d:fe:fe:56:78:fa:fe:2e:43:c7:
f9:88:b9:a2:42:d2:47:4b:73:e0:5d:da:c7:66:ce:
fe:3f:e8:9f:fe:93:39:46:a4:7a:05:95:74:ef:fb:
91:7d:8f:63:d8:ed:d4:6a:71:77:8d:b0:f8:37:38:
a2:94:cf:69:f7:02:73:8e:ba:b7:c8:7f:c6:5f:4f:
71:2d:d3:b1:9f:92:03:66:79:26:cb:1e:44:67:11:
29:35:17:bb:a9:c7:98:0f:8c:b9:2b:89:13:9f:32:
27:69:e7:15:3e:5c:05:6c:dc:0d:e9:81:24:ad:83:
2c:71:da:f4:42:04:6b:68:13:2b:ce:19:aa:a8:63:
c7:3a:ac:4f:6e:4e:4b:12:69:a9:2c:96:c9:d8:df:
eb:7a:17:82:3f:d4:82:5b:0c:7a:7b:01:89:3b:ac:
6c:51:f7:f7:c0:3e:46:49:b2:a7:0d:65:df:ac:d9:
ec:e6:21:77:8b:56:00:f7:35:b7:01:b3:76:07:63:
bc:1e:28:84:a6:99:7e:91:21:17:b2:cd:cc:ab:40:
1c:9d
Exponent: 65537 (0x10001)
X509v3 extensions:
X509v3 Basic Constraints:
CA:FALSE
Netscape Comment:
OpenSSL Generated Certificate
X509v3 Subject Key Identifier:
35:72:9F:AE:C3:0D:1C:CE:43:34:84:F1:83:88:59:0E:DE:5E:B5:7C
X509v3 Authority Key Identifier:
keyid:5D:EE:41:48:03:D1:0D:A6:85:DA:BC:05:29:AF:81:BF:82:67:11:05
Signature Algorithm: sha256WithRSAEncryption
91:8a:ba:32:4a:c4:36:0e:83:bd:e2:95:48:52:02:ce:d6:78:
5a:6b:73:ea:73:59:c7:68:f8:3e:fe:f7:52:2f:0a:3a:7b:8d:
4c:ac:bf:d8:d4:46:73:c3:34:25:3e:51:cd:b2:85:a5:a1:1b:
03:86:92:58:dd:f9:07:d6:72:ba:23:18:79:32:42:71:7d:c2:
ce:f9:0f:00:99:36:00:45:f5:c6:e3:4f:93:aa:e4:5c:aa:ad:
94:89:73:ca:09:e0:9d:64:41:7a:d6:60:da:35:c8:07:d8:f7:
7b:6c:46:41:3c:4c:ee:af:9a:82:b0:1e:25:e8:09:7f:88:e8:
55:7e:de:4e:23:3d:9c:21:ad:1b:e7:f9:7b:df:16:13:64:bc:
5f:fb:95:4f:79:15:cd:01:7b:e9:30:fa:4d:7d:0d:97:fe:9e:
06:40:c6:d0:e7:1f:ec:8a:4a:fd:ee:be:b3:50:8a:7a:9c:4d:
86:b6:33:81:75:af:3e:88:a2:d4:9b:6c:12:73:8a:1e:c5:46:
d7:7e:41:dc:ee:c1:15:29:74:f4:59:63:09:e9:9b:f3:53:4f:
b5:e9:2d:a7:cc:cd:82:17:a0:1e:54:a1:36:a7:f6:a4:3e:eb:
f0:14:de:be:41:e0:cc:78:36:d5:7a:ba:bb:04:8b:84:fb:3b:
40:53:81:dd
将证书发送至客户端,完成
[root@centos8 CA]#rsync -a certs/test.crt root@192.168.28.20:/data/将客户端收到的证书传递至windows系统查看

吊销证书
在客户端获取要吊销的证书的serial
openssl x509 -in /PATH/FROM/CERT_FILE ? -noout ? -serial ?-subject
在CA上,根据客户提交的serial与subject信息,对比检验是否与index.txt文件中的信息一致,吊销证书
openssl ca -revoke /etc/pki/CA/newcerts/SERIAL.pem
指定第一个吊销证书的编号,注意:第一次更新证书吊销列表前,才需要执行
echo 01 > /etc/pki/CA/crlnumber
更新证书吊销列表
openssl ca -gencrl -out /etc/pki/CA/crl.pem
查看crl文件
openssl crl -in /etc/pki/CA/crl.pem -noout -text
本文来自互联网用户投稿,该文观点仅代表作者本人,不代表本站立场。本站仅提供信息存储空间服务,不拥有所有权,不承担相关法律责任。 如若内容造成侵权/违法违规/事实不符,请联系我的编程经验分享网邮箱:chenni525@qq.com进行投诉反馈,一经查实,立即删除!