网安入门07-Sql注入(二次注入)
发布时间:2023年12月29日
渗透测试简介
黑盒测试:看不到后端代码,只能依靠前端页面显示来判断是否有注入点
白盒测试:可以看到后端代码,进行代码审计分析注入点
白+黑:既可以看到后端代码,也可以看到前端页面的回显
实战中黑盒占80%,客户提供源码白盒占5%,通过漏洞挖出源代码白+黑15%
二次注入
Less24

试图进行常规注入
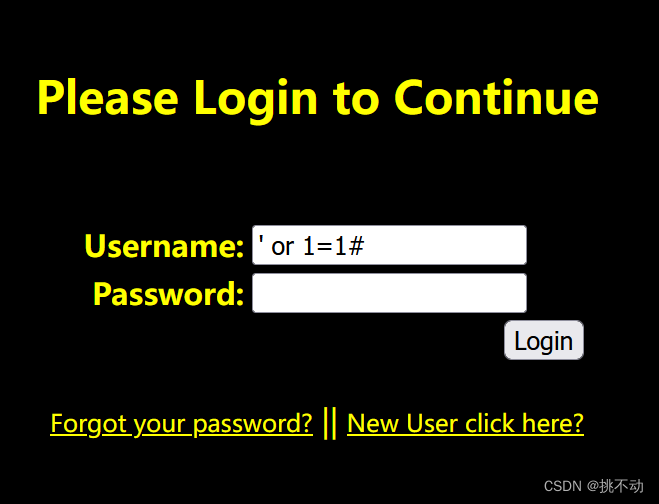
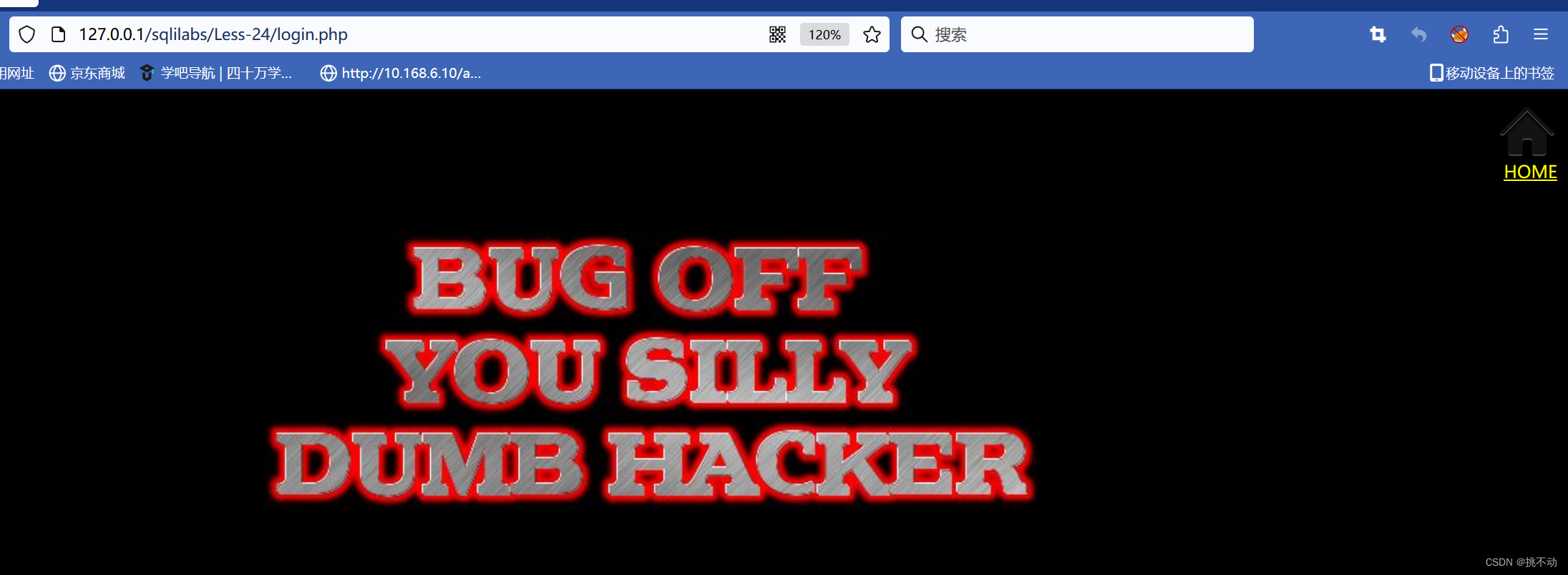
触发过滤机制,页面回显如下(滚开,你个愚蠢的黑客)
点击忘记密码:
注册账号页面,先试一下admin用户
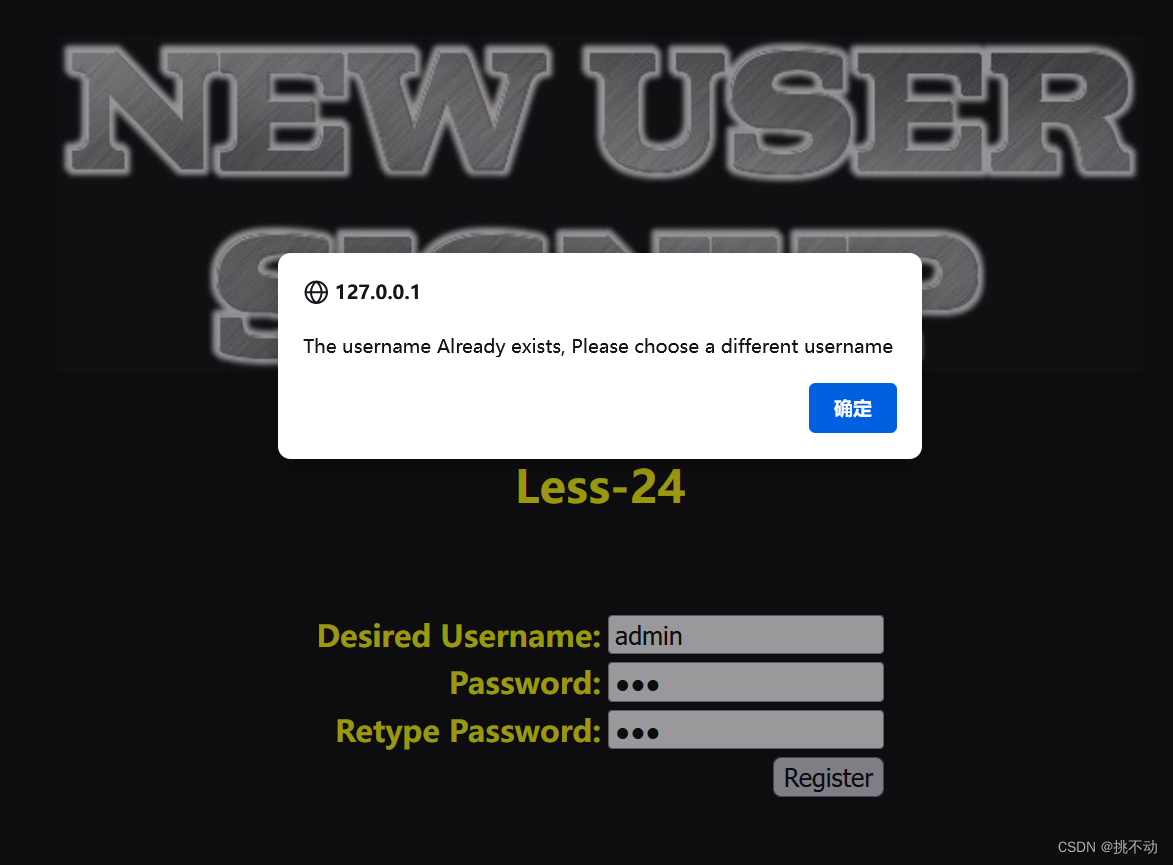
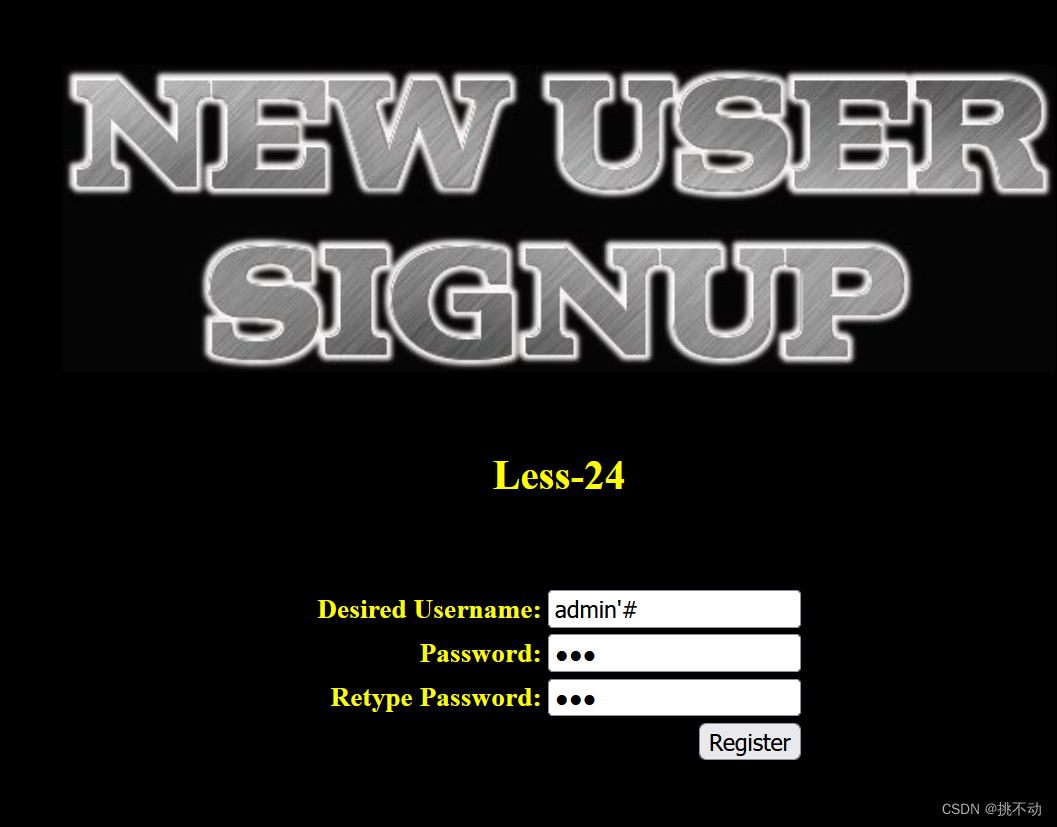
不让我注册!那我先注册一个admin‘#用户,密码123
然后登录admin’#
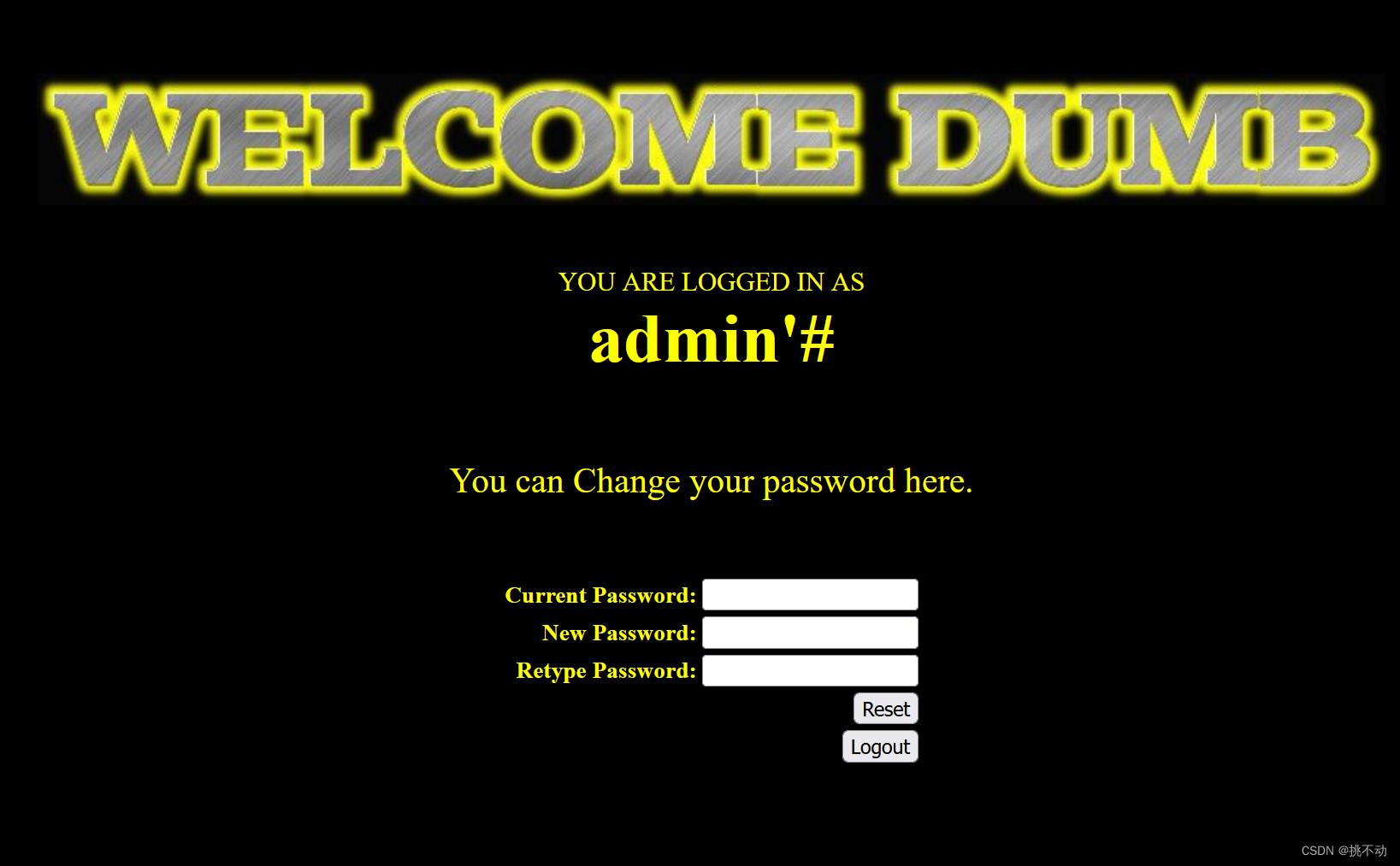
改一手密码
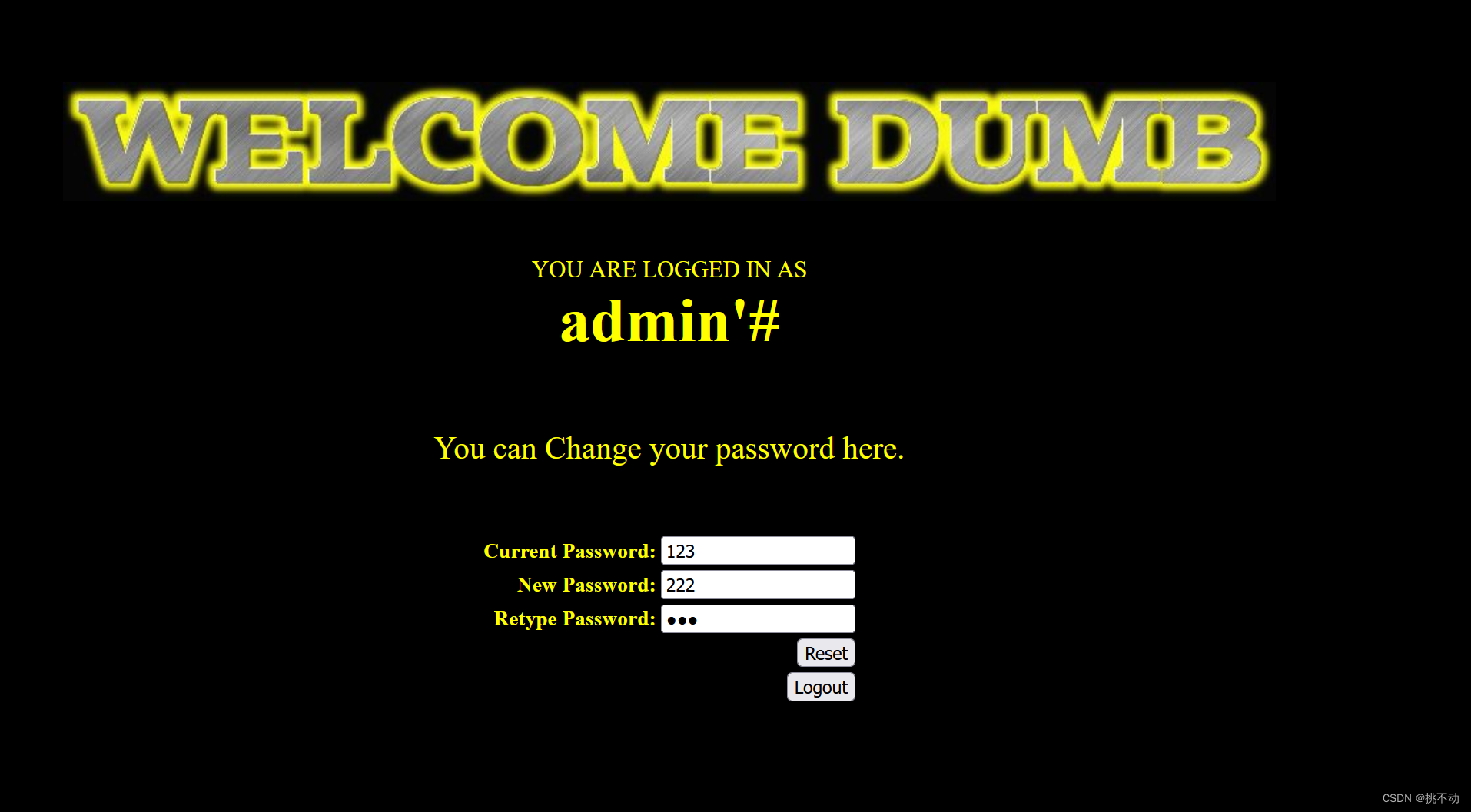
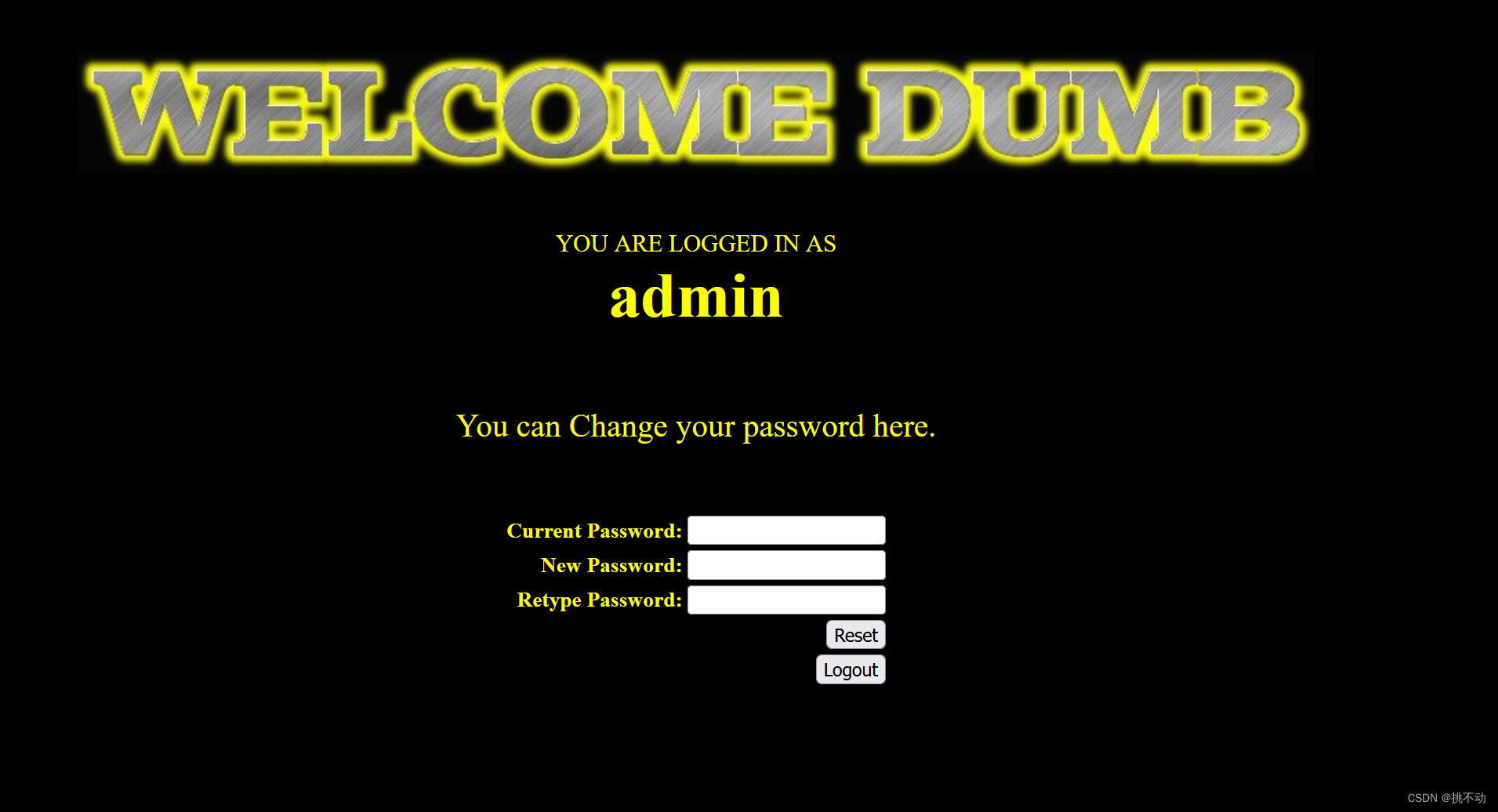
最后再用admin账号和刚改好的密码222,就登录成功啦!
原理
查看源代码,最重要的三个页面:登录,注册,改密码
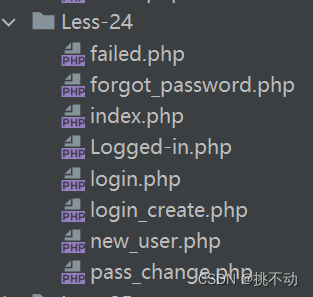
其中login.php是登录页面,login_crearte.php是注册页面,pass_change.php是改密码页面
login.php:
<html>
<head>
</head>
<body bgcolor="#000000">
<font size="3" color="#FFFF00">
<div align="right">
<a style="font-size:.8em;color:#FFFF00" href='index.php'><img src="../images/Home.png" height='45'; width='45'></br>HOME</a>
</div>
<?PHP
session_start();
//including the Mysql connect parameters.
include("../sql-connections/sql-connect.php");
function sqllogin(){
$username = mysql_real_escape_string($_POST["login_user"]);#' " \
$password = mysql_real_escape_string($_POST["login_password"]);
$sql = "SELECT * FROM users WHERE username='$username' and password='$password'";
//$sql = "SELECT COUNT(*) FROM users WHERE username='$username' and password='$password'";
$res = mysql_query($sql) or die('You tried to be real smart, Try harder!!!! :( ');
$row = mysql_fetch_row($res);
//print_r($row) ;
if ($row[1]) {
return $row[1];
} else {
return 0;
}
}
$login = sqllogin();
if (!$login== 0)
{
$_SESSION["username"] = $login;
setcookie("Auth", 1, time()+3600); /* expire in 15 Minutes */
header('Location: logged-in.php');
}
else
{
?>
<tr><td colspan="2" style="text-align:center;"><br/><p style="color:#FF0000;">
<center>
<img src="../images/slap1.jpg">
</center>
</p></td></tr>
<?PHP
}
?>
</body>
</html>
login_crearte.php:
<html>
<head>
</head>
<body bgcolor="#000000">
<?PHP
session_start();
?>
<div align="right">
<a style="font-size:.8em;color:#FFFF00" href='index.php'><img src="../images/Home.png" height='45'; width='45'></br>HOME</a>
</div>
<?php
//including the Mysql connect parameters.
include("../sql-connections/sql-connect.php");
if (isset($_POST['submit']))
{
# Validating the user input........
//$username= $_POST['username'] ;
$username= mysql_escape_string($_POST['username']) ;
$pass= mysql_escape_string($_POST['password']);
$re_pass= mysql_escape_string($_POST['re_password']);
echo "<font size='3' color='#FFFF00'>";
$sql = "select count(*) from users where username='$username'";
$res = mysql_query($sql) or die('You tried to be smart, Try harder!!!! :( ');
$row = mysql_fetch_row($res);
//print_r($row);
if (!$row[0]== 0)
{
?>
<script>alert("The username Already exists, Please choose a different username ")</script>;
<?php
header('refresh:1, url=new_user.php');
}
else
{
if ($pass==$re_pass)
{
# Building up the query........
$sql = "insert into users ( username, password) values(\"$username\", \"$pass\")";
mysql_query($sql) or die('Error Creating your user account, : '.mysql_error());
echo "</br>";
echo "<center><img src=../images/Less-24-user-created.jpg><font size='3' color='#FFFF00'>";
//echo "<h1>User Created Successfully</h1>";
echo "</br>";
echo "</br>";
echo "</br>";
echo "</br>Redirecting you to login page in 5 sec................";
echo "<font size='2'>";
echo "</br>If it does not redirect, click the home button on top right</center>";
header('refresh:5, url=index.txt');
}
else
{
?>
<script>alert('Please make sure that password field and retype password match correctly')</script>
<?php
header('refresh:1, url=new_user.php');
}
}
}
?>
</body>
</html>
pass_change.php:
<html>
<head>
</head>
<body bgcolor="#000000">
<?PHP
session_start();
if (!isset($_COOKIE["Auth"]))
{
if (!isset($_SESSION["username"]))
{
header('Location: index.txt');
}
header('Location: index.txt');
}
?>
<div align="right">
<a style="font-size:.8em;color:#FFFF00" href='index.php'><img src="../images/Home.png" height='45'; width='45'></br>HOME</a>
</div>
<?php
//including the Mysql connect parameters.
include("../sql-connections/sql-connect.php");
if (isset($_POST['submit']))
{
# Validating the user input........
$username= $_SESSION["username"]; #admin'#
$curr_pass= mysql_real_escape_string($_POST['current_password']);
$pass= mysql_real_escape_string($_POST['password']);
$re_pass= mysql_real_escape_string($_POST['re_password']);
if($pass==$re_pass)
{
$sql = "UPDATE users SET PASSWORD='$pass' where username='$username' and password='$curr_pass' ";
$res = mysql_query($sql) or die('You tried to be smart, Try harder!!!! :( ');
$row = mysql_affected_rows();
echo '<font size="3" color="#FFFF00">';
echo '<center>';
if($row==1)
{
echo "Password successfully updated";
}
else
{
header('Location: failed.php');
//echo 'You tried to be smart, Try harder!!!! :( ';
}
}
else
{
echo '<font size="5" color="#FFFF00"><center>';
echo "Make sure New Password and Retype Password fields have same value";
header('refresh:2, url=index.txt');
}
}
?>
<?php
if(isset($_POST['submit1']))
{
session_destroy();
setcookie('Auth', 1 , time()-3600);
header ('Location: index.txt');
}
?>
</center>
</body>
</html>
前面两个页面都有mysql_real_escape_string()的严格的过滤,无法进行注入
PHP mysqli_real_escape_string() 函数-菜鸟教程
突破点就在登录成功之后的这个地方
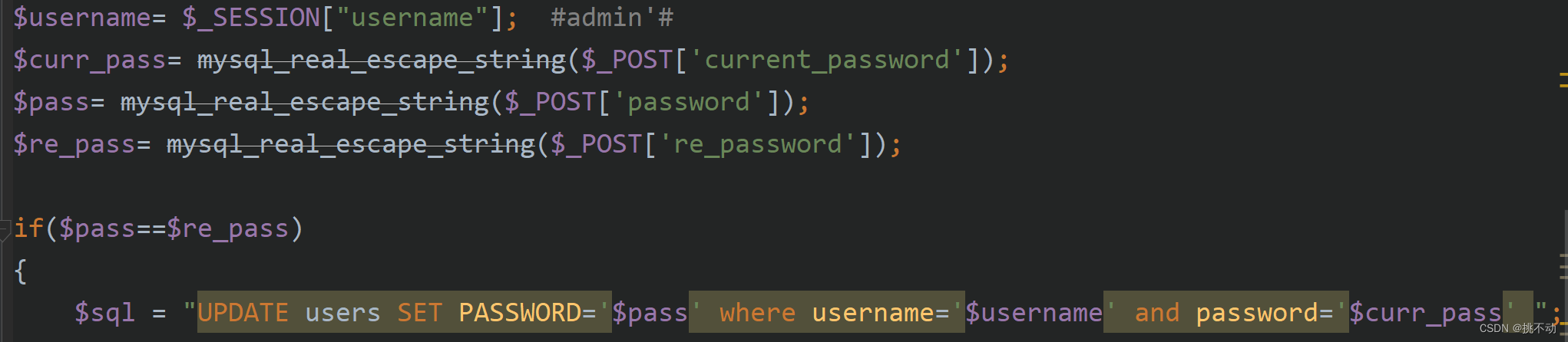
由于过滤只在进行sql查询的地方触发,过滤后还是以没被过滤的形式存入数据库的,在重置密码时就可以进行二次注入,admin’#进行闭合,注释了后面的语句,这样我们就成功改掉了admin的密码,得到所有权限了
文章来源:https://blog.csdn.net/m0_61499194/article/details/135197393
本文来自互联网用户投稿,该文观点仅代表作者本人,不代表本站立场。本站仅提供信息存储空间服务,不拥有所有权,不承担相关法律责任。 如若内容造成侵权/违法违规/事实不符,请联系我的编程经验分享网邮箱:chenni525@qq.com进行投诉反馈,一经查实,立即删除!
本文来自互联网用户投稿,该文观点仅代表作者本人,不代表本站立场。本站仅提供信息存储空间服务,不拥有所有权,不承担相关法律责任。 如若内容造成侵权/违法违规/事实不符,请联系我的编程经验分享网邮箱:chenni525@qq.com进行投诉反馈,一经查实,立即删除!
最新文章
- Python教程
- 深入理解 MySQL 中的 HAVING 关键字和聚合函数
- Qt之QChar编码(1)
- MyBatis入门基础篇
- 用Python脚本实现FFmpeg批量转换
- 【C++】异常
- Axure中如何使用交互样式&交互事件&交互动作&情形
- 深信服技术认证“SCCA-C”划重点:云计算基础
- 手把手教你搭建一个数据可视化看板
- selenium+python自动化测试之使用webdriver操作浏览器的方法
- iview inputNumber有一个默认值1,来看解决方案
- 偷流量、端口占用、网络负载高、socket创建释放异常等Android高阶TCP/IP网络问题定位思路
- 快快销ShopMatrix 分销商城多端uniapp可编译5端 - 订单金额满多少,一次性订单金额满多少,充值多少升级
- C# 反射的终点:Type,MethodInfo,PropertyInfo,ParameterInfo,Summry
- 关闭通知、Windows提示和建议、Windows欢迎体验、如何充分利用Windows