kubernetes Adminssion Webhook 准入控制器 (ImagePolicyWebhook)
发布时间:2024年01月09日
开头语
写在前面:如有问题,以你为准,
目前24年应届生,各位大佬轻喷,部分资料与图片来自网络
介绍 原理 流程
Admission Webhook 准入控制器Vebhook是准入控制插件的一种,用于拦截所有向APISERVER发送的 请求,并且可以修改请求或拒绝请求。
Admission webhook 为开发者提供了非常灵活的插件模式,在kubernetes资源持久化,之前,管理员通过程序 可以对指定资源做校验、修改等操作。例如为资源自动打标签、pod设置默认SA,自动注入sidecar容器等。
https://kubernetes.io/zh-cn/docs/reference/access-authn-authz/admission-controllers/- MutatingAdmissionWebhook? 修改资源,理论上可以监听并修改任何经过ApiServer处理的请求
- ValidatingAdmissionWebhook 验证资源
- ImagePolicyWebhook????????????? 镜像策略,主要验证镜像字段是否满足条件 (仓库,tag)
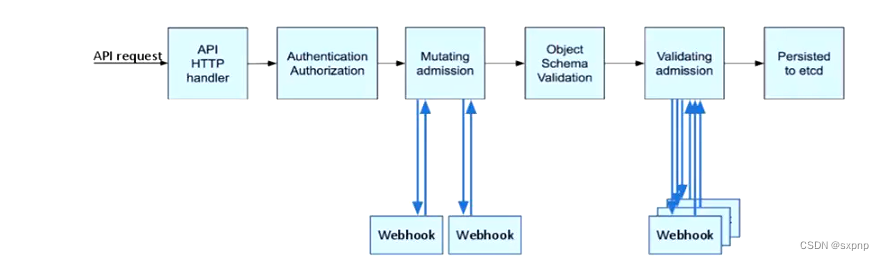
流程:当 api 接收到这个请求后,并进行身份验证授权(Authentication),通过调用准入控制的接口来处理传入过来的资源,资源会传入到Webhook(Mutating),进行对象架构验证(object),再进行资源验证,查看字段是否符合要求(Validating),最后传入etcd中(Persisted to etcd)
ImagePolicyWebhook
架构
通过将传给apiserver创建pod api 传到python docker 上进行检测镜像版本标签
如果不带标签则返回给apiserver拒绝语句,如果带标签则返回接收语句
启用
mkdir /etc/kubernetes/image-policy/
vim admission_configuration.yamlapiVersion: apiserver.config.k8s.io/v1
kind: AdmissionConfiguration
plugins:
- name: ImagePolicyWebhook
? configuration:???
??? imagePolicy:
????? kubeConfigFile: /etc/kubernetes/image-policy/connect_webhook.yaml
????? # 链接镜像策略服务器配置文件
????? # 以秒计的时长,控制批准请求的缓存时间
????? allowTTL: 50
????? # 以秒计的时长,控制拒绝请求的缓存时间
????? denyTTL: 50
????? # 以毫秒计的时长,控制重试间隔
????? retryBackoff: 500
????? # 确定 Webhook 后端失效时的行为
????? defaultAllow: true[root@master opa]# cp /root/.kube/config /etc/kubernetes/image-policy/connect_webhook.yaml
[root@master opa]# vim /etc/kubernetes/image-policy/connect_webhook.yamlzip文件在最顶部
[root@master webhook]# unzip image-policy-webhook.zip
Archive:? image-policy-webhook.zip
?? creating: image-policy-webhook/
? inflating: image-policy-webhook/Dockerfile
? inflating: image-policy-webhook/main.py
? inflating: admission_configuration.yaml
? inflating: connect_webhook.yaml
? inflating: image-policy-certs.sh[root@master image-policy-webhook]# docker pull library/python
Using default tag: latest
latest: Pulling from library/python
8457fd5474e7: Pull complete
13baa2029dde: Pull complete
[root@master image-policy-webhook]# docker build -t webhook-python .
Sending build context to Docker daemon? 3.584kB
Step 1/9 : FROM python
?---> a5d7930b60cc
Step 2/9 : RUN useradd python
?---> Running in 6a893ebbc97e
[root@master webhook]# chmod +x image-policy-certs.sh
[root@master webhook]# ./image-policy-certs.sh
2023/11/15 22:18:52 [INFO] generating a new CA key and certificate from CSR
2023/11/15 22:18:52 [INFO] generate received request
2023/11/15 22:18:52 [INFO] received CSR
2023/11/15 22:18:52 [INFO] generating key: rsa-2048
2023/11/15 22:18:52 [INFO] encoded CSR
2023/11/15 22:18:52 [INFO] signed certificate with serial number 39827921930120332354958212009020451382931127285
2023/11/15 22:18:52 [INFO] generate received request
2023/11/15 22:18:52 [INFO] received CSR
2023/11/15 22:18:52 [INFO] generating key: rsa-2048
2023/11/15 22:18:52 [INFO] encoded CSR
2023/11/15 22:18:52 [INFO] signed certificate with serial number 157085660290104533426640490732748948028109129205
2023/11/15 22:18:52 [INFO] generate received request
2023/11/15 22:18:52 [INFO] received CSR
2023/11/15 22:18:52 [INFO] generating key: rsa-2048
2023/11/15 22:18:53 [INFO] encoded CSR
2023/11/15 22:18:53 [INFO] signed certificate with serial number 20452152514611241358495370727393457709691078555
2023/11/15 22:18:53 [WARNING] This certificate lacks a "hosts" field. This makes it unsuitable for
websites. For more information see the Baseline Requirements for the Issuance and Management
of Publicly-Trusted Certificates, v.1.1.6, from the CA/Browser Forum (https://cabforum.org);
specifically, section 10.2.3 ("Information Requirements").
[root@master webhook]# ls
admission_configuration.yaml? apiserver-client.pem? ca-key.pem???????????? image-policy-webhook????? webhook-key.pem
apiserver-client.csr????????? ca-config.json??????? ca.pem???????????????? image-policy-webhook.zip? webhook.pem
apiserver-client-csr.json???? ca.csr??????????????? connect_webhook.yaml?? webhook.csr
apiserver-client-key.pem????? ca-csr.json?????????? image-policy-certs.sh? webhook-csr.json
[root@master webhook]# cp webhook* image-policy-webhook
[root@master webhook]# cd image-policy-webhook/
docker run -d -u root --name=webhook-python \
-v $PWD/webhook.pem:/data/www/webhook.pem \
-v $PWD/webhook-key.pem:/data/www/webhook-key.pem \
-e PYTHONUNBUFFERED=1 -p 8080:8080 \
webhook-python[root@master image-policy-webhook]# docker ps -a | grep python
fe9713e647e8?? webhook-python????????????????????????????????????? "/bin/sh -c 'python …"?? 11 seconds ago?? Exited (1) 9 seconds ago???????????? webhook-python[root@master webhook]# cp /root/k8s/cks/webhook/webhook.pem /etc/kubernetes/image-policy/
[root@master webhook]# cp /root/k8s/cks/webhook/apiserver-client-key.pem /etc/kubernetes/image-policy/
[root@master webhook]# cp /root/k8s/cks/webhook/apiserver-client.pem /etc/kubernetes/image-policy/
[root@master webhook]# ls /etc/kubernetes/image-policy/
admission_configuration.yaml? apiserver-client-key.pem? apiserver-client.pem? connect_webhook.yaml? webhook.pem下面文件的 /etc/kubernetes/image-policy 是容器内的路径
apiVersion: v1
kind: Config
clusters:
- cluster:
??? certificate-authority: /etc/kubernetes/image-policy/webhook.pem # 数字证书,用于验证远程服务
??? server: https://192.168.100.53:8080/image_policy # 镜像策略服务器地址,必须是https
? name: webhook
contexts:
- context:
??? cluster: webhook
??? user: apiserver
? name: webhook
current-context: webhook
preferences: {}
users:
- name: apiserver
? user:
??? client-certificate: /etc/kubernetes/image-policy/apiserver-client.pem # webhook准入控制器使用的证书
??? client-key: /etc/kubernetes/image-policy/apiserver-client-key.pem # 对应私钥证书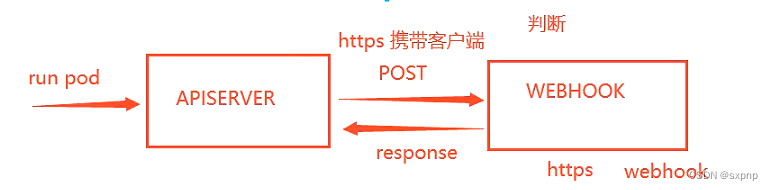
开启插件并使用hostpath 数据卷将宿主机/etc/kubernetes/image-policy目录挂载到容器中
??? - --enable-admission-plugins=NodeRestriction,ImagePolicyWebhook?
??? - --admission-control-config-file=/etc/kubernetes/image-policy/admission_configuration.yaml
# 挂载卷添加
??? - mountPath: /etc/kubernetes/image-policy
????? name: image-policy
?????
? - hostPath:
????? path: /etc/kubernetes/image-policy
????? type: DirectoryOrCreate
??? name: image-policysystemctl restart kubelet测试
是通过python docker 中的python函数进行判断的是否执行创建操作
[root@master image-policy-webhook]# kubectl run web --image=nginx
Error from server (Forbidden): pods "web" is forbidden: image policy webhook backend denied one or more images: 检查镜像失败!镜像标签不允许使用latest!
[root@master image-policy-webhook]# kubectl run web --image=nginx:1.17.1
pod/web created
[root@master image-policy-webhook]# kubectl get pod
NAME?? READY?? STATUS??? RESTARTS?? AGE
web??? 1/1???? Running?? 0????????? 5s策略解析(python)
from flask import Flask,request
import json
app = Flask(__name__)
@app.route('/image_policy',methods=["POST"])
def image_policy():
post_data = request.get_data().decode()
#print("POST数据: %s" %post_data)
data = json.loads(post_data)
for c in data['spec']['containers']:
if ":" not in c['image'] or ":latest" in c['image']: # 如果镜像里不带冒号或者带:latest说明是镜像使用latest标签
allowed, reason = False, "检查镜像失败!镜像标签不允许使用latest!"
break
else:
allowed, reason = True, "检查镜像通过."
print("检查结果: %s" %reason)
result = {"apiVersion": "imagepolicy.k8s.io/v1alpha1","kind": "ImageReview",
"status": {"allowed": allowed,"reason": reason}}
return json.dumps(result,ensure_ascii=False)
if __name__ == "__main__":
app.run(host="0.0.0.0",port=8080,ssl_context=('/data/www/webhook.pem','/data/www/webhook-key.pem'))
文章来源:https://blog.csdn.net/weixin_48297181/article/details/135478975
本文来自互联网用户投稿,该文观点仅代表作者本人,不代表本站立场。本站仅提供信息存储空间服务,不拥有所有权,不承担相关法律责任。 如若内容造成侵权/违法违规/事实不符,请联系我的编程经验分享网邮箱:chenni525@qq.com进行投诉反馈,一经查实,立即删除!
本文来自互联网用户投稿,该文观点仅代表作者本人,不代表本站立场。本站仅提供信息存储空间服务,不拥有所有权,不承担相关法律责任。 如若内容造成侵权/违法违规/事实不符,请联系我的编程经验分享网邮箱:chenni525@qq.com进行投诉反馈,一经查实,立即删除!
最新文章
- Python教程
- 深入理解 MySQL 中的 HAVING 关键字和聚合函数
- Qt之QChar编码(1)
- MyBatis入门基础篇
- 用Python脚本实现FFmpeg批量转换
- Android Studio开发之路(六)(合集)界面优化以及启动图标等
- Vue:将以往的JQ页面,重构成Vue组件页面的大致思路梳理(组件化编码大致流程)
- 【卡梅德生物】稳定细胞系构建的原理及流程
- 一起玩儿物联网人工智能小车(ESP32)——13. 用ESP32的GPIO控制智能小车运动起来(一)
- Acwing linux 第五讲git
- 后台管理系统html页面模板推荐
- 《DAMA数据管理知识体系指南》01—数据架构知识点记录
- 外包干了3个多月,技术退步明显。。。。。
- 手写Spring与基本原理--简易版
- vscode提取扩展时出错xhr