【Grafana】Grafana匿名访问以及与LDAP连接
发布时间:2023年12月22日
上一篇文章利用Docker快速部署了Grafana用来展示Zabbix得监控数据,但还需要给用户去创建账号允许他们登录后才能看展示得数据,那有什么办法让非管理员更方便得去访问Grafana呢?下面介绍两个比较方便实现的:
在开始设置前,为了数据持久化,需要对上一篇中的Docker启动中加入配置文件的持久化配置,具体如下:
# create a persistent volume for data
docker volume create grafana-data
# create a persistent volume for log
docker volume create grafana-log
# create a persistent volume for config
docker volume create grafana-config
# start grafana by using the above persistent storage and defining environment variables
docker run -d -p 3000:3000 --name=grafana --volume grafana-storage:/var/lib/grafana --volume grafana-log:/var/log/grafana --volume grafana-config:/etc/grafana -e "GF_INSTALL_PLUGINS=alexanderzobnin-zabbix-app" grafana/grafana-oss:latest
然后通过以下找到配置文件的具体位置
docker volume inspect grafana-config
[
{
"CreatedAt": "2023-12-22T03:25:15Z",
"Driver": "local",
"Labels": null,
"Mountpoint": "/var/lib/docker/volumes/grafana-config/_data",
"Name": "grafana-config",
"Options": null,
"Scope": "local"
}
]
cd /var/lib/docker/volumes/grafana-config/_data
文件夹内的grafana.ini, ldap.toml是下面配置的重点。
- 匿名访问
通过在配置文件中启用匿名访问来使 Grafana 可以在无需登录的情况下访问。在grafana.ini中找到以下部分并修改
#################################### Anonymous Auth ######################
[auth.anonymous]
# enable anonymous access (default: false)
enabled = true
# Organization name that should be used for unauthenticated users (default: Main Org.)
org_name = Main Org.
# Role for unauthenticated users, other valid values are `Editor` and `Admin` (default: Viewer)
org_role = Viewer
# Hide the Grafana version text from the footer and help tooltip for unauthenticated users (default: false)
hide_version = true
保存配置文件后,重启docker。
docker restart grafana
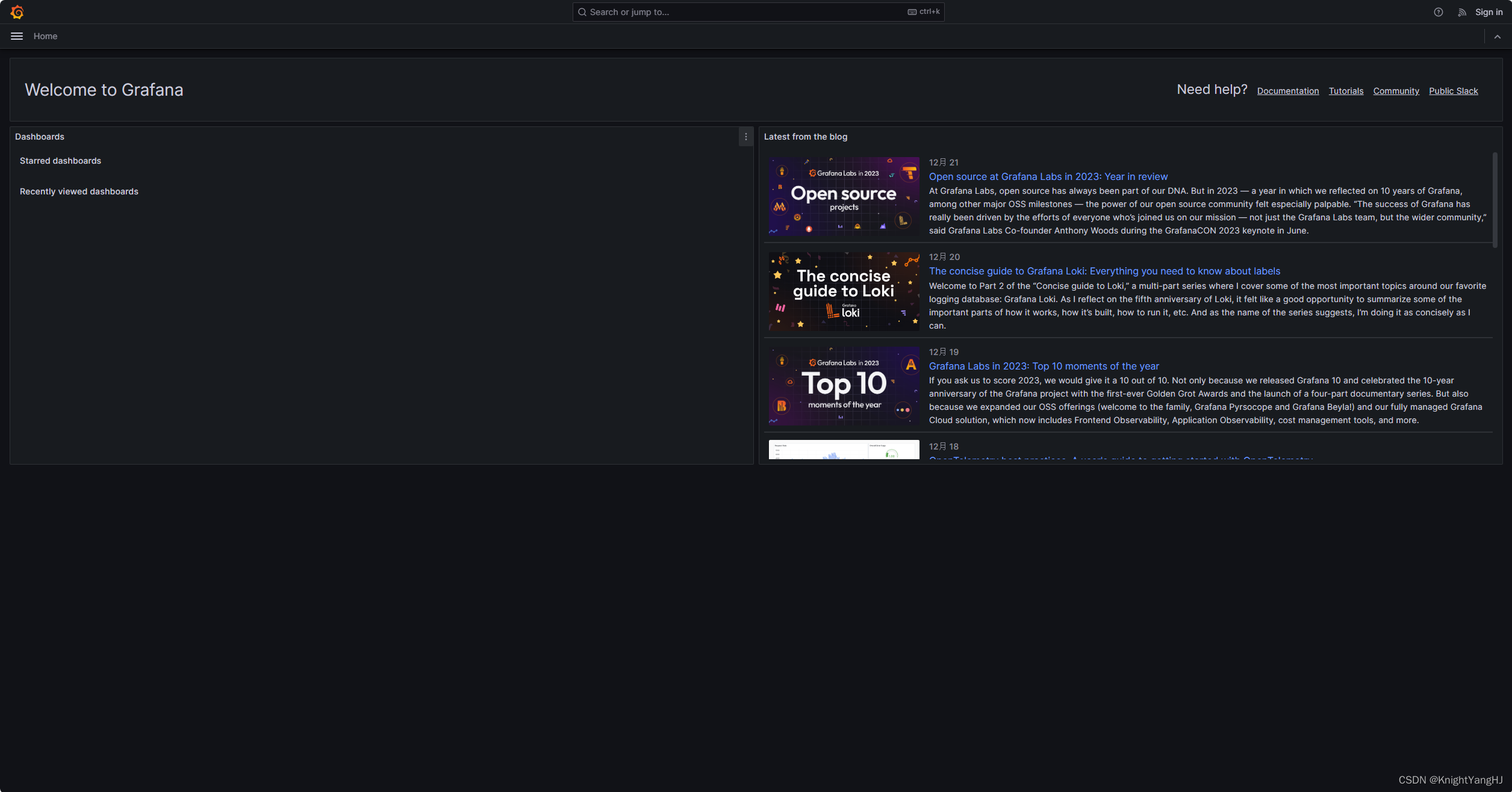
在浏览器中直接访问http://IP:3000/,即可以得到以下显示了。普通用户就不用登录即可查看dashboard了。
- 与LDAP(Windows AD)连接,统一认证登录
要使用 LDAP 集成,首先需要在主配置文件中启用 LDAP,并指定 LDAP 特定配置文件的路径(默认为/etc/grafana/ldap.toml)。
启用 LDAP 后,默认行为是在成功进行 LDAP 身份验证后自动创建 Grafana 用户。如果希望只允许现有的 Grafana 用户登录,您可以在[auth.ldap]部分将allow_sign_up更改为false。如果希望手动分配组织和角色,可以使用skip_org_role_sync配置选项。
#################################### Auth LDAP ##########################
[auth.ldap]
# Set to `true` to enable LDAP integration (default: `false`)
enabled = true
# Path to the LDAP specific configuration file (default: `/etc/grafana/ldap.toml`)
config_file = /etc/grafana/ldap.toml
# Allow sign-up should be `true` (default) to allow Grafana to create users on successful LDAP authentication.
# If set to `false` only already existing Grafana users will be able to login. (default: `true`)
allow_sign_up = true
# Prevent synchronizing ldap users organization roles (default: `false`)
skip_org_role_sync = false
修改完grafana.ini后然后修改ldap.toml文件,需要注意的是如下配置适用于Windows AD提供的LDAP设置。
# To troubleshoot and get more log info enable ldap debug logging in grafana.ini
# [log]
# filters = ldap:debug
[[servers]]
# Ldap server host (specify multiple hosts space separated)
host = "ldap.my_secure_remote_server.org"
# Default port is 389 or 636 if use_ssl = true
port = 389
# Set to true if LDAP server should use an encrypted TLS connection (either with STARTTLS or LDAPS)
use_ssl = false
# If set to true, use LDAP with STARTTLS instead of LDAPS
start_tls = false
# The value of an accepted TLS cipher. By default, this value is empty. Example value: ["TLS_AES_256_GCM_SHA384"])
# For a complete list of supported ciphers and TLS versions, refer to: https://go.dev/src/crypto/tls/cipher_suites.go
tls_ciphers = []
# This is the minimum TLS version allowed. By default, this value is empty. Accepted values are: TLS1.1, TLS1.2, TLS1.3.
min_tls_version = ""
# set to true if you want to skip ssl cert validation
ssl_skip_verify = false
# set to the path to your root CA certificate or leave unset to use system defaults
# root_ca_cert = "/path/to/certificate.crt"
# Authentication against LDAP servers requiring client certificates
# client_cert = "/path/to/client.crt"
# client_key = "/path/to/client.key"
# Search user bind dn
bind_dn = "cn=admin,dc=grafana,dc=org"
# Search user bind password
# If the password contains # or ; you have to wrap it with triple quotes. Ex """#password;"""
bind_password = "grafana"
# We recommend using variable expansion for the bind_password, for more info https://grafana.com/docs/grafana/latest/setup-grafana/configure-grafana/#variable-expansion
# bind_password = '$__env{LDAP_BIND_PASSWORD}'
# Timeout in seconds (applies to each host specified in the 'host' entry (space separated))
timeout = 10
# User search filter, for example "(cn=%s)" or "(sAMAccountName=%s)" or "(uid=%s)"
search_filter = "(sAMAccountName=%s)"
# An array of base dns to search through
search_base_dns = ["dc=grafana,dc=org"]
## For Posix or LDAP setups that does not support member_of attribute you can define the below settings
## Please check grafana LDAP docs for examples
# group_search_filter = "(&(objectClass=posixGroup)(memberUid=%s))"
# group_search_base_dns = ["ou=groups,dc=grafana,dc=org"]
# group_search_filter_user_attribute = "uid"
# Specify names of the ldap attributes your ldap uses
[servers.attributes]
name = "givenName"
surname = "sn"
username = "sAMAccountName"
member_of = "memberOf"
email = "email"
# Map ldap groups to grafana org roles
[[servers.group_mappings]]
group_dn = "cn=admins,ou=groups,dc=grafana,dc=org"
org_role = "Admin"
# To make user an instance admin (Grafana Admin) uncomment line below
# grafana_admin = true
# The Grafana organization database id, optional, if left out the default org (id 1) will be used
# org_id = 1
[[servers.group_mappings]]
group_dn = "cn=editors,ou=groups,dc=grafana,dc=org"
org_role = "Editor"
[[servers.group_mappings]]
# If you want to match all (or no ldap groups) then you can use wildcard
group_dn = "*"
org_role = "Viewer"
更多配置可以参考Grafana官方说明。保存配置文件后,重启docker。
docker restart grafana
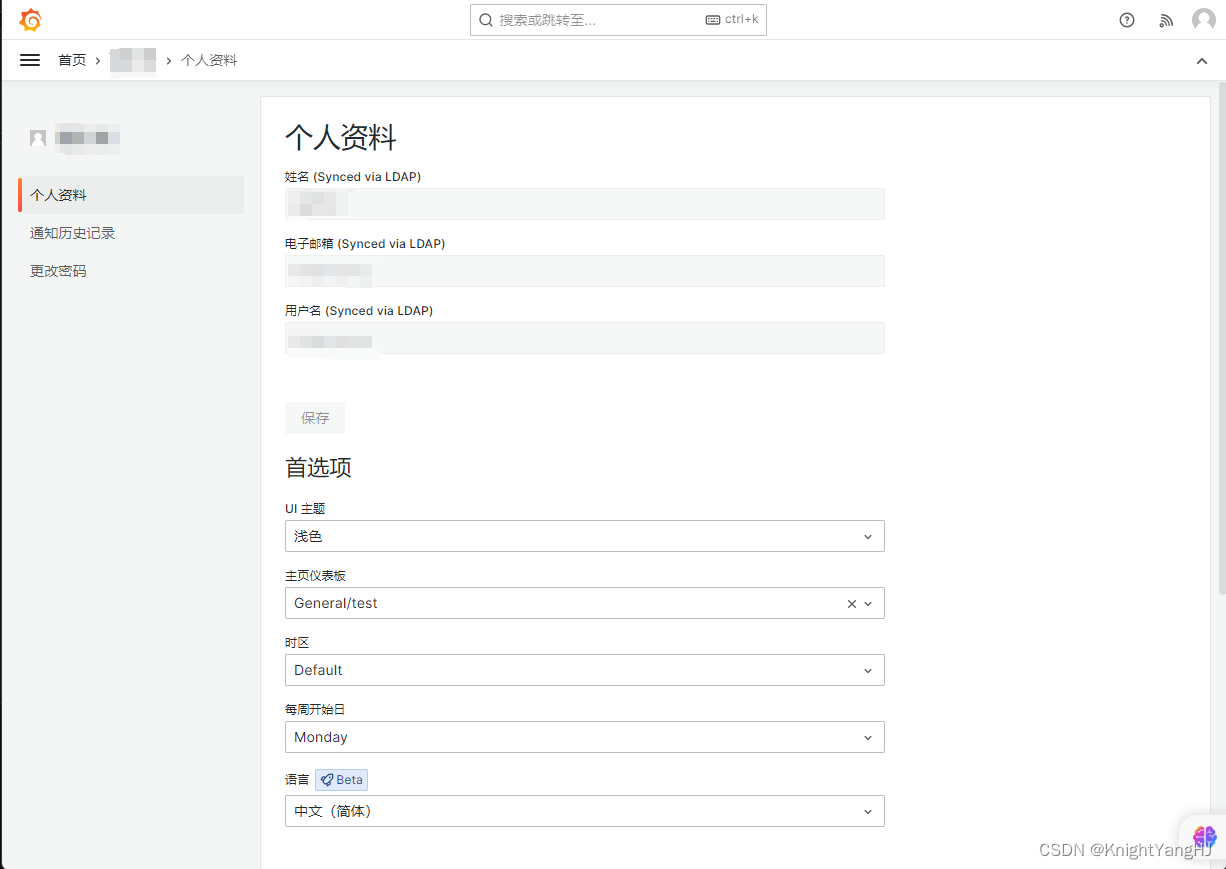
用AD账号登录后可以看到个人资料里面,很多信息就是从AD同步过来的。
文章来源:https://blog.csdn.net/u012153104/article/details/135154999
本文来自互联网用户投稿,该文观点仅代表作者本人,不代表本站立场。本站仅提供信息存储空间服务,不拥有所有权,不承担相关法律责任。 如若内容造成侵权/违法违规/事实不符,请联系我的编程经验分享网邮箱:chenni525@qq.com进行投诉反馈,一经查实,立即删除!
本文来自互联网用户投稿,该文观点仅代表作者本人,不代表本站立场。本站仅提供信息存储空间服务,不拥有所有权,不承担相关法律责任。 如若内容造成侵权/违法违规/事实不符,请联系我的编程经验分享网邮箱:chenni525@qq.com进行投诉反馈,一经查实,立即删除!
最新文章
- Python教程
- 深入理解 MySQL 中的 HAVING 关键字和聚合函数
- Qt之QChar编码(1)
- MyBatis入门基础篇
- 用Python脚本实现FFmpeg批量转换
- java四种线程池创建
- 什么是广告电商模式?
- linux嵌入式开发常用命令
- 查看oracle数据库的运行内存大小和磁盘空间占用大小
- 【知识点随笔分析 | 第六篇】HTTP/1.1,HTTP/2和HTTP/3的区别
- 12.23用树、DAG表示表达式
- TDsql中联合主键怎么创建,Hibernate注解映射联合主键
- Mac中nvm切换node版本失败
- 【Java】JUC并发编程(重量锁、轻量锁、偏向锁)
- 基于深度学习的人脸测距&社交距离过近警报系统