如何配置TLSv1.2版本的ssl
发布时间:2023年12月26日
1、tomcat配置TLSv1.2版本的ssl
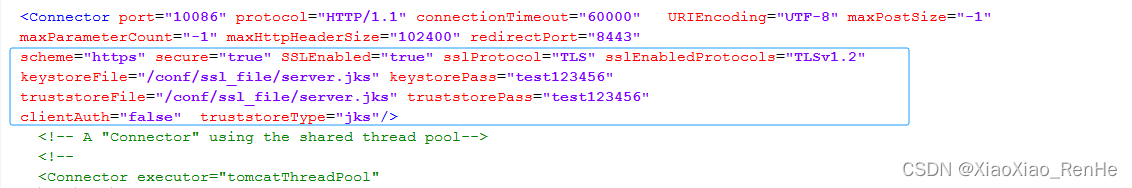
如下图所示,打开tomcat\conf\server.xml文件,进行如下配置:
?注意:需要将申请的tomcat版本的ssl认证文件,如server.jks存放到tomcat\conf\ssl_file\目录下。
<Connector port="10086" protocol="HTTP/1.1" connectionTimeout="60000" URIEncoding="UTF-8" maxPostSize="-1"
maxParameterCount="-1" maxHttpHeaderSize="102400" redirectPort="8443"
scheme="https" secure="true" SSLEnabled="true" sslProtocol="TLS" sslEnabledProtocols="TLSv1.2"
keystoreFile="/conf/ssl_file/server.jks" keystorePass="test123456"
truststoreFile="/conf/ssl_file/server.jks" truststorePass="test123456"
clientAuth="false" truststoreType="jks"/>2、nginx配置TLSv1.2版本的ssl
?nginx配置TLSv1.2版本示例如下:
{
server_name xxx.xxx.com;
listen 443;
ssl on;
access_log /logs/nginx/xxx.xxx.com_access.log main;
error_log /logs/nginx/xxx.xxx.com_error.log;
ssl_certificate /opt/nginx/ssl/xxx.xxx.com.pem; # 公钥证书
ssl_certificate_key /opt/nginx/ssl/xxx.xxx.com.key; # 私钥证书
ssl_session_timeout 5m; # 客户端能够重用会话缓存中ssl参数的过期时间
# 指定支持的协议,这里可以配置TLSv1 TLSv1.1 TLSv1.2, 如果只写1.2表示仅支持1.2. 注:OpenSSL版本要求 >= 1.0.1
ssl_protocols TLSv1.2;
# 加密套件,多个之间用冒号分隔,前有感叹号的表示必须废弃
ssl_ciphers ECDHE-ECDSA-AES128-GCM-SHA256:ECDHE-RSA-AES128-GCM-SHA256:ECDHE-ECDSA-AES256-GCM-SHA384:ECDHE-RSA-AES256-GCM-SHA384:ECDHE-ECDSA-CHACHA20-POLY1305:ECDHE-RSA-CHACHA20-POLY1305:DHE-RSA-AES128-GCM-SHA256:DHE-RSA-AES256-GCM-SHA384;
# 设置协商加密算法,优先使用服务端定义的加密套件
ssl_prefer_server_ciphers on;
}3、验证TLSv1.2是否生效
参照:TestSSLServer4.exe工具使用方法简单介绍(查SSL的加密版本SSL3或是TLS1.2)-CSDN博客
?工具下载见:https://download.csdn.net/download/XiaoXiao_RenHe/88666191
文章来源:https://blog.csdn.net/XiaoXiao_RenHe/article/details/135229183
本文来自互联网用户投稿,该文观点仅代表作者本人,不代表本站立场。本站仅提供信息存储空间服务,不拥有所有权,不承担相关法律责任。 如若内容造成侵权/违法违规/事实不符,请联系我的编程经验分享网邮箱:chenni525@qq.com进行投诉反馈,一经查实,立即删除!
本文来自互联网用户投稿,该文观点仅代表作者本人,不代表本站立场。本站仅提供信息存储空间服务,不拥有所有权,不承担相关法律责任。 如若内容造成侵权/违法违规/事实不符,请联系我的编程经验分享网邮箱:chenni525@qq.com进行投诉反馈,一经查实,立即删除!
最新文章
- Python教程
- 深入理解 MySQL 中的 HAVING 关键字和聚合函数
- Qt之QChar编码(1)
- MyBatis入门基础篇
- 用Python脚本实现FFmpeg批量转换
- 【计算机网络】八股文 | 第四章
- Cytoscape3.9安装包下载及安装教程
- c++ 静态联编+动态联编 (多态)
- PiflowX组件-PostgresCdc
- 中国飞行模拟器行业研究与投资前景报告(2024版)
- 在java语言中关于“标识符”(可以简单的理解为变量名,这里是为了方便理解,标识符包含变量名、类名、方法名和包名等)的使用规则
- 【梅西迭代姊妹篇2】BCH码和m序列参数估计(梅西迭代算法求多项式的C语言实现)
- 设计模式-依赖注入模式
- 鸿蒙开发-ArkUI框架实战【日历应用 】
- linux cat命令增加-f显示文件名功能