kubernetes 容器监控 Sysdig Falco
发布时间:2024年01月09日
?开头语
写在前面:如有问题,以你为准,
目前24年应届生,各位大佬轻喷,部分资料与图片来自网络
内容较长,页面右上角目录方便跳转
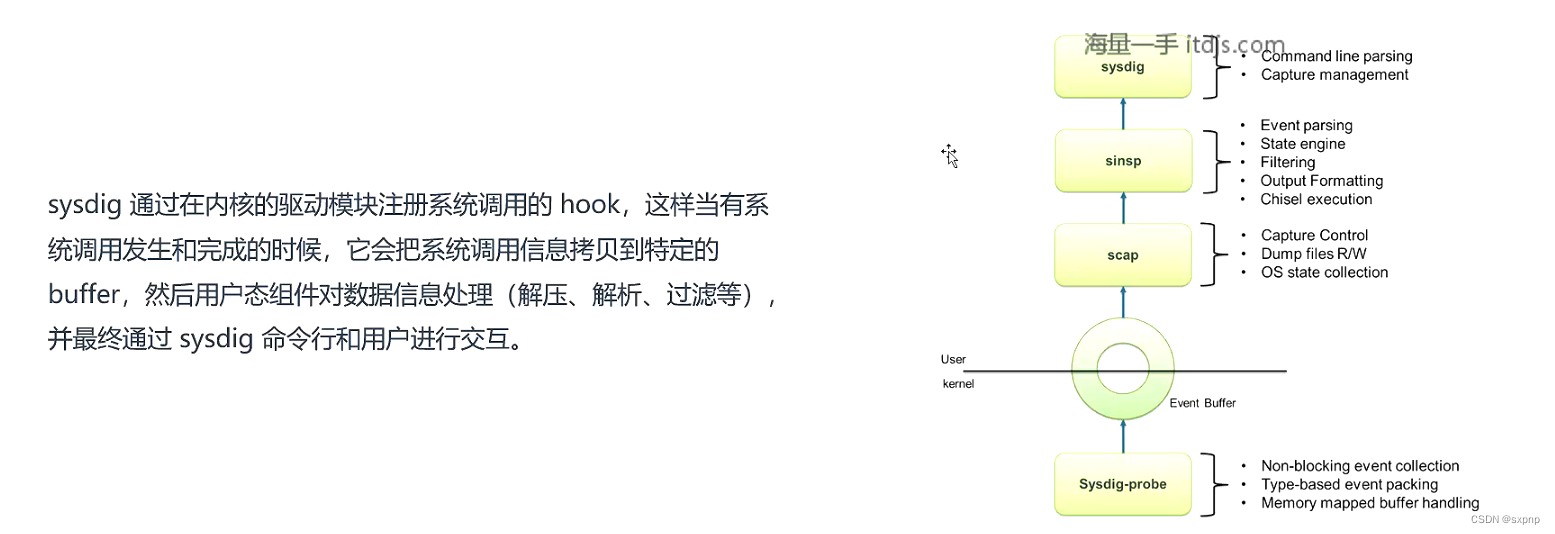
Sysdig 监控容器系统调用
介绍 资料
汇聚 strace+tcpdump+htop+iftop+lsof 工具功能于一身!
sysdig 除了能获取系统资源利用率、进程、网络连接、系统调用等信息,
项目地址:https:/github.com/draios/sysdig
文档:https:/github.com/draios/sysdig/wiki
安装
sudo docker run --rm -i -t --privileged --net=host \
??? -v /var/run/docker.sock:/host/var/run/docker.sock \
??? -v /dev:/host/dev \
??? -v /proc:/host/proc:ro \
??? -v /boot:/host/boot:ro \
??? -v /src:/src \
??? -v /lib/modules:/host/lib/modules:ro \
??? -v /usr:/host/usr:ro \
??? -v /etc:/host/etc:ro \
??? docker.io/sysdig/sysdigcurl -s https://s3.amazonaws.com/download.draios.com/stable/install-sysdig | bashhttps://github.com/draios/sysdig/releases/
[root@master bin]# pwd
/root/k8s/cks/sysdig-falco/sysdig-0.34.1-x86_64/usr/bin
[root@master bin]# ./scap-driver-loader
[root@master bin]# cp ./syscdig /usr/bin/
[root@master bin]# cp ./csyscdig /usr/bin/命令与内容解析
命令介绍
./syscdig
# 执行后所返回的就是工作在宿主机上所有进程系统调用信息
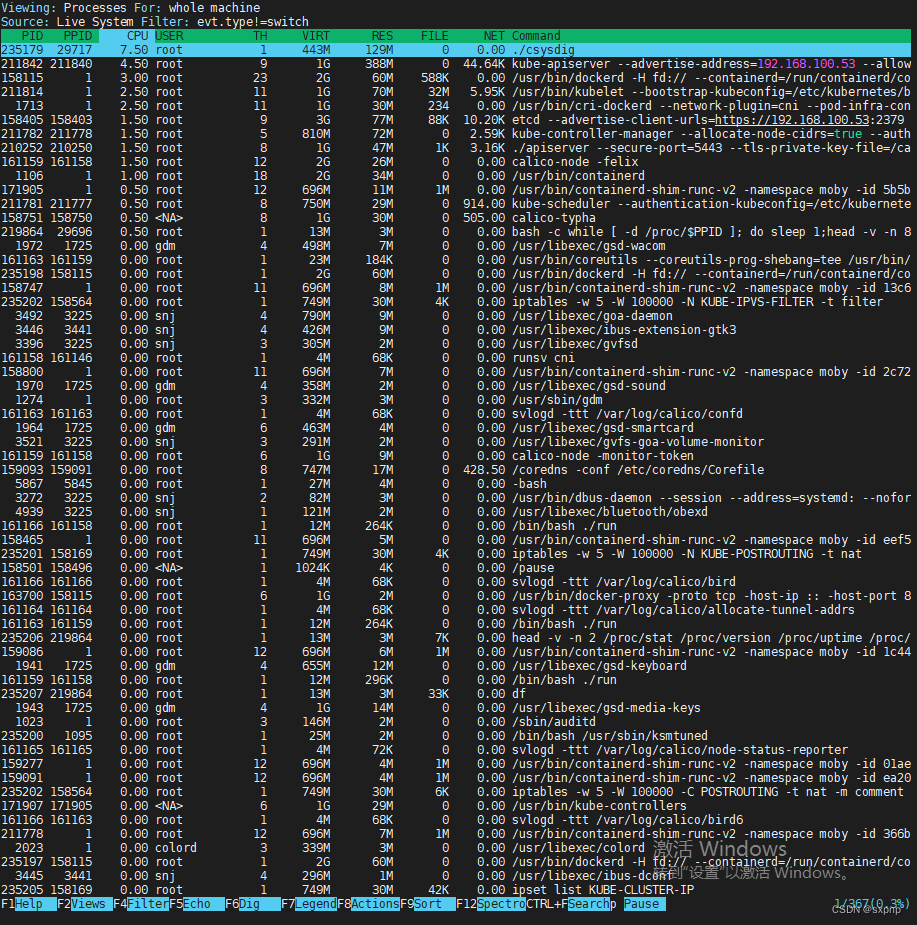
./csyscdig
# 显示以top方式显示sysdig 常用参数:
-l,--list:列出可用于过滤和输出的字段
-M <num seconds>:多少秒后停止收集
-p <output format>,-print:=<output format>:指定打印事件时使用的格式
??? 使用-pc或-pcontainer容器友好的格式
使用-pk或-pkubernetes k8s友好的格式
-c <chiselname><chiselargs>:指定内置工具,可直接完成具体的数据聚合、分析工作
-w <filename>:保存到文件中
-r <filename>:从文件中读取输出格式
53774 02:04:16.549209075 0 sshd (29696.29696) > switch next=0 pgft_maj=8 pgft_min=529 vm_size=165912 vm_rss=3420 vm_swap=0
evt.num: 53774
evt.time: 02:04:16.549209075
evt.cpu: 0
proc.name: sshd
thread.tid: (29696.29696)?sysdig -p "user:%user.name time:%evt.time proc name:%proc.name"
?# 10秒之后暂停
? sysdig? -M 10 -p "user:%user.name time:%evt.time proc name:%proc.name"示例
# 指定输出kubelet相关进程
sysdig proc.name=kubelet
# 查看指定容器中的系统调用,执行后可以在另一个端口使用curl访问一下
docker run -d? --name web nginx:1.17.1chisels
sysdig -cl 列出所有Chisels,以下是一些常用的:
- topprocs_cpu: 输出按照CPU使用率排序的进程列表,例如sysdig-c
- topprocs_net: 输出进程使用网络TOP
- topprocs file: 进程读写磁盘文件TOP
- topfiles bytes: 读写磁盘文件TOP
- netstat: 列出网络的连接情况
sysdig -c topprocs_cpu
CPU%??????????????? Process???????????? PID
--------------------------------------------------------------------------------
5.00%?????????????? kube-apiserver????? 2118426
3.00%?????????????? sysdig????????????? 2879420
3.00%?????????????? calico-node???????? 1611591
2.00%??????????? ???etcd??????????????? 1584058
2.00%?????????????? gvfs-udisks2-vo???? 3494
2.00%?????????????? dockerd???????????? 1581154
1.00%?????????????? containerd-shim???? 2117777
1.00%?????????????? systemd???????????? 1
1.00%?????????????? vmtoolsd??????????? 1074
1.00%?????????????? kubelet???????????? 2118147
可以看出哪个进程占cpu比较高
Falco 监控容器运行时 (未成功)
介绍 资料
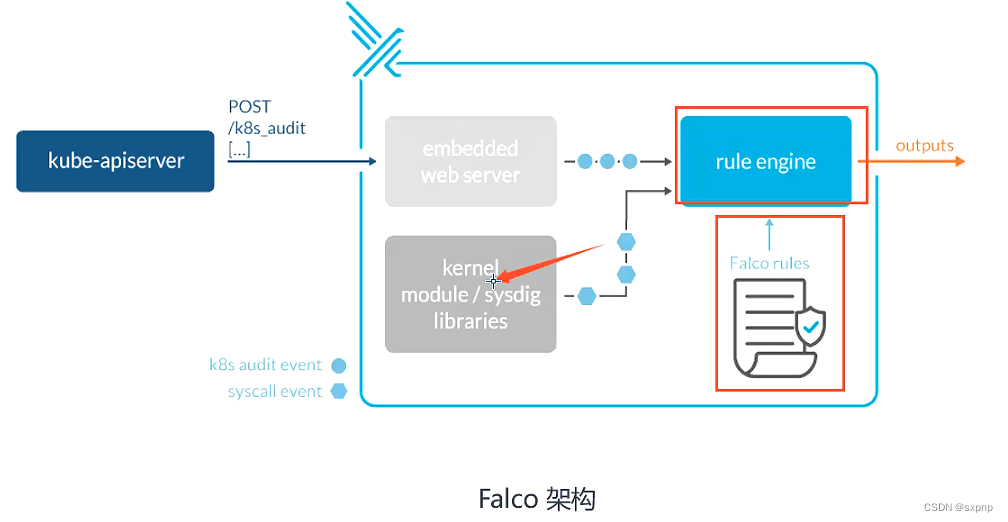
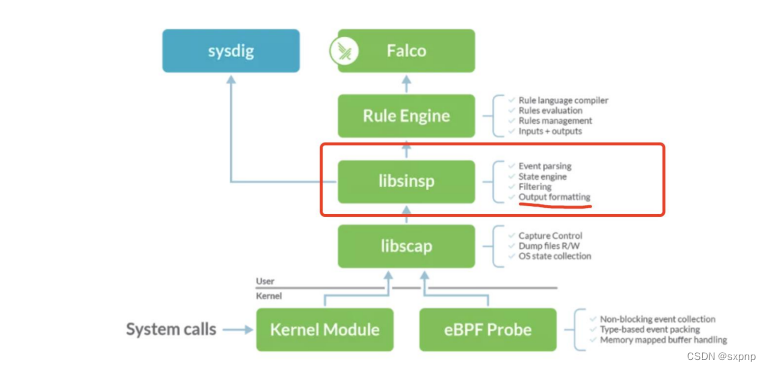
Falco 是一个Linux安全工具,它使用系统调用来保护和监控系统。
Falco 最初是由Sysdig开发的,后来加入CNCF孵化器,成为首个加入CNCF的运行时安全项目。
Falco 提供了一组默认规侧,可以监控内核态的异常行为,例如:
架构
安装
# 源码
https://github.com/falcosecurity/falco/releases/tag/0.36.2
# 源安装
https://falco.org/zh-cn/docs/installation/
rpm --import https://falco.org/repo/falcosecurity-packages.asc
curl -s -o /etc/yum.repos.d/falcosecurity.repo https://falco.org/repo/falcosecurity-rpm.repo
# yum list dkms 查看有没有这个包依赖没有则安装
# yum install epel-release && yum -y install? dkms
?yum -y install falco?# 加载模块
?falco-driver-loader
systemctl start falco-bpf.service && systemctl enable falco-bpf.service
[root@master sysdig-falco]# systemctl list-units | grep falco
? falco-bpf.service???????????????????????????????????????????????????????????????????????????????????????????????????????????????????????????? loaded activating auto-restart Falco: Container Native Runtime Security with ebpf??
? falcoctl-artifact-follow.service????????????????????????????????????????????????????????????????????????????????????????????????????????????? loaded active???? running????? Falcoctl Artifact Follow: automatic artifacts update service配置文件
falco rules.yaml 规侧文件,默认已经定义很多威胁场景(已经内置一些规则)
falco_rules.local.yaml 自定义扩展规则文件(专门给用户自定义的)
k8 s audit rules..yaml? Ka8s审计日志规则
[root@master ~]# tree /etc/falco/
/etc/falco/
├── aws_cloudtrail_rules.yaml
├── falco_rules.local.yaml
├── falco_rules.yaml
├── falco.yaml
├── k8s_audit_rules.yaml
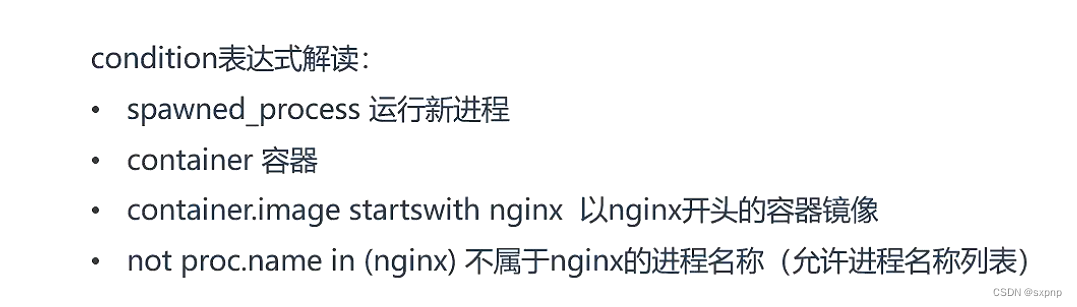
└── rules.d字段解析 falco_rules.local.yaml

编写示例
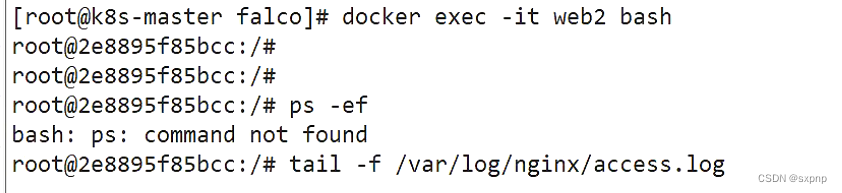
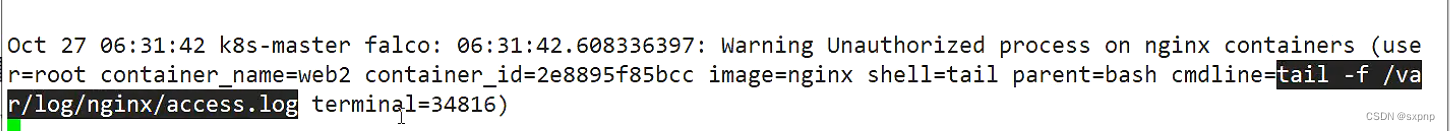
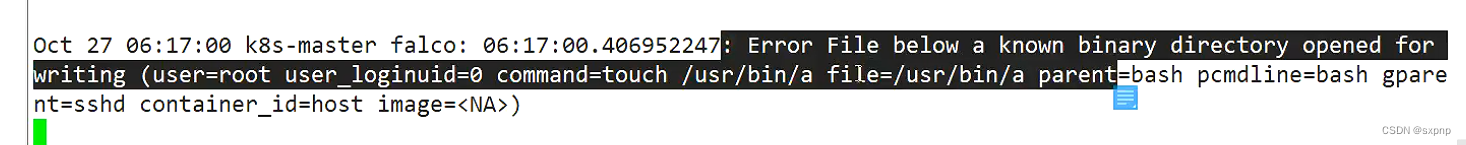
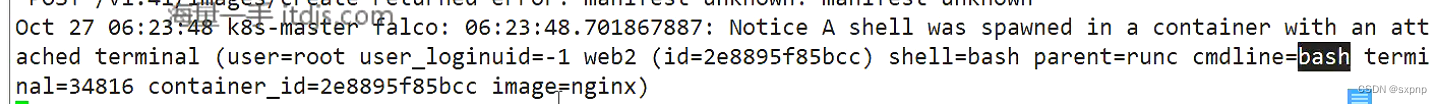
nginx容器里面执行不属于nginx的进程,就进行警告输出到 /var/log/messages
?
更改输出位置
?
?命令
[root@master ~]# falco
Sun Nov 19 21:20:29 2023: Falco version: 0.36.2 (x86_64)
Sun Nov 19 21:20:29 2023: Falco initialized with configuration file: /etc/falco/falco.yaml
Sun Nov 19 21:20:29 2023: Loading rules from file /etc/falco/falco_rules.yaml
Sun Nov 19 21:20:29 2023: Loading rules from file /etc/falco/falco_rules.local.yaml
Sun Nov 19 21:20:29 2023: The chosen syscall buffer dimension is: 8388608 bytes (8 MBs)
Sun Nov 19 21:20:29 2023: Starting health webserver with threadiness 2, listening on port 8765
Sun Nov 19 21:20:29 2023: Loaded event sources: syscall
Sun Nov 19 21:20:29 2023: Enabled event sources: syscall
Sun Nov 19 21:20:29 2023: Opening 'syscall' source with Kernel module
^CSun Nov 19 21:21:28 2023: SIGINT received, exiting...
Syscall event drop monitoring:
?? - event drop detected: 0 occurrences
?? - num times actions taken: 0
Events detected: 0
Rule counts by severity:
Triggered rules by rule name:tail -f /var/log/messages实操
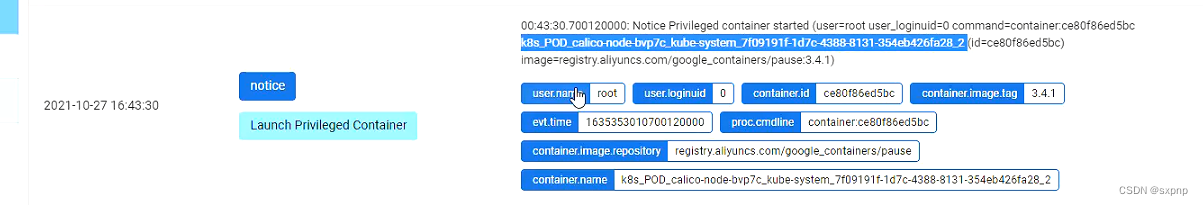
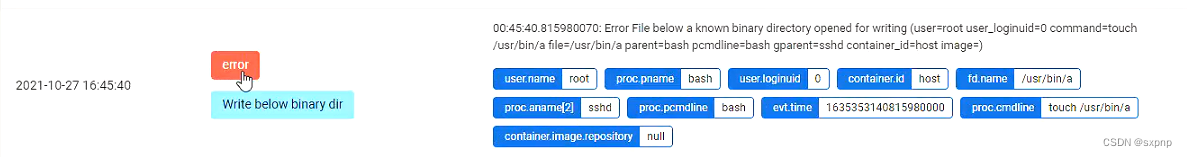
touch /root/testdocker run -d --name web nginx:1.17.1可视化监控(FalcoSideKick)
架构 资料
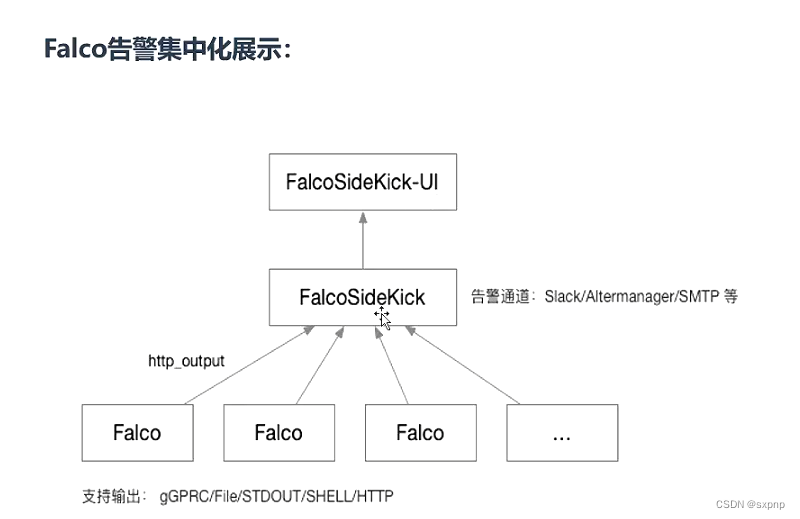
# FalcoSideKick: 一个集中收集并指定输出,支持大量方式输出,例如Influxdb、Elasticsearch等
https://github.com/falcosecurity/falcosidekick
# FalcoSideKick-ui: 告警通知集中图形展示系统
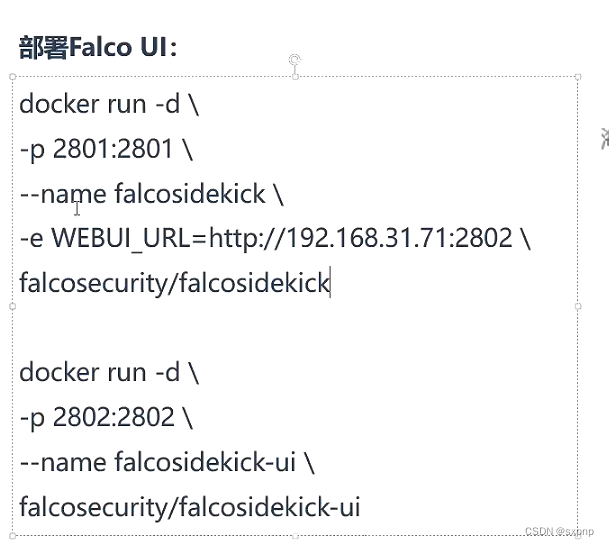
https://github.com/falcosecurity/falcosidekick-ui安装
docker run -d -p 2801:2801 --name falcosidekick -e WEBUI_URL=http://192.168.100.53:2802 falcosecurity/falcosidekick
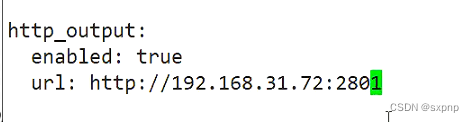
docker run -d -p 2802:2802 --name falcosidekick-ui falcosecurity/falcosidekick-ui修改输出方式
示例
文章来源:https://blog.csdn.net/weixin_48297181/article/details/135484024
本文来自互联网用户投稿,该文观点仅代表作者本人,不代表本站立场。本站仅提供信息存储空间服务,不拥有所有权,不承担相关法律责任。 如若内容造成侵权/违法违规/事实不符,请联系我的编程经验分享网邮箱:chenni525@qq.com进行投诉反馈,一经查实,立即删除!
本文来自互联网用户投稿,该文观点仅代表作者本人,不代表本站立场。本站仅提供信息存储空间服务,不拥有所有权,不承担相关法律责任。 如若内容造成侵权/违法违规/事实不符,请联系我的编程经验分享网邮箱:chenni525@qq.com进行投诉反馈,一经查实,立即删除!