一款一键渗透全流程
免责声明
由于传播、利用本文章所提供的信息而造成的任何直接或者间接的后果及损失,均由使用者本人负责,文章及作者不为此承担任何责任,一旦造成后果请自行承担!如有侵权烦请告知,我们会立即删除并致歉。谢谢!
项目简介
Osmedeus 是一个用于进攻性安全的工作流引擎,允许您在各种目标(包括域、URL、CIDR 和 GitHub 存储库)上构建和运行侦察系统。它的设计目的是建立坚实的基础,并具有自动适应和运行的能力,以执行侦察任务
集成工具
子域名收集工具Amass
子域名收集工具subfinder
POC扫描工具nuclei
http工具集,网站基本信息获取
快速提取网段内网站证书信息
网页爬虫httpx
tlsxkatana
DNS枚举工具dnsx
扩展子域名构建alterx
从第三方获取网站相关接囗gau
网站fuzz工具ffuf
网页爬虫工具gospider
自动化测试漏洞jaeles
OSINT 工具metabigor
快速获取接口的基本信息goverview
网站截图工具aquatone
网站截图工具gowitness
从 github寻找凭据trufflehog
查询 git 目录泄漏问题 gitleaks
子域名收集findomain
多个二进制小工具,比如 massdns、rustscan
安装
请注意,您需要一些基本工具,例如以 root 身份登录才能开始curl, wget, git, zip
bash <(curl -fsSL https://raw.githubusercontent.com/osmedeus/osmedeus-base/master/install.sh)
安装完成后,通过命令
osmedeus health
查看是否安装成功,以及其默认工作流:
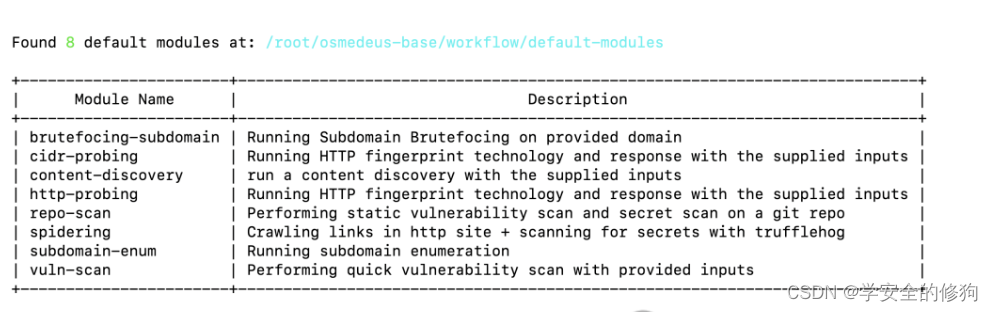
 还有内置的工作模块:
还有内置的工作模块:
 从源代码构建引擎
从源代码构建引擎
确保您已安装golang >= v1.17
go install -v github.com/j3ssie/osmedeus@latest
Osmedeus的主要特点
显著加快您的侦察过程
整理扫描结果
高效定制和优化您的侦察流程
与新的公共和私有工具无缝集成
易于跨大量目标进行扩展
易于在多个位置同步结果
用法
# Example Scan Commands:
## Start a simple scan with default 'general' flow
osmedeus scan -t sample.com
## Start a general scan but exclude some of the module
osmedeus scan -t sample.com -x screenshot -x spider
## Start a scan directly with a module with inputs as a list of http domains like this https://sub.example.com
osmedeus scan -m content-discovery -t http-file.txt
## Initiate the scan using a speed option other than the default setting
osmedeus scan -f vuln --tactic gently -t sample.com
osmedeus scan --threads-hold=10 -t sample.com
osmedeus scan -B 5 -t sample.com
## Start a simple scan with other flow
osmedeus scan -f vuln -t sample.com
osmedeus scan -f extensive -t sample.com -t another.com
osmedeus scan -f urls -t list-of-urls.txt
## Scan list of targets
osmedeus scan -T list_of_targets.txt
osmedeus scan -f vuln -T list-of-targets.txt
## Performing static vulnerability scan and secret scan on a git repo
osmedeus scan -m repo-scan -t https://github.com/j3ssie/sample-repo
osmedeus scan -m repo-scan -t /tmp/source-code-folder
osmedeus scan -m repo-scan -T list-of-repo.txt
## Scan for CIDR with file contains CIDR with the format '1.2.3.4/24'
osmedeus scan -f cidr -t list-of-ciders.txt
osmedeus scan -f cidr -t '1.2.3.4/24' # this will auto convert the single input to the file and run
## Directly run on vuln scan and directory scan on list of domains
osmedeus scan -f domains -t list-of-domains.txt
osmedeus scan -f vuln-and-dirb -t list-of-domains.txt
## Use a custom wordlist
osmedeus scan -t sample.com -p 'wordlists={{Data}}/wordlists/content/big.txt'
## Use a custom wordlist
cat list_of_targets.txt | osmedeus scan -c 2
## Start a normal scan and backup entire workflow folder to the backup folder
osmedeus scan --backup -f domains -t list-of-subdomains.txt
## Start the scan with chunk inputs to review the output way more much faster
osmedeus scan --chunk --chunk-parts 20 -f cidr -t list-of-100-cidr.txt
## Continuously run the scan on a target right after it finished
osmedeus utils cron --for --cmd 'osmedeus scan -t example.com'
## Backing up all workspaces
ls ~/workspaces-osmedeus | osmedeus report compress
# Scan Usage:
osmedeus scan -f [flowName] -t [target]
osmedeus scan -m [modulePath] -T [targetsFile]
osmedeus scan -f /path/to/flow.yaml -t [target]
osmedeus scan -m /path/to/module.yaml -t [target] --params 'port=9200'
osmedeus scan -m /path/to/module.yaml -t [target] -l /tmp/log.log
osmedeus scan --tactic aggressive -m module -t [target]
cat targets | osmedeus scan -f sample
# Practical Scan Usage:
osmedeus scan -T list_of_targets.txt -W custom_workspaces
osmedeus scan -t target.com -w workspace_name --debug
osmedeus scan -f general -t sample.com
osmedeus scan --tactic aggressive -f general -t sample.com
osmedeus scan -f extensive -t sample.com -t another.com
cat list_of_urls.txt | osmedeus scan -f urls
osmedeus scan --threads-hold=15 -f cidr -t 1.2.3.4/24
osmedeus scan -m ~/.osmedeus/core/workflow/test/dirbscan.yaml -t list_of_urls.txt
osmedeus scan --wfFolder ~/custom-workflow/ -f your-custom-workflow -t list_of_urls.txt
osmedeus scan --chunk --chunk-part 40 -c 2 -f cidr -t list-of-cidr.txt
💡 For full help message, please run: osmedeus --hh or osmedeus scan --hh
📖 Documentation can be found here: https://docs.osmedeus.org
使用例子
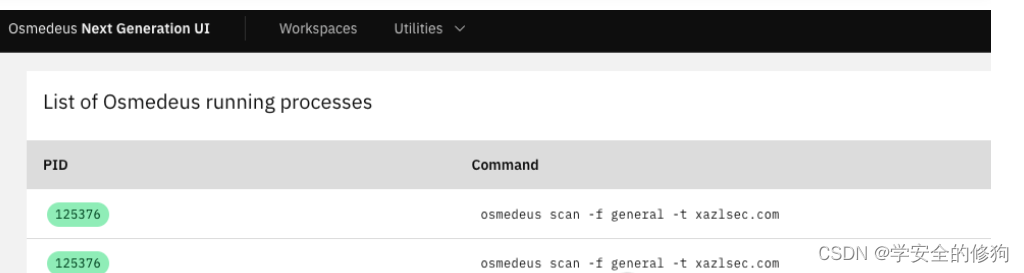
启动 web 界面
osmedeus server
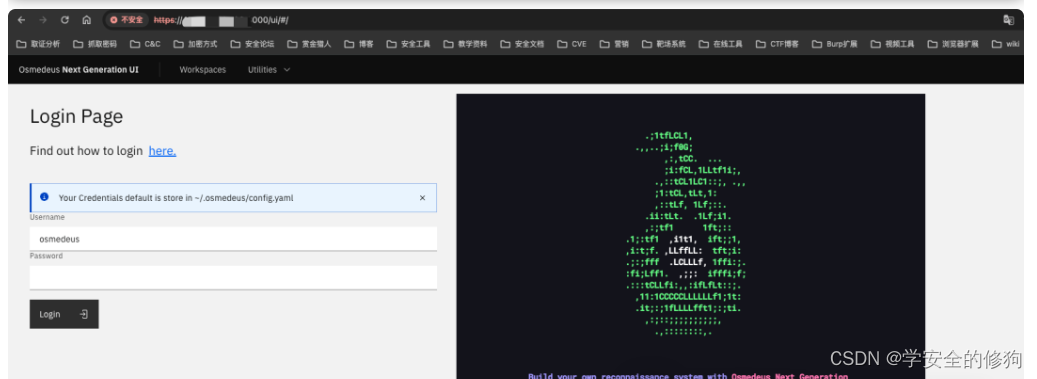
账号密码配置 ~/.osmedeus/config.yaml , 进入后台后:
 创建一个工作流,执行的工作流:
创建一个工作流,执行的工作流:
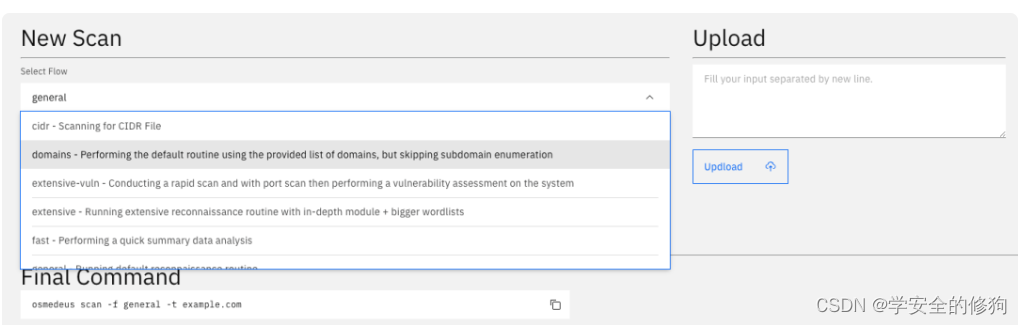
osmedeus scan -f general -t xazlsec.com
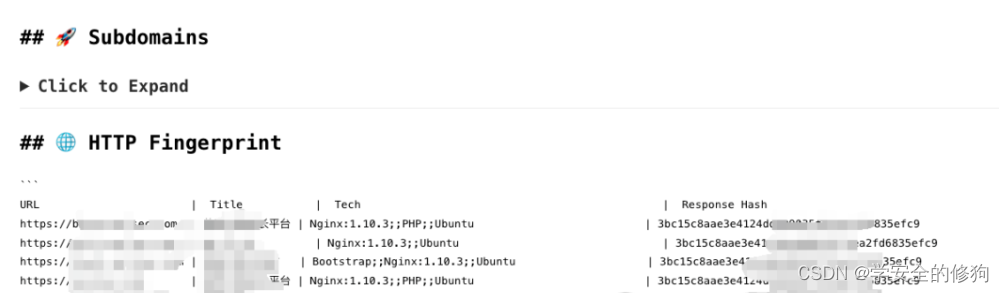
 生成markdown 版的报告
生成markdown 版的报告
下载地址
https://pan.xunlei.com/s/VNnvIWCoXdonbUcTnYCbeanYA1?pwd=h9pg#
https://pan.quark.cn/s/063e924219a3
https://github.com/j3ssie/osmedeus
本文来自互联网用户投稿,该文观点仅代表作者本人,不代表本站立场。本站仅提供信息存储空间服务,不拥有所有权,不承担相关法律责任。 如若内容造成侵权/违法违规/事实不符,请联系我的编程经验分享网邮箱:chenni525@qq.com进行投诉反馈,一经查实,立即删除!
- Python教程
- 深入理解 MySQL 中的 HAVING 关键字和聚合函数
- Qt之QChar编码(1)
- MyBatis入门基础篇
- 用Python脚本实现FFmpeg批量转换
- 软件企业在什么情况下需要找第三方软件测试机构?如何收费?
- 论文笔记 | ICLR 2023 WikiWhy:回答和解释因果问题
- 怎么一边讲PPT一边录视频 如何一边录制PPT一边录制人像 录屏软件免费录屏 PPT录制怎么录制
- 物联网协议之COAP简介及Java实践
- 支付宝 v3 验签如何实现
- Linux系统CPU持续飙高,如何排查?
- go语言实现文件复制、移动(cp、mv命令)
- 【vba】【excel】宏 选择文件夹
- 【Linux】基本指令
- locust快速入门--使用分布式提高测试压力