【新华三】IPsec VPN 实验配置(地址固定)
【新华三】IPsec VPN 实验配置(地址固定)

注意
因为本篇文章,就是IPsec的实验配置的话,它们两端的IP地址是固定的
那么就用第一阶段的主模式(Main Mode)
和第二阶段的快速模式(Quick Mode)就好啦
后面会有一个地址不固定的情况下,这个就需要用到野蛮模式的,也就是第一阶段会更改模式啦
实验需求
R1为企业总部网关,R3为企业分部网关,分部与总部通过公网建立通信。分部子网为202.101.23.0/24,总部子网为202.101.12.0/24。
企业希望对分部子网与总部子网之间相互访问的流量进行安全保护。分部与总部通过公网建立通信,可以在分部网关与总部网关之间建立一个IPSec隧道来实施安全保护。

配置思路
-
基础配置, 配置接口的IP地址和到对端的静态路由,保证两端路由可达。
-
第一阶段 IKE SA
① 配置IKE安全提议,定义IKE保护数据流方法
② 配置IKE对等体,定义对等体间IKE协商时的属性
③ 配置IKE profile,把前面两个关联在一起 -
第二阶段 IPsec SA
① 配置ACL,以定义需要IPSec保护的数据流
② 配置IPSec安全提议,定义IPSec的保护方法
③ 配置安全策略,并引用ACL、IPSec安全提议和IKE对等体,确定对何种数据流采取何种保护方法 -
在接口上应用安全策略组,使接口具有IPSec的保护功能
IPsec VPN 本质:阶段一保护阶段二 阶段二保护数据
配置命令
拓扑

R1
基础配置
配置R1的基础配置,再用默认路由实现公网可达
[H3C]sysn R1
[R1]undo info-center enable
[R1]int g0/0
[R1-GigabitEthernet0/0]ip address 202.101.12.1 24
[R1-GigabitEthernet0/0]qu
[R1]int g0/1
[R1-GigabitEthernet0/1]ip address 192.168.10.254 24
[R1-GigabitEthernet0/1]qu
[R1]ip route-static 0.0.0.0 0.0.0.0 202.101.12.2 ##配置默认路由指向ISP_R2运营商,实现公网可达
配置第一阶段 IKE SA
协商出IKE SA ,对第二阶段IPsecSA的协商过程做保护
## 配置R1的IKE安全提议,名字为 1
[R1]ike proposal 1 ## ike的提案(需要用什么)
[R1-ike-proposal-1]encryption-algorithm 3des-cbc ## 用3des加密IKE
[R1-ike-proposal-1]authentication-algorithm sha256 ## IKE用sha256 认证
[R1-ike-proposal-1]dh group5 ## IKE 处于group5
[R1-ike-proposal-1]qu
## 采用PSK,配置与对等体的信息,钥匙串名字为 1
[R1]ike keychain 1
[R1-ike-keychain-1]pre-shared-key address 202.101.23.3 key simple 520
[R1-ike-keychain-1]qu
## 将上面两个整合在一起,匹配对等体,profile 名字为 1
[R1]ike profile 1
[R1-ike-profile-1]keychain 1 ## 指定引用的IKE keychain为keychain 1
[R1-ike-profile-1]proposal 1 ## 指定引用的IKE proposal为proposal 1
[R1-ike-profile-1]match remote identity address 202.101.23.3 ## 指定对端的IP地址
[R1-ike-profile-1]qu
配置第二阶段 IPsec SA
在阶段1建立的IKE SA的保护下完成IPSec SA的协商
## IPSec SA的创建,转换集,名字为 myset
[R1]ipsec transform-set myset
[R1-ipsec-transform-set-myset]encapsulation-mode tunnel ## 流量以隧道的方式传输
[R1-ipsec-transform-set-myset]esp encryption-algorithm 3des-cbc ## 数据加密算法
[R1-ipsec-transform-set-myset]esp authentication-algorithm sha256 ## 身份认证算法
[R1-ipsec-transform-set-myset]qu
## 配置高级ACL,匹配子网192.168.10.0/24去子网192.168.20.0/24的数据
[R1]acl advanced 3000
[R1-acl-ipv4-adv-3000]rule permit ip source 192.168.10.0 0.0.0.255 destination 192.168.20.0 0.0.0.255
[R1-acl-ipv4-adv-3000]qu
## IPsec 和 IKE的安全策略的关联,名字为 mypolicy 优先级为 1
[R1]ipsec policy mypolicy 1 isakmp
[R1-ipsec-policy-isakmp-mypolicy-1]ike-profile 1 ## 关联IKE profile 1
[R1-ipsec-policy-isakmp-mypolicy-1]security acl 3000 ## 匹配需要保护的数据流
[R1-ipsec-policy-isakmp-mypolicy-1]transform-set myset ## 关联IPsec 转换集
[R1-ipsec-policy-isakmp-mypolicy-1]remote-address 202.101.23.3 ## 远端的IP地址
[R1-ipsec-policy-isakmp-mypolicy-1]qu
## 出接口上调用安全策略组
[R1]int g0/0
[R1-GigabitEthernet1/0]ipsec apply policy mypolicy
[R1-GigabitEthernet1/0]qu
ISP_R2
基础配置
[H3C]sysn ISP_R2
[ISP_R2]interface GigabitEthernet1/0
[ISP_R2-GigabitEthernet1/0]ip address 202.101.12.100 255.255.255.0
[ISP_R2-GigabitEthernet1/0]qu
[ISP_R2]int g2/0
[ISP_R2-GigabitEthernet2/0]ip address 202.101.23.100 255.255.255.0
[ISP_R2-GigabitEthernet2/0]qu
R3
基础配置
配置R3的基础配置,再用默认路由实现公网可达
[H3C]sysn R3
[R3]int g0/0
[R3-GigabitEthernet0/0]ip address 202.101.23.3 24
[R3-GigabitEthernet0/0]qu
[R3]int g0/1
[R3-GigabitEthernet0/1]ip address 192.168.20.254 24
[R3-GigabitEthernet0/1]qu
[R3]ip route-static 0.0.0.0 0.0.0.0 202.101.23.2 ##配置默认路由指向ISP_R2运营商,实现公网可达
配置第一阶段 IKE SA
协商出IKE SA ,对第二阶段IPsecSA的协商过程做保护
[R3]ike proposal 1
[R3-ike-proposal-1]encryption-algorithm 3des-cbc
[R3-ike-proposal-1]authentication-algorithm sha256
[R3-ike-proposal-1]dh group5
[R3-ike-proposal-1]qu
[R3]ike keychain 1
[R3-ike-keychain-1]pre-shared-key address 202.101.12.1 key simple 520
[R3-ike-keychain-1]qu
[R3]ike profile 1
[R3-ike-profile-1]keychain 1
[R3-ike-profile-1]proposal 1
[R3-ike-profile-1]match remote identity address 202.101.12.1
[R3-ike-profile-1]qu
配置第二阶段 IPsec SA
在阶段1建立的IKE SA的保护下完成IPSec SA的协商
[R3]ipsec transform-set myset
[R3-ipsec-transform-set-myset]encapsulation-mode tunnel
[R3-ipsec-transform-set-myset]esp encryption-algorithm 3des-cbc
[R3-ipsec-transform-set-myset]esp authentication-algorithm sha256
[R3-ipsec-transform-set-myset]qu
[R3]acl advanced 3000
[R3-acl-ipv4-adv-3000]rule permit ip source 192.168.20.0 0.0.0.255 destination 192.168.10.0 0.0.0.255
[R3-acl-ipv4-adv-3000]qu
[R3]ipsec policy mypolicy 1 isakmp
[R3-ipsec-policy-isakmp-mypolicy-1]ike-profile 1
[R3-ipsec-policy-isakmp-mypolicy-1]security acl 3000
[R3-ipsec-policy-isakmp-mypolicy-1]transform-set myset
[R3-ipsec-policy-isakmp-mypolicy-1]remote-address 202.101.12.1
[R3-ipsec-policy-isakmp-mypolicy-1]qu
[R3]int g0/0
[R3-GigabitEthernet1/0]ipsec apply policy mypolicy
[R3-GigabitEthernet1/0]qu
PC
PC1

PC2

检查
抓包查看(华三的IPsec VPN 是自己触发的,可以不用手动去Ping呀)

建立成功
里面主模式交换六个报文,成功协商IKE SA
而快速模式的三个报文,就成功的协商IPsec SA
这两个出来就成功建立了 IPsec VPN,对流量实施了加密啦~

查看命令
查看IKE SA的基本信息
[R1]display ike sa

查看IPsec SA的基本信息
[R1]display ipsec sa

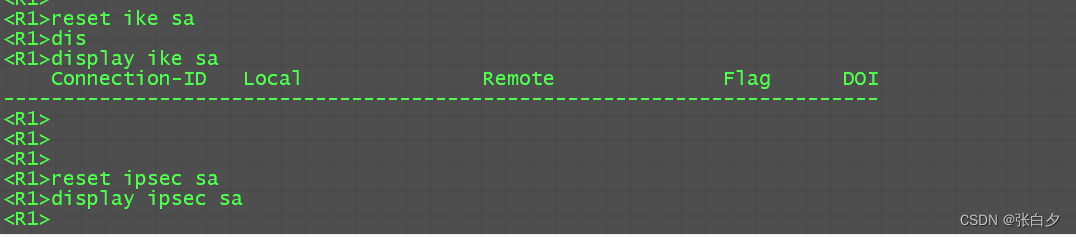
清除IKE / IPsec SA命令
在IPsec VPN 建立完成后,我们想修改一些东西的时候,需要把SA清除干净,这个时候才会去重新建立IPsec VPN,我们所添加的东西才会生效
可以看到,当我去清除掉IKE SA的时候,再查看已经被清除掉了,还有IPsec SA,说明清除成功啦
reset ike sa
reset ipsec sa
配置文档
R1
sys
sysn R1
int g0/0
ip address 202.101.12.1 24
qu
int g0/1
ip address 192.168.10.254 24
qu
ip route-static 0.0.0.0 0.0.0.0 202.101.12.2
ike proposal 1
encryption-algorithm 3des-cbc
authentication-algorithm sha256
dh group5
qu
ike keychain 1
pre-shared-key address 202.101.23.3 key simple 520
qu
ike profile 1
keychain 1
proposal 1
match remote identity address 202.101.23.3
qu
ipsec transform-set myset
encapsulation-mode tunnel
esp encryption-algorithm 3des-cbc
esp authentication-algorithm sha256
qu
acl advanced 3000
rule permit ip source 192.168.10.0 0.0.0.255 destination 192.168.20.0 0.0.0.255
qu
ipsec policy mypolicy 1 isakmp
ike-profile 1
security acl 3000
transform-set myset
remote-address 202.101.23.3
qu
int g0/0
ipsec apply policy mypolicy
qu
ISP_R2
sys
sysn ISP_R2
int g0/0
ip address 202.101.12.2 24
qu
int g0/1
ip address 202.101.23.2 24
qu
R3
sys
sysn R3
int g0/0
ip address 202.101.23.3 24
qu
int g0/1
ip address 192.168.20.254 24
qu
ip route-static 0.0.0.0 0.0.0.0 202.101.23.2
ike proposal 1
encryption-algorithm 3des-cbc
authentication-algorithm sha256
dh group5
qu
ike keychain 1
pre-shared-key address 202.101.12.1 key simple 520
qu
ike profile 1
keychain 1
proposal 1
match remote identity address 202.101.12.1
qu
ipsec transform-set myset
encapsulation-mode tunnel
esp encryption-algorithm 3des-cbc
esp authentication-algorithm sha256
qu
acl advanced 3000
rule permit ip source 192.168.20.0 0.0.0.255 destination 192.168.10.0 0.0.0.255
qu
ipsec policy mypolicy 1 isakmp
ike-profile 1
security acl 3000
transform-set myset
remote-address 202.101.12.1
qu
int g0/0
ipsec apply policy mypolicy
qu
本文来自互联网用户投稿,该文观点仅代表作者本人,不代表本站立场。本站仅提供信息存储空间服务,不拥有所有权,不承担相关法律责任。 如若内容造成侵权/违法违规/事实不符,请联系我的编程经验分享网邮箱:chenni525@qq.com进行投诉反馈,一经查实,立即删除!
- Python教程
- 深入理解 MySQL 中的 HAVING 关键字和聚合函数
- Qt之QChar编码(1)
- MyBatis入门基础篇
- 用Python脚本实现FFmpeg批量转换
- 多线程的概念
- 27 UVM queue
- props与TypeScript
- Caused by: java.net.ConnectException: 拒绝连接: hadoop104/192.168.124.130:4142
- 【学习笔记】环论
- vue3 实现主题色以及修改主题色
- 最后一次纪念在泰山OFFICE的日子,明年开源量子OFFICE
- 试题二(15分)和试题三(15分) (软件设计师笔记)
- 鸿蒙会不会像10几年前安卓一样,红极一时
- 华为OD机试真题-多段线数据压缩-2023年OD统一考试(C卷)